Ethical Hacking - NETWORK PENETRATION TESTING(23)
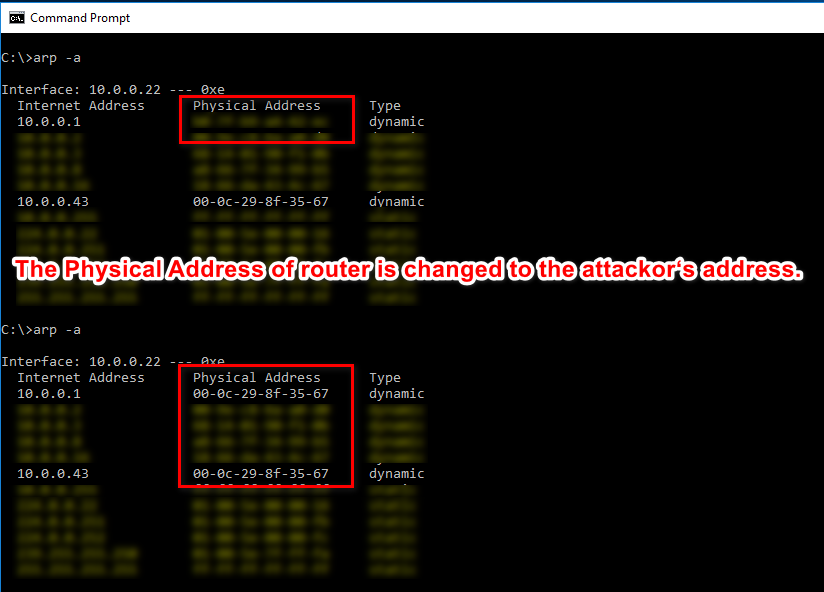
Detecting ARP Posionning Attacks
ARP main security issues:
1. Each ARP requests/response is trusted.
2. Clients can accept responses even if they did not send a request.
We can use the tool called Xarp(http://www.xarp.net/) to detect this kind attack.
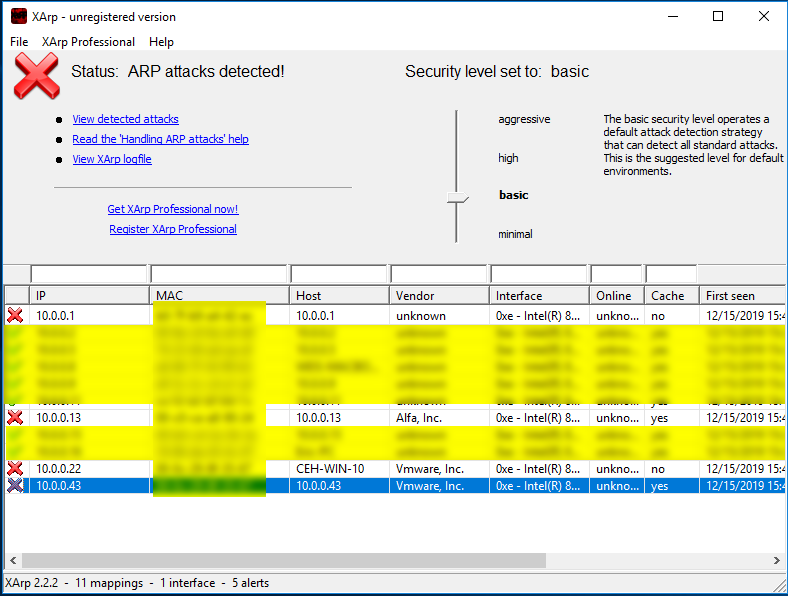
ARP attacks detected....
Ethical Hacking - NETWORK PENETRATION TESTING(23)的更多相关文章
- Ethical Hacking - NETWORK PENETRATION TESTING(15)
ARP Poisoning - arpspoof Arpspoof is a tool part of a suit called dsniff, which contains a number of ...
- Ethical Hacking - NETWORK PENETRATION TESTING(22)
MITM - Wireshark WIreshark is a network protocol analyser that is designed to help network administa ...
- Ethical Hacking - NETWORK PENETRATION TESTING(14)
MITM - ARP Poisoning Theory Man In The Middle Attacks - ARP Poisoning This is one of the most danger ...
- Ethical Hacking - NETWORK PENETRATION TESTING(13)
Nmap Nmap is a network discovery tool that can be used to gather detailed information about any clie ...
- Ethical Hacking - NETWORK PENETRATION TESTING(12)
Post Connection Attacks Sophisticated attacks that can be used after connecting to the target AP. Ga ...
- Ethical Hacking - NETWORK PENETRATION TESTING(11)
Securing your Network From the Above Attacks. Now that we know how to test the security of all known ...
- Ethical Hacking - NETWORK PENETRATION TESTING(10)
WPA Craking WPA was designed to address the issues in WEP and provide better encryption. The main is ...
- Ethical Hacking - NETWORK PENETRATION TESTING(8)
WEP Cracking Basic case Run airdump-ng to log all traffic from the target network. airodump-ng --cha ...
- Ethical Hacking - NETWORK PENETRATION TESTING(7)
Gaining Access to encrypted networks Three main encryption types: 1. WEP 2.WPA 3.WPA2 WEP Cracking W ...
随机推荐
- cb03a_c++_数据结构_顺序容器_STL_stack
/*cb03a_c++_数据结构_顺序容器_STL_stack堆栈:LIFO--Last In First Out后进先出,用于系统程序设计自适应容器(容器适配器),不是独立的容器,是一个适配器栈适配 ...
- @Inherited 注解的作用
@Inherited 用于放在注解上,例如 @Inherited @Documented @Target(ElementType.TYPE) public @interface InheritedAn ...
- java-IO流(commons-io-2.6)使用教程
工具库下载: https://pan.baidu.com/s/1tXXF4zjIfJ9ouObsU5RTpA 提取码:214v 1.打开IDEA 2.在模块下新建个lib文件夹将框架复制进去 3.点 ...
- 一不小心,我就上传了 279674 字的 MySQL 学习资料到 github 上了
自从2019年11月我们出版了<千金良方--MySQL 性能优化金字塔法则>一书之后,持续不断有人来询问我MySQL 4 个系统字典库相关的问题,因为篇幅原因,书中并没有完整收录4个字典库 ...
- openstack Rocky 社区版部署1.2 安装ntp service
一.controller节点安装ntp 1 安装ntp服务 yum install chrony 2 Edit the chrony.conf file and add, change, or rem ...
- GitLab Runner部署(kubernetes环境)
欢迎访问我的GitHub https://github.com/zq2599/blog_demos 内容:所有原创文章分类汇总及配套源码,涉及Java.Docker.Kubernetes.DevOPS ...
- 浅谈MySQL数据库
目录 什么是数据库 定义 发展现状 数据库基本概念 数据库分类 关系数据库 非关系型数据库(NoSQL) 数据库启动与连接 启动服务端 连接数据库 用户信息查看 数据库的基本操作 表的基本操作 记录的 ...
- Zookeeper-Access Control List(ACL)
概述 Z K作为一个分布式协调框架.内部存储着一些分布式系统运行时状态的元数据.如何有效的保护这些数据的安全.如何做一个比较好的权限控制显得非常的重要. ZK 为我们提供一套完善的 ACL(acces ...
- centos7设置系统时间与网络时间同步
Linux的时间分为System Clock(系统时间)和Real Time Clock (硬件时间,简称RTC). 系统时间:指当前Linux Kernel中的时间. 硬件时间:主板上有电池供电的时 ...
- idea2020.1.2破解,亲测可行,激活至2089年!
一.下载最新版IDEA2020安装包 官网:https://www.jetbrains.com/idea/download/ 旧版:https://www.jetbrains.com/idea/dow ...
