Python Ethical Hacking - NETWORK_SCANNER(2)
DICTIONARIES
- Similar to lists but use key instead of an index.
LISTS
- List of values/elements, all can be stored in one variable.
Improving the Program Using a List of Dictionaries:
#!/usr/bin/env python import scapy.all as scapy def scan(ip):
arp_request = scapy.ARP(pdst=ip)
broadcast = scapy.Ether(dst="ff:ff:ff:ff:ff:ff")
arp_request_broadcast = broadcast/arp_request
answered_list = scapy.srp(arp_request_broadcast, timeout=1, verbose=False)[0] clients_list = []
for element in answered_list:
clients_dict = {"ip": element[1].psrc, "mac": element[1].hwsrc}
clients_list.append(clients_dict)
return clients_list def print_result(results_list):
print("IP\t\t\tMAC Address\n------------------------------------------")
for client in results_list:
print(client["ip"] + "\t\t" + client["mac"]) scan_result = scan("10.0.0.1/24")
print_result(scan_result)
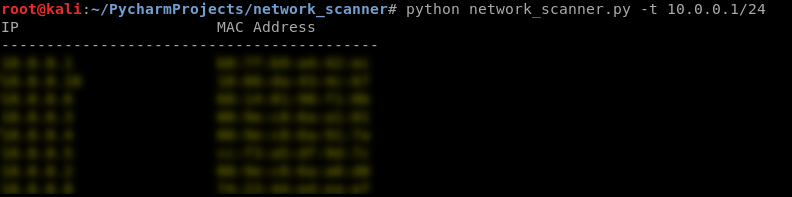
Result:

Complete the Python code:
#!/usr/bin/env python import scapy.all as scapy
import argparse def get_arguments():
parser = argparse.ArgumentParser()
parser.add_argument("-t", "--target", dest="target", help="Target IP / IP range.")
options = parser.parse_args()
return options def scan(ip):
arp_request = scapy.ARP(pdst=ip)
broadcast = scapy.Ether(dst="ff:ff:ff:ff:ff:ff")
arp_request_broadcast = broadcast/arp_request
answered_list = scapy.srp(arp_request_broadcast, timeout=1, verbose=False)[0] clients_list = []
for element in answered_list:
clients_dict = {"ip": element[1].psrc, "mac": element[1].hwsrc}
clients_list.append(clients_dict)
return clients_list def print_result(results_list):
print("IP\t\t\tMAC Address\n------------------------------------------")
for client in results_list:
print(client["ip"] + "\t\t" + client["mac"]) options = get_arguments()
scan_result = scan(options.target)
print_result(scan_result)
Python Ethical Hacking - NETWORK_SCANNER(2)的更多相关文章
- Python Ethical Hacking - NETWORK_SCANNER(1)
NETWORK_SCANNER Discover all devices on the network. Display their IP address. Display their MAC add ...
- Python Ethical Hacking - BACKDOORS(8)
Cross-platform hacking All programs we wrote are pure python programs They do not rely on OS-specifi ...
- Python Ethical Hacking - ARP Spoofing
Typical Network ARP Spoofing Why ARP Spoofing is possible: 1. Clients accept responses even if they ...
- Python Ethical Hacking - MAC Address & How to Change(3)
SIMPLE ALGORITHM Goal -> Check if MAC address was changed. Steps: 1. Execute and read ifconfig. ...
- Python Ethical Hacking - MAC Address & How to Change(2)
FUNCTIONS Set of instructions to carry out a task. Can take input, and return a result. Make the cod ...
- Python Ethical Hacking - MAC Address & How to Change(1)
MAC ADDRESS Media Access Control Permanent Physical Unique Assigned by manufacturer WHY CHANGE THE M ...
- Python Ethical Hacking - The Lab and Needed Software
The Lab and Needed Software Attacker Machine - Kali Linux https://www.kali.org/ 1. Install the softw ...
- Python Ethical Hacking - Basic Concetion
What is Hacking? Gaining unauthorized access. Hackers? 1.Black-hat Hackers 2.White-hat Hackers 3.Gre ...
- Python Ethical Hacking - VULNERABILITY SCANNER(9)
Automatically Discovering Vulnerabilities Using the Vulnerability Scanner 1. Modify the run_scanner ...
随机推荐
- 在群晖NAS上运行URLOS之后竟然能安装Discuz! Q!!
如果我们手头上有1台群晖NAS时,有没有考虑过把群晖NAS当成服务器来使用,这样会不会很有意思呢? 现在,我们终于可以尝试一番了,把群晖NAS变成一台实实在在的服务器,在上面跑各种运行环境!其实很简单 ...
- gitbub.com设置协作者提交代码步骤
1. 邀请协作者 点击settings 2. 等待协作者接受邀请 关注注册邮箱 3. 协作者生成公钥 一路回车即可 ssh-keygen -t rsa -b 4096 -C "公众号:九点半 ...
- 用VMware克隆CentOS 6.5如何进行网络设置
我们使用虚拟机的克隆工具克隆出了一个电脑,电脑连接采用nat方式 111电脑对于的ip地址设置如下 [root@localhost ~]# cd /etc/sysconfig/network-scri ...
- 删库吧,Bug浪——我们在同一家摸鱼的公司
那些口口声声, Bug越来越难写人的,应该盯着你们: 像我一样,我盯着你们,满眼恨意. IT积攒了几十年的漏洞, 所有的死机.溢出.404和超时, 像是专门为你们准备的礼物. 圈复杂度.魔鬼变量.内存 ...
- 【Vim命令】
命令 操作 :set nu 显示行号 i 编辑模式 :wq 修改并退出 :%s/a/b 把所有的a替换成b
- js语法基础入门(1)
1.基础入门 1.1.hello world 1.1.1.JavaScript是什么? JavaScript是一门跨平台.面向对象的轻量级脚本语言,在web开发中被广泛应用 1.1.2.JavaScr ...
- Security 10:权限管理
SQL Server 用于管理权限的TSQL命令有:GRANT用于授予权限,REVOKE 用于移除授予的权限,而DENY用于防止安全主体通过GRANT获得权限.但是,SQL Server的权限管理不是 ...
- 洛谷 P1314 【聪明的质监员】
二分 思路: 这道题思路还是蛮好想的,一开始想的是暴力枚举w,然后再仔细一看,w增长时,y肯定减小,那么思路出来了: 二分 但是在时二分时,分得是左右端点lr,做错了 求出w的上下界,然后二分 只二分 ...
- 四. sql上线平台
一.inception安装使用 inception是一个集审核.执行.备份及生成回滚语句于一身的MySQL自动化运维工具 [root@CentOS ~]# [root@CentOS ~]# wget ...
- css hack原理及常用hack
原理:利用不同浏览器对CSS的支持和解析结果不一样编写针对特定浏览器样式.常见的hack有1)属性hack.2)选择器hack.3)IE条件注释 IE条件注释:适用于[IE5, IE9]常见格式如下 ...
