Cyber Security - Palo Alto Firewall Objects Addresses, Services, and Groups(3)
LDAP Authentication and Remote Users and Groups
- Create Remote User Objects and LDAP Integration:
- samAccountName - eric.wei
- UserPrincipalName - eric.wei@pandabusiness.local
- Prerequisites:
- Microsoft Active Directory(LDAP)
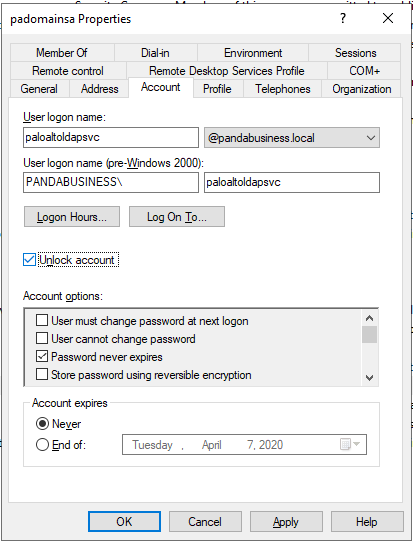
- AD service account for Palo Alto Firewall Integration
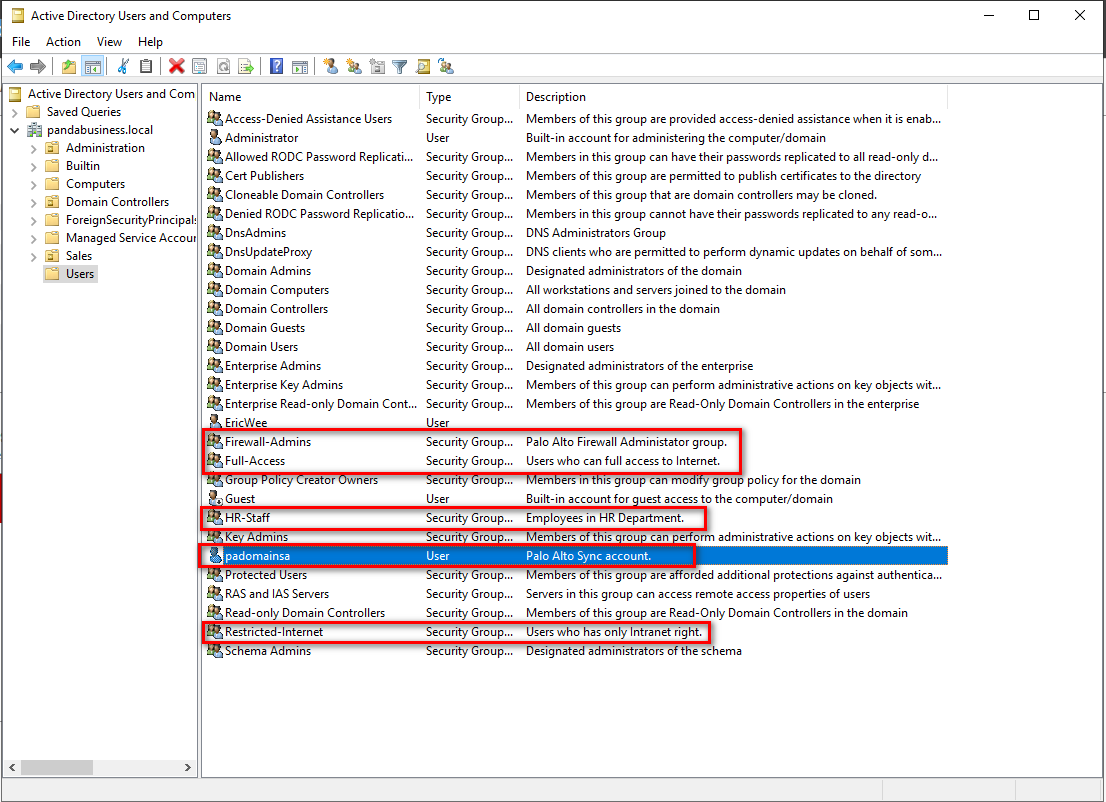
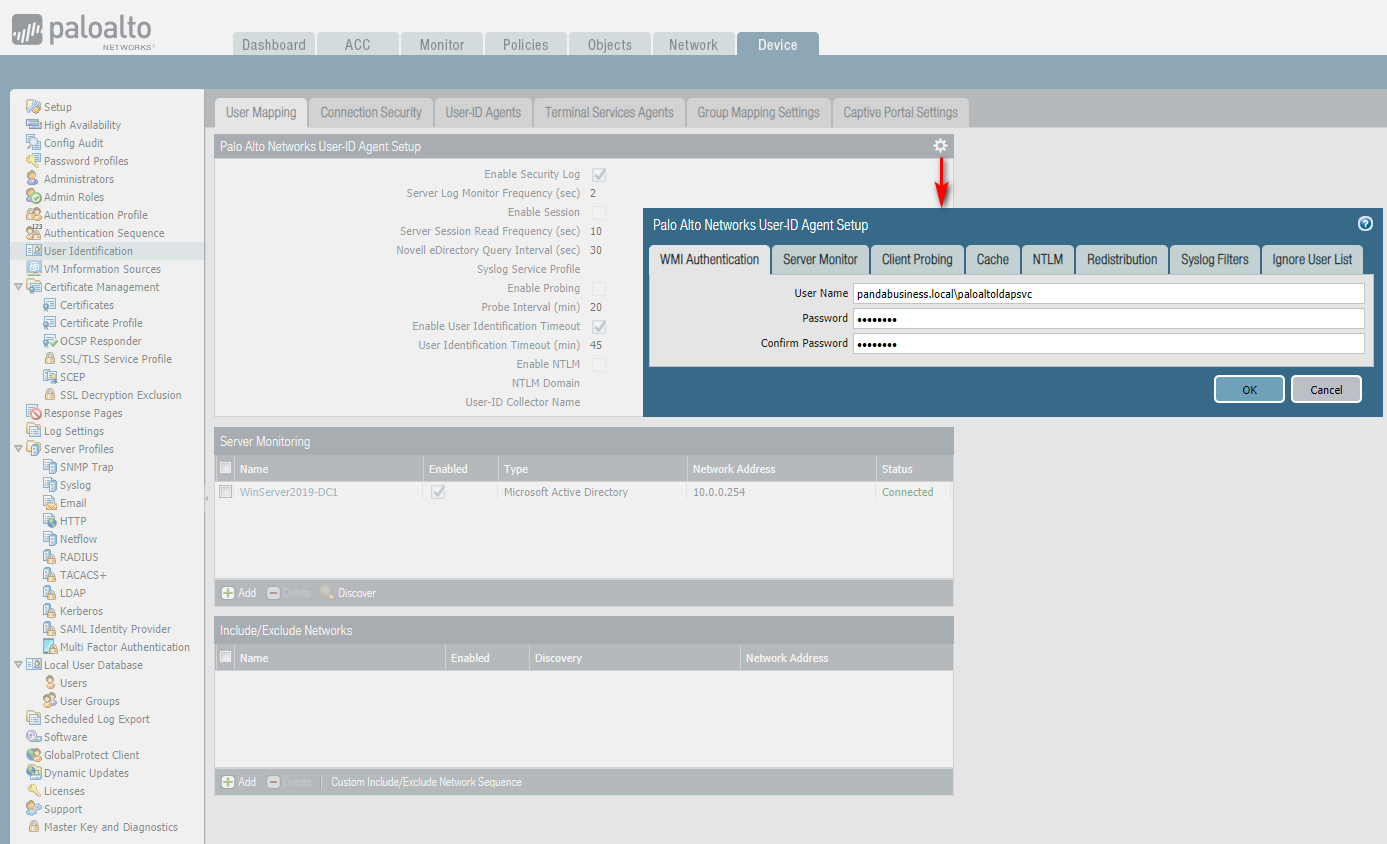
Create security groups and a function account in Users OU.
Test this account's WQL queries using WBEMTEST.
https://4sysops.com/archives/wbemtest-part-1-testing-wmi-connectivity/
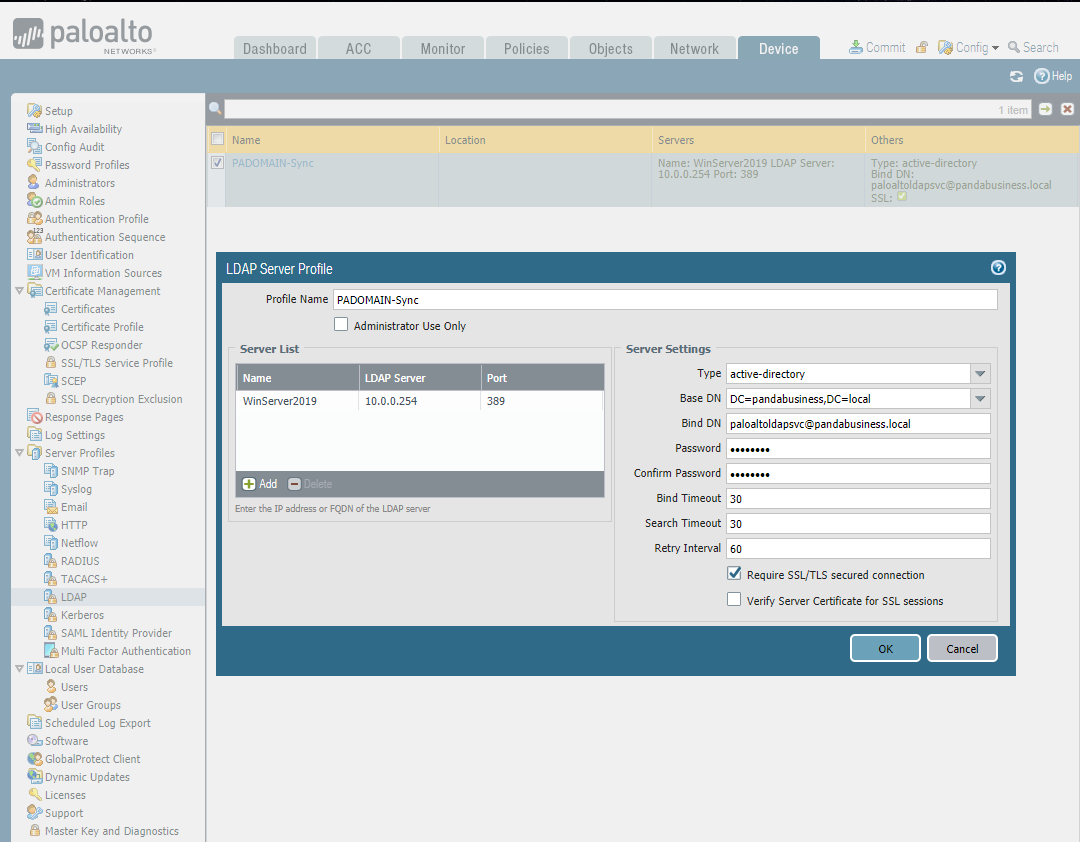
Set the LDAP Server Profile.
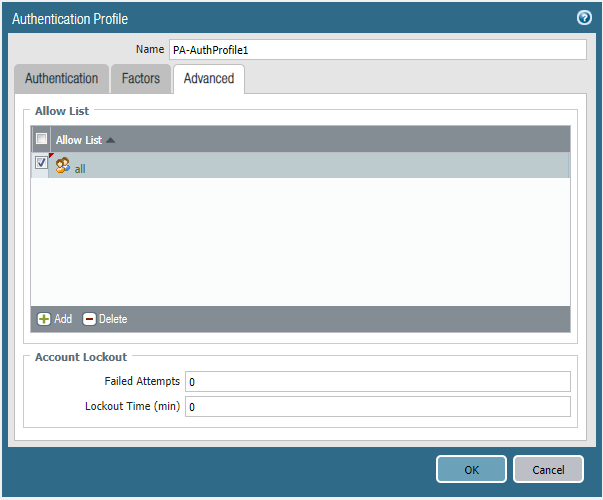
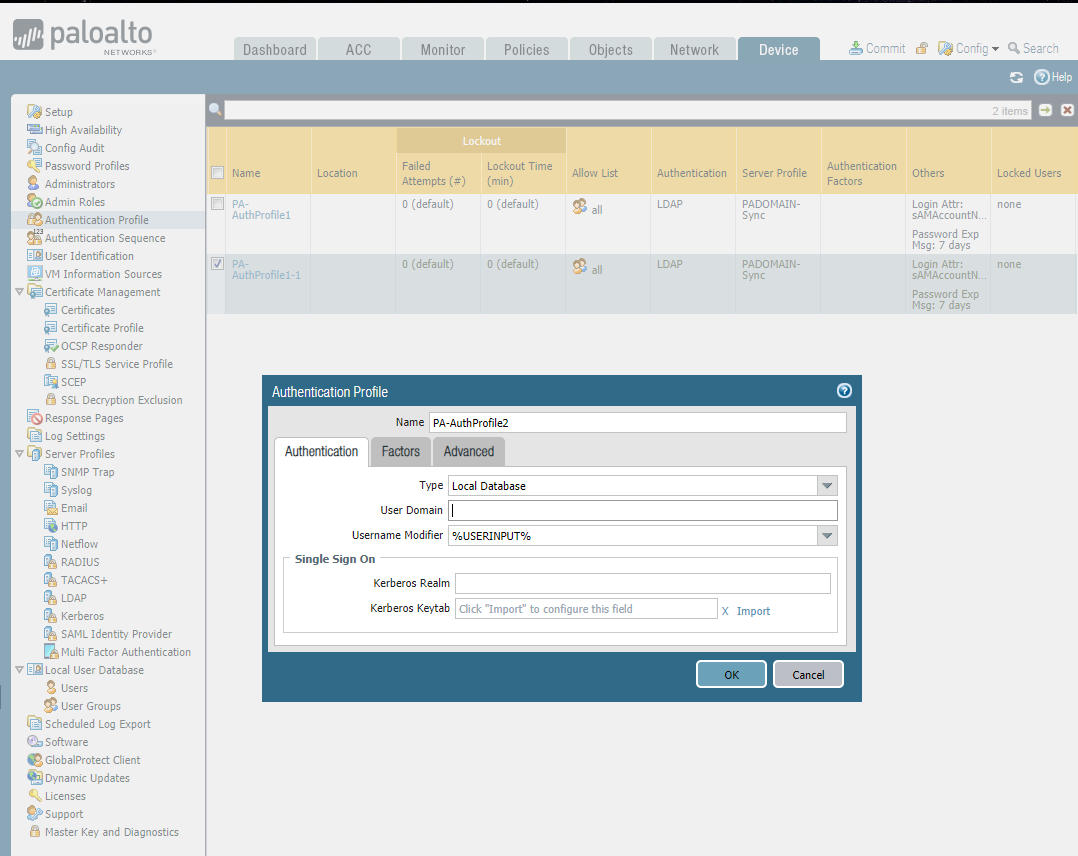
Create two Authentication Profiles.
LDAP Auth:

Local Database Auth:

Set Authentication Sequence.

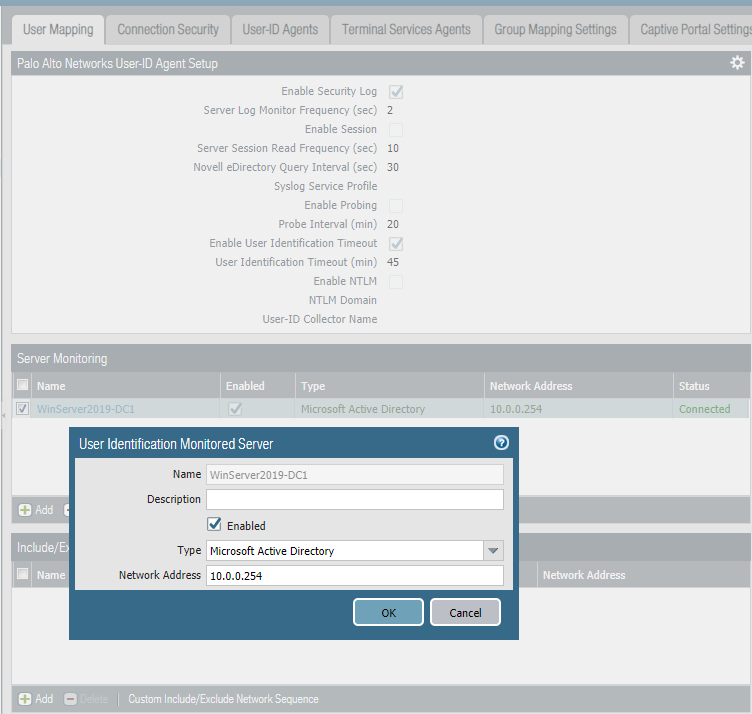
Set Server Monitoring in User Identification and commit the changes.
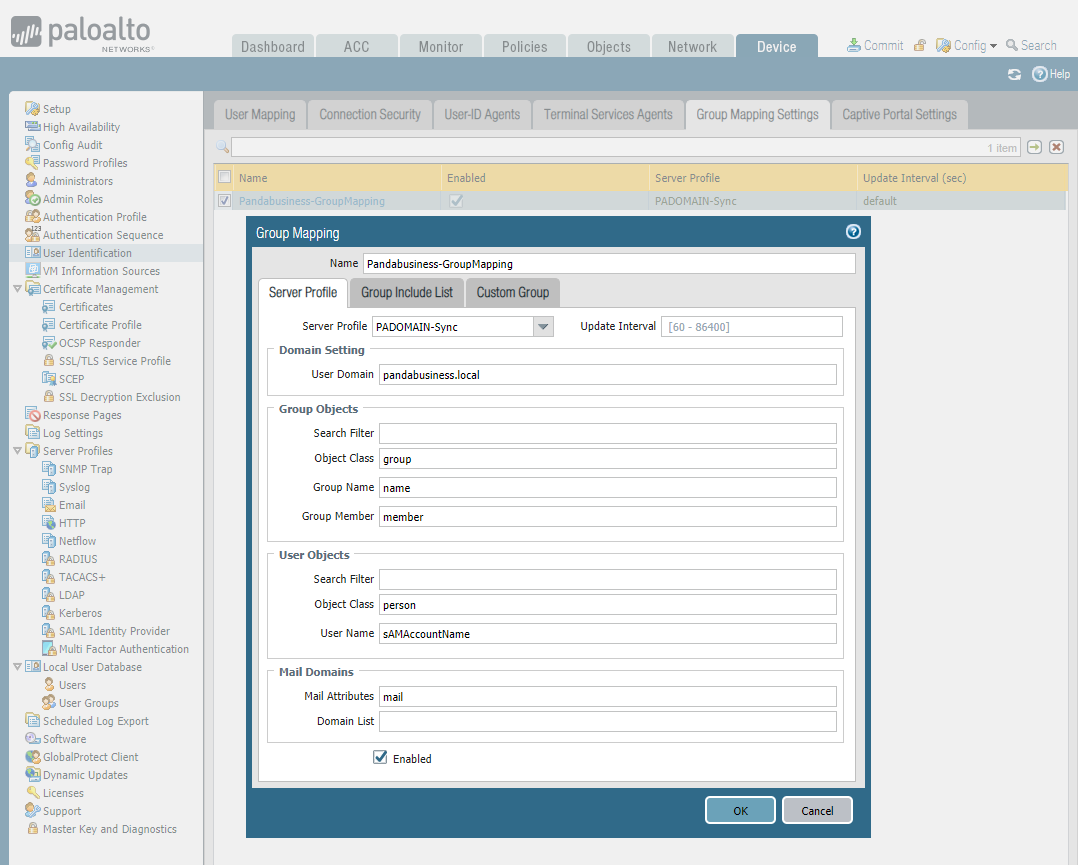
Set Group Mapping Settings.

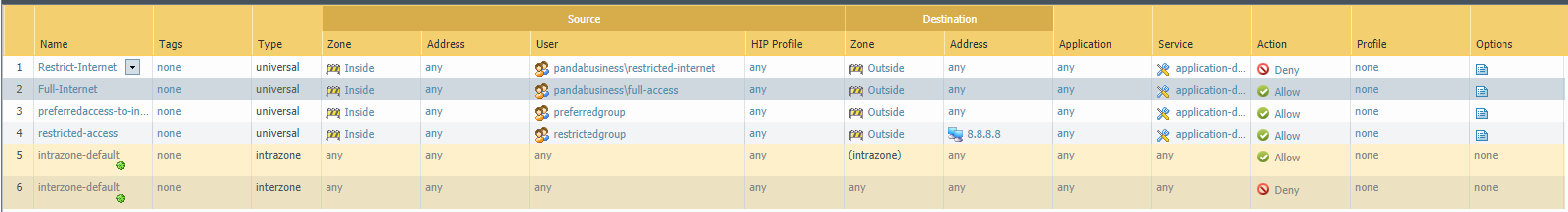
Finally set the security policies.
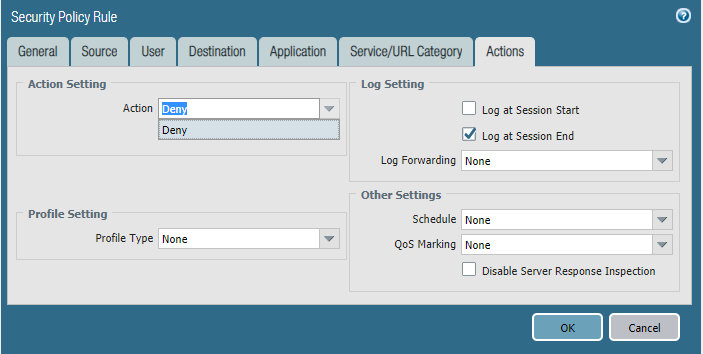
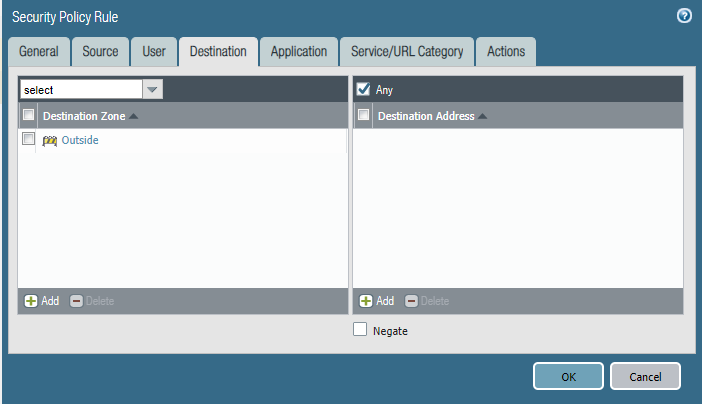
Policy 1 - Restrict-Internet

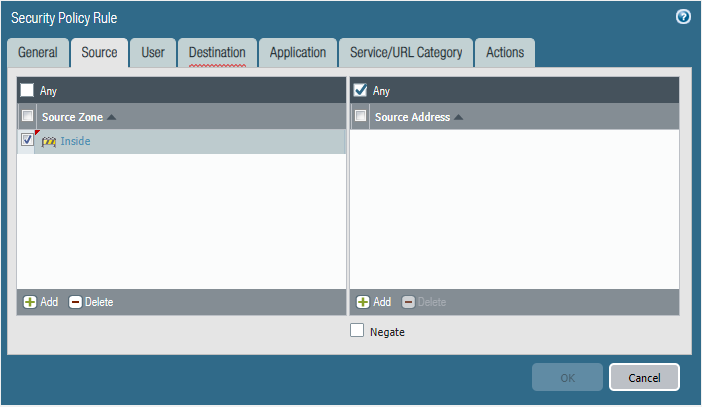

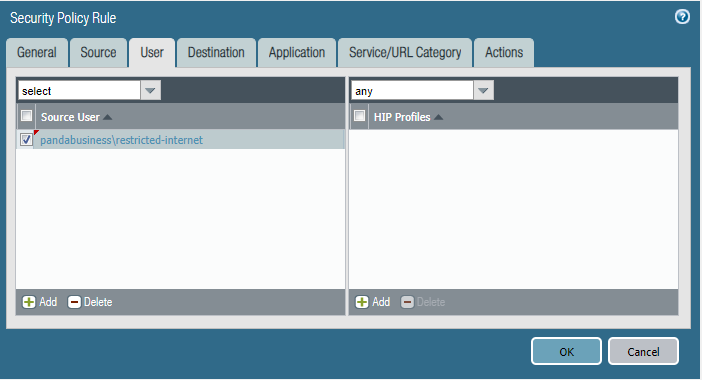
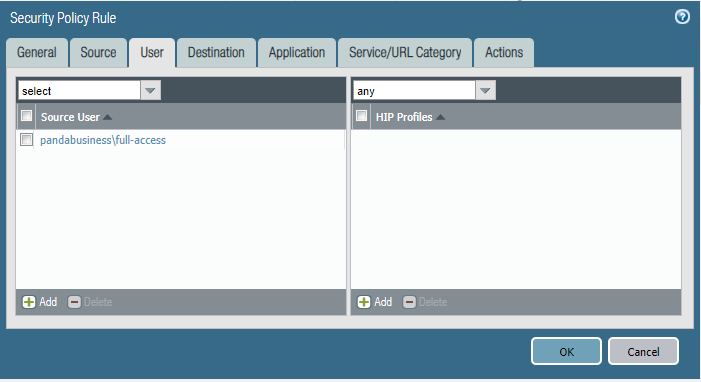
Policy 2 - Full Internet



Commit the change to take effective finally.
Cyber Security - Palo Alto Firewall Objects Addresses, Services, and Groups(3)的更多相关文章
- Cyber Security - Palo Alto Firewall Objects Addresses, Services, and Groups(1)
Address Objects and Groups Creating address objects. Organizing address objects with address groups ...
- Cyber Security - Palo Alto Firewall Objects Addresses, Services, and Groups(2)
Users Objects and Groups Creating local user objects. Creating local user groups. https://docs.paloa ...
- Cyber Security - Palo Alto Firewall Interface Types
Multiple options to integrate the Palo Alto Firewall into your: Network Layer 2 interfaces and VLAN ...
- Cyber Security - Palo Alto Firewall V-Wires
Leveraging V-Wires Bridge two physical connections and apply security Policies without influencing a ...
- Cyber Security - Palo Alto Firewall Security Zones
Firewall Security Zones Zones: The foundational aspect of every Firewall. Police network traffic Enf ...
- Cyber Security - Palo Alto Basic Introduction
Preparation of the Lab Environment: Download and Install Pan-OS from the following website https://d ...
- Cyber Security - Palo Alto Security Policies(1)
Security policies: Enforcing network traffic by configuring rules of what is allowed or denied to co ...
- Cyber Security - Palo Alto Security Policies(2)
Task 3 The SOC(Security Operation Center) monitoring team dashboard reported more 1,000 requests to ...
- Palo Alto GlobalProtect上的PreAuth RCE
0x00 前言 SSL VPN虽然可以保护企业资产免受互联网被攻击的风险影响,但如果SSL VPN本身容易受到攻击呢?它们暴露在互联网上,可以可靠并安全地连接到内网中.一旦SSL VPN服务器遭到入侵 ...
随机推荐
- 消息队列——RabbitMQ的基本使用及高级特性
文章目录 一.引言 二.基本使用 1. 简单示例 2. work queue和公平消费消息 3. 交换机 三.高级特性 1. 消息过期 2. 死信队列 3. 延迟队列 4. 优先级队列 5. 流量控制 ...
- pomelo 依赖分析
最新版本: 2.2.7 npm i pomelo 之后: ➜ haloServer npm i pomelonpm WARN deprecated node-uuid@1.4.0: Use uuid ...
- 05.DRF-Django REST framework 简介
一.明确REST接口开发的核心任务 分析一下上节的案例,可以发现,在开发REST API接口时,视图中做的最主要有三件事: 将请求的数据(如JSON格式)转换为模型类对象 操作数据库 将模型类对象转换 ...
- SLS编写规范
SLS编写规范 规范要点说明 首先,状态的执行不可回滚,执行完了就是执行完了,并不会中断回滚,其次,状态的执行,可以反复执行,也就是说一个状态文件,可以多次来进行调用. 在编写状态文件过程中,有以下几 ...
- Arthas协助排查线上skywalking不可用问题
前言 首先描述下问题的背景,博主有个习惯,每天上下班的时候看下skywalking的trace页面的error情况.但是某天突然发现生产环境skywalking页面没有任何数据了,页面也没有显示任何的 ...
- Java的前生今世
Java作为一门编程语言,自诞生以来已经流行了20多年,在学习它之前,我们有必要先了解一下它的历史,了解它是如何一步步发展到今天这个样子. 孕育 上世纪90年代,硬件领域出现了单片式计算机系统,比如电 ...
- 我的.net开发百宝箱
一.Resharper http://www.jetbrains.com/resharper/ 最强悍的VisualStudio的插件,它包括一系列丰富的,能大大增加C#和Visual Basic . ...
- HTML&CSS面试高频考点(三)
11. CSS隐藏元素的方式 /*占据空间,无法点击*/ visibility: hidden; position: relative; top: -999em; /* 不占据空间,无法点击 */ p ...
- gdi和gdi+比较
http://www.360doc.com/content/10/1013/17/1066008_60709410.shtmlhttp://www.360doc.com/content/10/1013 ...
- 补充:回答网友的问题,如何不用路径,而直接将CImage画到DC中,之后DC一起显示.
补充:回答网友的问题,如何不用路径,而直接将CImage画到DC中,之后DC一起显示.注释掉 pDC->BeginPath(); // 打开路径层 pDC->Rectangle(0,0,p ...
