Ethical Hacking - NETWORK PENETRATION TESTING(3)
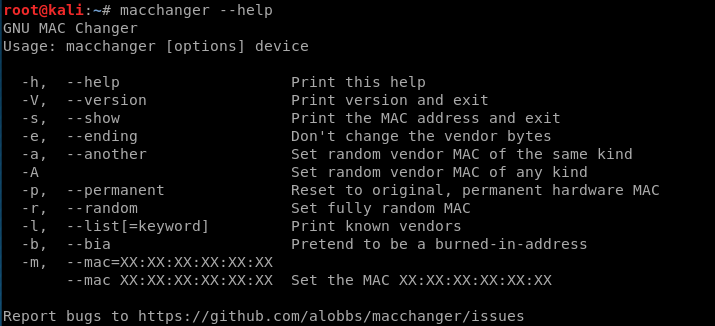
Change MAC Address using macchanger.
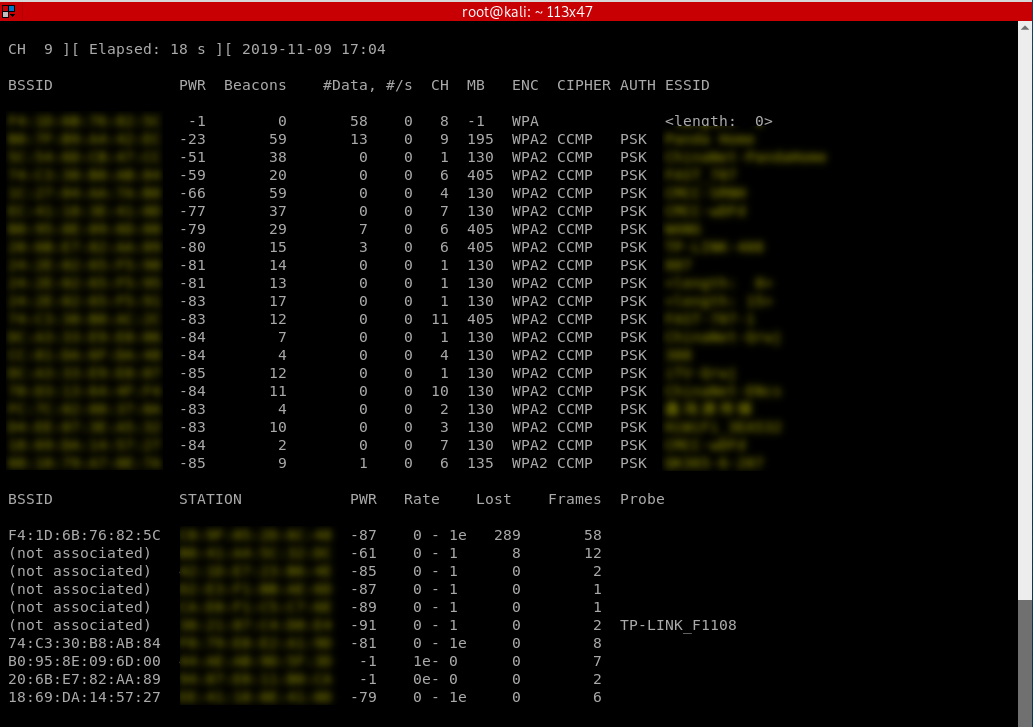
Packet Sniffing Basics Airodump-ng
airodump-ng is a program part of the aircrack-ng package, it's a packet sniffer that allows us to capture all the packets that are in our wifi card range. We can also use it to just scan all wifi networks around us and gather info about them.
Using Airodump-ng:
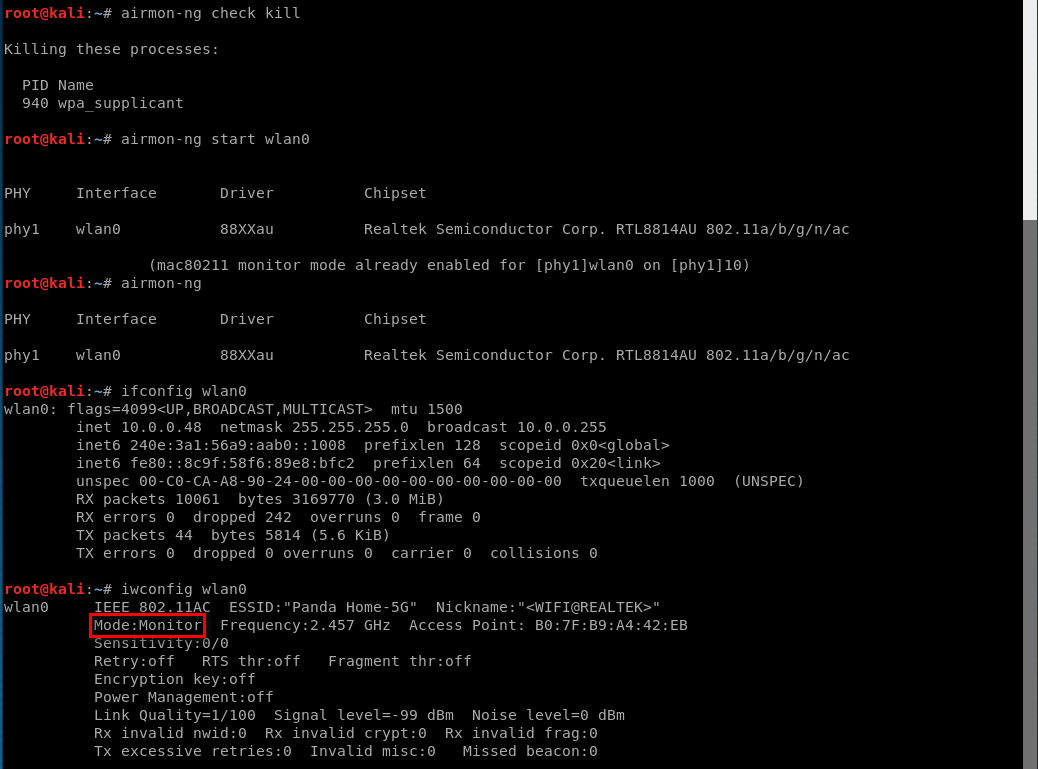
1. Enable monitor mode
airmon-ng start [interface]
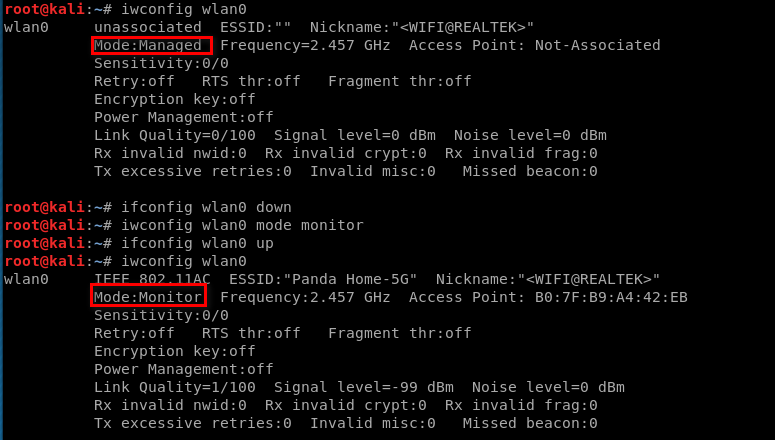
Enabling Monitor Mode Manually.
iwconfig [interface] mode monitor
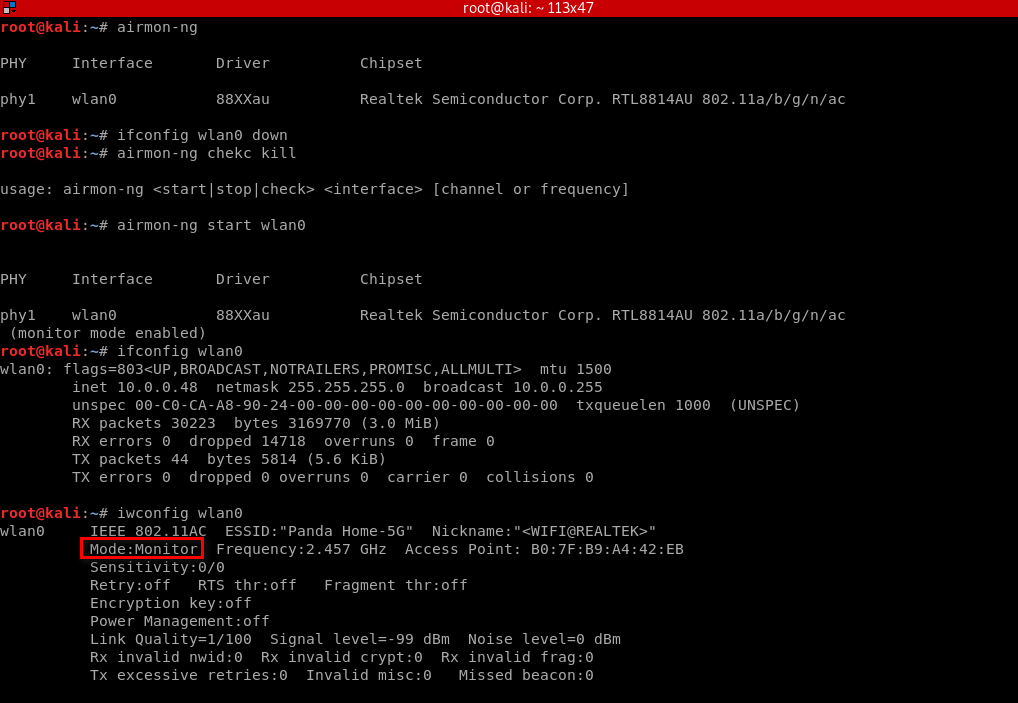
Enabling Monitor Mode Using airmon-ng
airmon-ng check kill
airmon-ng start [interface]
2. Start airodump-ng
airodump-ng [interface]
Ethical Hacking - NETWORK PENETRATION TESTING(3)的更多相关文章
- Ethical Hacking - NETWORK PENETRATION TESTING(15)
ARP Poisoning - arpspoof Arpspoof is a tool part of a suit called dsniff, which contains a number of ...
- Ethical Hacking - NETWORK PENETRATION TESTING(22)
MITM - Wireshark WIreshark is a network protocol analyser that is designed to help network administa ...
- Ethical Hacking - NETWORK PENETRATION TESTING(14)
MITM - ARP Poisoning Theory Man In The Middle Attacks - ARP Poisoning This is one of the most danger ...
- Ethical Hacking - NETWORK PENETRATION TESTING(13)
Nmap Nmap is a network discovery tool that can be used to gather detailed information about any clie ...
- Ethical Hacking - NETWORK PENETRATION TESTING(12)
Post Connection Attacks Sophisticated attacks that can be used after connecting to the target AP. Ga ...
- Ethical Hacking - NETWORK PENETRATION TESTING(11)
Securing your Network From the Above Attacks. Now that we know how to test the security of all known ...
- Ethical Hacking - NETWORK PENETRATION TESTING(10)
WPA Craking WPA was designed to address the issues in WEP and provide better encryption. The main is ...
- Ethical Hacking - NETWORK PENETRATION TESTING(8)
WEP Cracking Basic case Run airdump-ng to log all traffic from the target network. airodump-ng --cha ...
- Ethical Hacking - NETWORK PENETRATION TESTING(7)
Gaining Access to encrypted networks Three main encryption types: 1. WEP 2.WPA 3.WPA2 WEP Cracking W ...
- Ethical Hacking - NETWORK PENETRATION TESTING(5)
Deauthentication Attacks Theory This attack is used to disconnect any device from any network within ...
随机推荐
- 商城08——activeMQ 使用消息队列同步索引库
1. 课程计划 1.什么是MQ 2.MQ的应用场景 3.ActiveMQ的使用方法. 4.使用消息队列实现商品同步. 2. 同步索引库分析 方案一:在taotao-manager中,添加商品的业务 ...
- cb08a_c++_顺序容器的操作1
cb08a_c++_顺序容器的操作1容器定义的类型别名begin(闭区间)和end(开区间)成员{first,last)左闭右开,左包括,右不包括,end()指向最后一个的下一个. /*cb08a_c ...
- 基于web网站项目的性能测试结果分析
业务背景: 最近公司研发了一款对并发要求比较高的web项目,需要对其压力测试,模拟线上可能存在的问题,这个过程中遇到一些很多问题,这里重新梳理一下思路,希望能给遇到同样问题的小伙伴提供一个参考. 工具 ...
- cron计划任务
格式 crontab -e [-u 用户名] ##编辑:注意,每项工作都是一行. crontab -l [-u 用户名] ##查看 crontab -r [-u 用户名] #清除 分 时 日 月 周 ...
- QT槽函数获取信号发送对象
Qt 在槽函数中获取信号发送对象 Qt中提供了一个函数 qobject_cast(QObject *object),可以通过这个函数判断信号发出对象 Qt 帮助文档的解释: Returns the g ...
- C#数据结构与算法系列(十二):递归(Recursion)
1.介绍 简单的说:递归就是方法自己调用自己,每次调用时传入不同的变量,递归有助于编程者解决复杂的问题,同时也让代码变得整洁 2.规则 执行一个方法时,就创建一个新的受保护的独立空间(栈空间) 方法的 ...
- php - 如何解决CURL错误( 7 ): 无法连接到主机?
php - 如何解决CURL错误( 7 ): 无法连接到主机? 1. 问题描述 调用第三方接口,本地调用一切ok,线上调用失败! 本地通过curLRequest()方法调用第三方接口时,curl_er ...
- Python3-内置类型-集合类型
Python3中的集合类型主要有两种 set 可变集合 可添加和删除元素,它是不可哈希的,因此set对象不能用作字典的键或另一个元素的集合 forzenset 不可变集合 正好与set相反,其内容创建 ...
- 【秒懂Java】【第1章_初识Java】01_编程语言
各位小伙伴们好哇!从今日起,我将开始更新<秒懂Java>系列文章,从0开始讲解Java的方方面面,后面也将推出配套的视频版,欢迎大家保持关注! 我会尽力办到:在保证通俗易懂的同时,不丢失知 ...
- METS介绍
METS介绍 首页 > 关于METS > METS介绍 医护英语水平考试(Medical English Test System, 以下简称:METS)是由教育部考试中心与中国国际 ...
