Ethical Hacking - NETWORK PENETRATION TESTING(4)
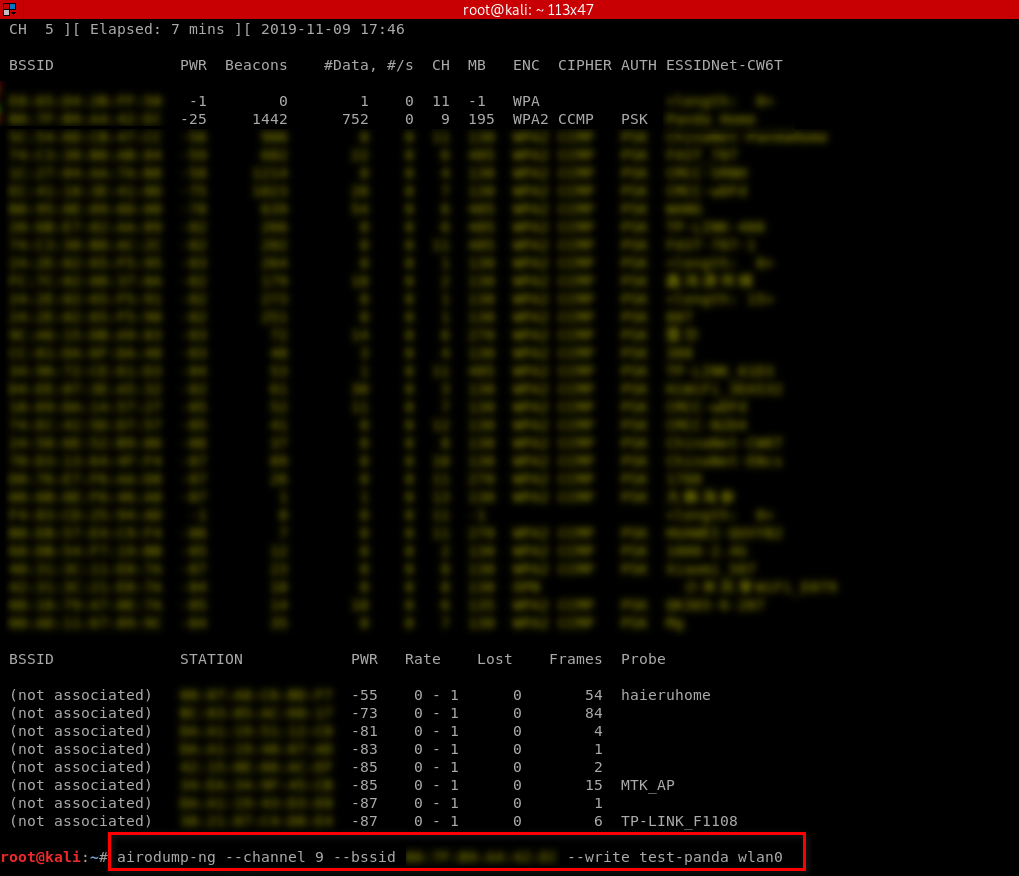
Targeted packet sniffing
airodump-ng --channel[channel] --bssid[bssid] --write[file-name][interface]
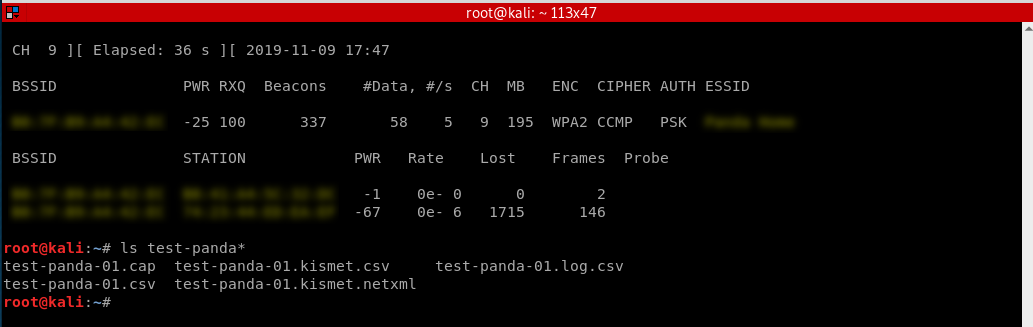
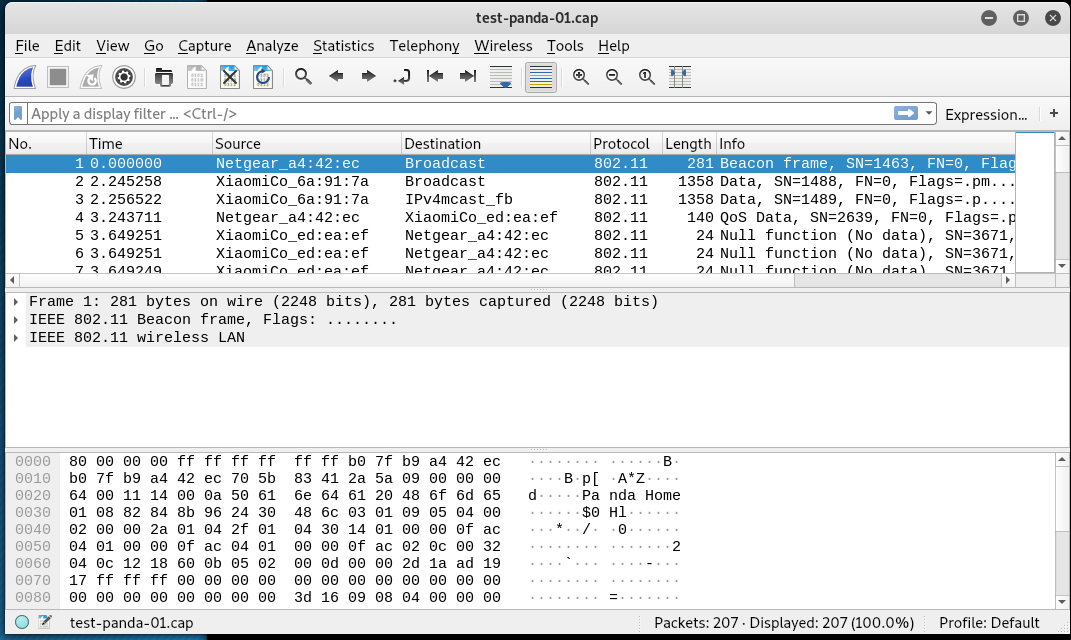
Now all the data will be stored in the file name specified after the -write option. We can analyze this data using Wireshark. The only problem is that the collected data will not be much of use if the target network uses encryption.
Monitor my home Wi-Fi as a sample.
Stop the monitor and find the packets.
Open the captured packets through WireShark and analyze.
Ethical Hacking - NETWORK PENETRATION TESTING(4)的更多相关文章
- Ethical Hacking - NETWORK PENETRATION TESTING(15)
ARP Poisoning - arpspoof Arpspoof is a tool part of a suit called dsniff, which contains a number of ...
- Ethical Hacking - NETWORK PENETRATION TESTING(22)
MITM - Wireshark WIreshark is a network protocol analyser that is designed to help network administa ...
- Ethical Hacking - NETWORK PENETRATION TESTING(14)
MITM - ARP Poisoning Theory Man In The Middle Attacks - ARP Poisoning This is one of the most danger ...
- Ethical Hacking - NETWORK PENETRATION TESTING(13)
Nmap Nmap is a network discovery tool that can be used to gather detailed information about any clie ...
- Ethical Hacking - NETWORK PENETRATION TESTING(12)
Post Connection Attacks Sophisticated attacks that can be used after connecting to the target AP. Ga ...
- Ethical Hacking - NETWORK PENETRATION TESTING(11)
Securing your Network From the Above Attacks. Now that we know how to test the security of all known ...
- Ethical Hacking - NETWORK PENETRATION TESTING(10)
WPA Craking WPA was designed to address the issues in WEP and provide better encryption. The main is ...
- Ethical Hacking - NETWORK PENETRATION TESTING(8)
WEP Cracking Basic case Run airdump-ng to log all traffic from the target network. airodump-ng --cha ...
- Ethical Hacking - NETWORK PENETRATION TESTING(7)
Gaining Access to encrypted networks Three main encryption types: 1. WEP 2.WPA 3.WPA2 WEP Cracking W ...
- Ethical Hacking - NETWORK PENETRATION TESTING(5)
Deauthentication Attacks Theory This attack is used to disconnect any device from any network within ...
随机推荐
- 基于node的前端项目编译时内存溢出问题
解决方法: CALL_AND_RETRY_LAST Allocation failed - JavaScript heap out of memory JavaScript堆内存不足,这里说的 Jav ...
- Mysql表结构转成Oracle
Navicat数据库连接工具
- 容器技术之Docker Machine
前文我们聊了下docker容器的资源限制,回顾请参考https://www.cnblogs.com/qiuhom-1874/p/13138725.html:今天我们来聊一聊docker machine ...
- CentOS7 开机进入emergency mode
今天突然操作了一下磁盘挂载,然后系统启动之后,就直接进入emergency模式了,然后只能输入密码进行救援,截图如下: 突然想了一下最近的一次操作,是因为要挂在镜像,然后每次开机都要挂载一次,觉得比较 ...
- Shiro简单加密服务
编码/加密 在涉及到密码存储问题上,应该加密 / 生成密码摘要存储,而不是存储明文密码.比如之前的 600w csdn 账号泄露对用户可能造成很大损失,因此应加密 / 生成不可逆的摘要方式存储. Sh ...
- java面试基础必备
一.Java基础 1. String类为什么是final的. 2. HashMap的源码,实现原理,底层结构. 3. 说说你知道的几个Java集合类:list.set.queue.map实现类咯... ...
- 慕课网--java权限管理系统
http://coding.imooc.com/class/evaluation/149.html
- ubuntu镜像源切换
换源准备: 换源之前明确使用平台,X86架构.ARM架构的源,ubuntu18.04和unbuntu16.04等源均不同,切忌病急乱投医,看到一个源复制过来添加后没用. 分析一条源: deb http ...
- git和github入门指南(4)
4.分支管理 4.1.什么是分支? 分支可以简单的理解为分叉,在主干上长出一条枝干出来,主干分支通常叫做master,在主分支上可以开很多分支出来,不同的人在不同的分支上做开发,最后合并到主分支,这样 ...
- 6.30集训模拟赛4(炸裂的一天qwq)
T1浇水: 题目描述 在一条长n米,宽m米米的长方形草地上放置着k个喷水装置.假设长方形草地的坐标范围为[ 0 , 0 ] ~ [ n , m ],那么第 i 个喷水装置的位置为(ai,m/2),也就 ...
