Ethical Hacking - NETWORK PENETRATION TESTING(16)
ARP Poisoning - MITMf
MITMf is a framework that allows us to launch a number of MITM attacks. MITMf also starts SSLstrip automatically to bypass HTTPS/SSL.
Download and Install the MITMf tool from the following website: https://github.com/byt3bl33d3r/MITMf

Installed successfully.
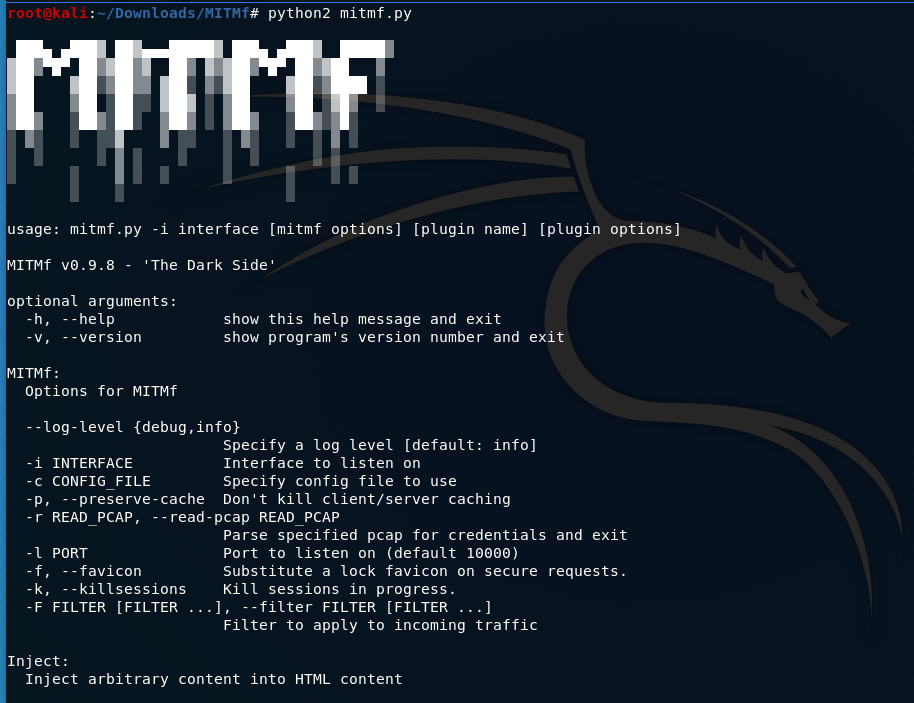
Usage:
mitmf --arp --spoof --gateway [GATEWAY IP] --targets [TARGET IPs] -i [interface]
e.g. python2 mitmf.py --arp --spoof --gateway 10.0.0.1 --target 10.0.0.210 -i eth0
echo >/proc/sys/net/ipv4/ip_forward

The MITMf is working now.

>>>My pip2 is broken. The following is the steps to fix this problem.
$ wget https://bootstrap.pypa.io/get-pip.py
$ sudo python2. get-pip.py
Ethical Hacking - NETWORK PENETRATION TESTING(16)的更多相关文章
- Ethical Hacking - NETWORK PENETRATION TESTING(15)
ARP Poisoning - arpspoof Arpspoof is a tool part of a suit called dsniff, which contains a number of ...
- Ethical Hacking - NETWORK PENETRATION TESTING(12)
Post Connection Attacks Sophisticated attacks that can be used after connecting to the target AP. Ga ...
- Ethical Hacking - NETWORK PENETRATION TESTING(22)
MITM - Wireshark WIreshark is a network protocol analyser that is designed to help network administa ...
- Ethical Hacking - NETWORK PENETRATION TESTING(14)
MITM - ARP Poisoning Theory Man In The Middle Attacks - ARP Poisoning This is one of the most danger ...
- Ethical Hacking - NETWORK PENETRATION TESTING(13)
Nmap Nmap is a network discovery tool that can be used to gather detailed information about any clie ...
- Ethical Hacking - NETWORK PENETRATION TESTING(11)
Securing your Network From the Above Attacks. Now that we know how to test the security of all known ...
- Ethical Hacking - NETWORK PENETRATION TESTING(10)
WPA Craking WPA was designed to address the issues in WEP and provide better encryption. The main is ...
- Ethical Hacking - NETWORK PENETRATION TESTING(8)
WEP Cracking Basic case Run airdump-ng to log all traffic from the target network. airodump-ng --cha ...
- Ethical Hacking - NETWORK PENETRATION TESTING(7)
Gaining Access to encrypted networks Three main encryption types: 1. WEP 2.WPA 3.WPA2 WEP Cracking W ...
随机推荐
- [置顶] linux中fork()函数详解(原创!!实例讲解)
分类: 计算机系统 linux2010-06-01 23:35 60721人阅读 评论(105) 收藏 举报 linux2010存储 一.fork入门知识 一个进程,包括代码.数据和分配给进程的资源 ...
- 505. The Maze II
原题链接:https://leetcode.com/articles/the-maze-ii/ 我的思路 在做完了第一道迷宫问题 http://www.cnblogs.com/optor/p/8533 ...
- 【解读】TCP协议
本文内容如下: 1)TCP协议概念 2)TCP头部结构和字段介绍 3)TCP流量控制 滑动窗口 4)TCP拥塞控制 慢 ...
- 操作系统识别-python、nmap
识别操作系统主要是用于操作系统漏洞的利用.不管是windows还是linux系统,在安装完毕后都会默认启动一些服务,开启一些端口. 识别目标主机的系统最简单的方法就是发送ping包,windows起始 ...
- 面试官:你刚说你喜欢研究新技术,那么请说说你对 Blazor 的了解
阅读本文大概需要 1.5 分钟. 最近在几个微信 .NET 交流群里大家讨论比较频繁的话题就是这几天自己的面试经历. 面试官:"你刚说你喜欢研究新技术,那么你对 Blazor 了解多少?&q ...
- ajax前后端交互原理(7)
7.ajax函数封装 7.1.实例引入 需求: 每秒钟请求一次服务器 获取到数据 实现: 把ajax进行封装 <!DOCTYPE html> <html> <head&g ...
- JavaScript基础-即时函数(Immediate Functions)(017)
1.即时函数的声明方法 即时函数(Immediate Functions)是一种特殊的JavaScript语法,可以使函数在定义后立即执行:(function () { alert('watch ...
- 问题: No module named _gexf 解决方法
最近在参与一个社交网络数据可视化的项目,要在后端将社交网络信息组建成网络传至前端以使其可视化.前端使用Echart显示网络,后端要通过Python的Gexf库组建网络. Gexf库安装过程为: pip ...
- Zookeeper 序列化
读完这篇文章你将会收获到 在 Zookeeper 源码项目中新建模块,使用 Jute 进行序列化和反序列化 修改 Jute 中的 buffer size 来序列化/反序列化大对象 序言 从 前面的文章 ...
- 收藏python开发各种资源官方文档
http://json.cn/ https://cn.bing.com/ https://processon.com/ https://docs.djangoproject.com/en/1.11/r ...
