Ethical Hacking - Web Penetration Testing(7)
VULNS MITIGATION
1. File Upload Vulns - Only allow safe files to be updated.
2. Code Execution Vulns:
- Don't use dangerous functions.
- Filter use input before execution.
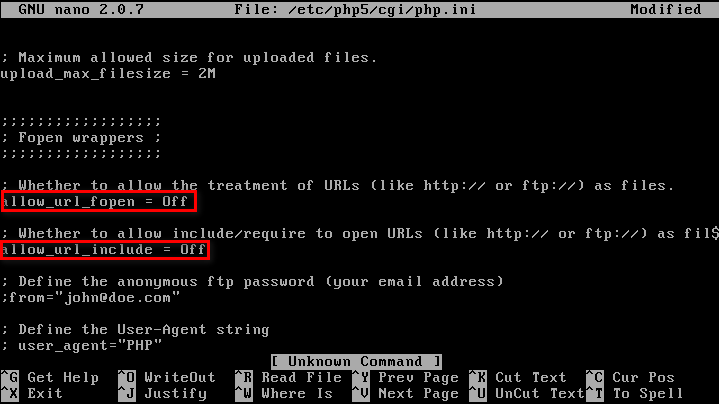
3. File inclusion:
- Disable allow_url_fopen & allow_url_include.
- Use static file inclusion.
Suggest using Hard Code Style, not using any variables, which is much more secure.
index.php?page=news.php index.php
code:
include($_GET('page')); index.php
code:
include('page.php');
Ethical Hacking - Web Penetration Testing(7)的更多相关文章
- Ethical Hacking - Web Penetration Testing(13)
OWASP ZAP(ZED ATTACK PROXY) Automatically find vulnerabilities in web applications. Free and easy to ...
- Ethical Hacking - Web Penetration Testing(8)
SQL INJECTION WHAT IS SQL? Most websites use a database to store data. Most data stored in it(userna ...
- Ethical Hacking - Web Penetration Testing(10)
SQL INJECTION SQLMAP Tool designed to exploit SQL injections. Works with many DB types, MySQL, MSSQL ...
- Ethical Hacking - Web Penetration Testing(6)
REMOTE FILE INCLUSION Similar to local file inclusion. But allows an attacker to read ANY file from ...
- Ethical Hacking - Web Penetration Testing(1)
How to hack a website? An application installed on a computer. ->web application pen-testing A co ...
- Python Ethical Hacking - WEB PENETRATION TESTING(1)
WHAT IS A WEBSITE Computer with OS and some servers. Apache, MySQL ...etc. Cotains web application. ...
- Python Ethical Hacking - WEB PENETRATION TESTING(2)
CRAWING DIRECTORIES Directories/folders inside the web root. Can contain files or other directories ...
- Ethical Hacking - Web Penetration Testing(12)
XSS VULNS XSS - CROSS SITE SCRIPTING VULNS Allow an attacker to inject javascript code into the page ...
- Ethical Hacking - Web Penetration Testing(11)
SQL INJECTION Preventing SQLi Filters can be bypassed. Use a blacklist of commands? Still can be byp ...
- Ethical Hacking - Web Penetration Testing(9)
SQL INJECTION Discovering SQLi in GET Inject by browser URL. Selecting Data From Database Change the ...
随机推荐
- Java并发编程的艺术(一、二章) ——学习笔记
第一章 并发编程的挑战 需要了解的一些概念 转自 https://blog.csdn.net/TzBugs/article/details/80921351 (1) 同步VS异步 同步和异步通常用来 ...
- cc40a_demo_Cpp_智能指针c++_txwtech
//40_21days_Cpp_智能指针c++_cc40a_demo.cpp_txwtech //智能指针.auto_ptr类//*常规指针-容易产生内存泄漏,内存被占满,程序就死机,或者系统死机// ...
- 机器学习——打开集成方法的大门,手把手带你实现AdaBoost模型
本文始发于个人公众号:TechFlow,原创不易,求个关注 今天是机器学习专题的第25篇文章,我们一起来聊聊AdaBoost. 我们目前为止已经学过了好几个模型,光决策树的生成算法就有三种.但是我们每 ...
- 01 . ELK Stack简介原理及部署应用
简介 ELK并不是一款软件,是一整套解决方案,是由ElasticSearch,Logstash和Kibana三个开源工具组成:通常是配合使用,而且先后归于Elastic.co公司名下,简称ELK协议栈 ...
- 采用Socket实现UDP
------------恢复内容开始------------ 1.1采用Socket实现UDP1.1.1简介 Socket实现UDP的基本步骤如下: (1)创建一个Socket对象 Socket my ...
- 010.OpenShift综合实验及应用
实验一 安装OpenShift 1.1 前置准备 [student@workstation ~]$ lab review-install setup 1.2 配置规划 OpenShift集群有三个节点 ...
- 大型ECShop安装搬家升级错误问题最全攻略
[引子] 最近将ECShop框架网站从租用服务器搬家至阿里云,虽然模块及功能上已经被修改的面目全非了,但基础部分还在. 在这个过程中遇到了很多的WARNING与ERROR,解决方案如下. [环境] 服 ...
- BERT的前世今生
Transformer Transformer来自论文: All Attention Is You Need 别人的总结资源: 谷歌官方AI博客: Transformer: A Novel Neura ...
- 使用spring-test时报错
java.lang.NoClassDefFoundError: org/springframework/core/annotation/MergedAnnotations$SearchStrategy ...
- maven跳过测试打包
1.在执行run as时候加上参数: clean install compile -Dmaven.test.skip=true 2.在pom文件中添加如下: <plugins> < ...
