An overview of network penetration testing
1、 an SQLi vulnerability will allow you to do the following
- query the database using select statement forezample users table. you might get the password or usersname
- Bypass the login page executing successfuly query results
- Execute system commands in the database in oreder compromise the web server
- Execute inserts.delete commands to manipulate the records in the database
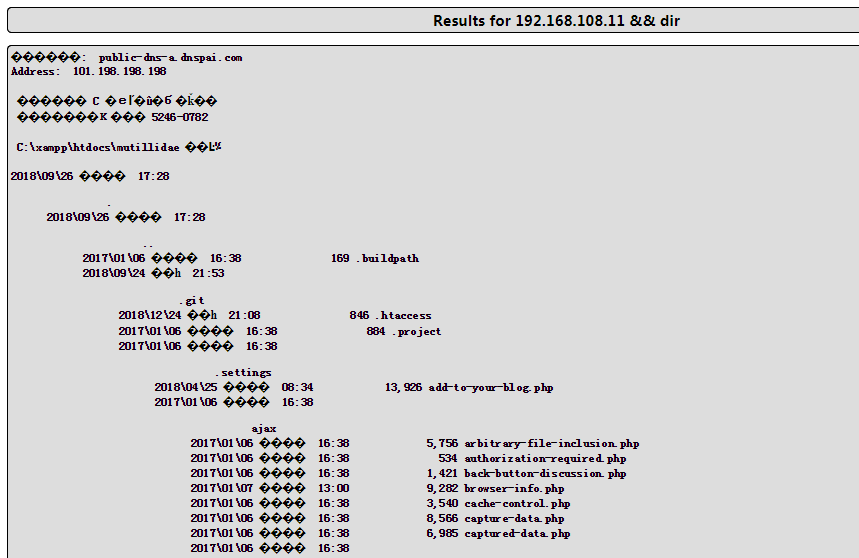
2、Command Injection
we can append other commands after the variable and the application will be to execute it for us , my goal is to make the backend execute someting like this [nslookup [domain name variable ] && [other command ]
3、OWASP top 10
Injection-----> when a attacker can inject and execute a custom command in the backend because of missing sanitization,besides it ,command Injection are more like LDAP、XPath、NoSQLo XML Parsers、STMTP Header
Broken Authentication ------> a hacker finds the user's idntity, credentials bouth name and password or web session
Sesitive Data 、 XML External Entities \ Broken Access Control \ Security Misconfig \Cross-site Scripting \ Insecure Deserialization \ Using Components with know vulnerability\ Insufficient logging
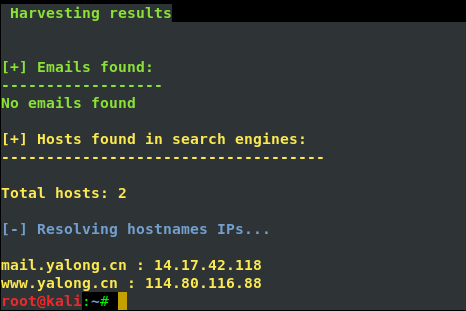
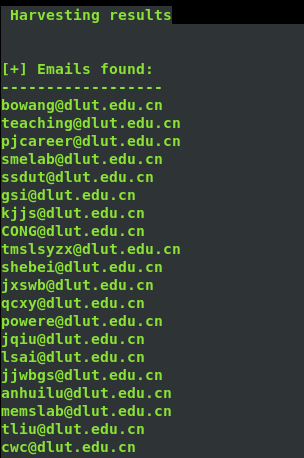
4、邮件信息收集
theharverster -d [目标网络域名地址] -l [邮件地址数量] -b [使用的搜索的公共知识库] eg : theharvester -d yalong.cn -l 20 -b baidu

5、 use Whois search DNS and ip register name and phone number and email
step one we can use the Whois.net the url: http:www.whois.net or another website is NetCraft the url :https://www.netcraft.com/
step two: use the command whois ,the screenshout as follow

another wegit tools is host it can translate ip to hostname
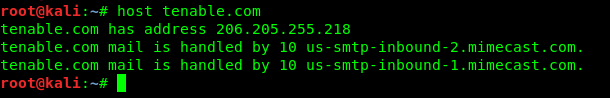
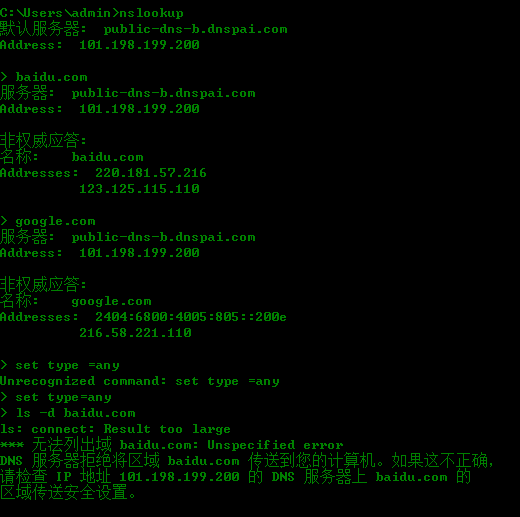
nslookup id find DNS
6、Reconnaissance or information gathering
a pen tester gather information an attacker's perspective ,anything that is useful is necessary to be collected:
- network Digrams、 application and their version、security defences such IDS IPS
- IP address baidu & Social or perfessional networking websites
- Domain names \sites\ Monster.com 、 IP Registries 、DNS registrars \
- Device name the company websites
7、nslookup is a windows tool to find the ip address associated with the given domain name
8、Scanning to finding live address
ICMP scanning use command Nmap -sP [ip range] 、 SYN scanning Commands Nmap -sS -P0 [ip range] 、all port scanning commamds Nmap -sS -p1=65535 -P0 -max-rtt-timeout<time> [iprange]
Specific Prot scanning we know the ususlly port 80` 443 wecan use command Nmap -sS -p80,443 -P0 [ip range]
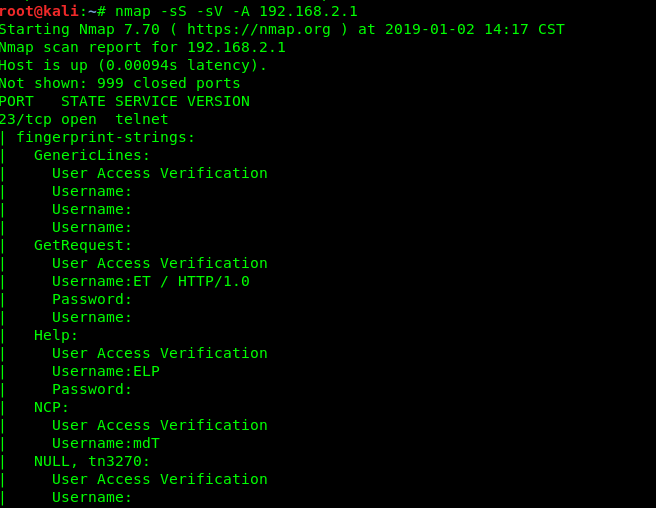
9、OS ans service FingerPrintering
OS detecting is to be done find out the system ,by which know vulnerabilities can be exploited .we can use the commands Namp -O [ip range ] or use Namp -sS -sV -O -P0[ip range] of cose can use the comand to find all port Nmap -sS -sV -O -P0 -p1-65535 -max-rrt-timeout<time> [ip range]
10、Vulnerability Scanning
Nmap has the vulnerability scan switch ,we can run the nmap vulnerability scan the command ; nmap -sS --sV -P0 -p1 -65535 -A --max-rate 500 --reason iL<inputfile.txt><outputfile.txt>
another way we can use nessus nskipfish ,BurpSuite
11、make a conclusion
The reported Vulnerability have to to be tested manually and confirmed since the vulnerability repprted by the scanners my be false positives at times.
An overview of network penetration testing的更多相关文章
- Ethical Hacking - NETWORK PENETRATION TESTING(15)
ARP Poisoning - arpspoof Arpspoof is a tool part of a suit called dsniff, which contains a number of ...
- Ethical Hacking - NETWORK PENETRATION TESTING(22)
MITM - Wireshark WIreshark is a network protocol analyser that is designed to help network administa ...
- Ethical Hacking - NETWORK PENETRATION TESTING(14)
MITM - ARP Poisoning Theory Man In The Middle Attacks - ARP Poisoning This is one of the most danger ...
- Ethical Hacking - NETWORK PENETRATION TESTING(13)
Nmap Nmap is a network discovery tool that can be used to gather detailed information about any clie ...
- Ethical Hacking - NETWORK PENETRATION TESTING(12)
Post Connection Attacks Sophisticated attacks that can be used after connecting to the target AP. Ga ...
- Ethical Hacking - NETWORK PENETRATION TESTING(11)
Securing your Network From the Above Attacks. Now that we know how to test the security of all known ...
- Ethical Hacking - NETWORK PENETRATION TESTING(10)
WPA Craking WPA was designed to address the issues in WEP and provide better encryption. The main is ...
- Ethical Hacking - NETWORK PENETRATION TESTING(8)
WEP Cracking Basic case Run airdump-ng to log all traffic from the target network. airodump-ng --cha ...
- Ethical Hacking - NETWORK PENETRATION TESTING(7)
Gaining Access to encrypted networks Three main encryption types: 1. WEP 2.WPA 3.WPA2 WEP Cracking W ...
随机推荐
- Vue项目搭建与部署
Vue项目搭建与部署 一,介绍与需求 1.1,介绍 Vue 是一套用于构建用户界面的渐进式框架.与其它大型框架不同的是,Vue 被设计为可以自底向上逐层应用.Vue两大核心思想:组件化和数据驱动.组 ...
- idea的一些好用的第三方插件
用了Idea真的回不去Eclipse了,安利一波. 这里记录一些好用的插件. GenerateAllSetter 这个插件是用在写代码的时候调用Setter的时候能一次性把实体类中的所有Setter方 ...
- 【win7】安装php7.3及扩展
php7.3插件php-redisphp-igbinaryphp-amqp [初识RabbitMQ,附RabbitMQ+PHP演示实例]https://www.cnblogs.com/miketwai ...
- BEX5下新建任务到待办任务
List<OrgUnit> list = new ArrayList<OrgUnit>(); // 1.查询出执行者 String sql = "select t.f ...
- css高級技巧
1.鼠標顯示 a:小手cursor:pointer b:默認cursor:default c:勾選文本cursor:text d:拖動cursor:move 2.css三種佈局模型 a.流動模型(默認 ...
- JS类型
1.查看类型 可以使用 typeof 操作符来检测变量的数据类型. typeof "John" // 返回 string typeof 3.14 // 返回 number type ...
- MT【322】绝对值不等式
已知 $a,b,c\in\mathbb R$,求证:$|a|+|b|+|c|+|a+b+c|\geqslant |a+b|+|b+c|+|c+a|$ 分析:不妨设$c=\max\{a,b,c\},\d ...
- python学习日记(初识面向对象)
面向过程 VS 面向对象 面向过程 面向过程的程序设计把计算机程序视为一系列的命令集合,即一组函数的顺序执行.为了简化程序设计,面向过程把函数继续切分为子函数,即把大块函数通过切割成小块函数来降低系统 ...
- python中 yield的用法和生成器generator的说明
详情: https://www.cnblogs.com/python-life/articles/4549996.html
- usb的hid鼠标键盘报告描述符(五)
title: usb的hid鼠标键盘报告描述符 tags: linux date: 2018/12/20/ 18:05:08 toc: true --- usb的hid鼠标键盘报告描述符 https: ...
