Python Ethical Hacking - VULNERABILITY SCANNER(1)
HTTP REQUESTS
BASIC INFORMATION FLOW
- The user clicks on a link.
- HTML website generates a request(client-side)
- The request is sent to the server.
- The server performs the requests(server-side)
- Sends response back.
GET vs POST
Two main methods used to send data to the web application:
1. Through the URL(Usually using GET).
a. http://webisite.com/news.php?id=1
b. http://website.com/?id=1
2. Through input elements(Usually using POST).
a. Search boxes.
b. Login boxes.
c. ..etc.
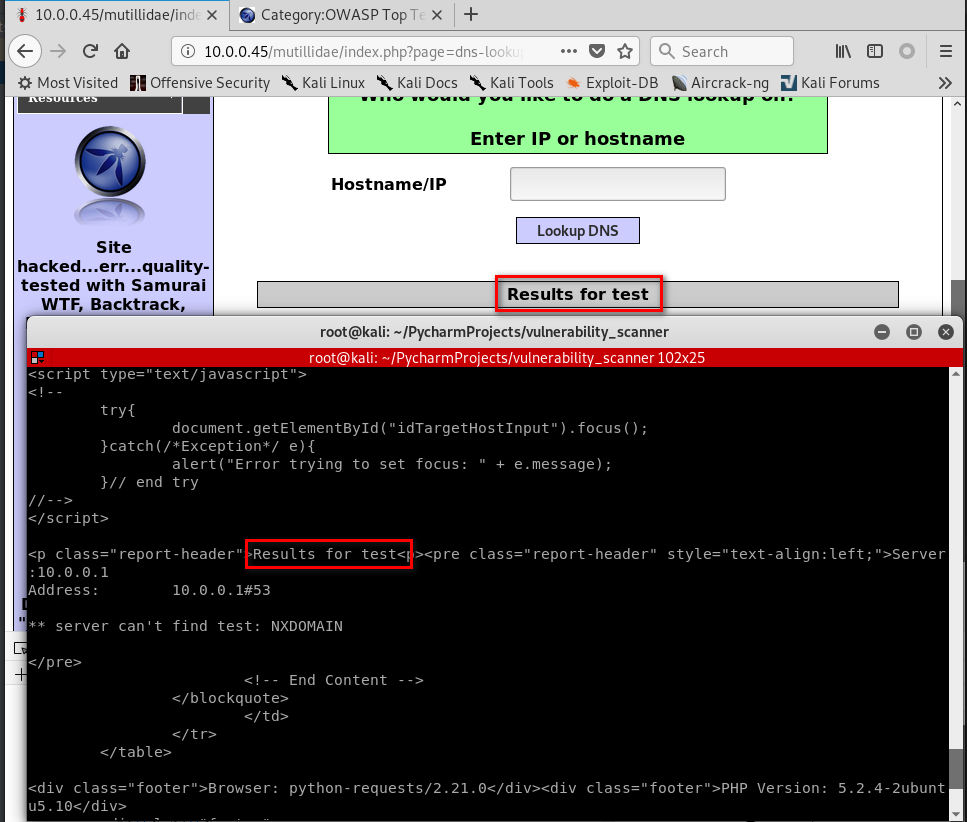
Target website:http://10.0.0.45/mutillidae/index.php?page=dns-lookup.php

#!/usr/bin/env python import requests
from bs4 import BeautifulSoup
from urllib.parse import urljoin def request(url):
try:
return requests.get(url)
except requests.exceptions.ConnectionError:
pass target_url = "http://10.0.0.45/mutillidae/index.php?page=dns-lookup.php"
response = request(target_url) parsed_html = BeautifulSoup(response.content.decode())
forms_list = parsed_html.findAll("form") for form in forms_list:
action = form.get("action")
post_url = urljoin(target_url, action)
method = form.get("method") inputs_list = form.findAll("input")
post_data = {}
for input in inputs_list:
input_name = input.get("name")
input_type = input.get("type")
input_value = input.get("value")
if input_type == "text":
input_value = "test" post_data[input_name] = input_value
result = requests.post(post_url, data=post_data)
print(result.content.decode())
Run the Python Code successfully.
Python Ethical Hacking - VULNERABILITY SCANNER(1)的更多相关文章
- Python Ethical Hacking - VULNERABILITY SCANNER(9)
Automatically Discovering Vulnerabilities Using the Vulnerability Scanner 1. Modify the run_scanner ...
- Python Ethical Hacking - VULNERABILITY SCANNER(7)
VULNERABILITY_SCANNER How to discover a vulnerability in a web application? 1. Go into every possibl ...
- Python Ethical Hacking - VULNERABILITY SCANNER(4)
Extracting & Submitting Forms Automatically Target website:http://10.0.0.45/dvwa/vulnerabilities ...
- Python Ethical Hacking - VULNERABILITY SCANNER(2)
VULNERABILITY_SCANNER How to discover a vulnerability in a web application? 1. Go into every possibl ...
- Python Ethical Hacking - VULNERABILITY SCANNER(8)
Implementing Code To Discover XSS in Parameters 1. Watch the URL of the XSS reflected page carefully ...
- Python Ethical Hacking - VULNERABILITY SCANNER(3)
Polish the Python code using sending requests in a session Class Scanner. #!/usr/bin/env python impo ...
- Python Ethical Hacking - VULNERABILITY SCANNER(6)
EXPLOITATION - XSS VULNS EXPLOITING XSS Run any javascript code. Beef framework can be used to hook ...
- Python Ethical Hacking - VULNERABILITY SCANNER(5)
EXPLOITATION - XSS VULNS XSS - CROSS SITE SCRIPTING VULNS Allow an attacker to inject javascript cod ...
- Python Ethical Hacking - BACKDOORS(8)
Cross-platform hacking All programs we wrote are pure python programs They do not rely on OS-specifi ...
随机推荐
- 利用Azure Functions和k8s构建Serverless计算平台
题记:昨晚在一个技术社区直播分享了"利用Azure Functions和k8s构建Serverless计算平台"这一话题.整个分享分为4个部分:Serverless概念的介绍.Az ...
- 查看apk安装包信息
➜ sdk aapt dump badging ~/Downloads/PermRoot8006.apk package: name='com.qihoo.permmgr' versionCode=' ...
- cb09a_c++_顺序容器的操作2-在顺序容器中添加元素_插入数据
cb09a_c++_顺序容器的操作2在顺序容器中添加元素vector不能向前插入数据,list可以用insertc.push_back(t);c.push_front(t);c.insert(p,t) ...
- Kali中密码暴力破解工具hydra的使用
前言 hydra是著名黑客组织thc的一款开源的暴力破解密码工具,功能非常强大,kali下是默认安装的,几乎支持所有协议的在线破解.密码能否破解,在于字典是否强大.本文仅从安全角度去讲解工具的使用,请 ...
- Java并发编程的本质是解决这三大问题
[本文版权归微信公众号"代码艺术"(ID:onblog)所有,若是转载请务必保留本段原创声明,违者必究.若是文章有不足之处,欢迎关注微信公众号私信与我进行交流!] 前言 并发编程的 ...
- Spring7——开发基于注解形式的spring
开发基于注解形式的spring SpringIOC容器的2种形式: (1)xml配置文件:applicationContext.xml; 存bean:<bean> 取bean: Appli ...
- Netty 源码解析(三): Netty 的 Future 和 Promise
今天是猿灯塔“365篇原创计划”第三篇. 接下来的时间灯塔君持续更新Netty系列一共九篇 Netty 源码解析(一): 开始 Netty 源码解析(二): Netty 的 Channel 当前:Ne ...
- 一行一行源码分析清楚AbstractQueuedSynchronizer
“365篇原创计划”第二十四篇. 今天呢!灯塔君跟大家讲: 一行一行源码分析清楚AbstractQueuedSynchronizer 在分析 Java 并发包 java.util.concurren ...
- css3条件判断_@supports的用法/Window.CSS.supports()的使用
为了判断浏览器是否支持css3的一些新属性样式,当不兼容该样式的时候,我们可以更优雅的降级处理.这就需要使用到css3的条件判断功能:在css中支持@supports标记.或者在js中使用CSS.su ...
- CF833 A The Meaningless Game
题干 Slastyona and her loyal dog Pushok are playing a meaningless game that is indeed very interesting ...
