Ethical Hacking - NETWORK PENETRATION TESTING(1)
Pre--Connection-Attacks that can be done before connecting to the network.
Gaining Access - How to break Wi-Fi keys(WEP/WPA/WPA2)
Post-Connection-Attacks can be done after connecting to the network.
Detection&Security - detect and prevent the above attacks
Sniffing Basics - MAC Address
Each network card has a physical static address assigned by the card manufacturer called MAC address(Media Access Control)
This address is used between devices to identify each other and to transfer packets to the right place.
Each packet has a source MAC and a destination MAC.
We can change your MAC address value that is stored in the memory using a program called macchanger like so:
ifconfig [INTERFACE] down
macchanger -m [MAC] [INTERFACE]
ifconfig [INTERFACE] up
[INFTERFACE] = your wifi card name
[MAC] = the mac address you want to use
Install TP-Link TL-WDN5200 Driver on Kali Linux:
1. Check system information and network setting.
root@kali:~# uname -a
Linux kali 5.2.-kali2-amd64 # SMP Debian 5.2.-2kali1 (--) x86_64 GNU/Linux
root@kali:~# cat /etc/issue
Kali GNU/Linux Rolling \n \l root@kali:~# lsusb
Bus Device : ID 0bda:c811 Realtek Semiconductor Corp. .11ac NIC
Bus Device : ID 1d6b: Linux Foundation 2.0 root hub
Bus Device : ID 0e0f: VMware, Inc. Virtual USB Hub
Bus Device : ID 0e0f: VMware, Inc. Virtual Mouse
Bus Device : ID 1d6b: Linux Foundation 1.1 root hub
root@kali:~# lsusb -t
/: Bus .Port : Dev , Class=root_hub, Driver=uhci_hcd/2p, 12M
|__ Port : Dev , If , Class=Human Interface Device, Driver=usbhid, 12M
|__ Port : Dev , If , Class=Hub, Driver=hub/7p, 12M
/: Bus .Port : Dev , Class=root_hub, Driver=ehci-pci/6p, 480M
|__ Port : Dev , If , Class=Vendor Specific Class, Driver=, 480M
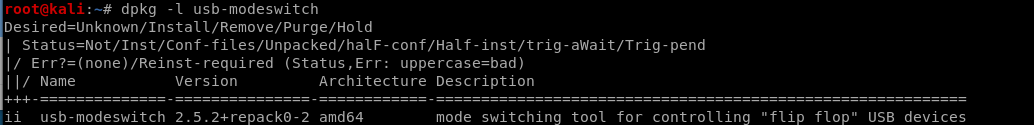
2. Check the usb-modeswitch installation status.
dpkg -l usb-modeswitch
3. Down load the driver code.
https://github.com/chenhaiq/mt7610u_wifi_sta_v3002_dpo_20130916
4.
I will continue after receive the ALFA AWUS1900 WiFi adapter.
Ethical Hacking - NETWORK PENETRATION TESTING(1)的更多相关文章
- Ethical Hacking - NETWORK PENETRATION TESTING(15)
ARP Poisoning - arpspoof Arpspoof is a tool part of a suit called dsniff, which contains a number of ...
- Ethical Hacking - NETWORK PENETRATION TESTING(22)
MITM - Wireshark WIreshark is a network protocol analyser that is designed to help network administa ...
- Ethical Hacking - NETWORK PENETRATION TESTING(14)
MITM - ARP Poisoning Theory Man In The Middle Attacks - ARP Poisoning This is one of the most danger ...
- Ethical Hacking - NETWORK PENETRATION TESTING(13)
Nmap Nmap is a network discovery tool that can be used to gather detailed information about any clie ...
- Ethical Hacking - NETWORK PENETRATION TESTING(12)
Post Connection Attacks Sophisticated attacks that can be used after connecting to the target AP. Ga ...
- Ethical Hacking - NETWORK PENETRATION TESTING(11)
Securing your Network From the Above Attacks. Now that we know how to test the security of all known ...
- Ethical Hacking - NETWORK PENETRATION TESTING(10)
WPA Craking WPA was designed to address the issues in WEP and provide better encryption. The main is ...
- Ethical Hacking - NETWORK PENETRATION TESTING(8)
WEP Cracking Basic case Run airdump-ng to log all traffic from the target network. airodump-ng --cha ...
- Ethical Hacking - NETWORK PENETRATION TESTING(7)
Gaining Access to encrypted networks Three main encryption types: 1. WEP 2.WPA 3.WPA2 WEP Cracking W ...
- Ethical Hacking - NETWORK PENETRATION TESTING(5)
Deauthentication Attacks Theory This attack is used to disconnect any device from any network within ...
随机推荐
- Spring中基于xml的AOP
1.Aop 全程是Aspect Oriented Programming 即面向切面编程,通过预编译方式和运行期动态代理实现程序功能的同一维护的一种技术.Aop是oop的延续,是软件开发中的 一个热点 ...
- WeChair项目Beta冲刺(3/10)
团队项目进行情况 1.昨日进展 Beta冲刺第三天 昨日进展: 昨天工作开始有条不紊地进行着,大家积极交流 2.今日安排 前端:扫码占座功能和预约功能并行开发 后端:扫码占座后端逻辑和预约功能逻 ...
- CentOS7 开机进入emergency mode
今天突然操作了一下磁盘挂载,然后系统启动之后,就直接进入emergency模式了,然后只能输入密码进行救援,截图如下: 突然想了一下最近的一次操作,是因为要挂在镜像,然后每次开机都要挂载一次,觉得比较 ...
- IDEA+Maven+Tomcat构建Web项目的三种方法
[本文版权归微信公众号"代码艺术"(ID:onblog)所有,若是转载请务必保留本段原创声明,违者必究.若是文章有不足之处,欢迎关注微信公众号私信与我进行交流!] 本文将介绍三种方 ...
- Git执行"git rebase -i HEAD~xxx"报错:git rebase fatal: Needed a single revision invalid upstream –i
一.问题"git rebase -i HEAD~xxx"是修改git 历史记录的一个很有用的命令. 但是有时在执行该命令时会出现以下错误:$ git rebase –i HEAD~ ...
- linux网络编程-socket(36)
进程是程序的一次动态执行的过程,进程是短暂的. 一个程序可以对应多个进程,可以打开多个记事本程序,存在多个进程. 线程是进程内部中的控制序列,一个进程至少有一个执行线路. 一个进程可以存在多个线程
- java 中的 自定义viewUtils框架
在前面学习的基础上,我们自己编写一个ViewUtils注解框架类,不清楚的原理看前面的源代码 package im.weiyuan.com.viewutils; import android.supp ...
- 四层发现-TCP发现
直接向目标ip发送一个ACK数据包,正常情况下up状态的目标ip会返回一个SRT数据包. 使用scapy构造TCP数据包: 然后在将一些数据类型设置好就可以发送了. 实用脚本实现批量扫描: #!/us ...
- jvm入门及理解(六)——垃圾回收与算法
一.jvm垃圾回收要做的事情 哪些内存需要回收 什么时候回收 怎么回收 二.如何判断对象已经死亡,或者说确定为垃圾 引用计数法: 给对象中添加一个引用计数器,每当有一个地方引用它时,计数器的值就加1: ...
- zabbix4.4安装
本安装操作系统为centos7.5. 安装前准备: 1.1 安装依赖包: yum -y install wget net-snmp-devel OpenIPMI-devel httpd openssl ...
