Ethical Hacking - NETWORK PENETRATION TESTING(1)
Pre--Connection-Attacks that can be done before connecting to the network.
Gaining Access - How to break Wi-Fi keys(WEP/WPA/WPA2)
Post-Connection-Attacks can be done after connecting to the network.
Detection&Security - detect and prevent the above attacks
Sniffing Basics - MAC Address
Each network card has a physical static address assigned by the card manufacturer called MAC address(Media Access Control)
This address is used between devices to identify each other and to transfer packets to the right place.
Each packet has a source MAC and a destination MAC.
We can change your MAC address value that is stored in the memory using a program called macchanger like so:
ifconfig [INTERFACE] down
macchanger -m [MAC] [INTERFACE]
ifconfig [INTERFACE] up
[INFTERFACE] = your wifi card name
[MAC] = the mac address you want to use
Install TP-Link TL-WDN5200 Driver on Kali Linux:
1. Check system information and network setting.
root@kali:~# uname -a
Linux kali 5.2.-kali2-amd64 # SMP Debian 5.2.-2kali1 (--) x86_64 GNU/Linux
root@kali:~# cat /etc/issue
Kali GNU/Linux Rolling \n \l root@kali:~# lsusb
Bus Device : ID 0bda:c811 Realtek Semiconductor Corp. .11ac NIC
Bus Device : ID 1d6b: Linux Foundation 2.0 root hub
Bus Device : ID 0e0f: VMware, Inc. Virtual USB Hub
Bus Device : ID 0e0f: VMware, Inc. Virtual Mouse
Bus Device : ID 1d6b: Linux Foundation 1.1 root hub
root@kali:~# lsusb -t
/: Bus .Port : Dev , Class=root_hub, Driver=uhci_hcd/2p, 12M
|__ Port : Dev , If , Class=Human Interface Device, Driver=usbhid, 12M
|__ Port : Dev , If , Class=Hub, Driver=hub/7p, 12M
/: Bus .Port : Dev , Class=root_hub, Driver=ehci-pci/6p, 480M
|__ Port : Dev , If , Class=Vendor Specific Class, Driver=, 480M
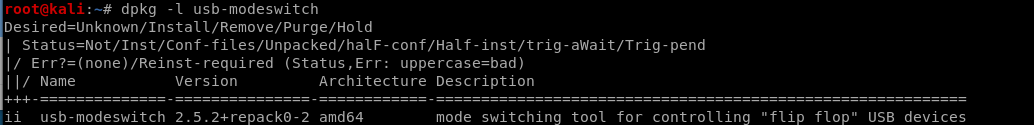
2. Check the usb-modeswitch installation status.
dpkg -l usb-modeswitch
3. Down load the driver code.
https://github.com/chenhaiq/mt7610u_wifi_sta_v3002_dpo_20130916
4.
I will continue after receive the ALFA AWUS1900 WiFi adapter.
Ethical Hacking - NETWORK PENETRATION TESTING(1)的更多相关文章
- Ethical Hacking - NETWORK PENETRATION TESTING(15)
ARP Poisoning - arpspoof Arpspoof is a tool part of a suit called dsniff, which contains a number of ...
- Ethical Hacking - NETWORK PENETRATION TESTING(22)
MITM - Wireshark WIreshark is a network protocol analyser that is designed to help network administa ...
- Ethical Hacking - NETWORK PENETRATION TESTING(14)
MITM - ARP Poisoning Theory Man In The Middle Attacks - ARP Poisoning This is one of the most danger ...
- Ethical Hacking - NETWORK PENETRATION TESTING(13)
Nmap Nmap is a network discovery tool that can be used to gather detailed information about any clie ...
- Ethical Hacking - NETWORK PENETRATION TESTING(12)
Post Connection Attacks Sophisticated attacks that can be used after connecting to the target AP. Ga ...
- Ethical Hacking - NETWORK PENETRATION TESTING(11)
Securing your Network From the Above Attacks. Now that we know how to test the security of all known ...
- Ethical Hacking - NETWORK PENETRATION TESTING(10)
WPA Craking WPA was designed to address the issues in WEP and provide better encryption. The main is ...
- Ethical Hacking - NETWORK PENETRATION TESTING(8)
WEP Cracking Basic case Run airdump-ng to log all traffic from the target network. airodump-ng --cha ...
- Ethical Hacking - NETWORK PENETRATION TESTING(7)
Gaining Access to encrypted networks Three main encryption types: 1. WEP 2.WPA 3.WPA2 WEP Cracking W ...
- Ethical Hacking - NETWORK PENETRATION TESTING(5)
Deauthentication Attacks Theory This attack is used to disconnect any device from any network within ...
随机推荐
- 阿里druid数据源属性配置表
https://cloud.tencent.com/developer/article/1368903 DRUID 属性说明表 属性(Parameter) 默认值(Default) 描述(Descri ...
- android自定义控件onMeasure方法
1.自定义控件首先定义一个类继承View 有时,Android系统控件无法满足我们的需求,因此有必要自定义View.具体方法参见官方开发文档:http://developer.android.com/ ...
- drf-Authentication认证
drf-Authentication认证 ## 源码分析 ```python """ 1)APIView的dispath(self, request, *args, ** ...
- 入门大数据---HBase Shell命令操作
学习方法 可以参考官方文档的简单示例来 点击查看 可以直接在控制台使用help命令查看 例如直接使用help命令: 从上图可以看到,表结构的操作,表数据的操作都展示了.接下来我们可以针对具体的命令使用 ...
- 怎么更改maven工程jdk版本(默为1.5,怎么更改jdk版本为1.8)
使用maven 创建工程更改默认jdk版本(1.5)方法 step1: 找到自己项目的pom.xml文件,添加下图黄色区域代码(文末附上的有代码:可以直接复制) step2: 保存一下更改后的的pom ...
- 全栈的自我修养: 001环境搭建 (使用Vue,Spring Boot,Flask,Django 完成Vue前后端分离开发)
全栈的自我修养: 环境搭建 Not all those who wander are lost. 彷徨者并非都迷失方向. Table of Contents @ 目录 前言 环境准备 nodejs v ...
- nginx配置奇怪问题记录
执行 nginx -t 检查配置报了如下错误: 下面是配置信息 遇到个很奇怪的问题,plm-api-stage 这么配置就可以正常校验过,但是改成 plm-stage-api,就会上面的警告信息: ...
- SpringCloud 断路器之Hystrix
Hystrix-断路器 在分布式环境中,许多服务依赖项中的一些必然会失败.Hystrix是一个库,通过添加延迟容忍和容错逻辑,帮助你控制这些分布式服务之间的交互.Hystrix通过隔离服务之间的访问点 ...
- Spring IoC bean 的初始化
前言 本系列全部基于 Spring 5.2.2.BUILD-SNAPSHOT 版本.因为 Spring 整个体系太过于庞大,所以只会进行关键部分的源码解析. 本篇文章主要介绍 Spring IoC 容 ...
- C语言学习笔记——特别篇(VScode安装使用)
B站有同步教学视频 参考博文: https://www.cnblogs.com/czlhxm/p/11794743.html 注意事项: 请在英文目录下运行!!! VScode下载链接: https: ...
