Python Ethical Hacking - WEB PENETRATION TESTING(1)
WHAT IS A WEBSITE
- Computer with OS and some servers.
- Apache, MySQL ...etc.
- Cotains web application.
- PHP, Python ...etc.
- Web application is executed here and not on the client's machine.
How to hack a website?
- An application installed on a computer.
- ->web application pentesting
- Computer uses an OS + other applications.
- ->server side attacks.
- Managed by humans.
- ->client side attacks.
INFORMATION GATHERING
- IP address.
- Domain name info.
- Technologies used.
- Other websites on the same server.
- DNS records.
- Files, sub-domains, directories.
CRAWLING SUBDOMAINS
- Domains before the actual domain name.
- Part of the main domain.
Ex:
- subdomain.target.com
- mail.google.com
- plus.google.com
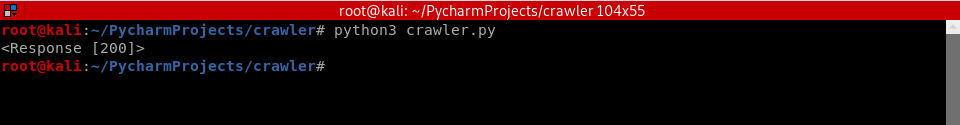
#!/usr/bin/env python import requests
url = "baidu.com"
try:
get_response = requests.get("http://" + url)
print(get_response)
except requests.exceptions.ConnectionError:
pass
Polished Python Code:
#!/usr/bin/env python import requests def request(url):
try:
return requests.get("http://" + url)
except requests.exceptions.ConnectionError:
pass target_url = "baidu.com" with open("subdomains.list", "r") as wordlist_file:
for line in wordlist_file:
word = line.strip()
test_url = word + "." + target_url
response = request(test_url)
if response:
print("[+] Discovered subdomain --> " + test_url)

Python Ethical Hacking - WEB PENETRATION TESTING(1)的更多相关文章
- Python Ethical Hacking - WEB PENETRATION TESTING(2)
CRAWING DIRECTORIES Directories/folders inside the web root. Can contain files or other directories ...
- Python Ethical Hacking - WEB PENETRATION TESTING(5)
Guessing Login Information on Login Pages Our target website: http://10.0.0.45/dvwa/login.php #!/usr ...
- Python Ethical Hacking - WEB PENETRATION TESTING(4)
CRAWING SPIDER Goal -> Recursively list all links starting from a base URL. 1. Read page HTML. 2. ...
- Python Ethical Hacking - WEB PENETRATION TESTING(3)
CRAWLING SUMMARY Our crawler so far can guess: Subdomains. Directories. Files. Advantages: ->Disc ...
- Ethical Hacking - Web Penetration Testing(13)
OWASP ZAP(ZED ATTACK PROXY) Automatically find vulnerabilities in web applications. Free and easy to ...
- Ethical Hacking - Web Penetration Testing(8)
SQL INJECTION WHAT IS SQL? Most websites use a database to store data. Most data stored in it(userna ...
- Ethical Hacking - Web Penetration Testing(10)
SQL INJECTION SQLMAP Tool designed to exploit SQL injections. Works with many DB types, MySQL, MSSQL ...
- Ethical Hacking - Web Penetration Testing(6)
REMOTE FILE INCLUSION Similar to local file inclusion. But allows an attacker to read ANY file from ...
- Ethical Hacking - Web Penetration Testing(4)
CODE EXECUTION VULNS Allows an attacker to execute OS commands. Windows or Linux commands. Can be us ...
随机推荐
- arduino连接1602LCD方法
arduino连接1602LCD方法 参考代码:
- selenium(4)-针对键盘的操作
有哪些键盘操作 删除键 空格键 制表键 回退键 回车键 全选 复制 剪切 粘贴 F1-F12 ......其实就是所有键盘都能模拟,包括alt.shift.insert.delete.home等等等. ...
- 连接 mongodb 数据库 :
mongodb 数据库: 安装 mongodb 数据库: 安装 mongodb 数据库网址: https://www.mongodb.com/download-center#community 检 ...
- 马士兵老师Java虚拟机调优
该视频主要讲解的内容如下所示: 1.虚拟机的内存结构 1.每一个线程都有一个虚拟机栈,线程中每调用一个方法都会开启一个栈帧,栈帧里面保存方法中的局部变量. 2.方法区在java8以后改名为永久区域pe ...
- Redis:rdb和aof
由于redis的数据都直接存储在内存里,在服务器发生宕机时内存的数据会瞬间清空,那么必须要有重启时恢复数据的方法. redis通过持久化机制将数据存储到磁盘中从而在服务器重启时恢复数据,这篇文章主要简 ...
- 入门大数据---Spark开发环境搭建
一.安装Spark 1.1 下载并解压 官方下载地址:http://spark.apache.org/downloads.html ,选择 Spark 版本和对应的 Hadoop 版本后再下载: 解压 ...
- day18__文件操作
一.3 种模式 r: 只读模式, r+: 读写模式,覆盖开头内容 w: 写模式,全覆盖 (如果是没有的文件则重新创建空文件) a+: 读写模式,从最开头写,覆盖开头内容 (如果是没有的 ...
- Oracle安装完成后修改服务器机器名,Oracle部分服务无法启动
Oracle安装完成后修改服务器机器名,Windows server 2012 R2系统提示Oracle 11g下面3个服务无法启动: OracleDBConsoleorcl OracleOraDb1 ...
- Hexo快速构建个人小站-Fulid主题下添加Valine评论系统(三)
Hexo目录: Hexo快速构建个人小站-Hexo初始化和将项目托管在Github(一) Hexo快速构建个人小站-自定义域名和自定义主题(二) 背景交代: 前面两章完成了Hexo的初始化和部分自定义 ...
- 洛谷 P4047 [JSOI2010]部落划分
这道题其实就是无线通讯网的双倍经验啦,只是在输出的时候不同罢了.还是一样的\(kruskal\)算法,但是在求的时候,应该在\(now=n-k+1\)的时候结束.本来到\(n-k\)就行了的,但是由于 ...
