OSCP Learning Notes - Post Exploitation(3)
Post-Exploit Password Attacks
1. Crack using the tool - john (Too slow in real world)
Locate the rockyou file.

john --wordlist=/usr/share/wordlists/rockyou.txt windows
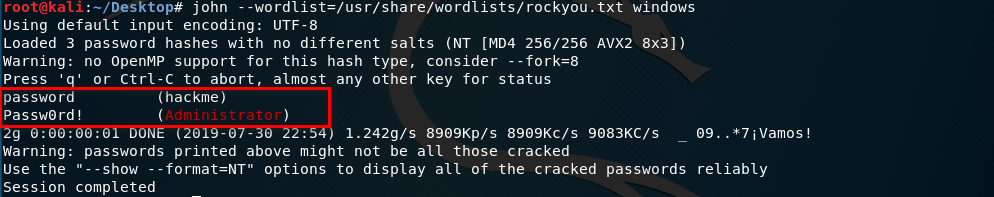
john --show windows

Conbine the files and save as unshadow.
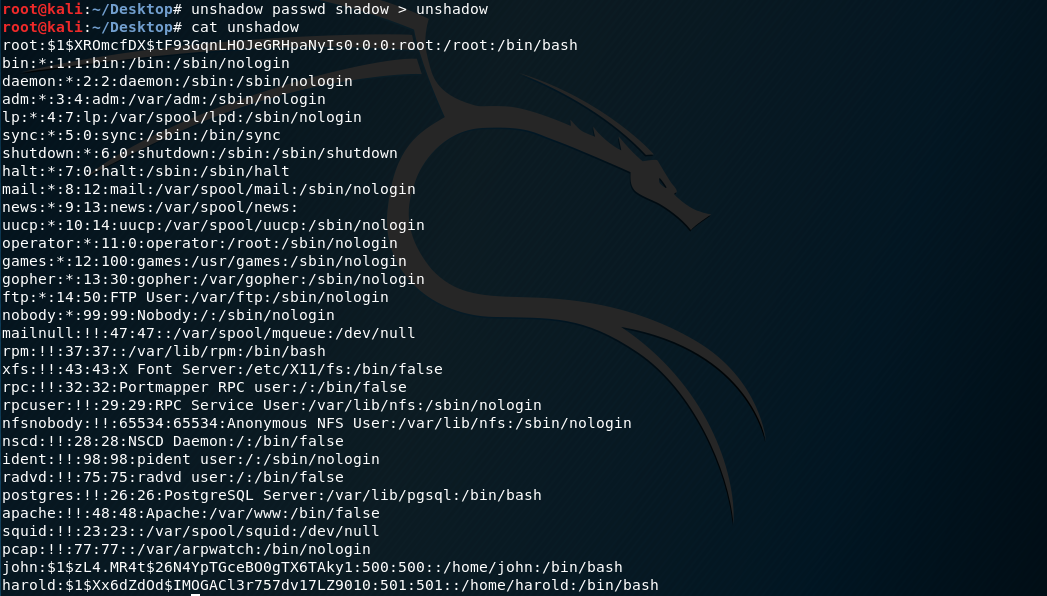
john --rules --wordlist=/usr/share/wordlists/rockyou.txt unshadow

2.Using Hash craker on the Internet. (Suggested)
8846F7EAEE8FB117AD06BDD830B7586C

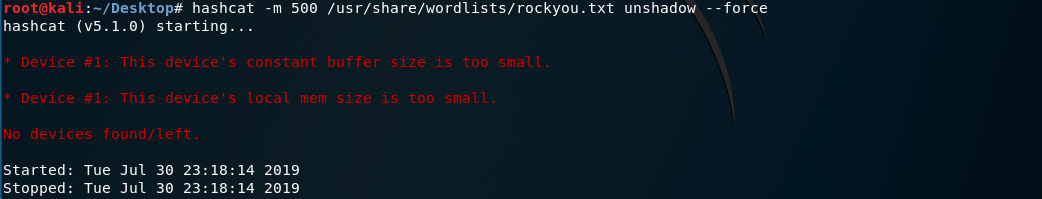
3. Use the tool hashcat
On Kali Linux.(Too slow locally)
hashcat -m /usr/share/wordlists/rockyou.txt unshadow --force
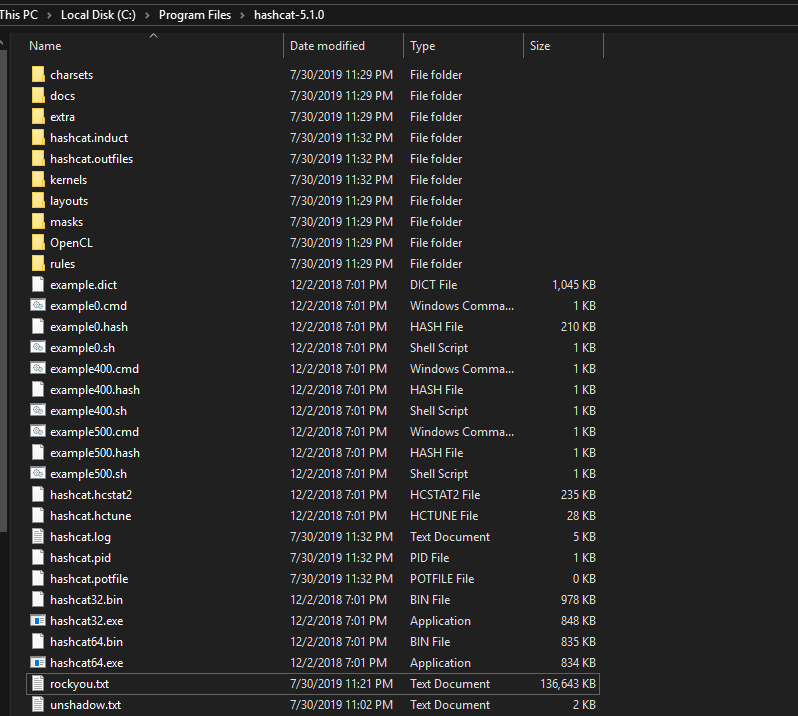
On Windows
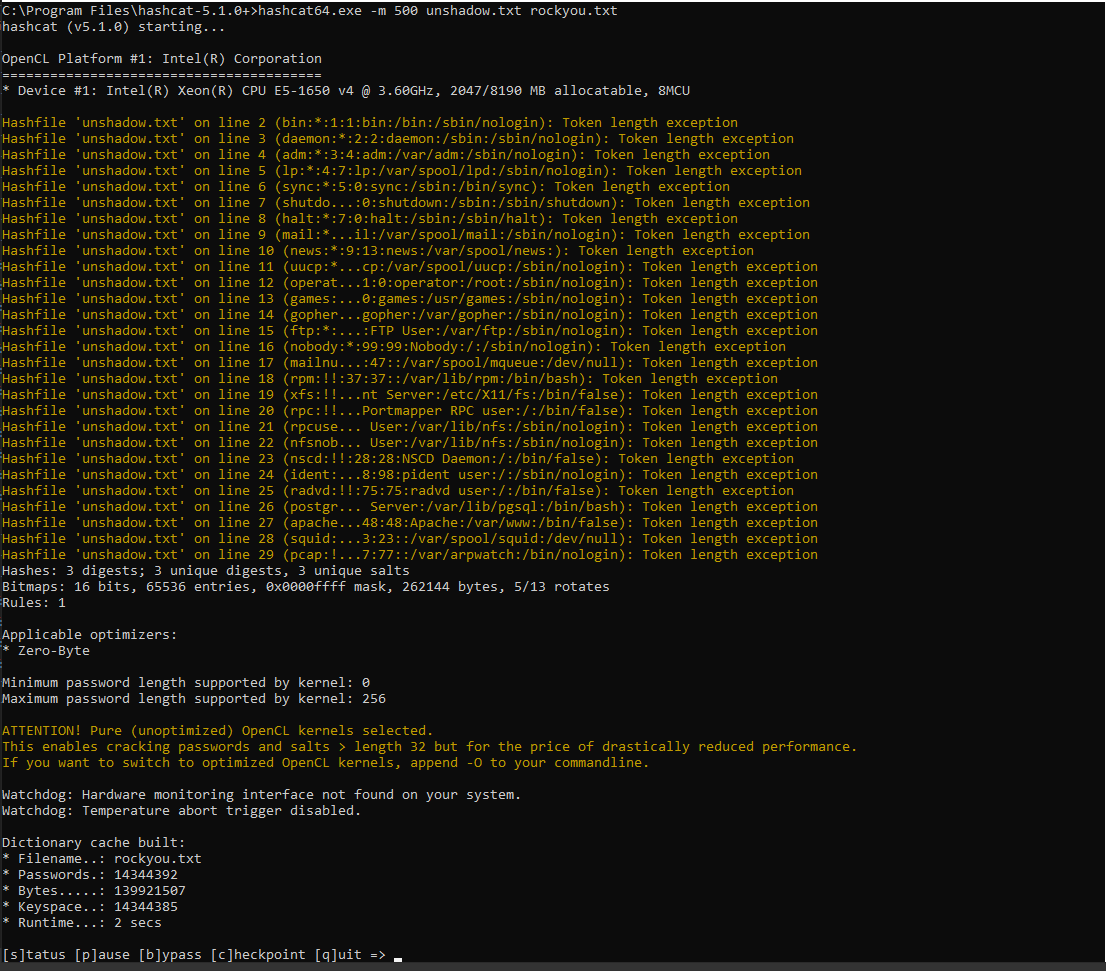
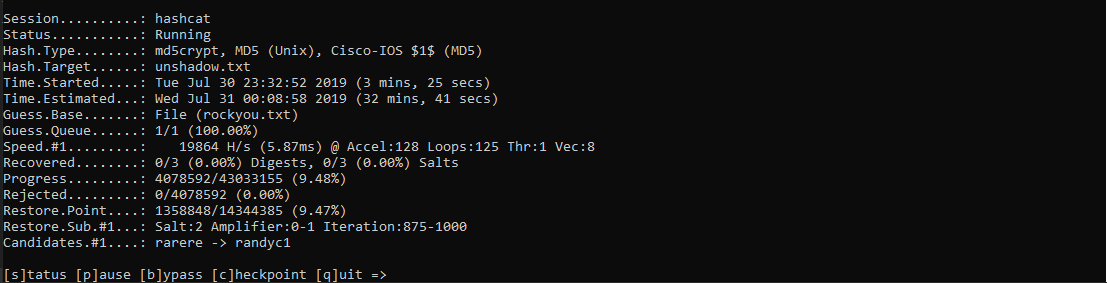
hashcat64.exe -m 500 unshadow.txt rockyou.txt
Hash Craker Websites:
Tips: If it is hard to crack the password, do not waste time on it. Just skip it and find another way.
OSCP Learning Notes - Post Exploitation(3)的更多相关文章
- OSCP Learning Notes - Post Exploitation(2)
Windows Post Exploitation Target Server: IE8-Win 7 VM 1. Download and upload the fgdump, PwDump7, wc ...
- OSCP Learning Notes - Post Exploitation(1)
Linux Post Exploitation Target Sever: Kioptrix Level 1 1. Search the payloads types. msfvenom -l pay ...
- OSCP Learning Notes - Post Exploitation(4)
Pivoting 1. Edit the virtual network settings of the Vmware. 2. Set the Network Adapter(s) of Kali L ...
- OSCP Learning Notes - WebApp Exploitation(5)
Remote File Inclusion[RFI] Prepare: Download the DVWA from the following website and deploy it on yo ...
- OSCP Learning Notes - WebApp Exploitation(4)
Local File Inclusion[LFI] Target Pentester Lab: Download from the following website: https://www.vul ...
- OSCP Learning Notes - WebApp Exploitation(3)
SQL Injection[SQLi] Refrence: SQL Injection Authentication Bypass Cheat Sheet https://pentestlab.blo ...
- OSCP Learning Notes - WebApp Exploitation(2)
Cross-Site Scripting(XSS) 1. Using the tool - netdiscover to find the IP of target server. netdiscov ...
- OSCP Learning Notes - WebApp Exploitation(1)
Installing XSS&MySQL FILE Download the Pentester Lab: XSS and MySQL FILE from the following webs ...
- OSCP Learning Notes - Overview
Prerequisites: Knowledge of scripting languages(Bash/Pyhon) Understanding of basic networking concep ...
随机推荐
- WeChair项目Alpha冲刺(8/10)
团队项目进行情况 1.昨日进展 Alpha冲刺第八天 昨日进展: 前端:安排页面美化,设计实名认证 后端:用户信息通过dao层存储数据库 数据库:修改数据表属性,与后端部署数据库交互 2.今日安 ...
- c#,pagerank算法实现一
PageRank让链接来"投票" 一个页面的“得票数”由所有链向它的页面的重要性来决定,到一个页面的超链接相当于对该页投一票.一个页面的PageRank是由所有链向它的页面(“链入 ...
- Docker Dockerfile 指令详解与实战案例
Dockerfile介绍及常用指令,包括FROM,RUN,还提及了 COPY,ADD,EXPOSE,WORKDIR等,其实 Dockerfile 功能很强大,它提供了十多个指令. Dockerfile ...
- 慕课网--java权限管理系统
http://coding.imooc.com/class/evaluation/149.html
- phpstorm设置xdebug调试
phpstorm设置xdebug调试# wamp开发环境安装完成以后,打开网页,输入 :localhost 检测xdebug是否开启 3.若xdebug已开启,请找到你wamp或者phpstudy的安 ...
- 分词搜索 sphinx+php+mysql
sphinx3.1.1的安装与使用 下载sphinx3.1.1 wget http://sphinxsearch.com/files/sphinx-3.1.1-612d99f-linux-amd64. ...
- Java 多线程基础(十一)线程优先级和守护线程
Java 多线程基础(十一)线程优先级和守护线程 一.线程优先级 Java 提供了一个线程调度器来监控程序启动后进去就绪状态的所有线程.线程调度器通过线程的优先级来决定调度哪些线程执行.一般来说,Ja ...
- Riccati方程迭代法求解
根据上述迭代法求解P,P为Riccati方程的解,然而用LQR需要计算K,再将K算出. (迭代过程中 ,我们可以将此算法和dlqr函数求解的参数进行对比,当误差小于我们设置的允许误差我们就可以把此算法 ...
- .NET Core下开源任务调度框架Hangfire
今天无意中发现了一个很好用的任务调度框架.Hangfire作为一款高人气且容易上手的分布式后台执行服务,支持多种数据库.在 .net core的环境中,由Core自带的DI管理着生命周期. 相较于qu ...
- Centos 6.4 安装KSnapshot 和gimp截图工具
一. # wget http://www.ibiblio.org/pub/Linux/X11/xutils/ksnapshot-0.2.7.tar.gz # tar -zxvf ksnapshot-0 ...
