Ethical Hacking - NETWORK PENETRATION TESTING(3)
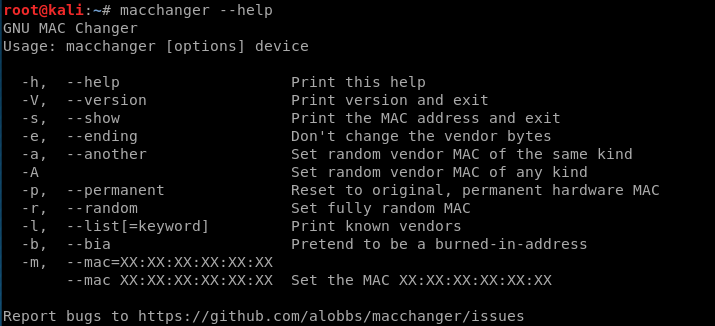
Change MAC Address using macchanger.
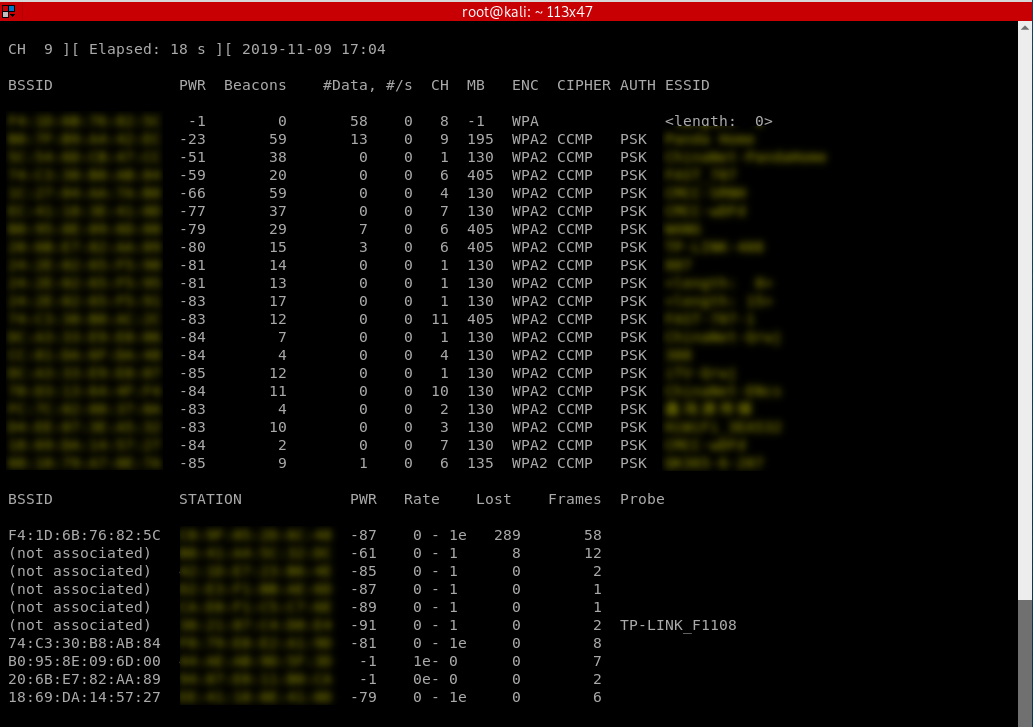
Packet Sniffing Basics Airodump-ng
airodump-ng is a program part of the aircrack-ng package, it's a packet sniffer that allows us to capture all the packets that are in our wifi card range. We can also use it to just scan all wifi networks around us and gather info about them.
Using Airodump-ng:
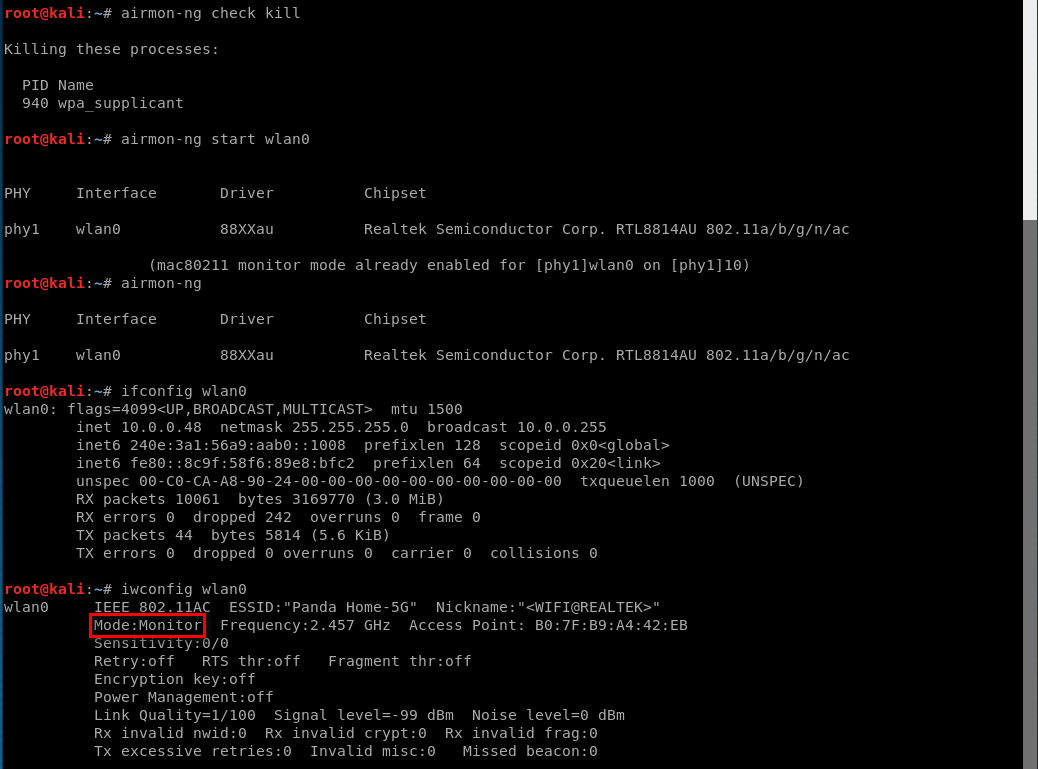
1. Enable monitor mode
airmon-ng start [interface]
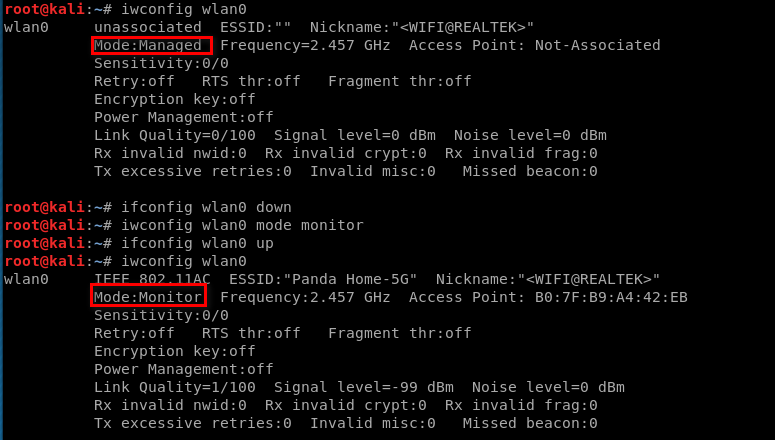
Enabling Monitor Mode Manually.
iwconfig [interface] mode monitor
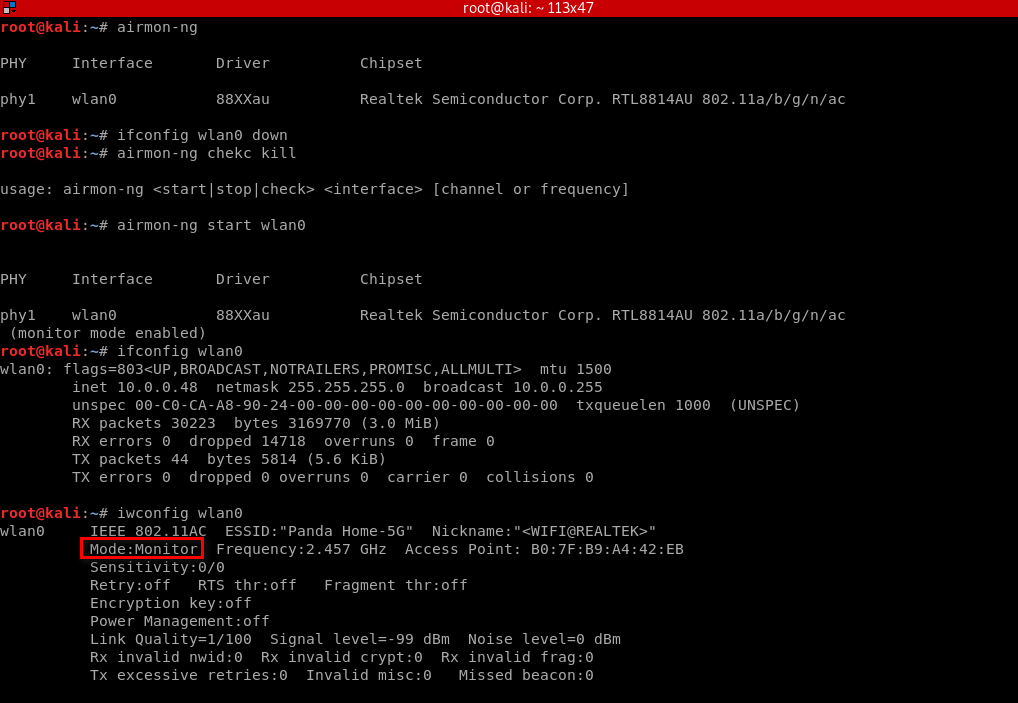
Enabling Monitor Mode Using airmon-ng
airmon-ng check kill
airmon-ng start [interface]
2. Start airodump-ng
airodump-ng [interface]
Ethical Hacking - NETWORK PENETRATION TESTING(3)的更多相关文章
- Ethical Hacking - NETWORK PENETRATION TESTING(15)
ARP Poisoning - arpspoof Arpspoof is a tool part of a suit called dsniff, which contains a number of ...
- Ethical Hacking - NETWORK PENETRATION TESTING(22)
MITM - Wireshark WIreshark is a network protocol analyser that is designed to help network administa ...
- Ethical Hacking - NETWORK PENETRATION TESTING(14)
MITM - ARP Poisoning Theory Man In The Middle Attacks - ARP Poisoning This is one of the most danger ...
- Ethical Hacking - NETWORK PENETRATION TESTING(13)
Nmap Nmap is a network discovery tool that can be used to gather detailed information about any clie ...
- Ethical Hacking - NETWORK PENETRATION TESTING(12)
Post Connection Attacks Sophisticated attacks that can be used after connecting to the target AP. Ga ...
- Ethical Hacking - NETWORK PENETRATION TESTING(11)
Securing your Network From the Above Attacks. Now that we know how to test the security of all known ...
- Ethical Hacking - NETWORK PENETRATION TESTING(10)
WPA Craking WPA was designed to address the issues in WEP and provide better encryption. The main is ...
- Ethical Hacking - NETWORK PENETRATION TESTING(8)
WEP Cracking Basic case Run airdump-ng to log all traffic from the target network. airodump-ng --cha ...
- Ethical Hacking - NETWORK PENETRATION TESTING(7)
Gaining Access to encrypted networks Three main encryption types: 1. WEP 2.WPA 3.WPA2 WEP Cracking W ...
- Ethical Hacking - NETWORK PENETRATION TESTING(5)
Deauthentication Attacks Theory This attack is used to disconnect any device from any network within ...
随机推荐
- AndroidStudio 编译失败;Caused by: org.gradle.api.resources.ResourceException: Could not get resource..
错误信息: Caused by: org.gradle.api.resources.ResourceException: Could not get resource 'https://jcenter ...
- MySQL LOAD DATA INFILE—批量从文件(csv、txt)导入数据
最近做的项目,有个需求(从Elastic Search取数据,业务运算后),每次要向MySQL插入1300万数据左右.最初用MySQL的executemany()一次插入10000条数据,统计的时间如 ...
- 【Vim命令】
命令 操作 :set nu 显示行号 i 编辑模式 :wq 修改并退出 :%s/a/b 把所有的a替换成b
- JDK8--08:Optional
在程序运行时,空指针异常应该是最常见的异常之一,因此JDK8提供了Optional来避免空指针异常. 首先说明JDK8新增的Optional及相关方法的使用 Optional的常用操作: Option ...
- 从数据库中取时间值,遇到:java.sql.Timestamp cannot be cast to java.lang.Long
将 java.sql.Timestamp 类型转换为 java.util.Date 类型.二者其实是父子关系,直接 Date d = (Date)时间戳 就可以了. Date d = (Date)时间 ...
- 《算法笔记》6.6小节 问题 A: 任务调度
这道题我一开始看到的时候,想到的是拓补排序,可是这么菜又这么懒的我怎么可能用呢,既然出现在优先队列里面,那么久一定和他有关了 可是并没有使用优先队列 思路: 对于这道题,我们肯定是对他们定义优先级,然 ...
- 让IE下载跟迅雷一样快?
网络上搜的没试过... 修改IE支持多线程即可: HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settin ...
- Java嵌套类,内部类和外部类
1.嵌套类,内部类 嵌套类是指被定义在一个类内部的类: JAVA的嵌套类有很多种类:1.静态成员类:2.非静态成员类:3.匿名类:4.局部类:其中,除了静态成员类之外,其他的都是内部类,因为静态成员类 ...
- Face The Right Way思维。。。
题目再次链接 题意: 已知01序列a,求进行定长子串取反的最少操作次数,以及最少时的定长. 分析: 首先,先想一想怎么暴力吧.这样想:要保证最小,那么必然不会对同一个区间反转两次,而在k一定时,则不会 ...
- cmake的下载和安装
背景: 最近迷上了 vscode 编辑器, 快速便捷,而且插件丰富,使用起来很爽.既然这样,本身游戏也是用 mingw 加 cygwin 开发的, 可以配置一下,开搞. 实操: 1.登陆cmake官网 ...
