Ethical Hacking - NETWORK PENETRATION TESTING(2)
ALFA AWUS 1900 RTL8814AU
https://www.alfa.com.tw/products_detail/2.htm

Follow the guide on aircrack-ng/rtl8812au step by step.
https://github.com/aircrack-ng/rtl8812au
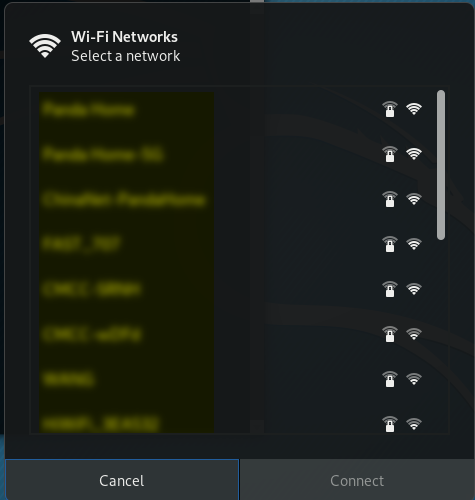
Because VMware Workstation has issues, giving kernel oops on module load. I swith to VirtualBOX VM platform.
Wahoo!! It works in Kali Linux on VirtualBox VM.
Ethical Hacking - NETWORK PENETRATION TESTING(2)的更多相关文章
- Ethical Hacking - NETWORK PENETRATION TESTING(15)
ARP Poisoning - arpspoof Arpspoof is a tool part of a suit called dsniff, which contains a number of ...
- Ethical Hacking - NETWORK PENETRATION TESTING(22)
MITM - Wireshark WIreshark is a network protocol analyser that is designed to help network administa ...
- Ethical Hacking - NETWORK PENETRATION TESTING(14)
MITM - ARP Poisoning Theory Man In The Middle Attacks - ARP Poisoning This is one of the most danger ...
- Ethical Hacking - NETWORK PENETRATION TESTING(13)
Nmap Nmap is a network discovery tool that can be used to gather detailed information about any clie ...
- Ethical Hacking - NETWORK PENETRATION TESTING(12)
Post Connection Attacks Sophisticated attacks that can be used after connecting to the target AP. Ga ...
- Ethical Hacking - NETWORK PENETRATION TESTING(11)
Securing your Network From the Above Attacks. Now that we know how to test the security of all known ...
- Ethical Hacking - NETWORK PENETRATION TESTING(10)
WPA Craking WPA was designed to address the issues in WEP and provide better encryption. The main is ...
- Ethical Hacking - NETWORK PENETRATION TESTING(8)
WEP Cracking Basic case Run airdump-ng to log all traffic from the target network. airodump-ng --cha ...
- Ethical Hacking - NETWORK PENETRATION TESTING(7)
Gaining Access to encrypted networks Three main encryption types: 1. WEP 2.WPA 3.WPA2 WEP Cracking W ...
- Ethical Hacking - NETWORK PENETRATION TESTING(5)
Deauthentication Attacks Theory This attack is used to disconnect any device from any network within ...
随机推荐
- Redis 的 5 种数据类型的基本使用
Redis 中的 5 种数据类型 Redis 中 有 5 种数据结构,分别是 "字符串/string","列表/list","集合/set" ...
- java中的excel操作
导入jxl.jar包: 下载个jxl.jar包,然后这个包放在什么位置都行,在你的项目中导入这个包就可以. 具体做法: 项目上右键,点击“属性”, 类别那里选择”库“,点击"添加jar文 ...
- vue入门的第一天:v-clock、v-text、v-html的使用
vue入门的第一天 1. v-cloak v-cloak可以解决插值闪烁问题(防止代码被人看见),在元素里加入 v-cloak即可 html: <p v-cloak>{{msg}}< ...
- python3 闭包函数 装饰器
闭包函数 1.闭:定义在函数内部的函数 2.包:内部函数引用了外部函数作用域的名字 在函数编程中经常用到闭包.闭包是什么,它是怎么产生的及用来解决什么问题呢.给出字面的定义先:闭包是由函数及其相关的引 ...
- web安全之跨站脚本漏洞(XSS)
XSS(跨站脚本)概述以及pikachu上的实验操作 Cross-Site Scripting 简称为“CSS”,为避免与前端叠成样式表的缩写"CSS"冲突,故又称XSS. XSS ...
- vueX基础知识点笔记
vuex是专门用来管理vue.js应用程序中状态的一个插件.他的作用是将应用中的所有状态都放在一起, 集中式来管理.需要声明的是,这里所说的状态指的是vue组件中data里面的属性.简单的来说, 它就 ...
- DOM-BOM-EVENT(4)
4.dom操作 createElement 创建一个元素 <button id="btn">点击</button> <ul id="ul1& ...
- JavaScript中bool类型的转化
JavaScript 中 if() 圆括号中的表达式将被看做布尔值来处理.这时就涉及到一些转化的问题. 1.特殊值undefined和null变成false. 2.数字0和NaN变成false. 3. ...
- (1)RabbitMQ简介与安装
1.RabbitMQ简介 因为RabbitMQ是基于开源的AMQP协议来实现的,所以在了解MQ时候,首先我们来了解下AMQP协议.AMQP,即Advanced Message Queuing Prot ...
- 洛谷 P6145 【[USACO20FEB]Timeline G】
这道题难就难在建图吧,建图懂了之后,跑一遍最长路就好了(也就是关键路径,但是不会用拓补排序求qnq,wtcl). 怎么建图呢?先不管输入的S,看下面的输入,直接建有向边即可,权值为x.如果现在跑最长路 ...
