Ethical Hacking - Web Penetration Testing(2)
INFORMATION GATHERING
- IP address.
- Domain name Info.
- Technologies used.
- Other websites on the same server.
- DNS records.
- Unlisted files, sub-domains, directories.
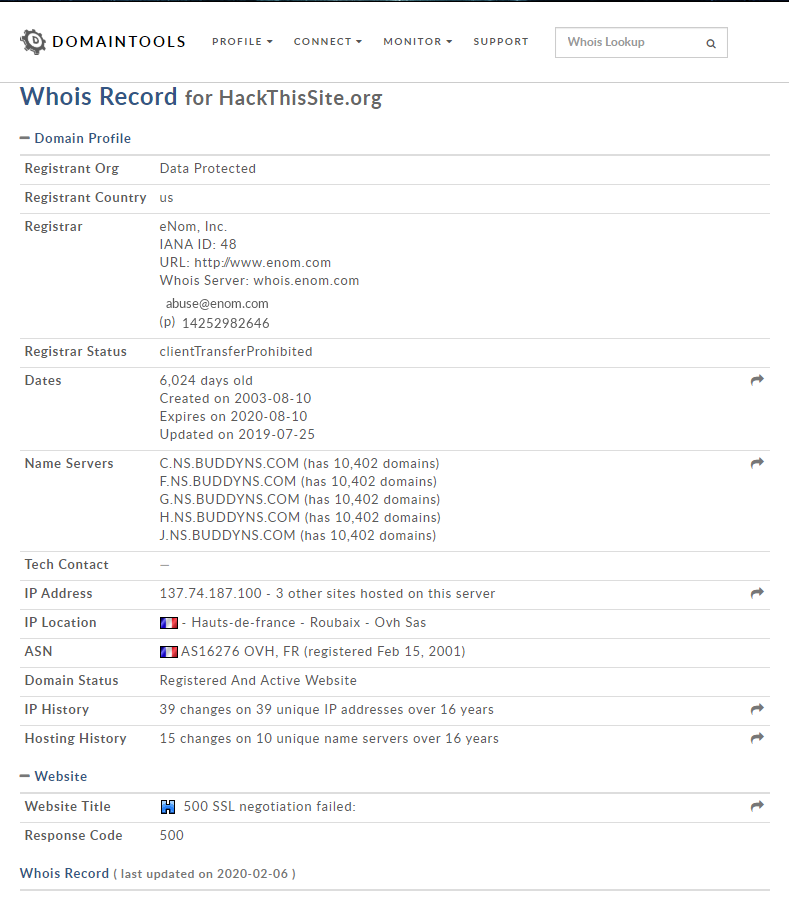
1. Whois Lookup - Find info about the owner of the target. ()
-> http://whois.domaintools.com/ https://www.whois.net/ etc.
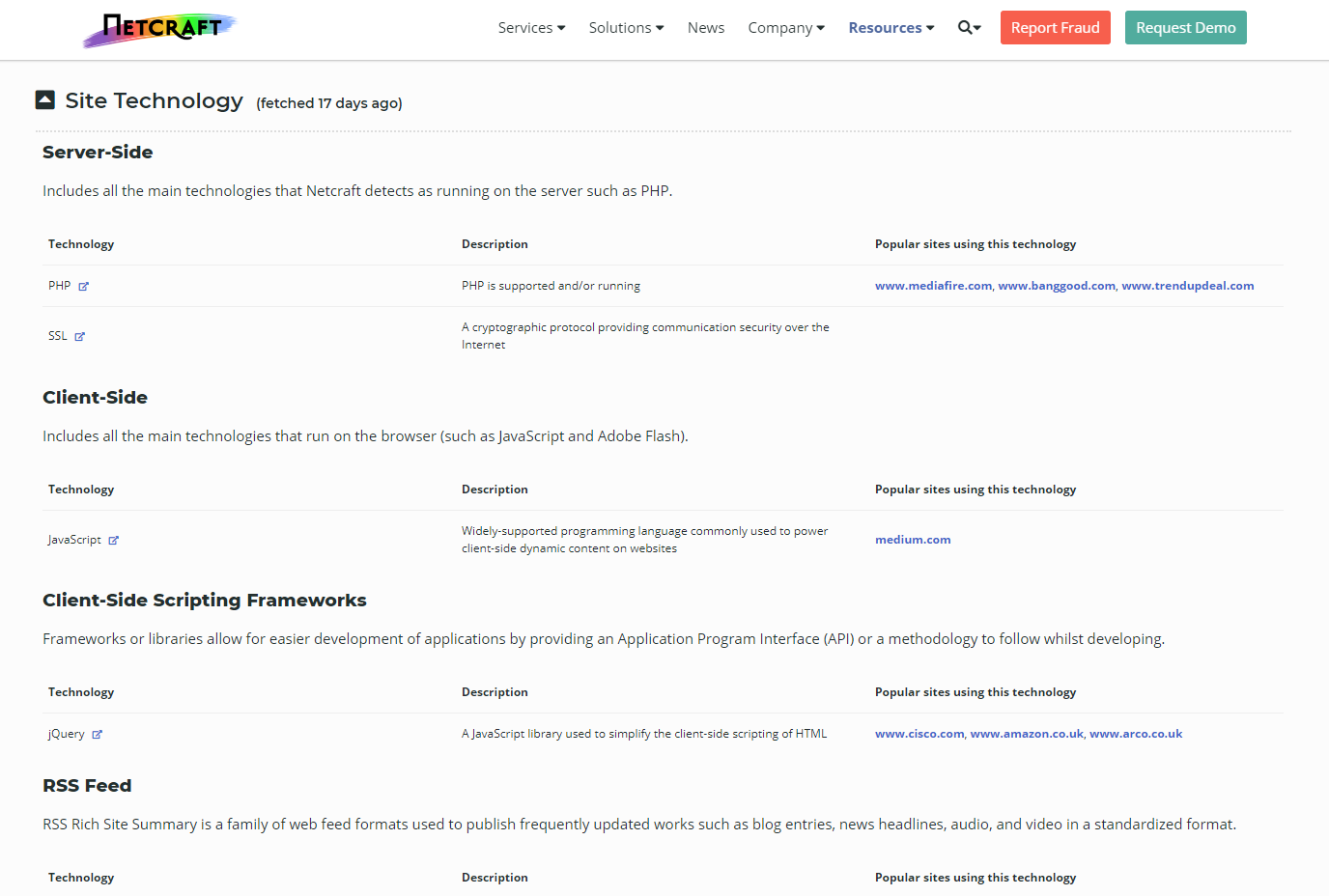
2. Netcraft Site Report - Shows technologies used on the target.
-> http://toolbar.netcraft.com/site_report
Such as :https://sitereport.netcraft.com/?url=https%3A%2F%2Fwww.hackthissite.org%2F
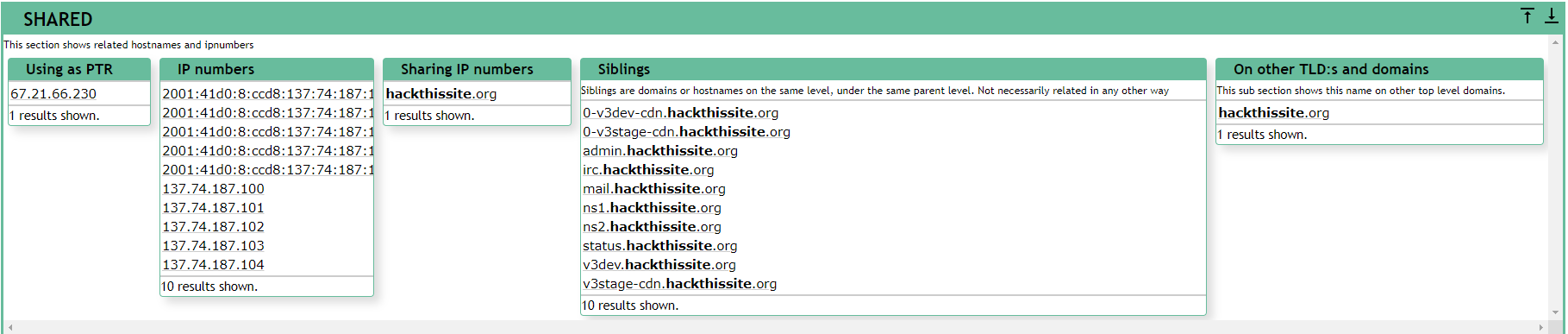
3. Robtex DNS lookup - Shows comprehensive info about the target website.

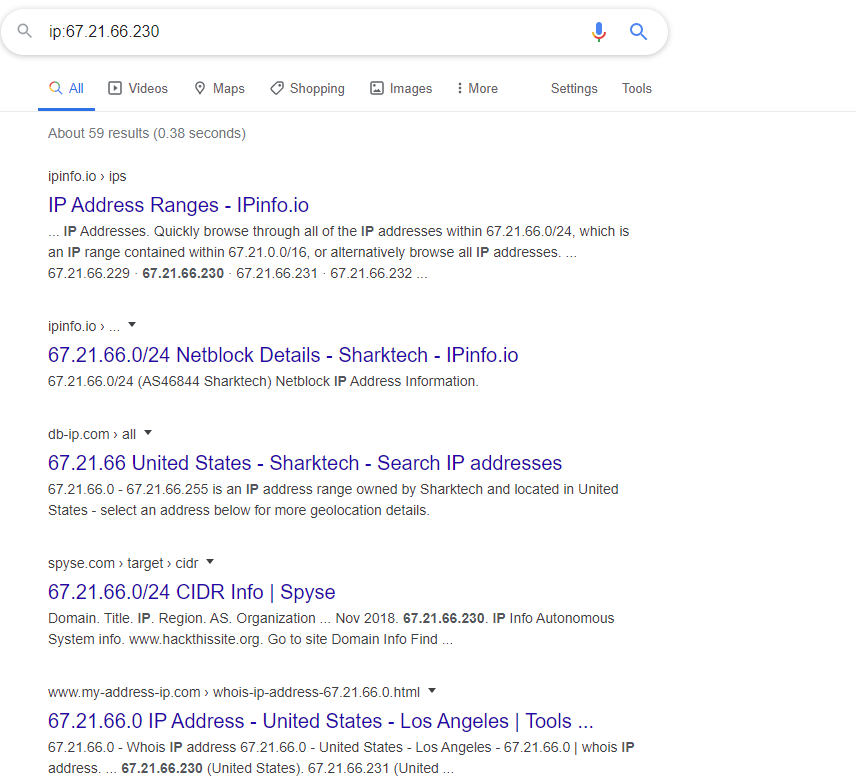
4. Discovering Websites On the Same Server
- One server can serve a number of websites.
- Gaining access to one can help gaining access to others.
To find websites on the same server:
(1) Use Robtex DNS lookup under"names pointing to same IP".
(2) Using bing.com, search for ip:[target ip]
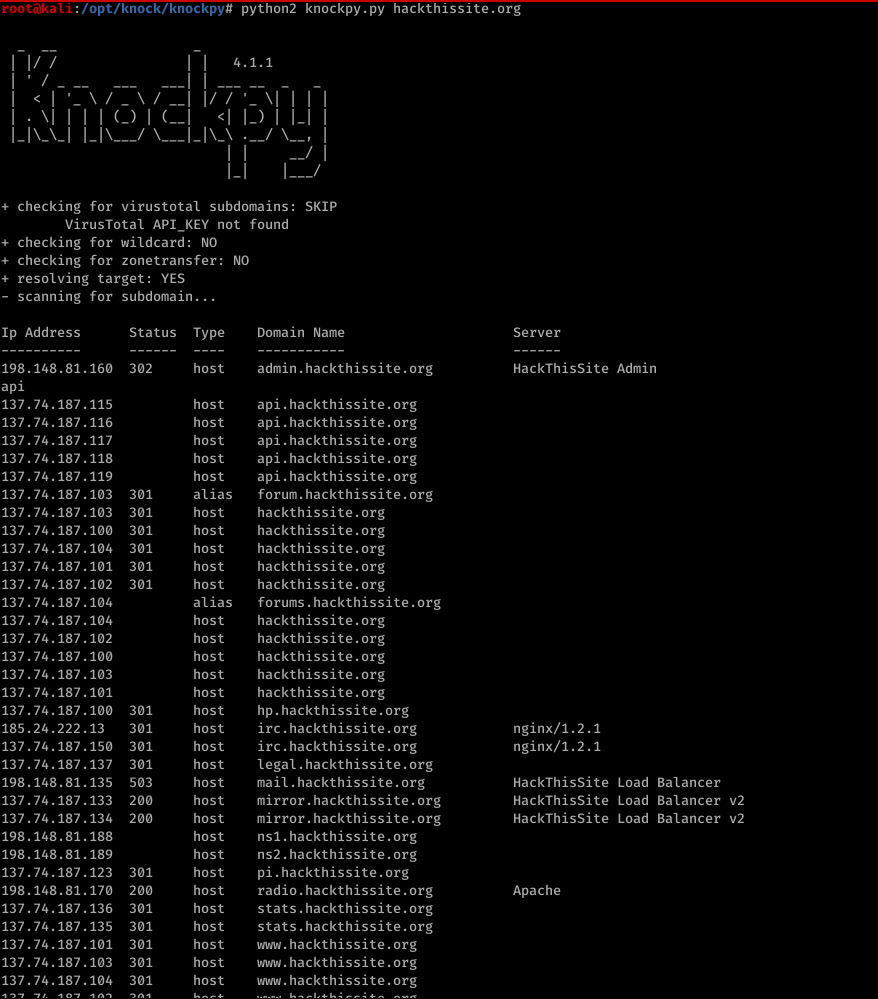
5. Discovering subdomains
- Subdomain.target.com
- Ex:https://www.hackthissite.org/
Knock can be used to find subdomainings of target.
(1)Download > git clone https://github.com/guelfoweb/knock.git
(2)Navigate to knock.py >cd knock/knock.py
(3)Run it > python knock.py [target]
6. Discovering Sensitive Files
Find files&directories in target website
Tool: drib
dirb [target] [worlist] [options]
For more info run > man dirb
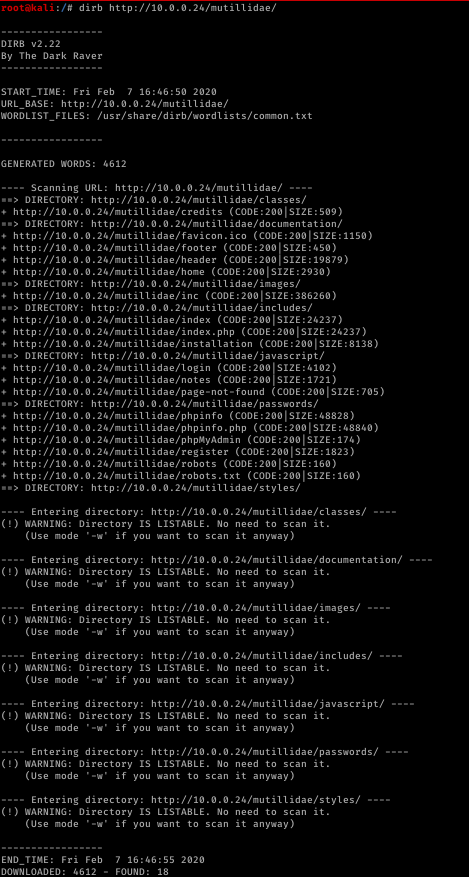
Analysing Discovered Files
---- Scanning URL: http://10.0.0.24/mutillidae/ ----
==> DIRECTORY: http://10.0.0.24/mutillidae/classes/
+ http://10.0.0.24/mutillidae/credits (CODE:200|SIZE:509)
==> DIRECTORY: http://10.0.0.24/mutillidae/documentation/
+ http://10.0.0.24/mutillidae/favicon.ico (CODE:200|SIZE:1150)
+ http://10.0.0.24/mutillidae/footer (CODE:200|SIZE:450)
+ http://10.0.0.24/mutillidae/header (CODE:200|SIZE:19879)
+ http://10.0.0.24/mutillidae/home (CODE:200|SIZE:2930)
==> DIRECTORY: http://10.0.0.24/mutillidae/images/
+ http://10.0.0.24/mutillidae/inc (CODE:200|SIZE:386260)
==> DIRECTORY: http://10.0.0.24/mutillidae/includes/
+ http://10.0.0.24/mutillidae/index (CODE:200|SIZE:24237)
+ http://10.0.0.24/mutillidae/index.php (CODE:200|SIZE:24237)
+ http://10.0.0.24/mutillidae/installation (CODE:200|SIZE:8138)
==> DIRECTORY: http://10.0.0.24/mutillidae/javascript/
+ http://10.0.0.24/mutillidae/login (CODE:200|SIZE:4102)
+ http://10.0.0.24/mutillidae/notes (CODE:200|SIZE:1721)
+ http://10.0.0.24/mutillidae/page-not-found (CODE:200|SIZE:705)
==> DIRECTORY: http://10.0.0.24/mutillidae/passwords/
+ http://10.0.0.24/mutillidae/phpinfo (CODE:200|SIZE:48828)
+ http://10.0.0.24/mutillidae/phpinfo.php (CODE:200|SIZE:48840)
+ http://10.0.0.24/mutillidae/phpMyAdmin (CODE:200|SIZE:174)
+ http://10.0.0.24/mutillidae/register (CODE:200|SIZE:1823)
+ http://10.0.0.24/mutillidae/robots (CODE:200|SIZE:160)
+ http://10.0.0.24/mutillidae/robots.txt (CODE:200|SIZE:160)
==> DIRECTORY: http://10.0.0.24/mutillidae/styles/ ---- Entering directory: http://10.0.0.24/mutillidae/classes/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway) ---- Entering directory: http://10.0.0.24/mutillidae/documentation/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway) ---- Entering directory: http://10.0.0.24/mutillidae/images/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway) ---- Entering directory: http://10.0.0.24/mutillidae/includes/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway) ---- Entering directory: http://10.0.0.24/mutillidae/javascript/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway) ---- Entering directory: http://10.0.0.24/mutillidae/passwords/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway) ---- Entering directory: http://10.0.0.24/mutillidae/styles/ ----
(!) WARNING: Directory IS LISTABLE. No need to scan it.
(Use mode '-w' if you want to scan it anyway) -----------------
END_TIME: Fri Feb 7 16:46:55 2020
DOWNLOADED: 4612 - FOUND: 18
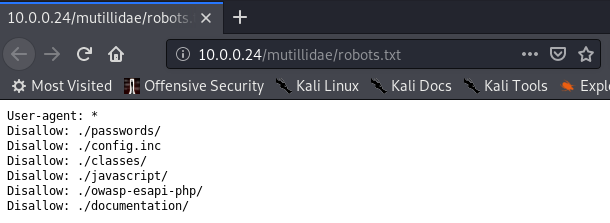
The URL in Red is useful to discove.
For example:
Gethering information is important, while it is harder to get useful information than before.
Ethical Hacking - Web Penetration Testing(2)的更多相关文章
- Ethical Hacking - Web Penetration Testing(13)
OWASP ZAP(ZED ATTACK PROXY) Automatically find vulnerabilities in web applications. Free and easy to ...
- Ethical Hacking - Web Penetration Testing(8)
SQL INJECTION WHAT IS SQL? Most websites use a database to store data. Most data stored in it(userna ...
- Ethical Hacking - Web Penetration Testing(10)
SQL INJECTION SQLMAP Tool designed to exploit SQL injections. Works with many DB types, MySQL, MSSQL ...
- Ethical Hacking - Web Penetration Testing(6)
REMOTE FILE INCLUSION Similar to local file inclusion. But allows an attacker to read ANY file from ...
- Ethical Hacking - Web Penetration Testing(1)
How to hack a website? An application installed on a computer. ->web application pen-testing A co ...
- Python Ethical Hacking - WEB PENETRATION TESTING(1)
WHAT IS A WEBSITE Computer with OS and some servers. Apache, MySQL ...etc. Cotains web application. ...
- Python Ethical Hacking - WEB PENETRATION TESTING(2)
CRAWING DIRECTORIES Directories/folders inside the web root. Can contain files or other directories ...
- Ethical Hacking - Web Penetration Testing(12)
XSS VULNS XSS - CROSS SITE SCRIPTING VULNS Allow an attacker to inject javascript code into the page ...
- Ethical Hacking - Web Penetration Testing(11)
SQL INJECTION Preventing SQLi Filters can be bypassed. Use a blacklist of commands? Still can be byp ...
- Ethical Hacking - Web Penetration Testing(9)
SQL INJECTION Discovering SQLi in GET Inject by browser URL. Selecting Data From Database Change the ...
随机推荐
- PHP|PHP之代码编写规范
PHP之代码编写规范 一.编辑器设置 1.使用Tab缩进(四个空格),不要直接使用空格 2.文件编码格式 二.命名设置 1.公共库名称空间 2.变量命名 2.1.所有字母都使用小写 2.2.首字母根据 ...
- 【初学Java学习笔记】AOP与OOP
AOP(Aspect Oriented Programming) 面向切面编程,是属于Spring框架中的内容.AOP相当于OOP的补充,当我们需要对多个对象引入一个公共行为,比如日志,操作记录等,就 ...
- 网易java高级开发课程 面对上亿数据量,网易用啥技术?
- linux shell编程子bash变量
参考视频:https://www.imooc.com/u/279399/courses?sort=publish https://www.imooc.com/video/6516 慕课网 用户的自定义 ...
- String类基础知识
1.String类的构造方法 (1)String(String original) //把字符串数据封装成字符串对象 (2)String(char[] c) //把字符数组的数据封装成字符串对象 ...
- SpringSceurity(5)---短信验证码登陆功能
SpringSceurity(5)---短信验证码登陆功能 有关SpringSceurity系列之前有写文章 1.SpringSecurity(1)---认证+授权代码实现 2.SpringSecur ...
- git push和pull如何解决冲突!!!精品
多人合作完成项目时,git push 和 pull经常会发生冲突,根本原因就是远程的东西和本地的东西长的不一样,以下步骤能完美解决所有冲突!(先查看一下分支(git branch),确认没错再进行下面 ...
- 错误C2280 Union:尝试引用已删除的函数
在编写Union共用体类型的时候,写了如下代码,在第5行出现错误: #include <iostream> #include <string> using namespace ...
- C# 特性篇 Attributes
特性[Required] (必修的) /// <summary> /// 操作人EmpID /// </summary> [Required] public string Op ...
- TreeMap实现
